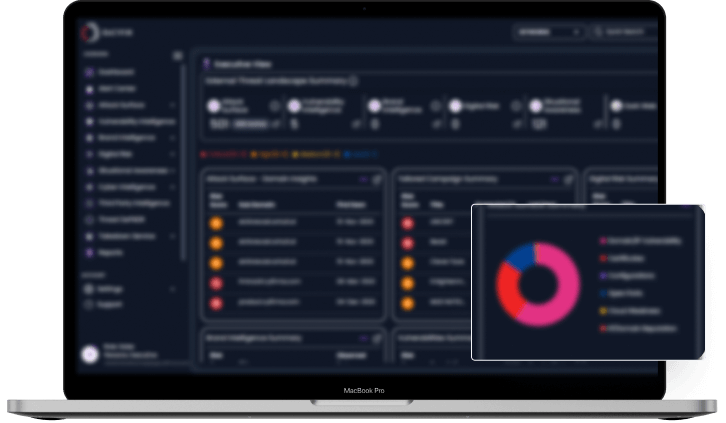
Comprehensive single-solution framework that correlates and attributes data to deliver precise, personalized, and prioritized insights

Integrates data from multiple sources, to create a consolidated view of all potential threats, ensuring nothing is overlooked

Advanced filtering and analytics to reduce noise by prioritizing threats based on relevance and context to the organization

Goes beyond traditional CVE scores by incorporating real-time intelligence and understanding adversary behaviour to identify not just high-severity vulnerabilities but also medium and low-severity ones that are actively being exploited

Emphasizes the personalization of threat data, tailoring insights to the specific needs and risks of the organization

Enriched context helps in understanding the intent, capabilities, and targets of potential attackers, allowing for a more informed and proactive defense strategy
DeCYFIR’s 9-Pillar Intelligence Preemptive ETLM Framework delivers comprehensive, proactive cyber defense through continuous, adversary-focused discovery and response.
You cannot defend what you cannot see. We are illuminating every shadow domain, forgotten asset, and silent exposure before the adversary ever see it.
Learn MoreContinuously maps IT and OT assets to identify vulnerabilities like misconfigurations, cloud gaps, open ports, weak certificates, and exposed logins or APIs. Combines threat intelligence, brand and third-party risks to deliver prioritized, actionable insights into critical attack paths based on adversary intent.
Learn More »Real-time detection of weaknesses in applications, operating systems, APIs, and misconfigurations. Integrates threat intelligence to deliver prioritized and actionable insights into vulnerabilities based on adversary intent.
Learn More »Proactive monitoring for impersonation, fraud, and brand abuse across digital channels.
Learn More »Detection and mitigation of data leaks, cloud exposures, and executive threats
Learn More »Assessment of supply chain vulnerabilities commonly exploited by attackers.
Learn More »Industry-specific, geo-targeted analysis of emerging threat trends.
Learn More »Provides actionable insights into attackers’ motives, tactics, and timelines, delivering early, environment-specific threat warnings tailored to the customer’s industry and location.
Learn More »Contextual, real-world threat education tailored for teams.
Learn More »Customized deception playbooks and intelligence from sector-focused sources, such as simulating supply-chain attacks in manufacturing to trap reconnaissance efforts or leveraging industry insider leaks for hyper-precise misdirection.
Learn More »Personalized to your needs
Developed for both business and technology leaders to support risk strategies
Case studies from some of our customers who have chosen DeCYFIR's intelligence-led approach to build a more secure enterprise
Predictive And Non-intrusive Solution Rather Than Expensive & Reactive Silo Offerings

DeCYFIR is the industry’ first Preemptive External Threat landscape management platform that delivers predictive, personalized and contextualized cyber intelligence enriched with attack surface and digital risk insights

The DeCYFIR platform informs defenders of impending cyberattacks at the stage of reconnaissance and weaponization before the adversary has started exploitation
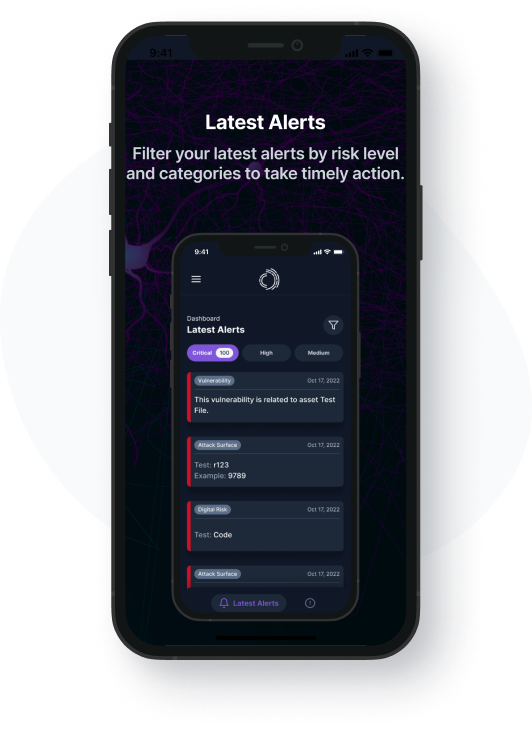
With the Alert App, clients gain the time advantage to take swift actions to close security gaps before cyber adversaries can cause damage
Clients can customize the notifications of the Alert App to support their risk posture management objectives