

Red Menshen is a China-linked advanced threat actor active since at least 2021, known for deploying highly stealthy “digital sleeper cells” within telecommunications networks. Its campaigns are designed to enable high-level espionage, including targeted intrusions into government networks. The group is assessed to be an APT conducting cyber espionage operations using custom-developed tools.
Alias:
Earth Bluecrow
Motivation:
Information Theft, Espionage
Targeted Industries:

Targeted Countries:
Egypt, India, the Middle East, Myanmar, South Korea, Thailand, Turkey, the US, Vietnam, and Cambodia.

Target Technologies:
Windows, Operating Systems
Malware used by Red Menshen:
BPFDoor
Deployment of BPFDoor for Stealth Persistence
Recent campaigns consistently show Red Menshen leveraging BPFDoor, a Linux-based backdoor that operates at the kernel level using Berkeley Packet Filter (BPF) functionality. Unlike traditional malware, BPFDoor does not rely on open ports or standard command-and-control communication. Instead, it passively monitors network traffic and activates only upon receiving specially crafted packets. This approach enables highly covert persistence within compromised environments and significantly reduces the likelihood of detection.
Targeting of Telecommunications Infrastructure
Red Menshen continues to prioritize telecommunications providers as its primary target. By infiltrating telecom networks, the group gains access to large volumes of data traversing these systems, including communications and metadata associated with government entities and enterprises. This targeting reflects a strategic focus on high-value infrastructure that enables broad intelligence collection rather than isolated system compromise.
Exploitation of Network Edge Devices for Initial Access
Recent activity indicates the group frequently exploits vulnerabilities in internet-facing network devices, including VPN appliances, firewalls, and enterprise network equipment. These systems serve as entry points into internal environments, allowing the actor to establish footholds without relying heavily on user interaction-based techniques such as phishing.
Use of Multi-Stage Post-Exploitation Toolchains
Following initial compromise, Red Menshen deploys a combination of custom and publicly available tools to expand access and maintain control. Observed toolsets include reverse shells, credential harvesting utilities, and cross-platform frameworks that facilitate lateral movement and remote command execution. This modular approach enables flexible operations across both Linux and Windows environments.
Covert Command-and-Control Mechanisms
Instead of maintaining persistent outbound connections, Red Menshen utilizes packet-triggered activation mechanisms within BPFDoor to control infected systems. This eliminates the need for continuous beaconing and allows command execution only when required, making network-based detection significantly more challenging.
Long-Term Persistence Within Critical Networks
Campaign observations indicate that Red Menshen maintains extended dwell times within compromised environments. The group focuses on sustaining undetected access over long periods, enabling continuous intelligence collection rather than immediate exploitation or disruption.
Shift Toward Infrastructure-Level Espionage
Red Menshen demonstrates a clear shift from traditional endpoint-focused attacks to compromising core network infrastructure, particularly within the telecommunications sector. This enables the actor to access and monitor data at scale, affecting multiple downstream organizations simultaneously.
Emphasis on Stealth and Passive Operations
The group prioritizes low-noise operations, avoiding techniques that generate detectable traffic such as frequent command-and-control communication. Passive backdoors and covert activation mechanisms are central to their operational model.
Advanced Use of Network-Level Techniques
The use of BPF-based malware reflects a deep understanding of network traffic handling and low-level system operations. This allows Red Menshen to operate below traditional security monitoring layers, indicating a high level of technical sophistication.
Strategic Pre-Positioning for Intelligence Collection
Rather than conducting rapid or destructive attacks, Red Menshen focuses on pre-positioning within critical infrastructure. By maintaining persistent access, the group ensures it can collect intelligence continuously or leverage access when required.
Consistent Focus on High-Value Targets
The actor continues to prioritize sectors associated with sensitive communications and national-level data, particularly telecommunications. This consistent targeting pattern highlights a long-term intelligence-driven objective.
Final Assessment
Red Menshen’s recent campaigns highlight a mature and highly specialized espionage model centered on stealth, persistence, and infrastructure access. The group’s continued use of BPFDoor and focus on telecom networks demonstrate a strategic approach aimed at broad, long-term intelligence collection rather than immediate operational impact.
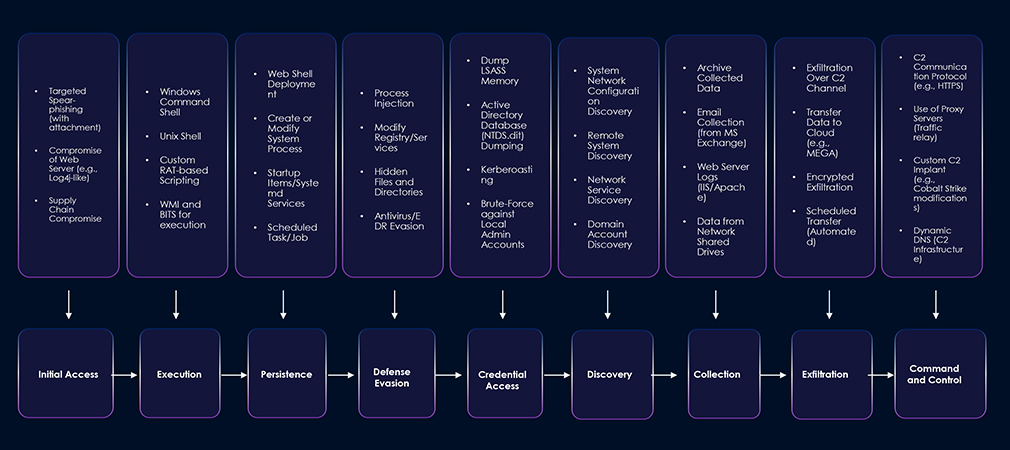
| Tactic | ID | Technique |
| Initial Access | T1190 | Exploit Public-Facing Application |
| Initial Access | T1078 | Valid Accounts |
| Execution | T1059 | Command and Scripting Interpreter |
| Persistence | T1547 | Boot or Logon Autostart Execution |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Persistence | T1078 | Valid Accounts |
| Privilege Escalation | T1547 | Boot or Logon Autostart Execution |
| Privilege Escalation | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1078 | Valid Accounts |
| Privilege Escalation | T1068 | Exploitation for Privilege Escalation |
| Defense Evasion | T1480 | Execution Guardrails |
| Defense Evasion | T1078 | Valid Accounts |
| Defense Evasion | T1564.004 | Hide Artifacts: NTFS File Attributes |
| Defense Evasion | T1036 | Masquerading |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1070 | Indicator Removal |
| Credential Access | T1056 | Input Capture |
| Credential Access | T1110 | Brute Force |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1018 | Remote System Discovery |
| Lateral Movement | T1021.004 | Remote Services: SSH |
| Lateral Movement | T1570 | Lateral Tool Transfer |
| Collection | T1005 | Data from Local System |
| Collection | T1056 | Input Capture |
| Tactic | ID | Technique |
| Collection | T1119 | Automated Collection |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and Control | T1095 | Non-Application Layer Protocol |
| Command and Control | T1572 | Protocol Tunneling |
| Command and Control | T1001 | Data Obfuscation |
| Command and Control | T1105 | Ingress Tool Transfer |
| Exfiltration | T1041 | Exfiltration Over C2 Channel |