

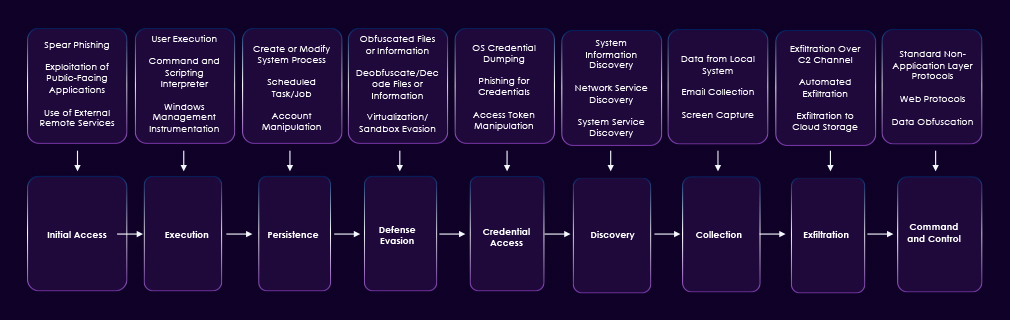
Earth Lusca (aka FishMonger) is a China-linked threat actor active since 2019, that focuses primarily on cyber-espionage against government, media, telecommunications, academic, and religious organizations, while also conducting financially motivated campaigns targeting cryptocurrency platforms. The group leverages tooling and tradecraft like APT41 and the Winnti Group cluster, but is assessed to operate independently from the Winnti Umbrella.
Alias:
FishMonger, Aquatic Panda, BountyGlad, Bronze University, CHROMIUM, Charcoal Typhoon, ControlX, Earth Krahang, RedDev10, RedHotel, RedScylla, and TAG-22.
Motivation:
Information theft, Political espionage, and Financial gain.
Targeted Industries

Targeted Countries:
Southeast Asia, Europe, Selected Middle Eastern targets, South Asia, United States

Target Technologies
Application Frameworks, Linux OS, Office Suite Software, Operating Systems, VPN, Web Applications, Web Servers
Malware used by Earth Lusca:
Spyder, SodaMaster, ShadowPad, XDealer, RESHELL, DinodasRAT (also known as XDealer), and KTLVdoor
Deployment of New Backdoors and Malware Evolution:
Recent campaigns show Earth Lusca expanding its malware arsenal with the introduction of KTLVdoor, a highly obfuscated multi-platform backdoor written in Go. The malware can masquerade as legitimate system utilities such as sshd, java, bash, or sqlite and enables attackers to perform remote command execution, port scanning, file manipulation, and system monitoring on both Windows and Linux systems. This development highlights the group’s continued focus on stealth and cross-platform persistence.
Continued Use of Established Espionage Toolsets:
Despite introducing new tools, the group continues to rely heavily on established malware families such as ShadowPad, Winnti, Spyder, and Cobalt Strike to maintain access to compromised environments and conduct data exfiltration. These tools provide modular capabilities, including remote command execution, system reconnaissance, and payload delivery, enabling long-term surveillance operations.
Targeting of Strategic Sectors in Asia:
Earth Lusca’s recent activity shows a continued focus on organizations in government, telecommunications, and technology sectors, particularly within the Asia-Pacific region. These targets are typically associated with sensitive political, economic, or technological information, indicating the group’s strategic objective of intelligence gathering and geopolitical monitoring.
Sophisticated Command-and-Control Infrastructure:
The group maintains a large and dynamic command-and-control (C2) infrastructure, with dozens of servers used to manage infected systems and exfiltrate data. Many of these servers have been observed hosted through cloud providers, allowing the attackers to quickly rotate infrastructure and evade detection by security defenses.
Advanced Obfuscation and Anti-Analysis Techniques:
Recent campaigns emphasize strong code obfuscation, encrypted communications, and disguised binaries to hinder malware analysis and detection. Earth Lusca also strips symbols and renames functions in malware binaries to random strings, making reverse engineering more difficult and extending the operational lifespan of their tools.
Persistence and Long-Term Espionage Strategy:
The group’s operations indicate a long-term intelligence-gathering strategy rather than immediate financial gain. By maintaining stealthy persistence within targeted networks and regularly updating their toolset, Earth Lusca is able to conduct prolonged espionage campaigns and continuously collect sensitive information from compromised environments.
| CVE ID | Affected Products | CVSS Score | Exploit Links |
| CVE-2024-21412 | Internet Shortcut Files Security | 8.1 | – |
| CVE-2016-5195 | Linux kernel | 7.0 | Link1, link2, link3, link4, link5, link6 |
| CVE-2023-32315 | Openfire | 7.5 | Link |
| CVE-2024-23897 | Jenkins | 9.8 | Link1, link2 |
| CVE-2022-21587 | Oracle Web Applications | 9.8 | link |
| CVE-2021-22555 | Linux | 7.8 | Link1, link2, link3, link4, link5 |
| Tactic | ID | Technique |
| Reconnaissance | T1595.002 | Active Scanning: Vulnerability Scanning |
| Resource Development | T1608.001 | Stage Capabilities: Upload Malware |
| Resource Development | T1583.001 | Acquire Infrastructure: Domains |
| Resource Development | T1583.004 | Acquire Infrastructure: Server |
| Resource Development | T1583.006 | Acquire Infrastructure: Web Services |
| Resource Development | T1584.004 | Compromise Infrastructure: Server |
| Resource Development | T1584.006 | Compromise Infrastructure: Web Services |
| Resource Development | T1588.002 | Obtain Capabilities: Tool |
| Resource Development | T1588.001 | Obtain Capabilities: Malware |
| Initial Access | T1189 | Drive-by Compromise |
| Initial Access | T1566.002 | Phishing: Spear Phishing Link |
| Initial Access | T1190 | Exploit Public-Facing Application |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
| Execution | T1059.007 | Command and Scripting Interpreter: JavaScript |
| Execution | T1047 | Windows Management Instrumentation |
| Execution | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Execution | T1204.002 | User Execution: Malicious File |
| Execution | T1204.001 | User Execution: Malicious Link |
| Execution | T1059.005 | Command and Scripting Interpreter: Visual Basic |
| Execution | T1059.006 | Command and Scripting Interpreter: Python |
| Persistence | T1547.012 | Boot or Logon Autostart Execution: Print Processors |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Persistence | T1574.001 | Hijack Execution Flow: DLL |
| Persistence | T1112 | Modify Registry |
| Persistence | T1098.004 | Account Manipulation: SSH Authorized Keys |
| Persistence | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Privilege Escalation | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Privilege Escalation | T1098.004 | Account Manipulation: SSH Authorized Keys |
| Privilege Escalation | T1548.002 | Abuse Elevation Control Mechanism: Bypass User Account Control |
| Privilege Escalation | T1547.012 | Boot or Logon Autostart Execution: Print Processors |
| Privilege Escalation | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1574.001 | Hijack Execution Flow: DLL |
| Defense Evasion | T1140 | Deobfuscate/Decode Files or Information |
| Defense Evasion | T1548.002 | Abuse Elevation Control Mechanism: Bypass User Account Control |
| Defense Evasion | T1574.001 | Hijack Execution Flow: DLL |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1036.005 | Masquerading: Match Legitimate Resource Name or Location |
| Defense Evasion | T1027.003 | Obfuscated Files or Information: Steganography |
| Defense Evasion | T1218.005 | System Binary Proxy Execution: Mshta |
| Defense Evasion | T1112 | Modify Registry |
| Credential Access | T1003.001 | OS Credential Dumping: LSASS Memory |
| Credential Access | T1003.006 | OS Credential Dumping: DCSync |
| Discovery | T1482 | Domain Trust Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1049 | System Network Connections Discovery |
| Discovery | T1007 | System Service Discovery |
| Discovery | T1018 | Remote System Discovery |
| Discovery | T1016 | System Network Configuration Discovery |
| Discovery | T1033 | System Owner/User Discovery |
| Lateral Movement | T1210 | Exploitation of Remote Services |
| Collection | T1056.001 | Input Capture: Keylogging |
| Command and Control | T1090 | Proxy |
| Exfiltration | T1567.002 | Exfiltration Over Web Service: Exfiltration to Cloud Storage |