


The CYFIRMA Industry Report delivers original cybersecurity insights and telemetry-driven statistics of global industries, covering one sector each week for a quarter. This report focuses on the manufacturing industry, presenting key trends and statistics in an engaging infographic format.
Welcome to the CYFIRMA infographic industry report, where we delve into the external threat landscape of the manufacturing industry over the past three months. This report provides valuable insights and data-driven statistics, delivering a concise analysis of attack campaigns, phishing telemetry, and ransomware incidents targeting the manufacturing industry.
We aim to present an industry-specific overview in a convenient, engaging, and informative format. Leveraging our cutting-edge platform telemetry and the expertise of our analysts, we bring you actionable intelligence to stay ahead in the cybersecurity landscape.
CYFIRMA provides cyber threat intelligence and external threat landscape management platforms, DeCYFIR and DeTCT, which utilize artificial intelligence and machine learning to ingest and process relevant data, complemented by manual CTI research.
For the purpose of these reports, we leverage the following data from our platform. These are data processed by AI and ML automation, based on both human research input and automated ingestions.
Each attaLeveraging our Early Warning platform data set, we present known attack campaigns conducted by known advanced persistent threat actors, both nation-state and financially motivated.
ck campaign may target multiple organizations across various countries.
Campaign durations can vary from weeks to months or even years. They are sorted by the “last seen” date of activity to include the most relevant ones. Note that this may result in campaigns stacking up on later dates, affecting time-based trends.
Attribution to specific threat actors can be murky due to increasingly overlapping TTPs and commodity tools used. While suspected threat actors in this report are attributed with high confidence, we acknowledge the potential for inaccuracy.
Our data focuses on phishing campaigns rather than individual phishing or spear-phishing emails, which may limit visibility into more advanced single-target attacks.
Our primary focus is on detecting brand impersonation over intended targets. Due to our collection methodology and automation, we may not present comprehensive victimology for phishing campaigns across all industries, as some are simply not good phishing lures.
Our data on victims in this report is directly collected from respective ransomware blogs, though some blogs may lack detailed victim information beyond names or domains, impacting victimology accuracy during bulk data processing.
In some cases, there are multiple companies that share the same name but are located in different countries, which may lead to discrepancies in geography and industry. Similar discrepancies occur with multinational organizations where we are not able to identify which branch in which country was actually compromised. In such a case, we count the country of the company’s HQ.
During the training of our processing algorithms, we manually verified results for industry and geography statistics at an accuracy rate of 85% with a deviation of ±5%. We continuously fine-tune and update the process.
Data related to counts of victims per ransomware group and respective dates are 100% accurate at the time of ingestion, as per their publishing on the respective group’s blog sites.
Finally, we acknowledge that many victims are never listed as they are able to make a deal with the attackers to avoid being published on their blogs.
Manufacturing organizations featured in 5 out of the 20 observed campaigns, which is a presence in 25% of campaigns.
Observed Campaigns per Month
The monthly chart shows consistent moderate detections throughout the months.
Suspected Threat Actors

Majority of the detections are associated with the APT41 nexus, collectively tracked as Mission2025. Additionally, we have observed Leviathan; another Chinese group operating in the Middle East, as well as the Russian Cozy Bear and an unidentified English-speaking group with victims in China, Russia, KSA and UAE.
GEOGRAPHICAL DISTRIBUTION
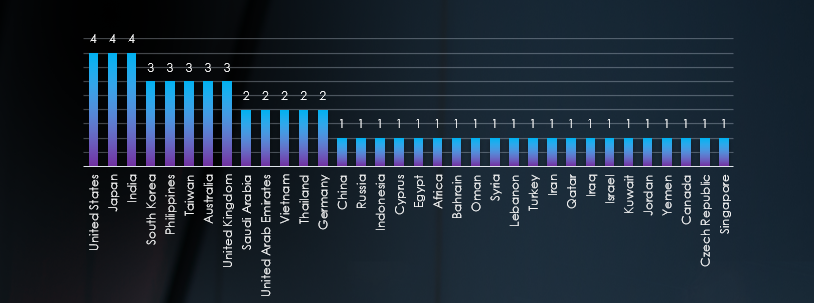
Recorded victims of observed attack campaigns span 34 different countries, with the US, Japan, and India having the highest number of victims in campaigns targeting the manufacturing industry, which correlates with the respective sizes of industry. Despite Leviathan APT having only one detected campaign, its presence extends across the entire Middle East region.
TOP ATTACKED TECHNOLOGY
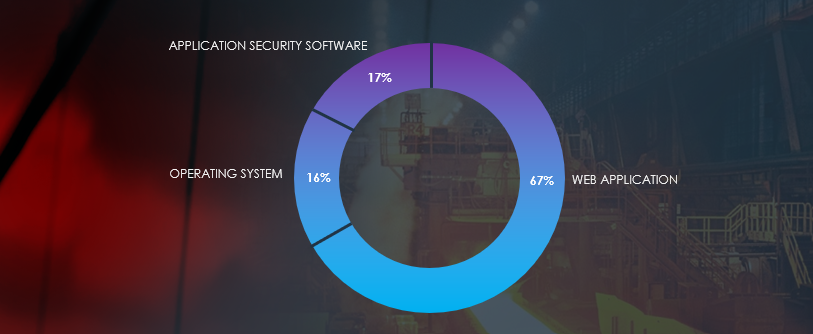
Attack campaigns focused on Web Applications, Operating Systems and Application Security Software.
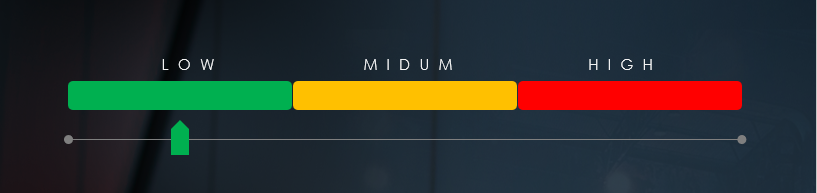
Risk Level Indicator: Medium

In the past 90 days, the manufacturing industry has maintained a moderate level of risk, although the overall share fell from 50% to 25%. Key threat actors in this sector include Chinese APT41-nexus (tracked as Mission2025), Mustang Panda, Stone Panda, and Leviathan. Despite Leviathan’s activity being counted as a single campaign, it has been detected across the entire Middle East region. Russian activity in the manufacturing sector appears to have slowed down, with a single detection by Cozy Bear. Additionally, we observed a campaign by an unknown English-speaking group with victims in China, Russia, Saudi Arabia, and the United Arab Emirates.
Overall, the most targeted regions were the US, Japan, and India, aligning with the sizes of their respective manufacturing industries. In addition to traditionally targeted Western countries, there is a noteworthy and growing presence in the APAC region, correlating with Chinese strategic interests.
Web applications continue to be the most frequently targeted technology across various industries, closely followed by operating systems in terms of susceptibility and Application Security Software bypassing.
Over the past 3 months, CYFIRMA’s telemetry recorded only 9 phishing campaigns out of a total of 333,072 that impersonated the manufacturing industry organizations.
Observed manufacturing-related phishing themes equal to 0.002% and as such are not being tracked as a category.
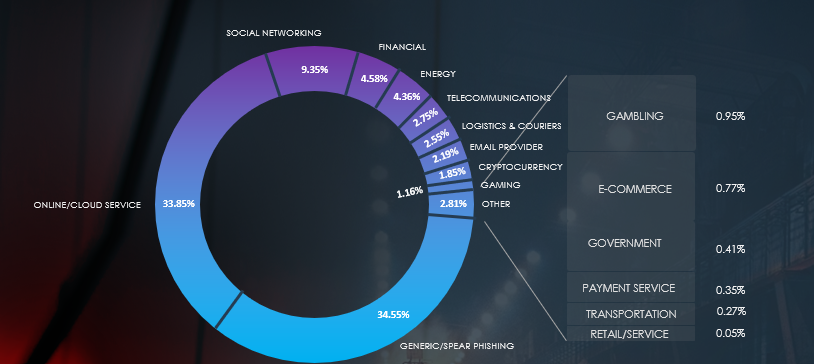
Global Distribution of Phishing Themes per Sector
Top Impersonated Brands
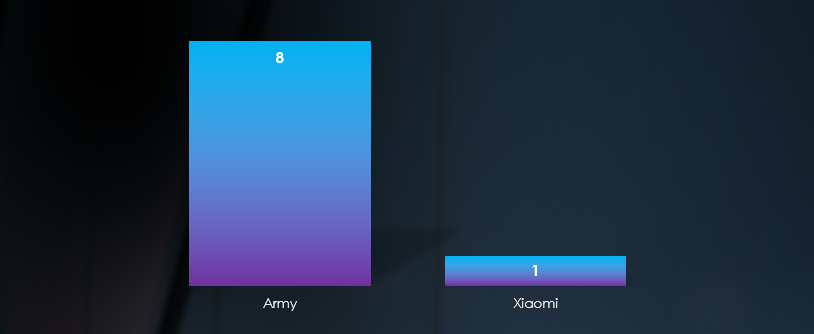
Only one manufacturing brand, Xiaomi, was observed in impersonation campaigns. However, a manual review of the logs identified eight campaigns impersonating the military, utilizing the .army top-level domain (TLD) and matching aerospace & defense heuristic filters, which can be considered within the scope of manufacturing.
Top Countries of Origin based on ASN
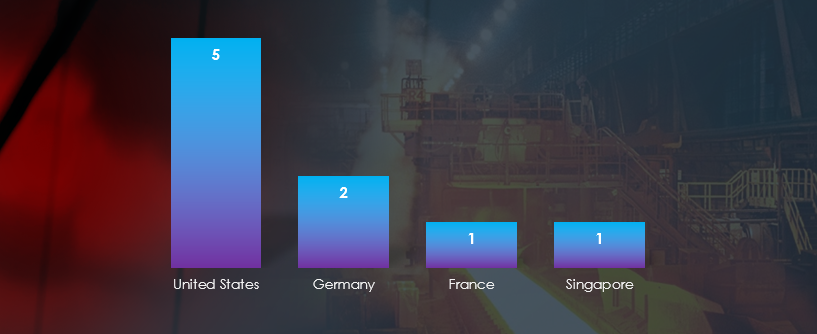
ASN origin of observed campaigns note the US, Germany and France as sources of the Army themes phishing and Singapore as the origin for Xiaomi impersonation.
Risk Level Indicator: Low
Excluding spear-phishing attacks by geopolitically motivated APTs and ransomware affiliates, the manufacturing industry is generally not considered an attractive lure or target for phishing campaigns for several reasons. Primarily, the nature of their operations involves specialized machinery, production processes, and proprietary technologies that are challenging to understand and may not be as valuable or easily monetizable for cybercriminals, when compared to other sectors like finance or healthcare.
Furthermore, manufacturing companies typically have less direct access to high-value personal or financial information that cybercriminals typically target, such as credit card data or social security numbers. This limitation reduces the potential rewards for phishing attacks on these organizations. The absence of extensive customer databases in manufacturing can also act as a deterrent for cybercriminals, as they often prefer sectors with more substantial troves of personal information to exploit.
In the past 90 days, CYFIRMA has identified 155 verified ransomware victims within the manufacturing industry sectors, excluding automotive for a standalone report. This accounts for 14.3% of the overall total of 1,086 ransomware incidents during the same period.
The Monthly Activity Chart
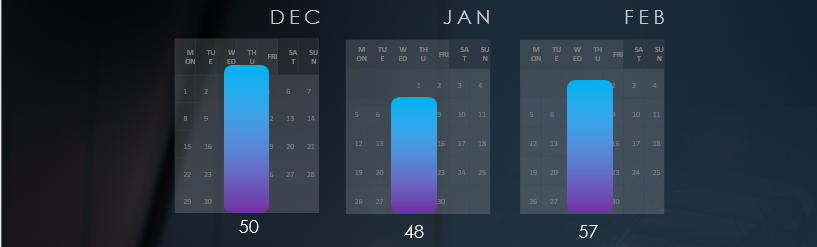
The monthly activity chart shows consistently high numbers across months, without a clear trend.
Breakdown of Monthly Activity by Gangs
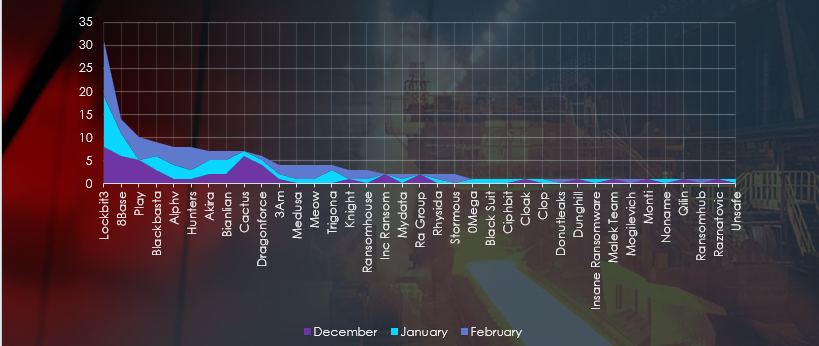
A breakdown of the monthly activity provides insights into per-group activity. For example, LockBit3 was highly active across months, whereas Cactus recorded most victims in December.
Ransomware Victims in the Manufacturing Industry per Group
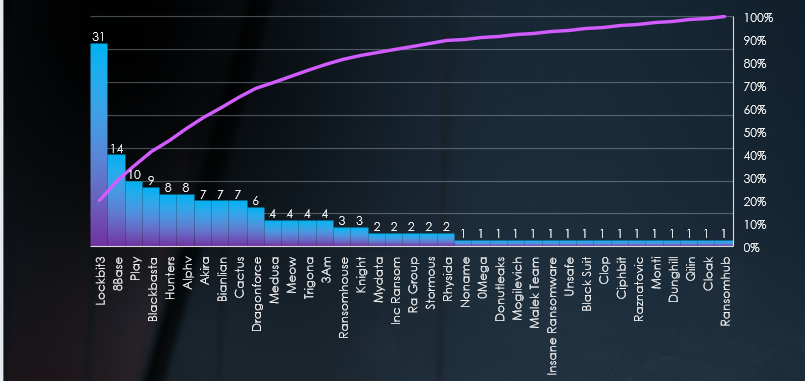
In total 37 out of 53 active groups recorded manufacturing organization victims in the past 90 days. The top 5 are responsible for half of them.
Comparison to All Ransomware Victims by Group
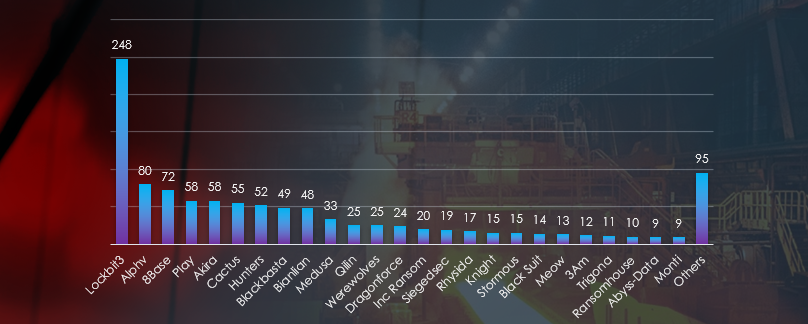
Comparing the manufacturing industry to all victims recorded, we can see for example 8base and Play with a relatively high share of manufacturing industry victims (19.4% and 17.2% respectively), suggesting high focus.
Geographic Distribution of Victims
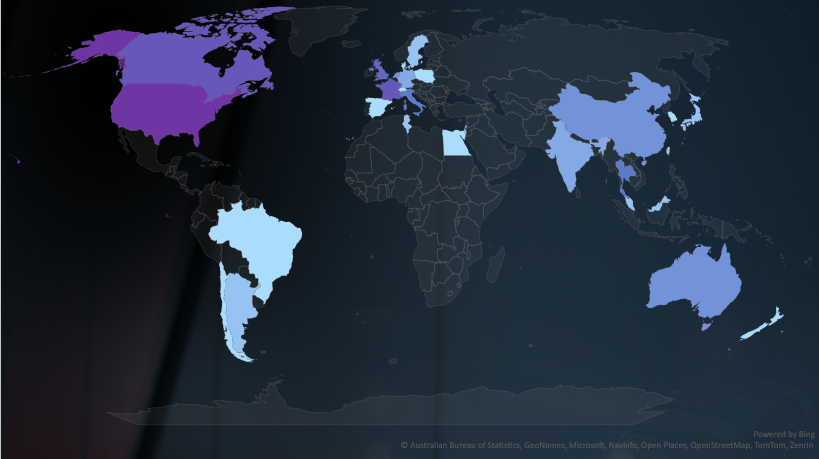
The heatmap of geographic distribution shows a truly global reach of ransomware.
Total Victims per Country
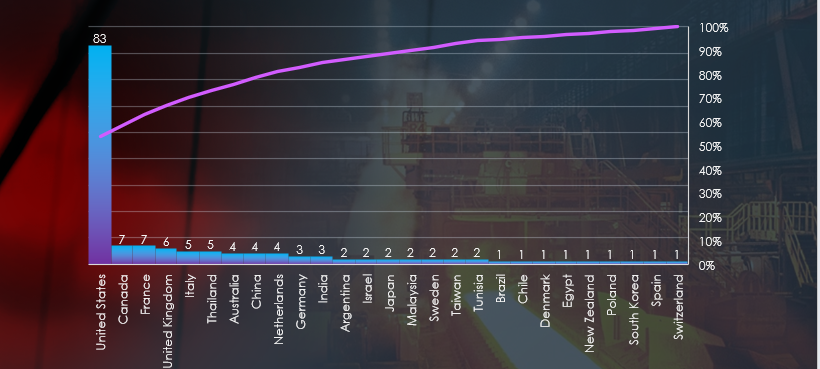
In total 27 countries recorded ransomware victims with the US alone accounting for ~54% of all victims with identified geography.
Sectors Distribution
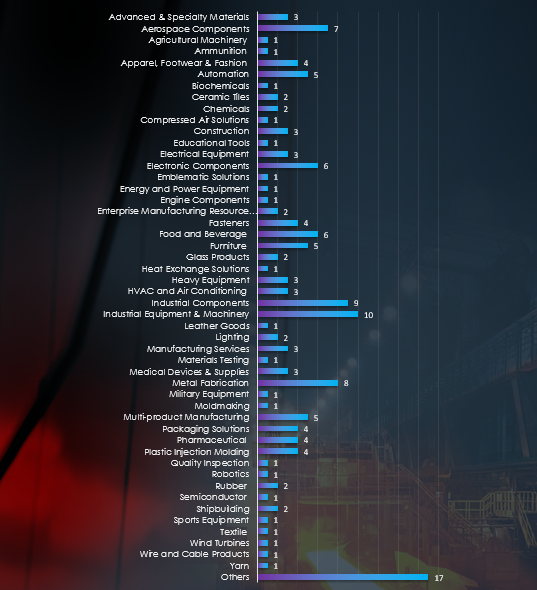
Listing consolidated sectors falling under the manufacturing industry umbrella reveals that industrial components, equipment, and machinery, along with metal fabrication, are the most attacked sectors. Additionally, we see a diverse range of impacted sectors, including various niches.
Risk Level Indicator: High

The manufacturing industry currently bears the highest brunt of ransomware attacks, accounting for 14.3% of all victims in the last 90 days, marking an increase from the previous 11.5% share. Despite an overall decrease in the number of manufacturing businesses affected (189 to 155) and a decline in total ransomware victims (1,641 to 1,086), monthly activity showcases a consistent volume of victims with no discernible trends.
Breaking down the victimology by ransomware group, LockBit3 emerges as the most active, responsible for 20% of the total 155 victims. Furthermore, the 8base and Play gangs show a notable focus on the manufacturing sector, representing 19.4% and 17.2% of their respective total victims.
The trend of high involvement from mid to small-sized ransomware groups continues, with 37 out of 53 active groups in the last 90 days having victims in this industry—a trend initiated in September of the previous year.
Analyzing the 155 victims across 27 different countries, the United States bears the highest impact with 83 victims (54% of all), followed by Canada and France, each with 7 victims.
Examining specific sectors within manufacturing reveals that Industrial Components, Equipment and Machinery manufacturing, along with metal fabrication, are the most severely impacted.
For a comprehensive, up-to-date global ransomware tracking report on a monthly basis, please refer to our new monthly “Tracking Ransomware” series here.
In the manufacturing industry’s external threat landscape, we observe mixed risk factors.
The presence of manufacturing businesses in observed Advanced Persistent Threat (APT) campaigns has decreased from 50% to 25%. However, despite this decline, we maintain a moderate risk factor. A detailed analysis reveals a reduced number of tracked campaigns, yet the activity within those campaigns remains notably high. The majority of detections are attributed to Chinese APT41-nexus (Mission2025), Mustang Panda, Stone Panda, and Leviathan. The latter is particularly active across the entire Middle East region. Additionally, we identified a campaign conducted by an unknown English-speaking group, targeting China, Russia, Saudi Arabia, and the United Arab Emirates.
Phishing remains a low risk in the manufacturing industry. The intricacies of manufacturing operations and the absence of easily monetizable data make it an unsuitable theme for broad phishing campaigns. Manufacturing businesses generally lack direct access to high-value personal or financial information, and their customer databases are typically limited.
Ransomware remains a high threat, with manufacturing organizations accounting for over 14.5% of all victims in the last 90 days. Most active groups include LockBit3, 8base and Play. However, participation by small to mid-sized groups adds up to a substantial share of all victims as well. The US is by far the most targeted with 83 victims, followed by Canada and France (7 each).