


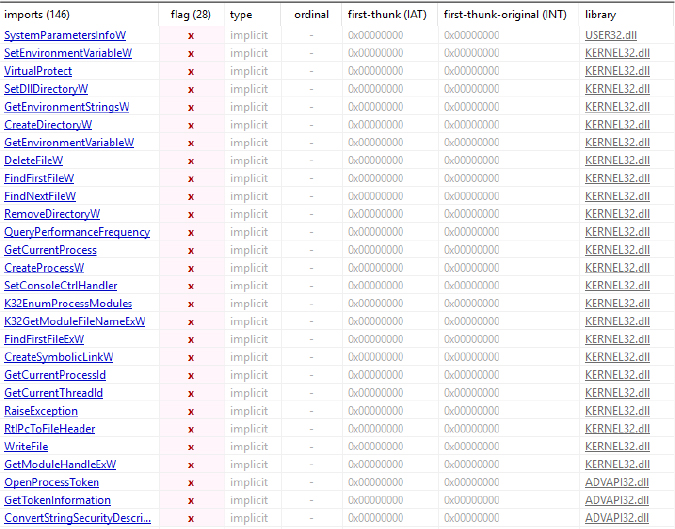
Cyfirma’s threat intelligence assessment reveals Inf0s3c Stealer, a Python-based grabber designed to collect system information and user data. The executable imports a range of Windows API functions for file and directory operations, process enumeration, system configuration access, memory manipulation, and security management, supporting its data collection and operational functionality. During execution, the malware systematically collects system details, including host identifiers, CPU information, and network configuration, and captures screenshots. It enumerates running processes and generates hierarchical views of user directories, such as Desktop, Documents, Pictures, and Downloads. All collected data is organized into a temporary working directory and compiled into a password-protected archive.
The analysis further indicates that the malware demonstrates automated exfiltration behavior by transmitting the packaged data to an external communication channel, reflecting capabilities for host reconnaissance, data aggregation, and secure packaging of stolen information.
This report documents the technical analysis of a Windows-based grabber malware specimen, “Inf0s3c stealer”. The binary under review was identified as a 64-bit Portable Executable (PE) that had been compressed with UPX and subsequently packed using PyInstaller. Upon unpacking and extraction, embedded Python bytecode and resources were retrieved, enabling closer inspection of the malware’s structure and behavior. The analysis covers the executable’s packing layers, imported Windows API functions, extracted components, and observed functionality relating to data collection and exfiltration.

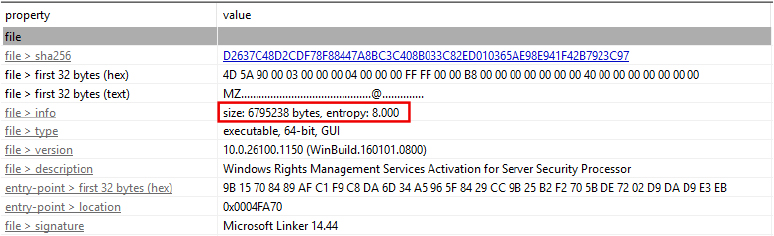
The sample file is a 64-bit Windows executable (PE format) with a size of 6,795,238 bytes and a very high entropy value of 8.000, indicating it is packed. The entry point at 0x0004FA70 contains atypical instructions, reinforcing the possibility of obfuscation.
The binary is packed with UPX 5.02 (NRV brute method), a common packer known for executable compression. The detection output also highlights modified overlays, section collisions, and appended data beginning at offset 0x00022000 with a size of 0x000658fe61, consistent with PyInstaller’s practice of embedding Python bytecode, libraries, and resources into the executable.
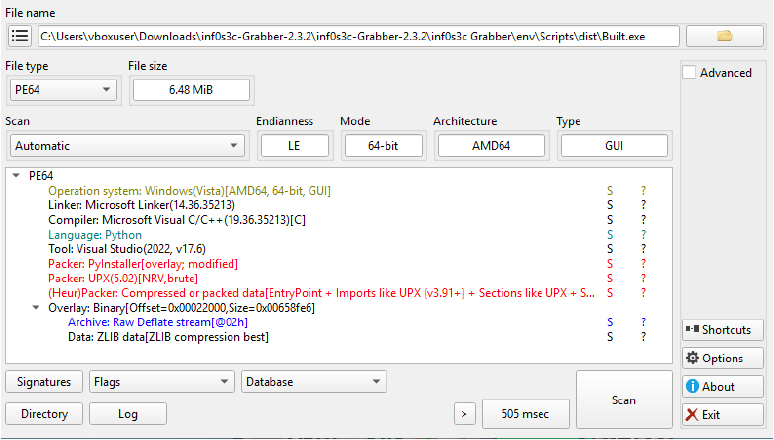
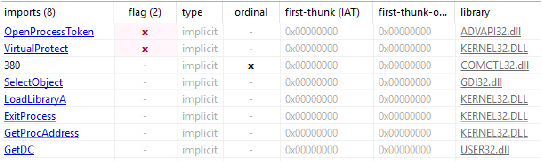
APIs such as OpenProcessToken and VirtualProtect are present in the import table, reflecting the binary’s capability requirements rather than unpacked runtime behavior. Overall, the file represents a PyInstaller-packed Python executable further compressed with UPX, with the packing layers serving both to reduce size and obscure internal code structure.
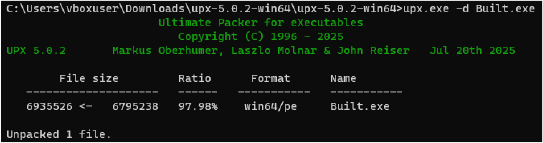
After removing the UPX packing, the executable is now restored to its original PyInstaller-packed form, with clean PE sections and visible imports, enabling further analysis of its Python bytecode and runtime behavior possible.
The executable imports a set of Windows API functions related to file operations, process management, environment control, memory handling, and system interaction, indicating capabilities consistent with system enumeration, persistence, and potential evasion techniques.
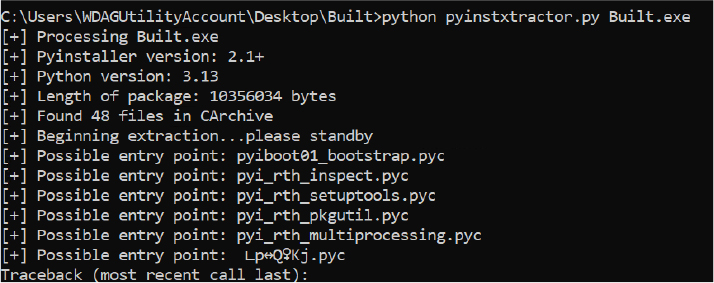
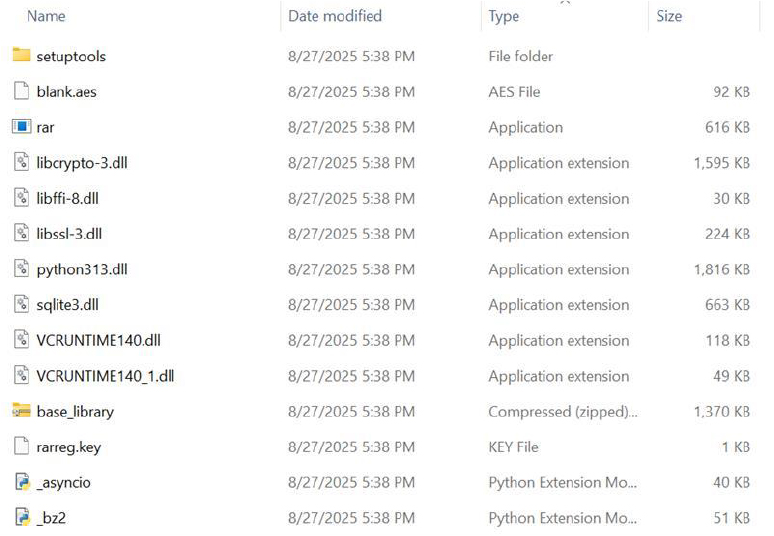
The unpacked executable was processed with a PyInstaller extractor, which retrieved the embedded files stored within the binary. This step pulled out the bundled resources and compiled Python bytecode (.pyc files) that PyInstaller had packaged into the overlay of the executable. The extraction separated these components into an accessible directory structure, allowing further examination and potential decompilation of the Python code to understand the program’s original logic and functionality.
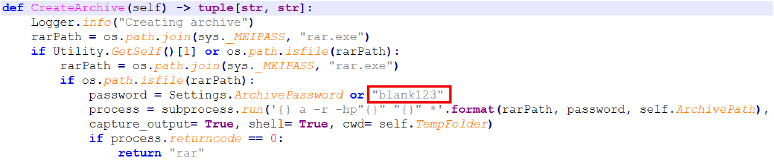
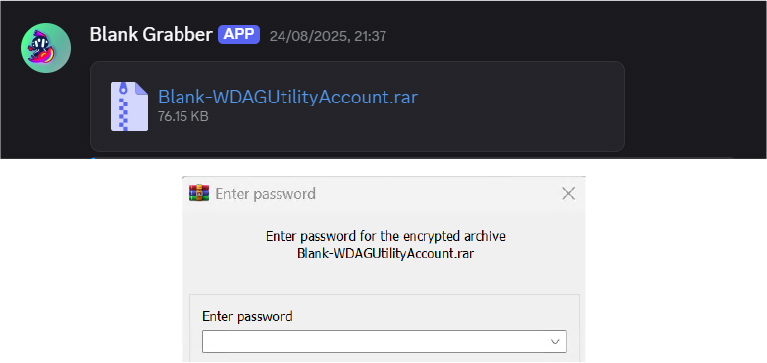
The extracted code includes a function that creates a password-protected RAR archive of collected data using rar.exe from the PyInstaller directory, applying either a configured or default password (“blank123”). In this case, it produced Blank-WDAGUtilityAccount.rar, confirming the malware’s design for secure data exfiltration.
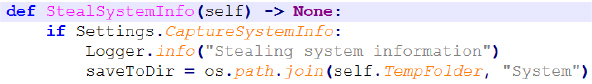
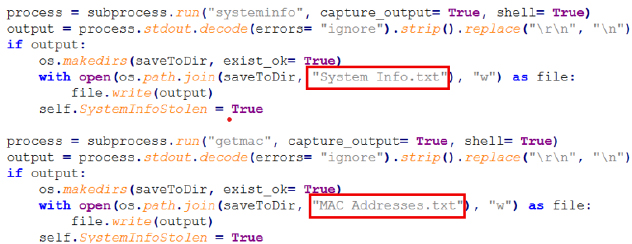
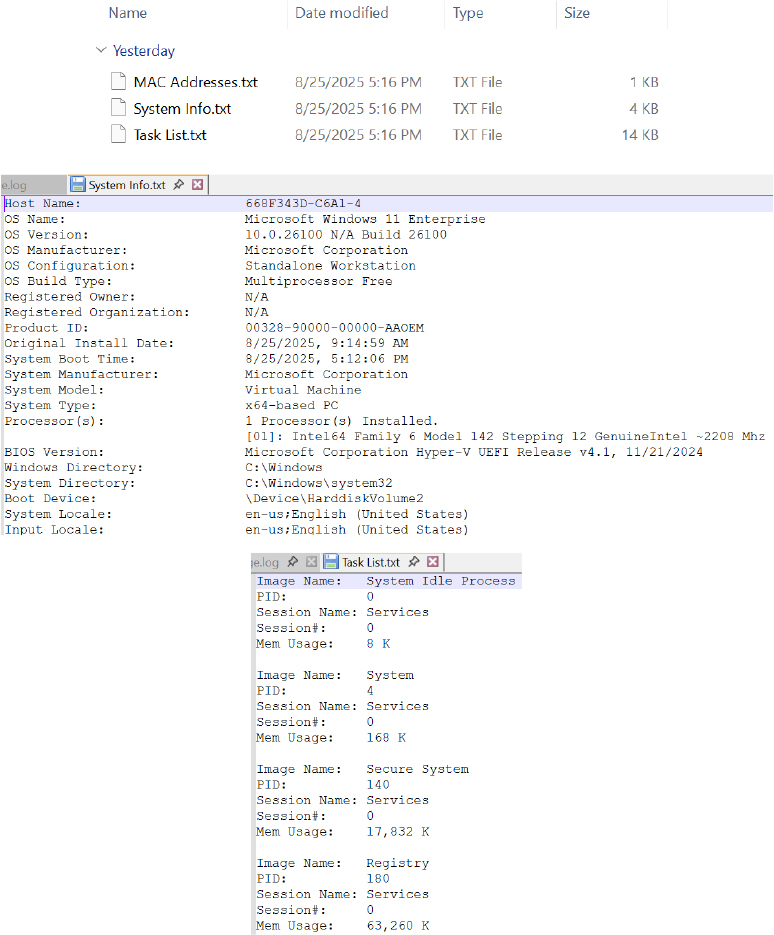
This snippet checks if system info collection is enabled, logs the action, and prepares a directory path (System) where the stolen information will be saved.
This code executes Windows commands (systeminfo and getmac) to gather detailed system information and MAC addresses, then saves the results into text files inside the designated directory.
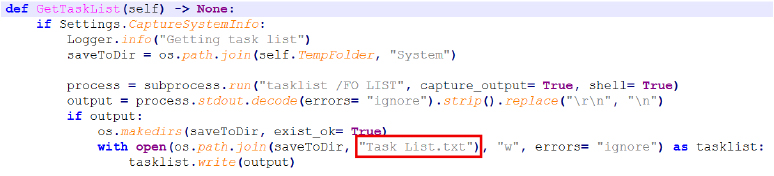
The function runs the tasklist command to capture all currently running processes on the system and saves the output into a text file for later use.
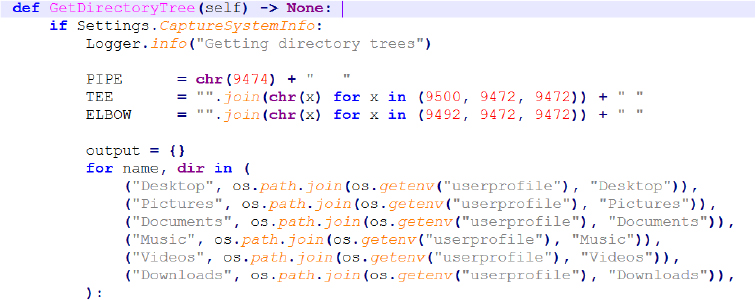
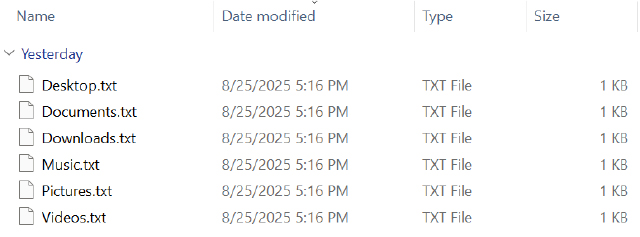
It enumerates common user directories (Desktop, Documents, Pictures, Music, Videos, Downloads) and generates a structured tree representation of their contents.
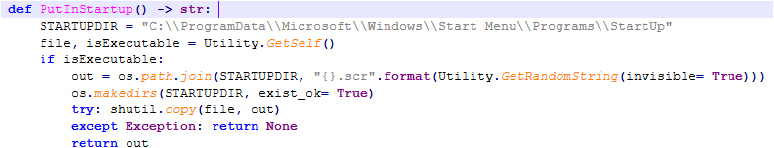
It copies the executable into the Windows Startup folder (disguised with a .scr extension) so it runs automatically each time the system starts.
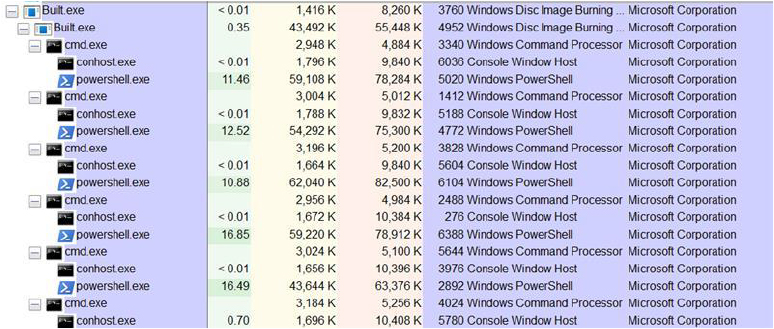
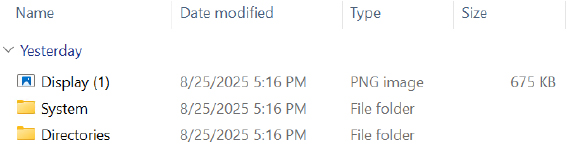
Upon execution, Build.exe silently invokes multiple PowerShell commands through the Command Prompt to gather host information, including system configuration, network details, running processes, and directory structures from common user folders.
It then creates a directory within a %temp% to store collected data and generated files, serving as the grabber’s isolated workspace.
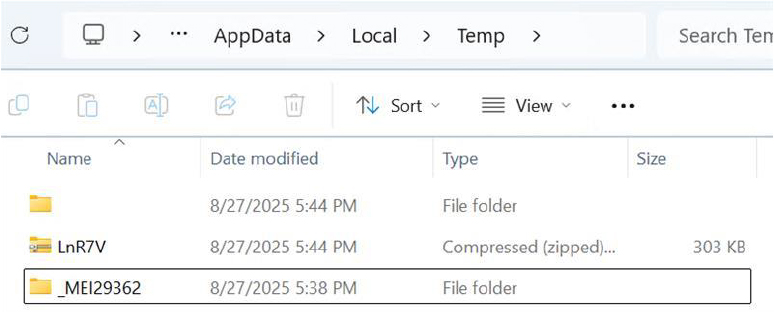
The executable unpacks and loads bundled dependency libraries, including an embedded Python environment and required modules, enabling independent execution without relying on host system components.
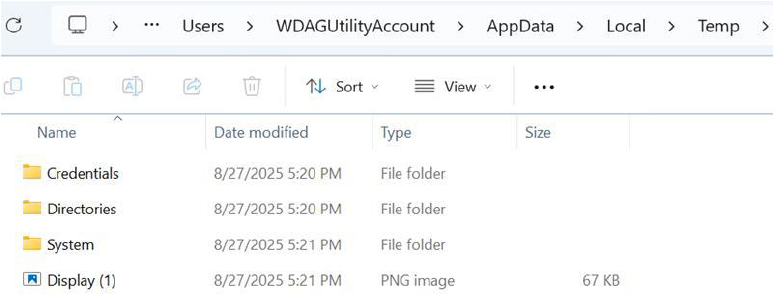
The program then creates subdirectories (e.g., Credentials, Directories, System) to store system details, process lists, network data, and a desktop screenshot, which are organized in the temp directory before being archived and exfiltrated to the attacker’s Discord channel.
The report captures system details such as computer name, CPU information, and product key, while fields like OS, memory, UUID, and GPU were targeted but not retrieved during this execution.
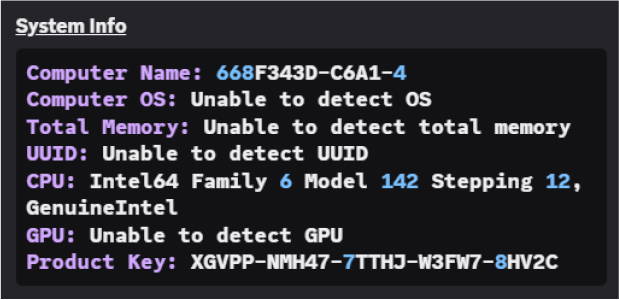
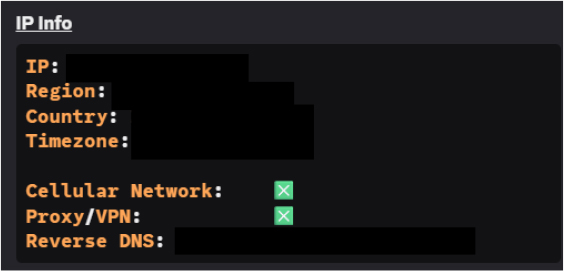
Additionally, the malware successfully collects IP information, including external IP, region, country, time zone, reverse DNS, and confirms the absence of proxy or VPN usage.
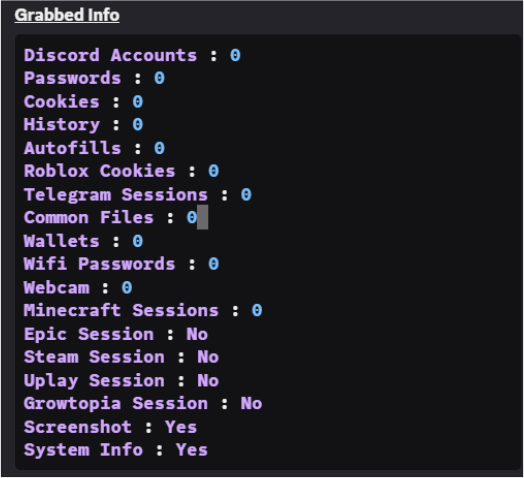
The grabber targets a wide range of sensitive information, including Discord accounts and passwords, cookies, browser history, autofills, Roblox cookies, Telegram sessions, cryptocurrency wallets, Wi-Fi credentials, Minecraft and Epic Games sessions, Growtopia accounts, screenshots, and other related data.
The results, delivered via Discord, include a RAR archive named Blank-WDAGUtilityAccount.rar containing the stolen data.
When enabled, the malware runs systeminfo and getmac to collect OS, hardware, and MAC address details, saving them in a System folder within its temporary directory. The data package also includes Display (1).png, indicating it captures both textual system information and screenshots.
The stealer retrieves a list of running processes by executing the command tasklist/FO LIST and saves the output as Task List.txt within the System folder, storing process details together with other collected information.
The function GetDirectoryTree() collects directory structures from user folders (Desktop, Pictures, Documents, Music, Videos, Downloads) using tree /A /F, reformats the output for readability, and saves each as a text file in the Directories folder within the temporary directory.
Inf0s3c Stealer demonstrates capabilities for system reconnaissance, data collection, and automated exfiltration, indicating its potential as a versatile information-stealing tool. Given its modular design, obfuscation mechanisms, and alignment with other publicly available malware projects, future variants could expand functionality to target additional user data, employ stronger evasion techniques, or integrate with broader attack frameworks.
During execution, the grabber transmits the collected data to an external channel, where it appears as a message labeled “Blank Grabber” accompanied by its corresponding icon.
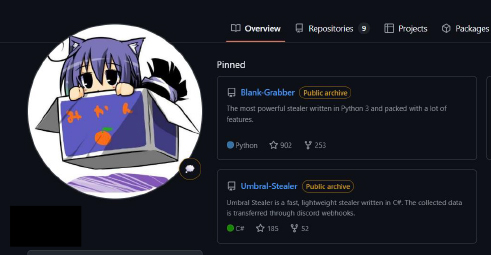
Analysis of the extracted script reveals an obfuscation routine that compresses and Base64-encodes the Python code, which is then reconstructed and executed at runtime, providing a layer of protection against inspection. The techniques and structure observed in this script closely align with publicly available projects shared by the same developer, including both the Blank Grabber and Umbral-Stealer. This consistent design, obfuscation strategy, and operational behavior indicate that the author of the analyzed infosec grabber may also be responsible for these other malware projects.
The similarity of its design and methods to other publicly observed malware projects indicates potential for rapid iteration and wider distribution. Organizations should prioritize proactive endpoint protection, network monitoring, and threat intelligence sharing to detect and mitigate evolving variants, alongside user awareness and secure data handling practices to reduce exposure to such threats.
The grabber analyzed in this report illustrates the deliberate design and operational sophistication of modern information-stealing malware. By combining system reconnaissance, organized data collection, and encrypted packaging, it achieves automated exfiltration while limiting visibility into its internal processes. The presence of obfuscation and modular code highlights the emphasis on evasion and adaptability. Its ability to collect diverse system information and generate structured archives demonstrates a clear focus on efficient data theft. This analysis underscores the importance of continuous monitoring, timely threat intelligence, and comprehensive endpoint defenses to detect and respond to such evolving malware threats.
| Tactic | ID | Technique Name |
| Execution | T1047 | Windows Management Instrumentation |
| T1059.001 | Command and Scripting Interpreter: PowerShell | |
| T1064 | Scripting | |
| T1106 | Native API | |
| T1129 | Shared Modules | |
| Persistence | T1112 | Modify Registry |
| T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder | |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Defense Evasion | T1027.002 | Obfuscated Files or Information: Software Packing |
| T1036 | Masquerading | |
| T1070.006 | Indicator Removal: Timestomp | |
| T1140 | Deobfuscate/Decode Files or Information | |
| T1202 | Indirect Command Execution | |
| T1497.001 | Virtualization/Sandbox Evasion: System Checks | |
| T1562.001 | Impair Defenses: Disable or Modify Tools | |
| Credential Access | T1003 | OS Credential Dumping |
| Discovery | T1057 | Process Discovery |
| T1082 | System Information Discovery | |
| T1083 | File and Directory Discovery | |
| T1497.001 | Virtualization/Sandbox Evasion: System Checks | |
| Collection | T1005 | Data from Local System |
| T1115 | Clipboard Data | |
| Command and Control | T1071 | Application Layer Protocol |
| Impact | T1485 | Data Destruction |
| T1486 | Data Encrypted for Impact |
rule Inf0s3c_Grabber_Malware
{
meta:
description = “Detects Inf0s3c Grabber malware”
author = “Cyfirma Research”
date = “2025-08-26”
hash = “50AE8793DBF1D9B543EE3CFAA01CAB0547DABB83033D1F142F2E672FCD0DC040”
strings:
// Unique identifiers from analysis
$s1 = “Blank Grabber” ascii wide nocase
$s2 = “blank123” ascii wide // hardcoded archive password
$s3 = “rar.exe” ascii wide
// API imports used for process/system operations
$api1 = “OpenProcessToken” ascii wide
$api2 = “VirtualProtect” ascii wide
$api3 = “GetEnvironmentVariableW” ascii wide
$api4 = “ConvertStringSecurityDescriptorToSecurityDescriptorW” ascii wide
// PyInstaller + UPX indicators
$pyi1 = “pyi_rth_” ascii
$pyi2 = “_MEIPASS” ascii
$upx1 = “UPX!” ascii
condition:
uint16(0) == 0x5A4D and // PE file
3 of ($s*) and
2 of ($api*) and
1 of ($pyi*) and
$upx1
}