


The CYFIRMA Industry Report delivers original cybersecurity insights and telemetry-driven statistics of global industries, covering one sector each week for a quarter. This report focuses on the consumer goods & services industry, presenting key trends and statistics in an engaging infographic format.
Welcome to the CYFIRMA infographic industry report, where we delve into the external threat landscape of the consumer goods & services industry over the past three months. This report provides valuable insights and data-driven statistics, delivering a concise analysis of attack campaigns, phishing telemetry, and ransomware incidents targeting the consumer goods & services industry.
We aim to present an industry-specific overview in a convenient, engaging, and informative format. Leveraging our cutting-edge platform telemetry and the expertise of our analysts, we bring you actionable intelligence to stay ahead in the cybersecurity landscape.
CYFIRMA provides cyber threat intelligence and external threat landscape management platforms, DeCYFIR and DeTCT, which utilize artificial intelligence and machine learning to ingest and process relevant data, complemented by manual CTI research.
For the purpose of these reports, we leverage the following data from our platform. These are data processed by AI and ML automation based on both human research input and automated ingestions.
While this report contains statistics and graphs generated primarily by automation, it undergoes thorough review and enhancement for additional context by CYFIRMA CTI analysts to ensure the highest quality and provide valuable insights.
Consumer goods & services organizations featured in 5 out of the 10 observed campaigns, which is a presence in 50% of campaigns.
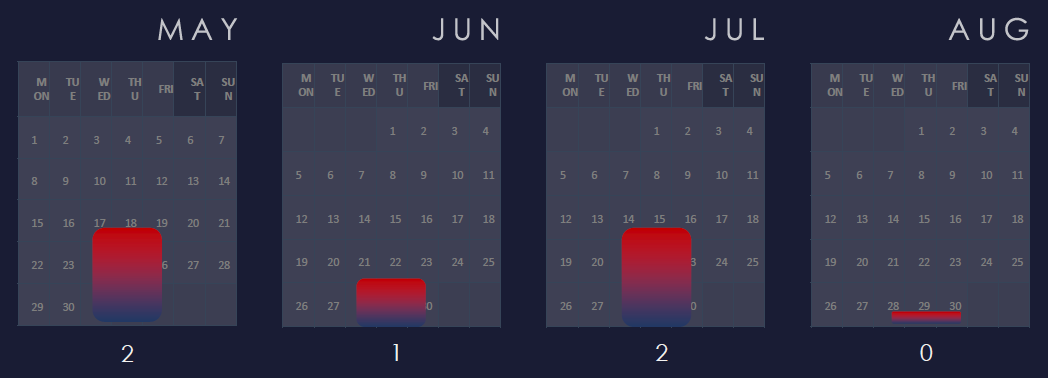
We are observing a moderate, but sustained interest in last 90 days.
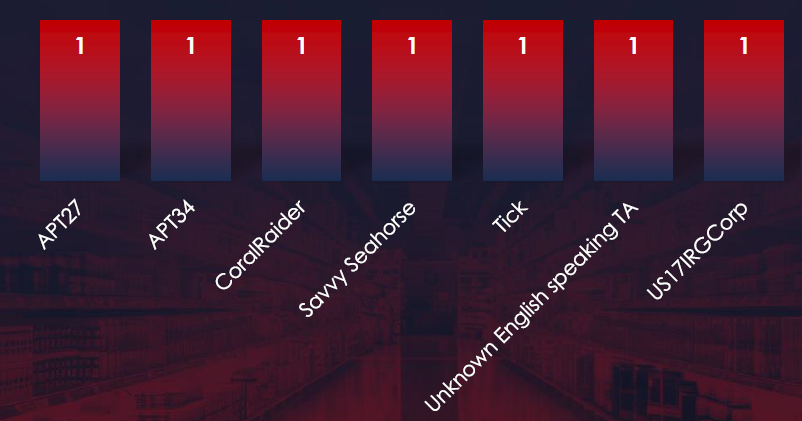
The 5 observed campaigns were carried out by a wide variety of threat actors, including APT27 and Tick from China, APT34 and US17IRGCorp from Iran, and CoralRaider from Vietnam.
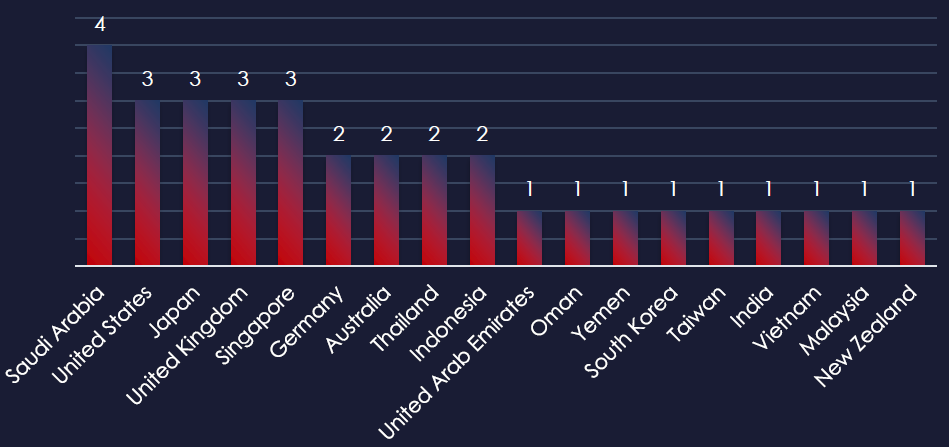
Recorded victims of observed attack campaigns span 18 different countries. Kingdom of Saudi Arabia recorded victims in 4 observed campaigns. The US, Japan, UK, and Singapore were hit by 3 out of 5 observed campaigns.
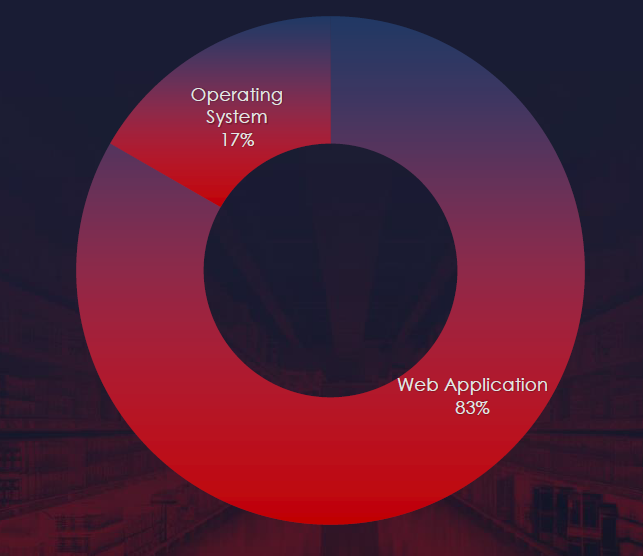
Web applications continue to rank as the most targeted technology across industries. Additionally, compromises were observed in operating systems.
EXTERNAL THREAT LANDSCAPE MANAGEMENT (ETLM) OVERVIEW
Risk Level Indicator: Moderate

In the past 90 days, consumer goods & services organizations have been significantly impacted by advanced persistent threat (APT) campaigns. Notably, 50% of observed APT campaigns targeted the consumer goods & services sectors, with 5 out of 10 total campaigns affecting this industry.
Monthly Trends
An analysis of monthly trends shows moderate but sustained interest over time.
Key Threat Actors
There were no single outstanding threat actors, but both China and Iran-linked groups had their hand in two campaigns.
Geographical Impact
The campaigns impacted a total of 18 countries, with Saudi Arabia being hit by 4 out of 5 observed campaigns. Other significantly affected countries included the United States, Japan the United Kingdom, and Singapore. Overall geographical spread correlates with the broad strategic interests of involved nation-states linked to these threat actors.
Targeted Technologies
Web applications emerged as the most targeted technology within these campaigns.
Over the past 3 months, CYFIRMA’s telemetry detected 6,308 phishing campaigns themed around the consumer goods & services industry out of a total of 215.
The chart below illustrates the global distribution of observed themes. Combined e-Commerce, Gambling, and Retail/Service account for 2.92% of all captured phishing attempts.
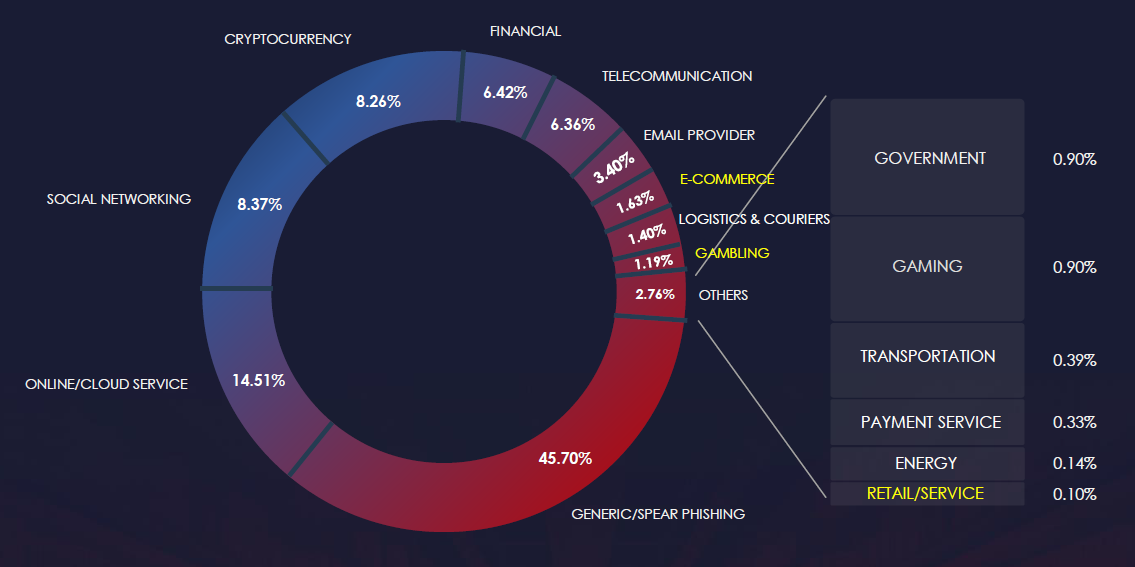
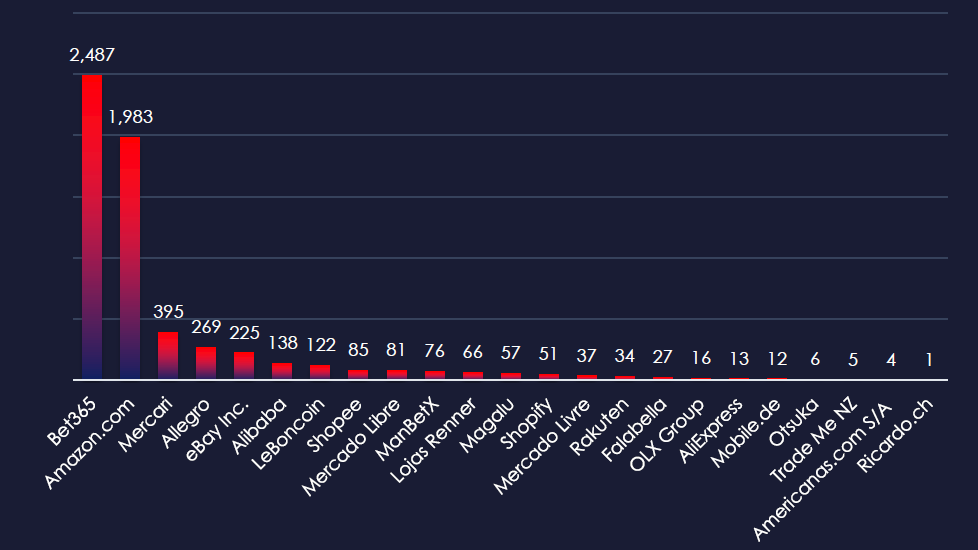
Prominent betting platform Bet365 and Amazon e-Commerce are the by far the most impersonated brands. Various other international and regional platforms are also represented.
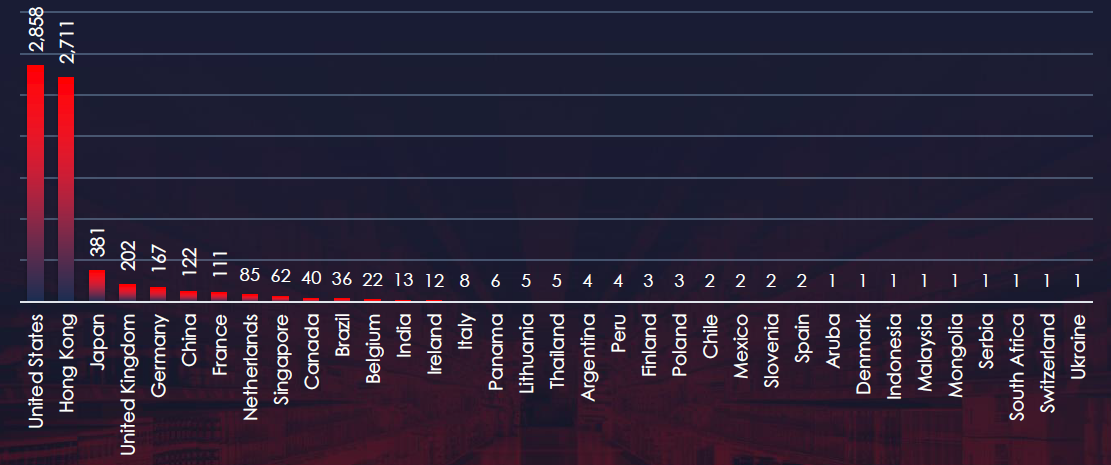
The geographical sources of observed phishing campaigns show that most of it comes from the US and Hong Kong.
Risk Level Indicator: Moderate
Some sectors of the consumer goods & services industry remain popular phishing themes. Specifically, e-commerce and gambling for obvious reasons – there is money to be made directly by threat actors.
Bet365 stands out as the most frequently exploited platform for phishing. Following this, Amazon is also significantly impersonated.
Overall, the list includes 23 organizations from 35 countries. Many international and regional platforms are being impersonated.
ASN-origin data reveals that the United States is the leading source of phishing emails impersonating information technology organizations, reflecting the sheer size of the market in the U.S. and the vast number of compromised devices used in botnets to send phishing emails. Significant activity has also been observed in Hong Kong.
Southeast Asia, Latin America, and even Africa are steadily growing as sources and targets of phishing.
The presence in both developed and developing nations highlights that phishing campaigns are opportunistic and globally pervasive.
In the past 90 days, CYFIRMA has identified 143 verified ransomware victims in the consumer goods & services industry. This accounts for 11.2% of the overall total of 1,281 ransomware victims during the same period.
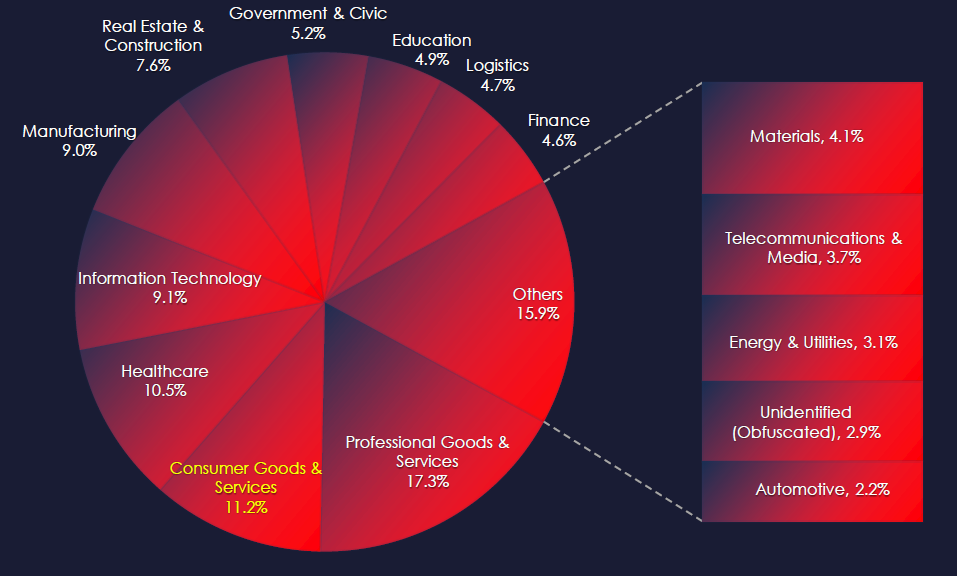

Food & Beverage by far are the most frequent victims of ransomware in consumer goods & services industry.
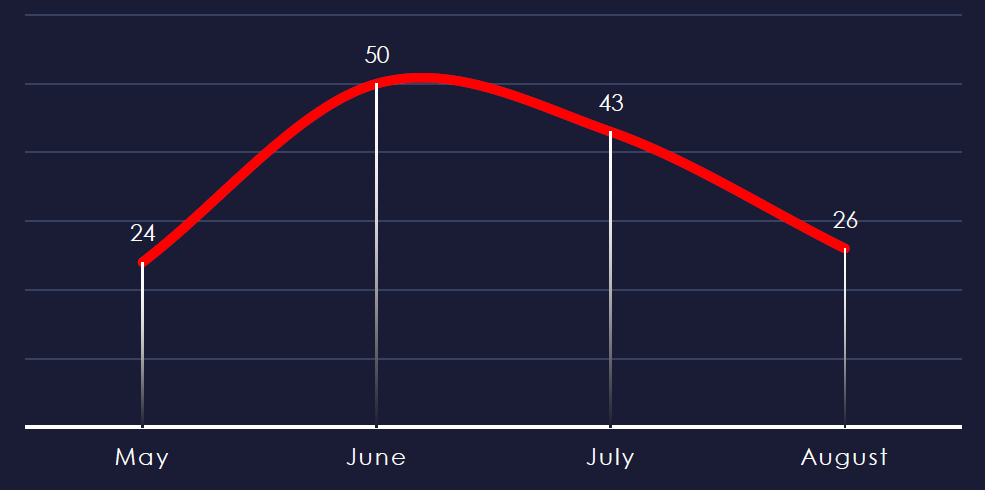
Considering May and August are equally split in half at the time of collection, we can see sustained and consistent numbers across the months.
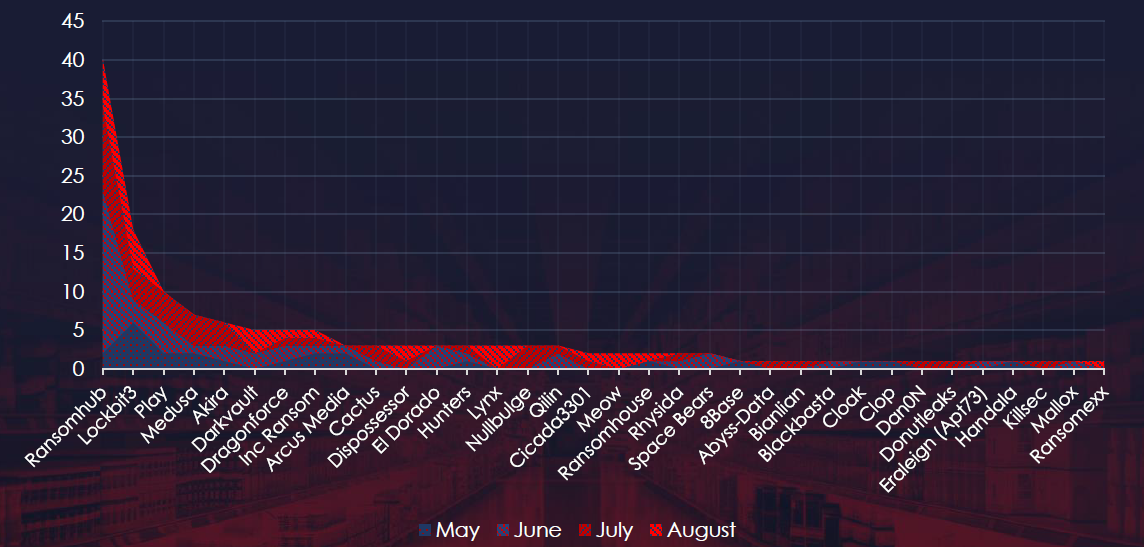
A breakdown of the monthly activity provides insights into which gangs were active each month. For example, RansomHub recorded a large number of victims in June. LockBit3 came back in May after law enforcement disruption. Lynx and Meow have victims only in August.
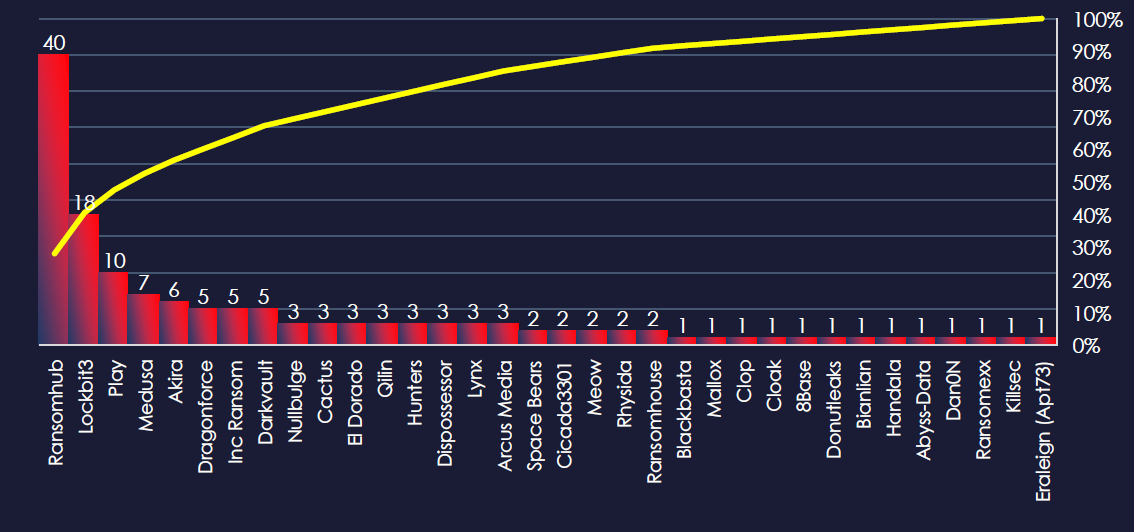
In total 34 out of 61 active groups recorded consumer goods & services organizations victims in the past 90 days.
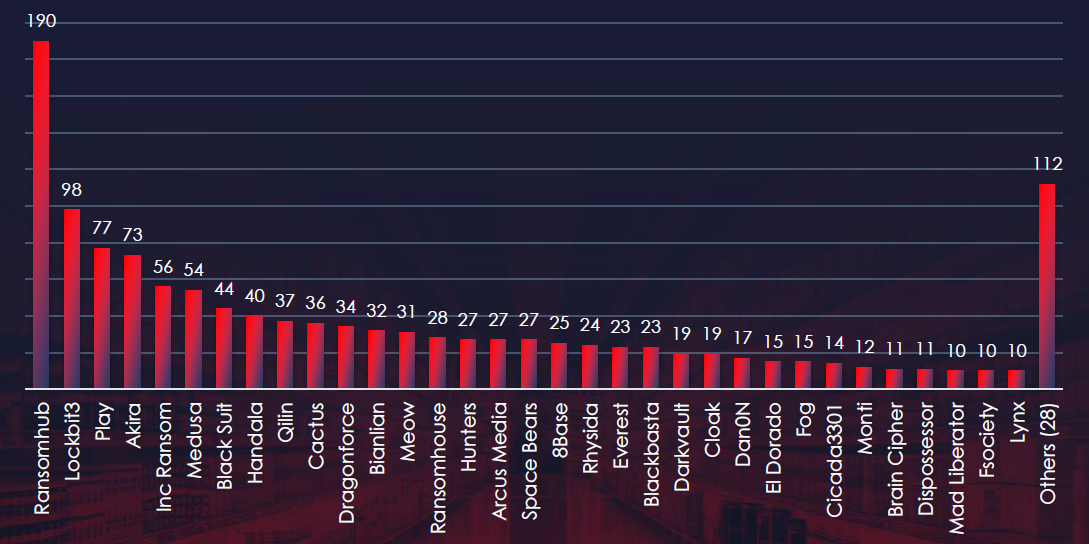
Comparing the consumer goods & services industry to all recorded victims, none of the gangs particularly stand out with a high percentage of victims in this industry. The highest is the most active RansomHub with 40 out of 190 (21%) victims.
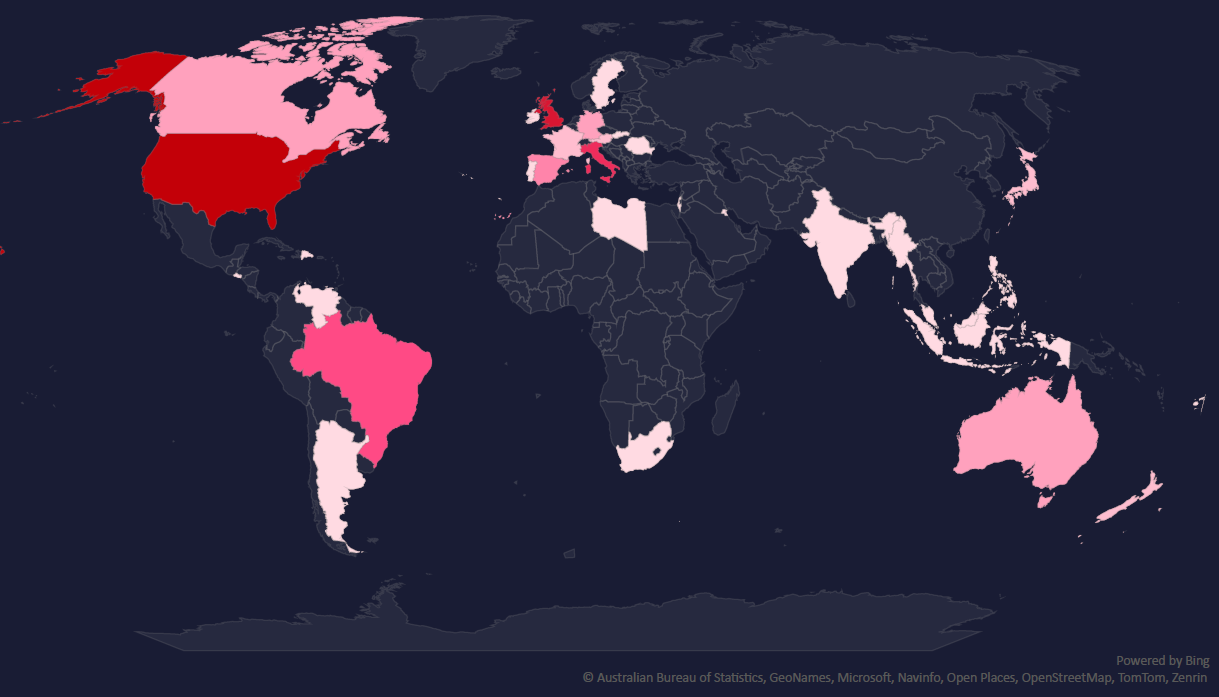
The geographic distribution heatmap underscores the widespread impact of ransomware, highlighting the countries where victims in this industry have been recorded.
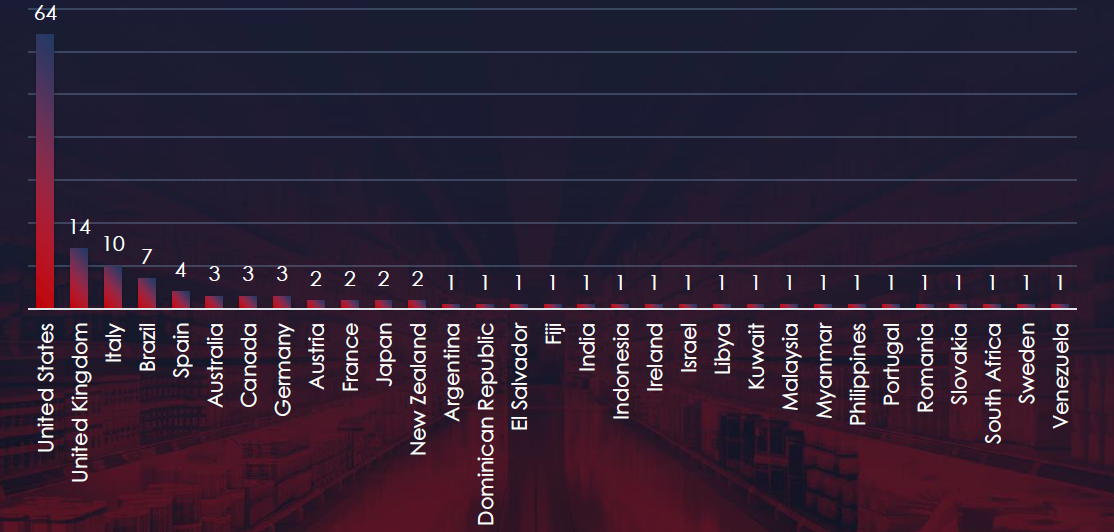
In total 31 countries recorded ransomware victims with the US alone accounting for ~47% of all victims with identified geography.
Risk Level Indicator: Moderate

The consumer goods & services industry ranked 2nd in terms of the number of victims. However, we maintain an overall moderate risk simply due to the sheer number of small and medium businesses in this industry.
That said, Food & Beverages, major Retailers, and Fashion & Apparel brands warrant a high-risk factor as they are among the most frequent victims in this industry.
Monthly Activity Trends
Ransomware activity in the consumer goods & services industry has shown steady numbers of victims each month, with a minor uptick during June.
This uptick is due to the RansomHub gang spree in the same month.
Ransomware Gangs
A total of 34 out of 61 active ransomware groups targeted this industry in the past 90 days:
RansomHub: Responsible for 28% of all consumer goods & services victims, and 21% of their victims were in this industry (40 out of 190 victims), implying a significant interest.
No other gang seems to stand out.
Geographic Distribution
The geographic distribution of ransomware victims in the consumer goods & services industry highlights the widespread nature of these attacks:
47% of all victims with identified geography are located in the US. The UK and Italy also appear to be frequently targeted in this sector in the last 90 days with 14 and 10 victims respectively.
In total, 31 countries reported ransomware victims in this industry.
For a comprehensive, up-to-date global ransomware tracking report, please refer to our new monthly “Tracking Ransomware” series here.
In the past 90 days, consumer goods & services organizations have faced moderate to high risk across monitored categories.
APT campaigns present a moderate risk to the consumer goods & services industry, with 50% of observed APT campaigns in the past 90 days targeting this sector. The consistent interest over time, particularly with 5 out of 10 campaigns affecting this industry, indicates a sustained threat level.
Notable involvement from threat actors linked to China and Iran has driven these campaigns, which have impacted a wide geographical area, including Saudi Arabia (hit by 4 out of 5 campaigns), the United States, Japan, the United Kingdom, and Singapore. The primary attack vectors involve web applications, emphasizing the focus on critical online infrastructures within the industry.
In Phishing, the consumer goods & services sector also faces a moderate risk level. Despite the large volume of attempts, the sector remains a popular theme for phishing, especially in the e-commerce and gambling sectors. Bet365 stands out as the most frequently exploited platform, followed by Amazon.
The phishing campaigns are globally pervasive, with 23 organizations across 35 countries being impersonated. The United States has emerged as the leading source of phishing emails, reflecting the size and scope of the IT market there. Notably, Southeast Asia, Latin America, and Africa are becoming increasingly active, both as sources, and targets of phishing, demonstrating the opportunistic nature of these attacks.
Ransomware risk in the consumer goods & services industry is considered moderate, with the industry ranking 2nd overall in terms of the number of victims. However, the Food & Beverage, Retail, and Fashion & Apparel sectors warrant a high risk as the most frequent victims.
The RansomHub gang, responsible for 28% of all victims in this industry, significantly contributed to the activity, with 40 out of their 190 victims coming from this sector. While other ransomware groups are active, none stand out to the same extent. The geographical distribution of ransomware victims is widespread, with 47% of identified victims located in the US, followed by the UK and Italy, with 14 and 10 victims respectively. This distribution highlights the broad, yet concentrated, nature of these attacks.