


Ransomware activity in March 2026 reflects a maturing, highly adaptive, and increasingly industrialized threat ecosystem, with 772 incidents recorded, continuing the sustained growth observed throughout 2025 and confirming that activity is scaling rather than declining. The landscape is characterized by dynamic actor redistribution, where dominant groups such as Qilin significantly expand operations while others contract, indicating a competitive and continuously rebalanced ransomware-as-a-service (RaaS) environment supported by a fragmented network of affiliates and initial access brokers. Targeting remains strategically focused on high-value economies, led overwhelmingly by the United States, and on operationally critical sectors, such as Professional Services, Manufacturing, Healthcare, and Information Technology, where data sensitivity and business disruption can be effectively monetized. At the same time, attackers are advancing tradecraft through rapid exploitation of vulnerabilities, credential-based access, living-off-the-land techniques, and low-detection execution methods, enabling faster and stealthier intrusions. A significant structural shift is also evident in ransomware economics, with declining victim payment rates but increasing ransom demands, reflecting a move toward selective high-value extortion alongside broad attack volume, while the growing convergence with state-sponsored operations and scalable infrastructure abuse underscores ransomware’s evolution into a resilient, modular, and globally distributed cybercrime ecosystem.
Welcome to the March 2026 Ransomware Threat Report. This report delivers a detailed analysis of the ransomware landscape, highlighting the emergence of new ransomware groups, evolving attack techniques, and notable shifts in targeted industries. By examining key trends, tactics, and significant incidents, this report aims to support organizations and security teams in understanding the current threat environment. As ransomware campaigns continue to grow in complexity, this report serves as a vital resource for anticipating future threats and strengthening proactive cybersecurity strategies.
Throughout March 2026, there was notable activity from several ransomware groups. Here are the trends regarding the top 10:
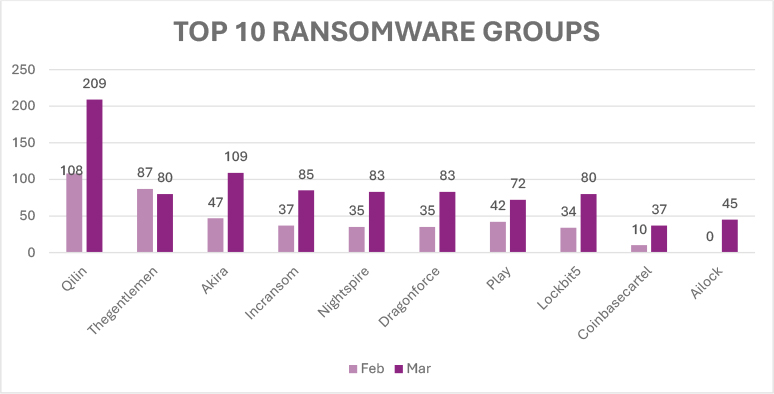
The February–March 2026 data indicates a clear intensification of ransomware activity driven by uneven growth across multiple groups rather than a uniform trend. Qilin remained the most active operator, increasing sharply from 108 to 209 incidents, which suggests a significant expansion in operational capacity and possibly broader affiliate participation. Thegentlemen experienced a moderate decline (87 → 80), but its activity level still reflects consistent operational presence. Several groups recorded notable increases, including Akira (47 → 109), which more than doubled its activity, along with Incransom (37 → 85), Nightspire (35 → 83), and Dragonforce (35 → 83), all pointing to heightened campaign execution and scaling efforts. Play (42 → 72) and LockBit5 (34 → 80) also demonstrated steady upward movement, indicating the continued relevance and adaptability of established ransomware operations. At the same time, Coinbasecartel (10 → 37) and Ailock (0 → 45) showed rapid emergence or expansion, highlighting new entrants or previously low-visibility actors gaining traction. Overall, March reflects a more competitive and active ransomware landscape, where growth across a broad set of actors offsets minor declines, emphasizing ongoing evolution and expansion within the ransomware-as-a-service ecosystem.
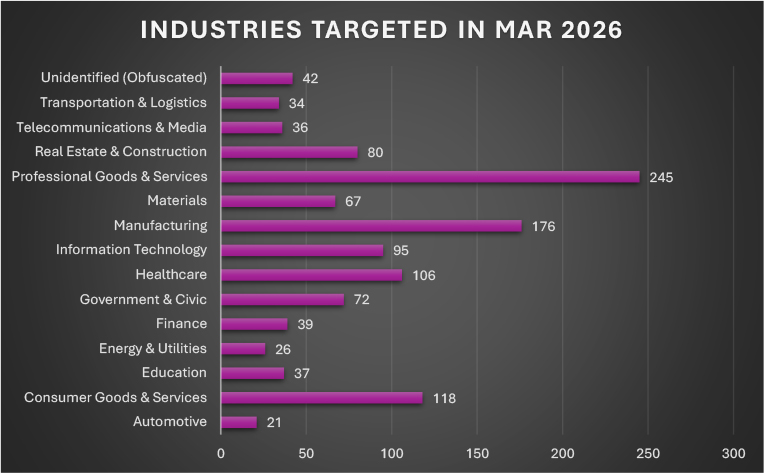
In March 2026, ransomware activity remained heavily concentrated in sectors combining operational dependency with high-value data exposure, with Professional Goods & Services (245 incidents) emerging as the most targeted sector, reflecting attackers’ focus on organizations holding sensitive client and business-critical data. Manufacturing (176) and Consumer Goods & Services (118) also recorded substantial activity, highlighting continued pressure on production-driven and customer-facing industries where disruption directly impacts revenue streams. Significant targeting was further observed in Healthcare (106) and Information Technology (95), underscoring risks to critical services and the strategic role of IT providers within broader supply chains. Additional activity was distributed across Real Estate & Construction (80), Government & Civic (72), and Materials (67), indicating sustained exposure in infrastructure and public-facing sectors. Mid-tier activity included Finance (39), Education (37), Telecommunications & Media (36), and Transportation & Logistics (34), while comparatively lower volumes were recorded in Energy & Utilities (26) and Automotive (21); alongside 42 unidentified or obfuscated cases, the overall distribution reinforces a consistent targeting strategy focused on industries where operational disruption and data compromise can be most effectively monetized.
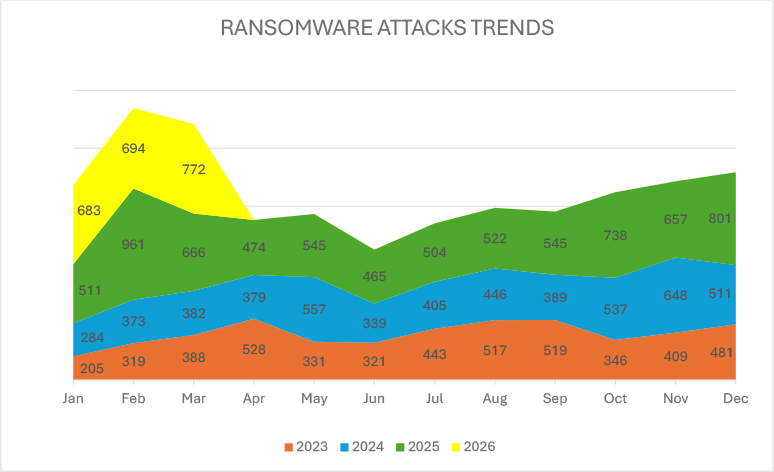
Ransomware activity demonstrates a clear year-on-year escalation, with December 2025 reaching 801 incidents, the highest monthly total across the 2023–2026 dataset, significantly surpassing December 2024 (511) and December 2023 (481), indicating structural growth rather than seasonal fluctuation. Throughout 2025, activity remained consistently elevated, with most months exceeding 500 incidents and a pronounced surge in Q4, particularly in October (738), November (657), and the December peak. This upward momentum has carried into 2026, with January recording 683 incidents, February 694, and March rising further to 772, compared to 511, 961, and 666 in the same period of 2025 and notably lower levels in 2024 and 2023. While February 2025 represents an outlier spike, the broader trend confirms sustained operational scaling, expansion of ransomware-as-a-service (RaaS) affiliate ecosystems, and improved campaign throughput, reinforcing that ransomware activity is not only persisting but continuing to mature and expand into 2026.
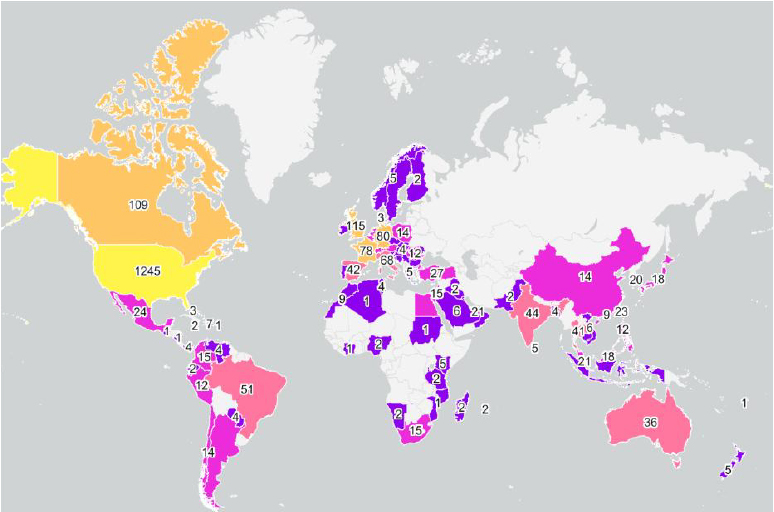
Ransomware activity in March 2026 remained heavily concentrated in the United States, which recorded 1,245 victims, maintaining a dominant lead over all other countries and reinforcing its position as the primary global target. A second tier of heavily targeted regions included the United Kingdom (115) and Canada (109), followed by Germany (80), France (78), and Italy (68), highlighting sustained adversary focus on mature, high-value economies. Beyond this, notable activity was observed in Brazil (51), India (44), Spain (42), Thailand (41), and Australia (36), indicating continued expansion into both developed and emerging markets. Mid-level activity was distributed across countries such as Switzerland (27) and Turkey (27), Mexico (24), Taiwan (23), Singapore (21), UAE (21), South Korea (20), and Argentina (19), reflecting consistent targeting of globally connected economies and regional hubs, while the remaining countries largely reported low double-digit or single-digit incidents, demonstrating a long-tail pattern of opportunistic attacks; overall, the landscape continues to exhibit a strong geographic concentration alongside broad global dispersion.
Fragmentation and Value Extraction Reshaping the Ransomware Economy
Recent data from the blockchain intelligence platform Chainalysis indicates a structural shift in ransomware operations, where the number of attacks continues to surge while victim payment rates decline significantly. In 2025, only 28% of victims paid ransom demands compared to 62.8% in 2024 and 78.9% in 2022, despite ransomware actors claiming substantially more attacks. This trend highlights a transition from reliance on high payment compliance to broader attack volume and diversified extortion strategies. At the same time, the median ransom payment increased by 368%, indicating that ransomware operators are focusing on extracting larger payments from a smaller subset of victims. The ecosystem has also become increasingly fragmented, with approximately 85 active extortion groups operating simultaneously, contrasting with earlier years when a few dominant Ransomware-as-a-Service (RaaS) groups controlled the landscape. The emergence of supporting criminal services such as initial access brokers and the continued targeting of high-value organizations in developed economies demonstrate how the ransomware ecosystem has matured into a distributed cybercrime supply chain.
ETLM Assessment:
Looking ahead, ransomware operators are likely to further refine selective targeting and extortion models to compensate for declining payment compliance. Threat actor groups may increasingly prioritize high-impact sectors and organizations with sensitive data, enabling them to demand higher ransom amounts even if fewer victims ultimately pay. The growing fragmentation of extortion groups suggests that smaller or emerging threat actor groups could adopt automation, AI-assisted reconnaissance, and data-driven victim profiling to scale operations efficiently. Additionally, the expanding role of initial access brokers and the declining cost of network access may enable ransomware actors to industrialize intrusion pipelines, potentially leading to faster attack cycles, more coordinated data-theft-driven extortion campaigns, and greater integration with other cybercrime ecosystems such as stealer-log marketplaces and underground access-trading networks.
State-Sponsored Financial Operations Converging with the Ransomware Ecosystem
Security researchers at Symantec linked ransomware activity involving the Medusa Ransomware platform to the threat actor group Lazarus Group, specifically a subgroup believed to be Andariel. This development reflects a notable shift where state-backed cyber operators integrate financially motivated ransomware campaigns alongside espionage operations. Medusa, which has impacted hundreds of organizations since its emergence in 2021, is now being leveraged as part of North Korean’s revenue-generation activities targeting U.S. healthcare organizations. The operational toolkit observed in these attacks includes commodity and previously attributed Lazarus-linked tools such as Blindingcan, credential harvesting utilities, and access mechanisms similar to those associated with Diamond Sleet. This blending of ransomware-as-a-service infrastructure with state-sponsored intrusion tradecraft highlights how ransomware operations are no longer limited to financially motivated cybercrime groups but are increasingly integrated into geopolitical cyber strategies designed to fund broader intelligence and military objectives.
ETLM Assessment:
The involvement of a state-backed threat actor group such as Lazarus in ransomware operations suggests that financially driven extortion campaigns may increasingly serve as strategic funding mechanisms for sanctioned regimes. In the future, state-aligned threat actors could further leverage RaaS ecosystems to obscure attribution, outsource parts of the intrusion lifecycle, and scale revenue-generating attacks while maintaining plausible deniability. This convergence may also lead to hybrid campaigns where ransomware intrusions simultaneously enable data exfiltration, intelligence collection, and financial theft. Additionally, targeting patterns may continue to expand across critical infrastructure sectors such as healthcare, defense contractors, and technology providers, as these environments provide both sensitive data and the financial pressure necessary to drive higher ransom demands.
Rapid Weaponization of Enterprise Remote Access Vulnerabilities in Ransomware Intrusions
The exploitation of CVE-2026-1731 in BeyondTrust Remote Support demonstrates how ransomware operators increasingly capitalize on newly disclosed vulnerabilities in enterprise access platforms to accelerate intrusion campaigns. The vulnerability, a pre-authentication remote code execution flaw affecting Remote Support and BeyondTrust Privileged Remote Access, was rapidly weaponized following disclosure, with exploitation observed even before public proof-of-concept code became widely available. According to the Cybersecurity and Infrastructure Security Agency, the flaw was added to the Known Exploited Vulnerabilities catalog after evidence showed it was being leveraged in ransomware operations. This pattern reflects a broader shift in ransomware tradecraft where threat actors prioritize high-impact enterprise software vulnerabilities to gain immediate privileged access to internal networks, enabling faster lateral movement and large-scale deployment of ransomware payloads.
ETLM Assessment:
The operational use of critical remote access vulnerabilities in ransomware campaigns suggests that future actors will increasingly monitor vulnerability disclosures and rapidly operationalize exploits within days or even hours of public release. Ransomware operators and affiliated access brokers may automate vulnerability scanning against exposed enterprise management platforms to identify unpatched systems at scale. As organizations continue to rely on remote administration and privileged access solutions, these systems are likely to remain high-value targets for initial access operations, potentially leading to faster intrusion timelines and more opportunistic ransomware deployments that exploit patching delays across enterprise environments.
International Law Enforcement Pressure Targeting Distributed Ransomware Affiliate Networks
The arrest of a suspect linked to the Phobos Ransomware during the multinational investigation known as Operation Aether highlights the decentralized structure that characterizes modern ransomware ecosystems. Phobos operates as a ransomware-as-a-service (RaaS) platform in which affiliates conduct network intrusions and deploy ransomware while core operators maintain the infrastructure and tooling. According to Europol and national authorities, coordinated investigations have increasingly targeted multiple operational layers, including administrators, infrastructure operators, and intrusion affiliates. Evidence recovered from the arrested individual, including stolen credentials, credit card data, and server access information, demonstrates how ransomware campaigns rely on supporting criminal resources such as credential theft and illicit access markets. This case illustrates how ransomware operations have evolved into distributed cybercrime networks where affiliates, access brokers, and infrastructure operators collectively enable large-scale attacks across thousands of organizations.
ETLM Assessment:
Sustained international law enforcement actions against ransomware affiliates and infrastructure are likely to push ransomware ecosystems toward greater operational resilience and decentralization. Threat actor groups operating RaaS platforms may increasingly adopt compartmentalized operational structures, anonymous communication channels, and rotating infrastructure to reduce the risk of disruption. At the same time, affiliates may rely more heavily on underground marketplaces for stolen credentials, network access, and exploit kits to maintain attack pipelines even when core operators are disrupted. These developments suggest that ransomware ecosystems could become more modular and fragmented, allowing threat actor groups to rapidly reconstitute operations despite arrests or infrastructure seizures.
Operational Camouflage Through Legitimate Administrative Tooling in Ransomware Intrusions
Investigations by Huntress revealed that the threat actor group Crazy Ransomware Gang leveraged legitimate enterprise software such as Net Monitor for Employees Professional and SimpleHelp to maintain persistent access within compromised corporate environments. Instead of relying solely on custom malware, the attackers installed legitimate monitoring and remote administration tools using native utilities such as msiexec.exe, enabling them to remotely observe user activity, transfer files, execute commands, and monitor sensitive behaviors such as cryptocurrency wallet usage. This approach reflects a growing ransomware tactic often referred to as “living-off-the-land,” where adversaries rely on legitimate tools and administrative utilities to blend into normal network activity and evade traditional security controls. The attackers also implemented redundancy by deploying multiple remote access tools and disabling security mechanisms such as Windows Defender, demonstrating how ransomware operators increasingly prioritize stealthy persistence and operational visibility before deploying encryption payloads.
ETLM Assessment:
The increasing abuse of legitimate remote monitoring and administrative software suggests that ransomware operators may continue shifting toward tool-based intrusion strategies that minimize the need for custom malware. Threat actor groups could expand this approach by leveraging widely used enterprise IT management platforms, remote support applications, and cloud-based monitoring services to disguise malicious activity within legitimate administrative workflows. Additionally, attackers may increasingly integrate credential theft, session monitoring, and behavioral triggers such as detecting cryptocurrency wallet usage or security tool activity to optimize the timing of ransomware deployment or financial theft. As a result, future ransomware campaigns may rely more heavily on credential-based access, trusted software abuse, and layered persistence mechanisms, making detection more challenging for organizations relying primarily on signature-based security controls.
Supply-Side Software Weaknesses Enabling High-Impact Ransomware Intrusions
The breach of SmarterTools by the threat actor group Warlock Ransomware Group demonstrates how ransomware operators increasingly exploit vulnerabilities in enterprise communication platforms to gain privileged access and stage network-wide attacks. In this incident, attackers leveraged CVE-2026-23760 affecting SmarterMail to reset administrator credentials and obtain full control over an unpatched virtual machine. After gaining access, the attackers performed lateral movement through Active Directory and deployed legitimate administrative and digital forensics utilities such as Velociraptor and SimpleHelp to maintain persistence and expand network control before attempting ransomware deployment. Security researchers at ReliaQuest linked the activity with moderate-to-high confidence to the threat actor Storm-2603, illustrating the growing convergence of vulnerability exploitation, legitimate tool abuse, and ransomware deployment in sophisticated intrusion campaigns.
ETLM Assessment:
The exploitation of enterprise software vulnerabilities for ransomware operations indicates that attackers will continue prioritizing widely deployed business applications such as email servers, remote access platforms, and collaboration systems as initial access vectors. Future campaigns may increasingly chain multiple vulnerabilities and built-in administrative features to achieve stealthier privilege escalation and lateral movement. Threat actor groups could also expand the use of legitimate security and forensic tools to persist within networks while blending into routine administrative activity, making detection significantly more challenging. As ransomware operations increasingly intersect with state-linked threat actors and advanced intrusion techniques, organizations may face more hybrid campaigns that combine vulnerability exploitation, espionage-style persistence, and financially motivated extortion.
Unpatched Enterprise Collaboration Platforms Emerging as High-Value Ransomware Entry Points
The exploitation of CVE-2026-24423 in SmarterMail highlights how ransomware operators increasingly weaponize vulnerabilities in widely deployed business communication platforms to obtain immediate system-level access. According to the Cybersecurity and Infrastructure Security Agency, the flaw caused by missing authentication in the ConnectToHub API allows attackers to execute operating system commands remotely without prior authentication. Because SmarterMail is commonly deployed by managed service providers and hosting providers, exploitation of such vulnerabilities can provide attackers with privileged access across multiple organizational environments simultaneously. The rapid inclusion of this vulnerability in the Known Exploited Vulnerabilities catalog indicates that ransomware actors are actively integrating newly disclosed enterprise software flaws into their intrusion pipelines to accelerate initial access and large-scale compromise.
ETLM Assessment:
The active exploitation of collaboration and messaging infrastructure suggests that ransomware operators may increasingly prioritize vulnerabilities in platforms that provide centralized communication, authentication, and administrative functionality. Future campaigns may focus on managed service providers and shared hosting environments where compromising a single platform can potentially expose multiple downstream organizations. In addition, attackers may automate scanning for exposed enterprise services and rapidly deploy exploit chains targeting newly disclosed vulnerabilities, reducing the time between vulnerability disclosure and active ransomware exploitation. This trend indicates a growing reliance on vulnerability-driven initial access strategies that enable ransomware actors to scale attacks across interconnected business ecosystems.
Enterprise Messaging Infrastructure Vulnerabilities Accelerating Ransomware Initial Access
The active exploitation of CVE-2026-24423 in SmarterMail demonstrates how ransomware operators increasingly weaponize vulnerabilities in widely deployed enterprise communication platforms to gain immediate system-level access. The flaw, identified by researchers from watchTowr, CODE WHITE, and VulnCheck, allows attackers to execute operating system commands remotely through the ConnectToHub API due to missing authentication controls. According to the Cybersecurity and Infrastructure Security Agency, ransomware actors have already incorporated this vulnerability into active campaigns, leading to its inclusion in the Known Exploited Vulnerabilities (KEV) catalog. Because SmarterMail is widely used by managed service providers, hosting providers, and small-to-medium enterprises across more than 120 countries, exploitation of this vulnerability provides attackers with a scalable entry point into organizational environments, reinforcing the growing reliance of ransomware operations on vulnerability-driven initial access.
ETLM Assessment:
The exploitation of enterprise messaging and collaboration infrastructure indicates that ransomware actors will likely continue prioritizing widely deployed administrative platforms that provide centralized access to communication and identity systems. Future campaigns may increasingly automate the scanning and exploitation of exposed email servers, particularly those used by managed service providers, where compromising a single instance could provide indirect access to multiple downstream organizations. Additionally, attackers may continue chaining authentication bypass flaws, API-level vulnerabilities, and remote execution exploits to establish stealthy persistence within enterprise infrastructure before deploying ransomware payloads or conducting data-extortion operations.
Abuse of Virtual Infrastructure Platforms for Scalable Ransomware Payload Distribution
Researchers at Sophos observed ransomware operators leveraging virtual machines provisioned through VMmanager, developed by ISPsystem, to host and distribute malicious payloads at scale. The activity was identified during investigations into incidents involving the threat actor group associated with WantToCry Ransomware, where attackers deployed Windows virtual machines using default templates that reused identical hostnames and system identifiers. This infrastructure pattern was also observed across campaigns linked to other ransomware threat actor groups, including LockBit Ransomware, Qilin Ransomware, Conti Ransomware, and BlackCat Ransomware. By leveraging low-cost virtual infrastructure offered by hosting providers and bulletproof hosting environments, ransomware operators can deploy command-and-control servers and payload delivery nodes that blend into legitimate hosting environments. This reflects an ongoing shift where ransomware operations increasingly rely on scalable cloud and virtualization infrastructure to distribute malware, obscure attribution, and reduce the likelihood of rapid infrastructure takedowns.
ETLM Assessment:
The use of commercial virtualization platforms for ransomware infrastructure suggests that threat actor groups will continue leveraging legitimate cloud, hosting, and virtual machine services to scale malicious operations. Future campaigns may increasingly automate the rapid deployment of disposable infrastructure across multiple hosting providers, enabling ransomware operators to rotate command-and-control servers and payload delivery systems with minimal operational cost. Additionally, threat actors may exploit configuration weaknesses, template reuse, and automation features within virtualization management platforms to rapidly provision large infrastructure clusters that support malware distribution, staging environments, and data exfiltration. As ransomware ecosystems continue to industrialize their infrastructure operations, defenders may face increasing difficulty distinguishing malicious infrastructure from legitimate cloud workloads.
Hypervisor Vulnerabilities Emerging as Strategic Entry Points for Ransomware Operations
The exploitation of CVE-2025-22225 in ransomware campaigns highlights how attackers are increasingly targeting virtualization infrastructure to gain deeper control over enterprise environments. The vulnerability affects widely deployed platforms, including VMware ESXi and related VMware virtualization products, allowing attackers with privileges in the VMX process to perform arbitrary kernel writes and escape the virtual machine sandbox. According to the Cybersecurity and Infrastructure Security Agency, ransomware actors have now incorporated this flaw into active attacks after it was previously exploited as a zero-day. Research from Huntress also suggests Chinese-speaking threat actors had been chaining VMware vulnerabilities in attacks since early 2024. This activity reflects a broader development in ransomware tradecraft where attackers prioritize hypervisors and virtualization platforms, as compromising these layers can grant control over multiple virtual machines simultaneously, dramatically amplifying the operational impact of ransomware deployment.
ETLM Assessment:
The targeting of virtualization infrastructure suggests that ransomware actors may increasingly focus on hypervisors, cloud orchestration platforms, and centralized infrastructure management systems to maximize attack scale. By compromising the underlying virtualization layer, threat actor groups could potentially encrypt or disrupt multiple virtualized workloads simultaneously, increasing operational leverage during extortion attempts. Additionally, attackers may continue chaining multiple virtualization vulnerabilities, such as sandbox escapes, privilege escalation flaws, and management interface weaknesses, to establish persistent control over enterprise environments. As organizations continue consolidating workloads within virtualized and cloud infrastructures, these platforms will likely remain high-value targets for both financially motivated ransomware actors and advanced intrusion groups seeking broad operational impact.
Based on available public reports, approximately 31% of enterprises are compelled to halt their operations, either temporarily or permanently, in the aftermath of a ransomware onslaught. The ripple effects extend beyond operational disruptions, as detailed by additional metrics:
Impact Assessment
Ransomware remains a major threat to both organizations and individuals, locking critical data and demanding payment for its release. The consequences extend well beyond the ransom, often leading to costly recovery efforts, extended downtime, reputational harm, and potential regulatory fines. Such disruptions can destabilize operations and erode stakeholder trust. Addressing this growing risk demands a proactive cybersecurity posture and stronger collaboration between public and private sectors to build resilience against future attacks.
Victimology
Cybercriminals are increasingly targeting industries that manage vast amounts of sensitive data, ranging from personal and financial information to proprietary assets. Sectors such as manufacturing, real estate, healthcare, FMCG, e-commerce, finance, and technology remain high on the threat radar due to their complex and extensive digital infrastructures. Adversaries strategically exploit vulnerabilities in economically advanced regions, launching well-planned attacks designed to encrypt critical systems and extract significant ransom payments. These operations are calculated to yield maximum financial returns.
Ransomware entering 2026 is no longer a discrete cyber incident but an enduring, multi-stage business threat that blends elements of cybercrime, espionage tradecraft, and economic coercion. The continued separation of access, execution, and extortion, combined with browser-based trust abuse, engineered delivery artifacts, and long-lived access infrastructure, has significantly eroded the effectiveness of exploit-centric and signature-driven defenses. At the same time, the scale and complexity of affiliate-driven operations introduce inherent fragility, creating opportunities for disruption beyond traditional endpoint containment, particularly at the levels of access brokerage, backend infrastructure, and coordination workflows. For organizations, resilience in this environment will depend less on preventing individual intrusions and more on governance readiness, third-party risk management, user interaction telemetry, and executive decision preparedness. As ransomware groups continue to evolve toward stealth, optionality, and psychological leverage, proactive external threat landscape management and cross-functional response planning will be critical to reducing both operational impact and long-term business risk.
Strengthen Cybersecurity Measures: Invest in robust cybersecurity solutions, including advanced threat detection and prevention tools, to proactively defend against evolving ransomware threats.
Employee Training and Awareness: Conduct regular cybersecurity training for employees to educate them about phishing, social engineering, and safe online practices to minimize the risk of ransomware infections.
Incident Response Planning: Develop and regularly update a comprehensive incident response plan to ensure a swift and effective response in case of a ransomware attack, reducing the potential impact and downtime.
Cyber Insurance: Evaluate and consider cyber insurance policies that cover ransomware incidents to mitigate financial losses and protect the organization against potential extortion demands.
Security Audits: Conduct periodic security audits and assessments to identify and address potential weaknesses in the organization’s infrastructure and processes.
Security Governance: Establish a strong security governance framework that ensures accountability and clear responsibilities for cybersecurity across the organization.
Patch Management: Regularly update software and systems with the latest security patches to mitigate vulnerabilities that threat actors may exploit.
Network Segmentation: Implement network segmentation to limit the lateral movement of ransomware within the network, isolating critical assets from potential infections.
Multi-Factor Authentication (MFA): Enable MFA for all privileged accounts and critical systems to add an extra layer of security against unauthorized access.