


CYFIRMA has identified and analyzed a phishing campaign actively targeting organizations through business-related email lures and malicious attachments. The campaign is characterized by its use of invoice, payment, and operational themes designed to blend seamlessly into routine corporate communications. The timing of this activity coincides with the financial year-end period, a phase marked by increased financial reconciliation, vendor payments, and audit-related processes. During this period, employees within finance and procurement functions are more likely to engage with transactional emails, making them prime targets for socially engineered attacks. Current observations indicate that while email content varies across samples, the underlying attack methodology remains consistent, relying on document-based interaction to initiate redirection to credential harvesting infrastructure. This reflects a deliberate strategy to balance evasion and effectiveness, aligning with broader trends in phishing campaigns that emphasize multi-stage delivery and user-driven execution.
CYFIRMA assesses an ongoing and evolving phishing campaign targeting finance and operational functions through invoice-themed social engineering and malicious document attachments. The campaign demonstrates a balance between content variability and technical consistency, enabling evasion of static detection while maintaining effective credential harvesting mechanisms. The observed increase in activity aligns with the financial year-end period, when organizations face higher transaction volumes, vendor reconciliations, and audit-driven processes. This environment increases the likelihood of user interaction with unsolicited financial communications, which threat actors exploit to improve success rates.
Technical analysis highlights a multi-stage attack workflow where document-based payloads act as an intermediary between email delivery and phishing infrastructure. These payloads require user interaction, helping bypass conventional security controls before redirecting users to credential harvesting interfaces that mimic legitimate authentication portals. The campaign also shows operational scalability, with multiple phishing kits sharing similar front-end designs but differing in backend infrastructure. This modular approach allows rapid adaptation, infrastructure rotation, and sustained activity despite defensive measures.
From a risk perspective, the focus on finance and procurement functions increases the likelihood of downstream impacts, including unauthorized access, business email compromise scenarios, and financial fraud. The combination of timing, targeting, and technique underscores a heightened threat posture requiring proactive detection and strengthened controls.
Campaign Overview
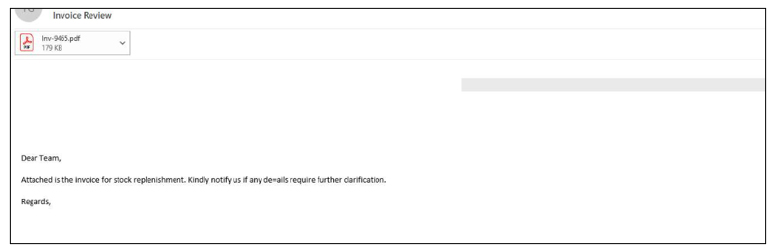
The observed campaign leverages business-oriented pretexts, including invoices, stock replenishment notices, and payment updates, to distribute malicious PDF attachments. Email content varies across samples and is often delivered from external or potentially spoofed domains, enabling evasion of pattern-based detection. The messaging is deliberately crafted to appear routine and operational in nature, increasing the likelihood of user interaction within finance and procurement workflows.
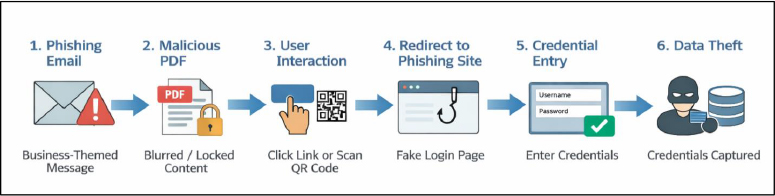
Attack Flow
The attack begins with a phishing email leveraging business-related themes and containing a malicious PDF attachment. Upon opening, the PDF presents blurred or restricted content designed to prompt user interaction. When the user engages with embedded elements such as links or QR codes, they are redirected to a phishing website mimicking a legitimate login portal. The user is then prompted to enter credentials, which are subsequently captured by the attacker.
Initial Access Vector
Phishing emails associated with this campaign employ a range of business-related themes and are designed to blend into routine corporate communications. Rather than relying on a single template, emails exhibit content variability while maintaining consistent social engineering objectives.
Common characteristics include:
Common Email Lure Types:
This variation in email content suggests an effort to evade signature-based detection, while maintaining credibility across different business functions.
Social Engineering Techniques
Payload Analysis
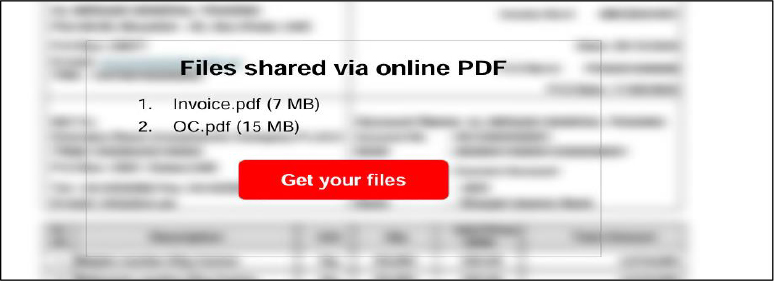
Malicious PDF attachments serve as the primary payload delivery mechanism within the campaign, acting as an intermediary stage between the initial phishing email and credential harvesting infrastructure.
These PDF documents commonly employ visual obfuscation techniques, where content is intentionally blurred, restricted, or partially concealed. Users are prompted to interact with embedded elements such as buttons, hyperlinks, or images to “view,” “unlock,” or access the document.
Upon interaction, these elements initiate redirection to externally hosted phishing pages.
This approach provides multiple advantages to the threat actor:
Overall, the use of PDF-based lures reflects a deliberate shift toward multi-step phishing techniques designed to bypass detection and improve success rates.
QR Code Phishing (Quishing)
Some PDFs include QR codes directing users to phishing sites.
Notable aspects:

Embedded Link Redirection
Credential Harvesting & Phishing Kits
Following redirection from the PDF payload, users are directed to fraudulent login pages designed to harvest credentials. These pages typically mimic legitimate authentication portals, increasing the likelihood of successful compromise.
Analysis of multiple samples indicates the use of distinct phishing kits exhibiting a consistent front-end design but differing in underlying implementation and hosting infrastructure. This includes variations in page structure, script behavior, and data exfiltration mechanisms.
A notable pattern is the reuse of visual templates across different kits, suggesting either shared resources or adaptation of widely available phishing frameworks. At the same time, backend diversity, such as differing domains, hosting providers, and redirection logic, indicates efforts to distribute infrastructure and reduce detection or takedown impact.
This combination of template reuse and infrastructure variation reflects a modular phishing ecosystem, enabling threat actors to rapidly deploy and rotate components while maintaining a consistent user-facing experience.
CYFIRMA’s assessment indicates an ongoing phishing campaign leveraging invoice-themed social engineering combined with PDF-based payload delivery and QR-enabled redirection techniques. The observed use of varied email content, alongside consistent post-delivery exploitation mechanisms, suggests a structured and adaptable threat model designed to evade traditional detection controls. The presence of multiple phishing kits with similar user-facing templates further reflects a modular ecosystem, enabling rapid infrastructure rotation and sustained campaign activity.
From a forward-looking perspective, this campaign is likely to evolve through increased adoption of advanced evasion techniques, including enhanced obfuscation within document payloads and more sophisticated methods for bypassing multi-factor authentication. The continued use of QR-based delivery mechanisms is expected to grow, particularly as organizations strengthen email filtering for conventional phishing links.
In terms of sectoral impact, organizations with high volumes of financial transactions, particularly finance, procurement, and supply chain functions, are expected to remain primary targets. Additionally, industries operating under time-sensitive financial cycles or regulatory deadlines may face elevated risk due to increased susceptibility to urgency-based social engineering. The campaign aligns with broader trends indicating a shift toward multi-stage phishing operations that prioritize stealth, user interaction, and credential compromise over traditional malware delivery.
| Tactic | Technique ID | Technique Name |
| Initial Access | T1566.001 | Phishing: Spear phishing Attachment |
| Initial Access | T1566.002 | Phishing: Spear phishing Link |
| Initial Access | T1189 | Drive-by Compromise |
| Execution | T1204.002 | User Execution: Malicious File |
| Credential Access | T1556 | Modify Authentication Process |
| Credential Access | T1056.003 | Input Capture: Web Portal Capture |
| Credential Access | T1110 | Brute Force (if observed, optional) |
| Defense Evasion | T1036 | Masquerading |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Collection | T1056 | Input Capture |
| Credential Access | T1621 | Multi-Factor Authentication Request Generation |
The analyzed campaign reflects a structured and adaptable phishing operation that leverages business-context lures and document-based payloads to facilitate credential compromise. By combining variability in email delivery with consistent post-interaction mechanisms, threat actors are able to bypass traditional detection approaches and maintain effectiveness across diverse targets and organizational environments. This balance between evasion and consistency highlights a deliberate strategy to maximize user engagement while minimizing detection.
The use of modular phishing infrastructure and evolving delivery techniques indicates a sustained threat capability with the potential for continued adaptation. The ability to reuse front-end templates while rotating backend components allows threat actors to maintain operational continuity even when parts of the infrastructure are identified or taken down. Given the alignment with high-activity financial periods and the focus on roles with access to sensitive financial processes, the campaign presents a significant risk to organizational security and financial integrity, particularly in environments with high transaction volumes and time-sensitive operations.
To mitigate the risks associated with this campaign, organizations should implement a combination of technical controls and user-focused measures:
Email & Attachment Security
Identity & Access Controls
Network & Web Protection
User Awareness & Training
Monitoring & Response