


The CYFIRMA Industries Report delivers original cybersecurity insights and telemetry-driven statistics of global industries, covering one sector each week for a quarter. This report focuses on the finance industry, presenting key trends and statistics in an engaging infographic format.
Welcome to the CYFIRMA infographic industry report, where we delve into the external threat landscape of the finance industry over the past three months. This report provides valuable insights and data-driven statistics, delivering a concise analysis of attack campaigns, phishing telemetry, and ransomware incidents targeting finance industry.
We aim to present an industry-specific overview in a convenient, engaging, and informative format. Leveraging our cutting-edge platform telemetry and the expertise of our analysts, we bring you actionable intelligence to stay ahead in the cybersecurity landscape.
CYFIRMA provides cyber threat intelligence and external threat landscape management platforms, DeCYFIR and DeTCT, which utilize artificial intelligence and machine learning to ingest and process relevant data, complemented by manual CTI research.
Include that we are only presenting verified data, no extrapolation, simulation or estimates
For the purpose of these reports, we leverage the following data from our platform. These are data processed by AI and ML automation based on both human research input and automated ingestions.
Leveraging our Early Warning platform data set, we present known attack campaigns conducted by known advanced persistent threat actors. Both nation-state and financially motivated.
Each attack campaign may target multiple organizations across various countries.
Campaign durations can vary from weeks to months or even years. They are sorted by the “last seen” date of activity to include the most relevant ones. Note that this may result in campaigns stacking up on later dates, affecting time-based trends.
Attribution to specific threat actors can be murky due to increasingly overlapping TTPs and commodity tools used. The suspected threat actors in this report are attributed with varying levels of confidence not shown in this report to keep it concise. However, we acknowledge the potential for inaccuracy.
Our data focuses on phishing campaigns rather than individual phishing or spear-phishing emails, which may limit visibility into more advanced single-target attacks.
Our primary focus is on detecting brand impersonation over intended targets. Due to our collection methodology and automation, we may not present comprehensive victimology for phishing campaigns across all industries as some are simply not good phishing lures.
Our data on victims in this report is directly collected from respective ransomware blogs, though some blogs may lack detailed victim information beyond names or domains, impacting victimology accuracy during bulk data processing.
In some cases, there are multiple companies that share the same name but are located in different countries, which may lead to discrepancies in geography and industry. Similar discrepancies occur with multinational organizations where we are not able to identify which branch in which country was actually compromised. In such a case, we count the country of the company’s HQ.
During the training of our processing algorithms, we manually verified results for industry and geography statistics at an accuracy rate of 85% with a deviation of ±5%. We continuously fine-tune and update the process.
Data related to counts of victims per ransomware group and respective dates are 100% accurate at the time of ingestion, as per their publishing on the respective group’s blog sites.
Finally, we acknowledge that many victims are never listed as they are able to make a deal with the attackers to avoid being published on their blogs.
While this report contains statistics and graphs generated primarily by automation, it undergoes thorough review and enhancement for additional context by CYFIRMA CTI analysts to ensure the highest quality and provide valuable insights.
Financial organizations featured in 19 out of the 28 observed campaigns, which is a presence in 67% of campaigns.
Observed Campaigns per month
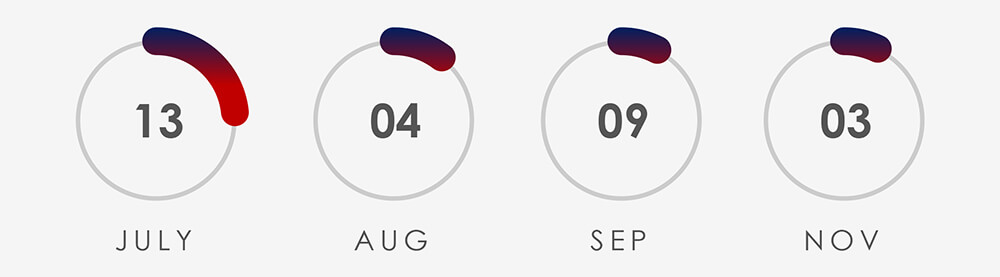
The monthly chart shows a significant drop in active campaigns since the spike in July.
Suspected Threat Actors
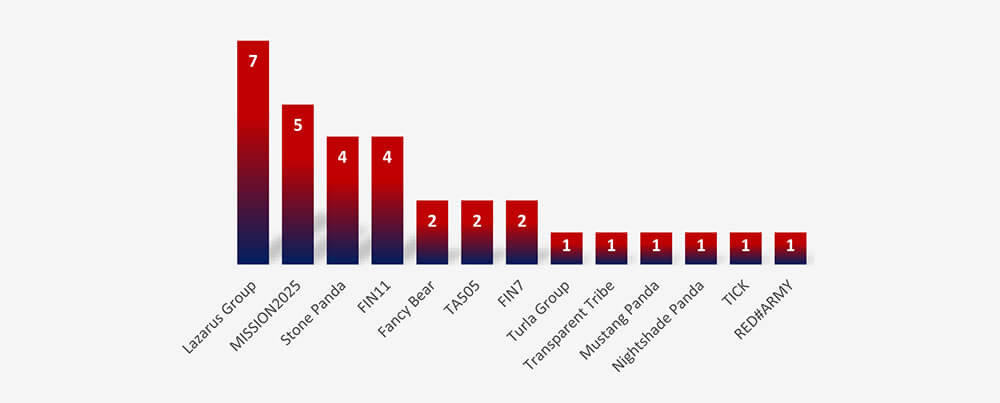
Accounting for overlaps between Mission2025 and Stone Panda, financially motivated threat actors, including Lazarus Group are behind the most active campaigns in the finance industry.
GEOGRAPHICAL DISTRIBUTION
Europe is again taking the lead as the most attacked region. Our hypothesis is related to Russian linked threat actors aiming at energy utilities in relation to war with Ukraine.
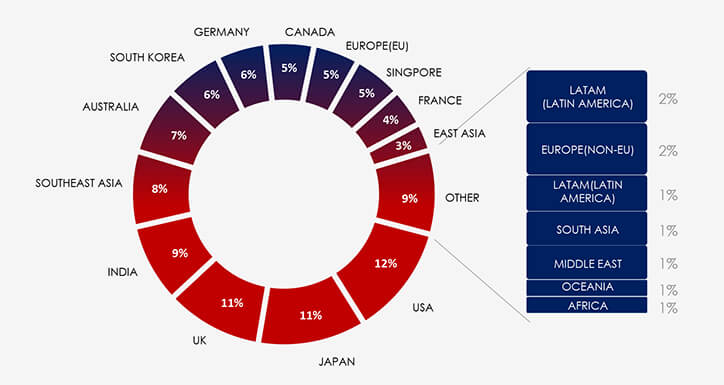
Note: Due to the overlapping nature of monitoring telemetry, further breakdown beyond the top 10 countries is calculated for regions rather than individual countries to maintain clarity.
The USA, Japan, UK and India are taking nearly even lead among the most attacked countries.
TOP ATTACKED TECHNOLOGY
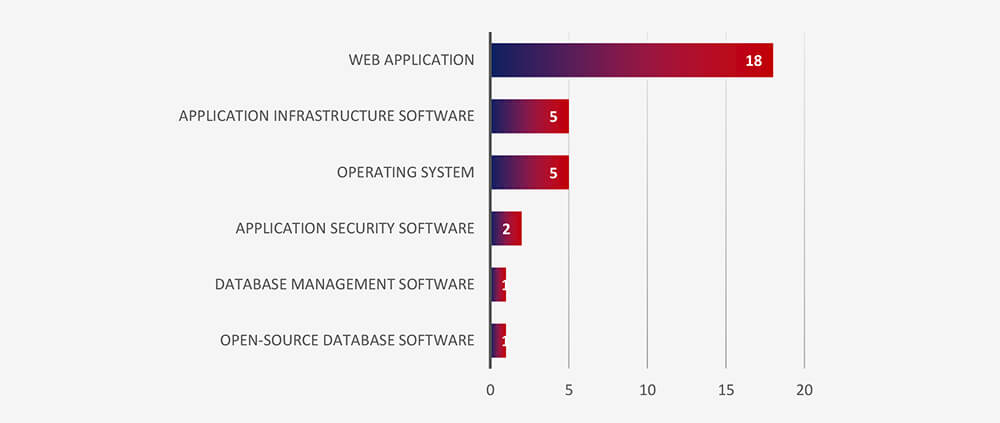
Web applications continue to be the most attacked technology across industries.
Risk Level Indicator : High
Monthly activity exhibited a significant surge in July, predominantly driven by heightened engagement from the Lazarus Group, directly linked to the discovery of MagicRAT and QuiteRAT. Concurrently, there was an upswing in Chinese cyber activity, leveraging the Barracuda ESG vulnerability and employing similar Tactics, Techniques, and Procedures (TTPs) within their campaigns, resulting in a notable increase in detections. Subsequent to these events, our findings have not indicated a significant increase in newly detected Advanced Persistent Threat (APT) campaigns.
Regarding suspected threat actors focusing on financial organizations, the landscape primarily features financially motivated groups, including the prominent Lazarus Group, alongside entities like FIN11, FIN7, and TA505.
In terms of geographical impact, the United States is the most targeted region, closely followed by Japan, the United Kingdom, and India. Notably, Southeast Asia, including Australia, has also witnessed elevated attack volumes. This surge can be attributed to the heightened activity of the Lazarus Group, primarily targeting financial institutions in the Asia-Pacific region.
Web applications remain the top-attacked technology for cyberattacks across various industries, with operating systems following closely in terms of susceptibility. Additionally, we’ve observed instances of attacks targeting database and application infrastructure.
Over the past 3 months, CYFIRMA’s telemetry recorded only 33,304 phishing attacks out of a total of 201,478 that involved Finance industry campaigns.
As per the chart below, this is 16.53% of all observed themes CYFIRMA telemetry is tracking.
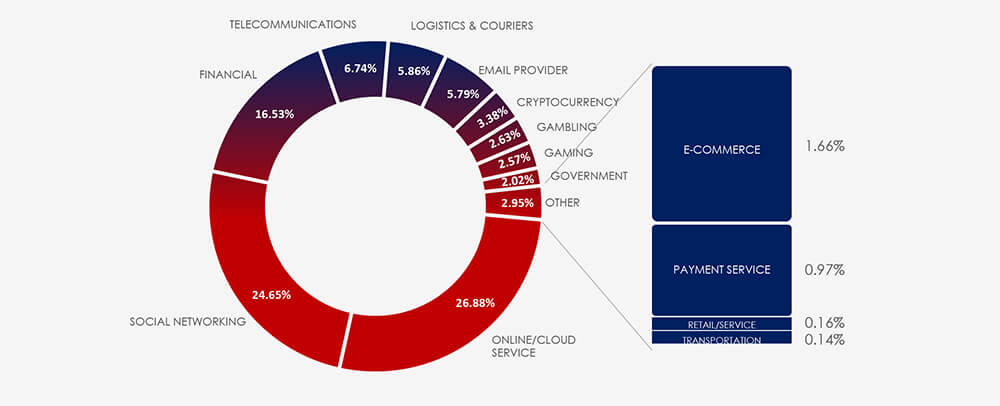
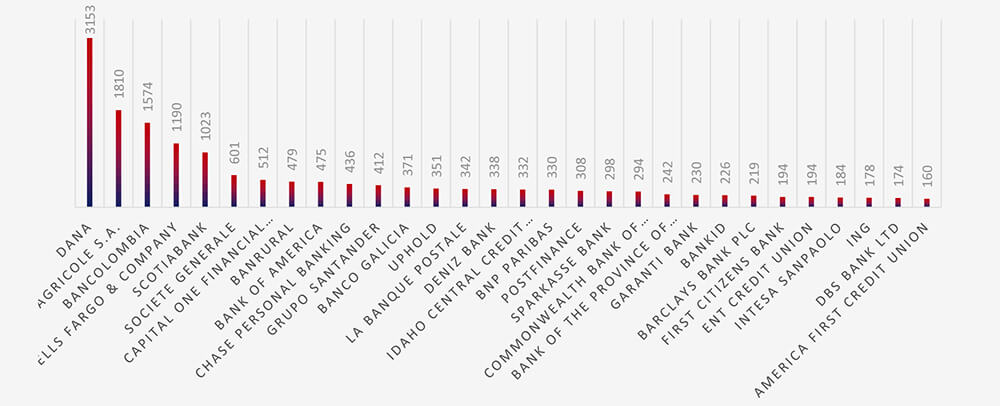
The top three impersonated brands are Indonesian, French, and Colombian. Notably, the first U.S. brand ranks fourth, highlighting shifts in the finance scam phishing landscape.
ASN-based origin of finance phishing remains by a large margin in the USA.
Risk Level Indicator: High
The finance industry has historically been among the most popular phishing lures ever since the inception of email.
Our observations have documented impersonation attempts against 272 distinct financial organizations. Reflecting a growing trend of increased lower-tier cybercriminal activity beyond the United States and other developed economies, the Indonesian financial platform DANA has become the most frequently impersonated brand. Moreover, there is a noticeable rise in fraudulent activities targeting Latin American and French financial institutions, often tailored to specific regions and countries.
Interestingly, our ASN Origin-based telemetry data indicates that a significant number of phishing campaigns impersonating DANA and other foreign brands originate from within the United States. This suggests an international dimension to these activities, with a portion conducted by local cybercriminal entities.
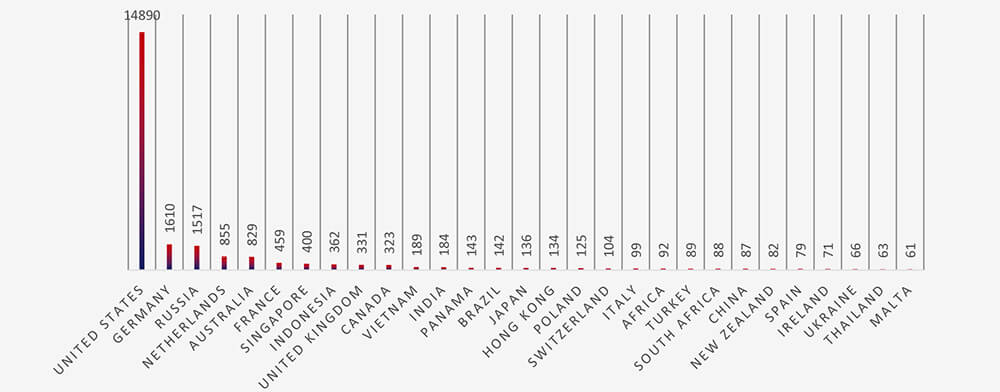
In the past 90 days, CYFIRMA has identified 228 verified ransomware victims within the financial industry sectors. This accounts for 12,7% of the overall total of 1,797 ransomware incidents during the same period.
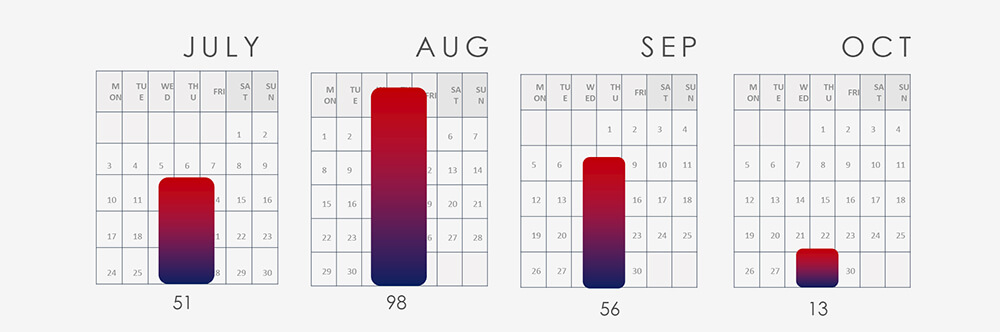
Monthly trends show a significant spike above the average during August.
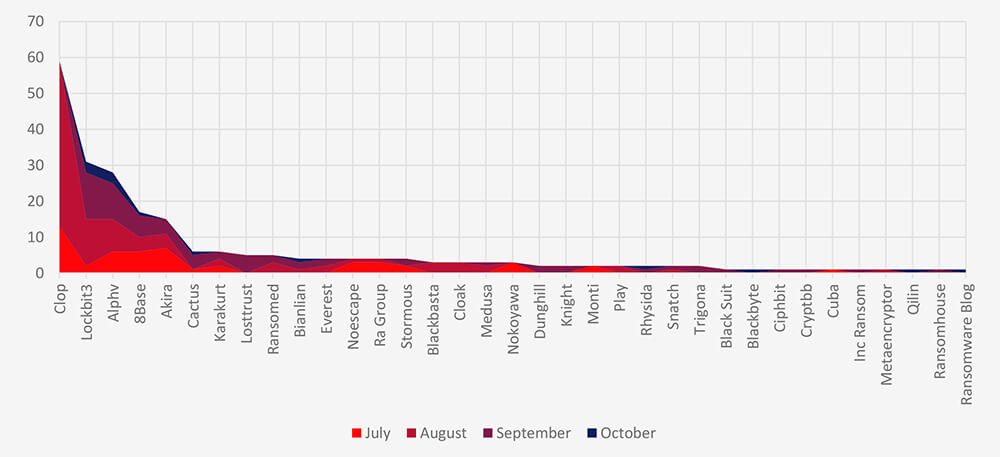
A breakdown of the monthly activity shows the Cl0p gang with their summer rampage is behind the August spike.
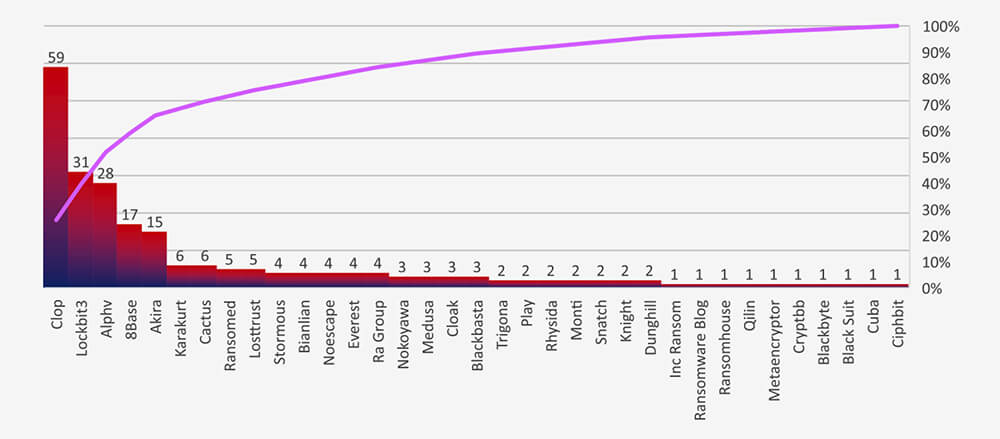
In total 35 groups recorded finance organization victims in the past 90 days. The top 3 are responsible for over 50% of them.
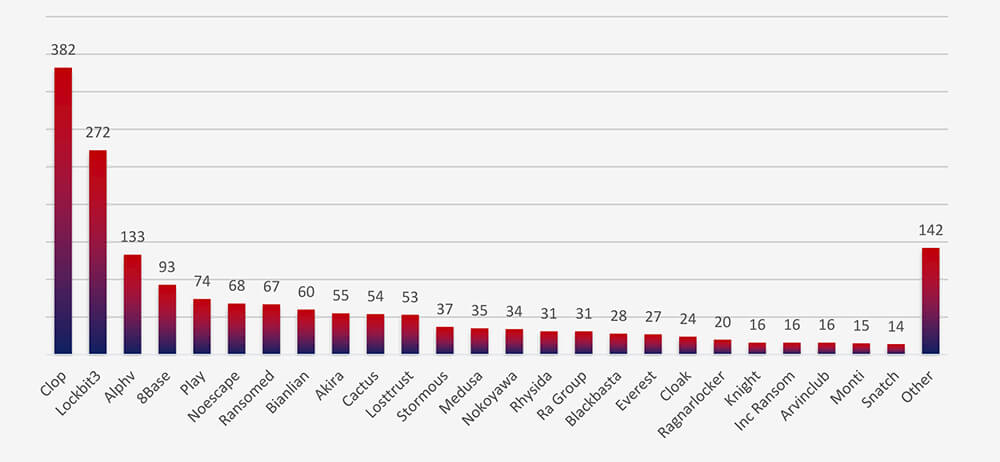
Compared to all recorded victims in the same time period some groups, such as Play show significantly fewer victims in the finance industry, implying a focus on other industries.
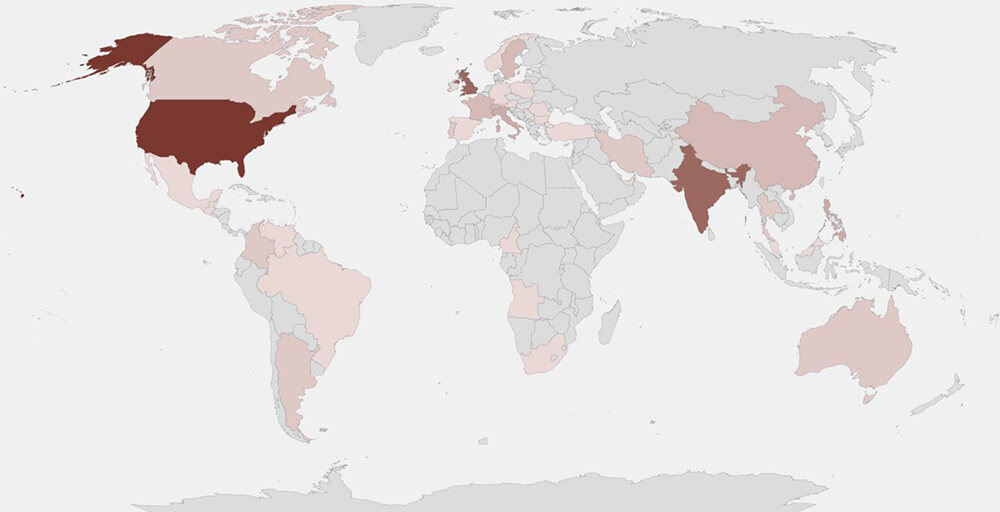
The heatmap of geographic distribution illustrates the global reach of ransomware across all continents and surging interest in growing economies.
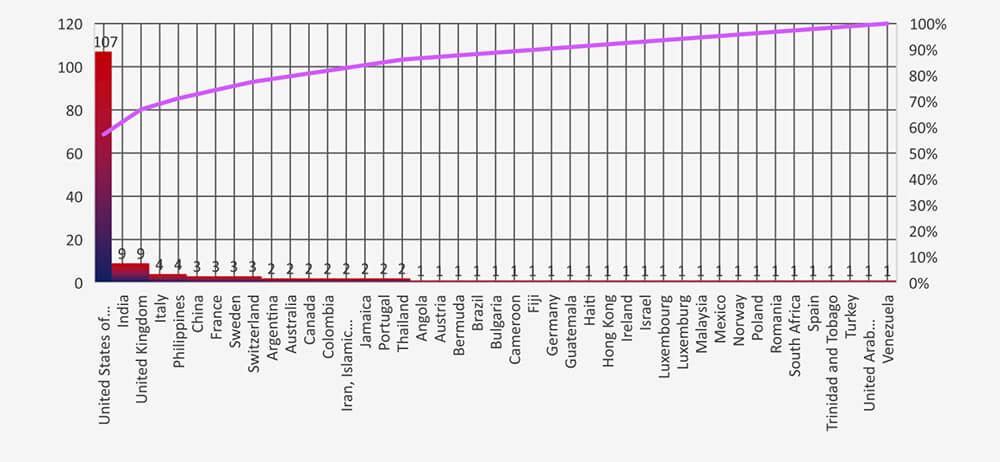
In total 43 countries recorded finance industry ransomware victims with the US alone accounting for ~60% of all.
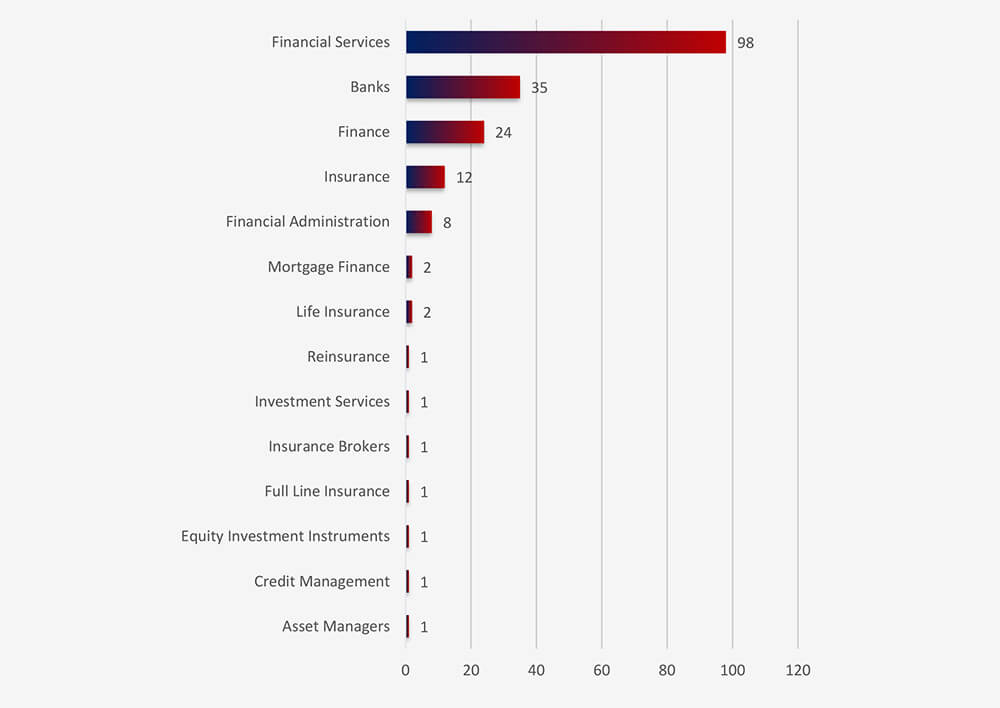
Financial services, banks and insurance are the most vulnerable sectors within finance industry.
Risk Level Indicator: High
Monthly activity consistently shows a substantial volume of attacks, with a noteworthy surge in August. A closer look at the groups behind these attacks highlights Cl0p’s significant activity during that month, followed by Lockbit3, ALPHV, and 8base, which all maintained consistent levels of attacks.
The data on the total number of victims per group underscores the dominance of major ransomware gangs, with the top three accounting for over half of all victims. This data further emphasizes the collective impact of smaller groups, although some, like Play or Noescape, displayed reduced interest in the finance industry when compared to the total number of victims over the same period.
Of the 47 active gangs in the past 90 days, 35 have targeted the finance sector. Notably, Cl0p has shown a heightened focus on this industry, frequently leveraging its ‘MoveIt’ exploits during August.
Among the 188 victims with identified locations in 43 different countries, the United States ranks as the most affected, with 107 victims, followed by India and the UK. The United States remains the most targeted country across various industries, owing to its vast economy and diverse financial landscape. In the finance industry, many emerging economies with rapidly growing financial institutions and high digitalization levels provide a broad range of attack vectors.
For a comprehensive, up-to-date global ransomware tracking report on a monthly basis, please refer to our new monthly “Tracking Ransomware” series here.
The finance industry plays a significant role in the global cyber threat landscape, consistently facing higher risks. Our data confirms the ongoing trend of increased cyberattacks targeting financial institutions in densely populated emerging economies. This trend is due to rapid digitalization and lower cybersecurity awareness, which creates a favourable environment for cybercriminals of varying skill levels.
This complex threat landscape involves highly sophisticated groups like the Lazarus Group, as well as a notable increase in ransomware incidents. Geographically, non-English speaking countries predominantly serve as the base for impersonated brands, highlighting the diverse targets and global presence of cyber adversaries.