


CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple – industries, geography, and technology – that could be relevant to your organization.
Type: Ransomware
Target Technologies: Windows OS, enterprise network endpoints
Introduction:
CYFIRMA Research and Advisory Team has found Uragan Ransomware while monitoring various underground forums as part of our Threat Discovery Process.
Uragan Ransomware
Uragan ransomware has been identified as a file-encrypting malware strain that restricts access to victim data by encrypting files and appending the “.uragan” extension, rendering them inaccessible. Upon execution, the malware deploys a ransom note titled “README.txt” and indicates that critical infrastructure, including systems, servers, and backups, may be impacted. The operators claim that only they possess the capability to restore the encrypted data through a unique decryption key and warn victims against attempting recovery using third-party tools or modifying encrypted files, stating such actions may result in permanent data loss. Additionally, the threat actors employ double extortion tactics, asserting that sensitive information may have been exfiltrated during the intrusion and could be publicly disclosed or shared if ransom demands are not met. Currently, no publicly available or verified decryption tool exists for this ransomware, and payment does not guarantee successful data recovery.
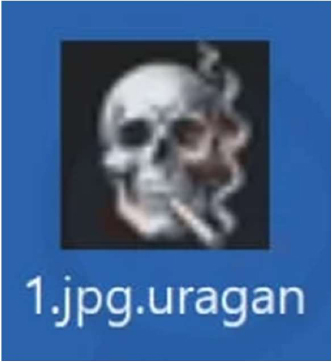
Screenshot: File encrypted by the ransomware (Source: Surface Web)
The ransom note associated with Uragan ransomware, typically delivered as “README.txt”, informs victims that their files have been encrypted and access has been restricted. It emphasizes that only the attackers can provide the necessary decryption key and discourages victims from renaming encrypted files or using third-party recovery tools, claiming this could permanently damage the data. The message further reinforces coercion by stating that multiple parts of the victim’s infrastructure may be affected and by introducing data leakage threats, indicating that exfiltrated sensitive information may be disclosed or shared if the ransom is not paid. Overall, the note follows standard ransomware intimidation strategies, combining claims of irreversible encryption with data exposure risks, while offering no verifiable guarantee of file recovery after payment.
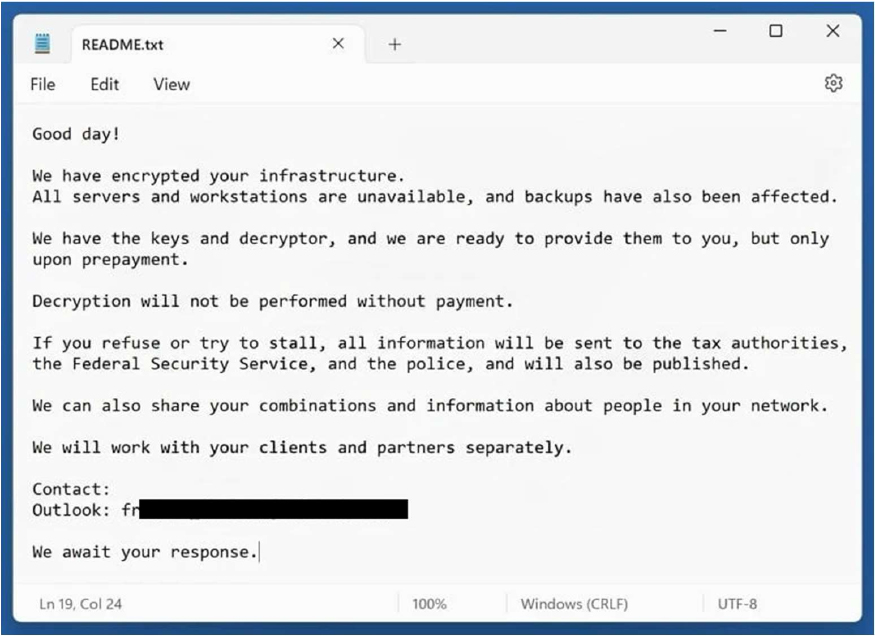
Screenshot: The appearance of the Uragan’s Ransom Note (Source: Surface Web)
The following are the TTPs based on the MITRE Attack Framework
| Tactic | Technique ID | Technique Name |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1129 | Shared Modules |
| Persistence | T1112 | Modify Registry |
| Persistence | T1543 | Create or Modify System Process |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Persistence | T1547 | Boot or Logon Autostart Execution |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1055 | Process Injection |
| Privilege Escalation | T1543 | Create or Modify System Process |
| Privilege Escalation | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1547 | Boot or Logon Autostart Execution |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1548 | Abuse Elevation Control Mechanism |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1027.002 | Obfuscated Files or Information: Software Packing |
| Defense Evasion | T1036 | Masquerading |
| Defense Evasion | T1055 | Process Injection |
| Defense Evasion | T1070 | Indicator Removal |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1112 | Modify Registry |
| Defense Evasion | T1202 | Indirect Command Execution |
| Defense Evasion | T1497 | Virtualization/Sandbox Evasion |
| Defense Evasion | T1548 | Abuse Elevation Control Mechanism |
| Defense Evasion | T1562 | Impair Defenses |
| Defense Evasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| Defense Evasion | T1564 | Hide Artifacts |
| Defense Evasion | T1564.003 | Hide Artifacts: Hidden Window |
| Credential Access | T1003 | OS Credential Dumping |
| Credential Access | T1539 | Steal Web Session Cookie |
| Credential Access | T1552 | Unsecured Credentials |
| Credential Access | T1552.001 | Unsecured Credentials: Credentials In Files |
| Credential Access | T1555 | Credentials from Password Stores |
| Credential Access | T1555.003 | Credentials from Password Stores: Credentials from Web Browsers |
| Discovery | T1012 | Query Registry |
| Discovery | T1057 | Process Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1497 | Virtualization/Sandbox Evasion |
| Collection | T1005 | Data from Local System |
| Collection | T1074 | Data Staged |
| Collection | T1114 | Email Collection |
| Command and Control | T1071 | Application Layer Protocol |
| Command and Control | T1095 | Non-Application Layer Protocol |
| Impact | T1485 | Data Destruction |
| Impact | T1486 | Data Encrypted for Impact |
| Impact | T1489 | Service Stop |
Relevancy and Insights
ETLM Assessment:
CYFIRMA’s analytical assessment suggests that Uragan ransomware operators may continue to evolve within the boundaries of established ransomware tradecraft, with future activity likely focused on operational refinement rather than fundamental innovation. Based on its current use of file encryption, ransom messaging, and data exposure threats, the group may enhance the reliability and speed of encryption routines, improve ransom note clarity to increase payment conversion rates, and standardize extortion workflows. There is also a realistic possibility of expanded double extortion practices, including more structured use of data leakage pressure to amplify coercion. Additionally, operators may attempt to improve initial access efficiency—potentially leveraging common vectors such as phishing or exploitation of exposed services—while maintaining a focus on broad, opportunistic targeting rather than sector-specific campaigns. However, there is currently no direct evidence indicating the development of advanced capabilities (e.g., novel encryption mechanisms, highly targeted intrusions, or custom exploitation frameworks), suggesting that any near-term evolution will most likely remain incremental and aligned with existing ransomware operational models.
Sigma rule:
title: Uncommon Svchost Command Line Parameter tags:
– attack.defense-evasion
– attack.privilege-escalation
– attack.t1036.005
– attack.t1055
– attack.t1055.012 logsource:
category: process_creation product: windows
detection: selection:
# Example of command to simulate: “C:\Windows\System32\svchost.exe” calc.exe
Image|endswith: ‘\svchost.exe’ filter_main_flags:
CommandLine|re: ‘-k\s\w{1,64}(\s?(-p|-s))?’ filter_main_empty:
CommandLine: ” filter_main_null:
CommandLine: null filter_optional_defender:
ParentImage|endswith: ‘\MsMpEng.exe’ CommandLine|contains: ‘svchost.exe’
filter_optional_mrt: ParentImage|endswith: ‘\MRT.exe’ CommandLine: ‘svchost.exe’
condition: selection and not 1 of filter_main_* and not 1 of filter_optional_* falsepositives:
– Unlikely level: high
(Source: Surface Web)
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
Type: Information Stealer | Objective: Information/Data Exfiltration |
Target Technology: MacOS| Target Geography: Global
CYFIRMA collects data from various forums based on which the trend is ascertained. We identified a few popular malwares that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week, “MacSync Stealer” is in focus.
Overview of Operation MacSync Stealer Malware
MacSync Stealer is a type of malware that targets macOS systems and is built to quietly collect sensitive information without drawing attention. Instead of behaving in an obvious or aggressive way, it runs silently in the background and uses normal system tools so that its activity looks like regular system behavior. This makes it much harder for users or basic security tools to notice anything unusual.
It connects to a remote server to receive instructions and can carry out tasks in accordance with the attacker’s commands. This means malware can adapt its behavior over time. One of its primary objectives is to gather important data, such as login details, system information, or personal files, and then send that data back to the attacker.
In simple terms, MacSync Stealer is designed to stay hidden while giving attackers access to your system and data. Because it operates quietly and blends in with normal activity, it can remain unnoticed for a long time, increasing the risk of data theft and further misuse of the compromised system.
Attack Method
The attack begins with a hidden script that runs silently in the background, ensuring that no visible signs alert the user. It avoids detection by suppressing activity on the screen and even closing open terminal windows, making it difficult to notice any suspicious behavior during execution.
Following successful execution, the script connects to a remote server controlled by the attacker. It sends initial information and waits for instructions. The commands received from the server are executed directly on the system using built-in tools, allowing the attacker to dynamically control the compromised machine without needing to install additional files.
Once the commands are executed, the script gathers sensitive data from the system. This information is then compressed into a file and sent back to the attacker’s server.
This process ensures efficient data exfiltration while minimizing the chances of detection.
To cover its tracks, the script deletes the compressed file after transmission. Overall, the attack is designed to remain stealthy, maintain remote control, and quietly steal data while avoiding detection by users and security tools.
The following are the TTPs based on the MITRE Attack Framework for Enterprise
| Tactic | Technique ID | Technique Name |
| Execution | T1059.002 | Command and Scripting Interpreter: AppleScript |
| Execution | T1059.003 | Command and Scripting Interpreter: Windows Command Shell |
| Execution | T1204.002 | User Execution: Malicious File |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1057 | Process Discovery |
| Command and control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and control | T1105 | Ingress Tool Transfer |
| Exfiltration | T1041 | Exfiltration Over C2 Channel |
| Exfiltration | T1048 | Exfiltration Over Alternative Protocol |
INSIGHTS
This malware shows how attackers are trying to stay hidden by behaving like normal system activity instead of doing anything obviously suspicious. It uses everyday tools and processes to minimize its footprint and blends in with normal system activity, making it harder for security systems to detect. This reflects a shift toward more subtle and discreet attack methods.
Another key point is that the malware depends on externally delivered instructions, typically from a remote server. Rather than operating as a fully self-contained program, it waits for commands from a remote source, which allows the attacker to change its behavior whenever needed. As a result, it becomes more difficult to fully understand its behavior through static code analysis alone.
It also tries to remove any signs of its activity after completing its operations. By cleaning up traces and reducing evidence, it makes post-incident investigation more difficult. This shows that malware is designed not just to carry out an attack, but also to evade detection and hinder subsequent analysis.
ETLM ASSESSMENT
From an ETLM perspective, this malware reflects a trend where attacks become more discreet and closely resemble normal system activity, making it harder to detect and investigate. Instead of using obvious malicious behavior, such threats are expected to rely on familiar tools and standard processes to operate quietly within systems. This shift suggests that attackers will continue to refine techniques that help them stay hidden while maintaining control over compromised environments.
For organizations and individuals, this evolution increases the risk of sensitive data being accessed or misused without immediate detection. It also highlights the increasing importance of awareness, as routine actions and system interactions could potentially be exploited. Over time, this may change how people trust and use digital systems, encouraging more cautious behavior and making it more important to pay attention to unusual or unexpected activity.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems.
YARA Rules
rule MacSync_Shell_Backdoor
{
meta:
description = “Detection of macOS shell script abusing osascript for C2 and exfiltration”
author = “CYFIRMA” date = “2026-03-23”
severity = “critical”
strings:
$hash1 =
“055ce8476ae9079d0ab8a2b99a65040536114384a1a999e1963ca3840174c04b”
$hash2 =
“158b697c0e4ae73256fc23a9b25a18cd57140ede60757875fea9c2bb688b8552”
$shebang = “#!/bin/zsh”
$exec_null = “exec >/dev/null”
$exec_null_err = “exec 2>/dev/null”
$kill_terminal = “killall Terminal”
$curl_osascript = “curl”
$osascript = “osascript”
$c2_domain = “nordmest.com”
$dynamic_path = “/dynamic”
$gate_path = “/gate”
$api_header = “api-key:”
$user_agent = “Mozilla/5.0 (Macintosh; Intel Mac OS X”
$post_file = “-F \”file=@”
$rm_tmp = “rm -f /tmp/osalogging.zip”
$suspicious_combo = “| osascript”
condition:
any of ($hash*) or ($shebang and
(3 of ($exec_null, $exec_null_err, $kill_terminal)) and
$curl_osascript and
$osascript and
($c2_domain or $dynamic_path or $gate_path) and
$api_header and
$user_agent and
($post_file or $rm_tmp or $suspicious_combo))
}
Strategic Recommendations
Management Recommendations
Tactical Recommendations
Key Intelligence Signals:
Fancy Bear, aka APT28, is carrying out targeted campaigns
About the Threat Actor
FANCY BEAR is a well-documented Russian state-sponsored threat actor that has been active since at least 2007 and is widely assessed to operate in close coordination with Russian intelligence services. Security researchers have attributed multiple high-profile cyber operations to the group, including election interference activities in several countries, aimed at influencing political outcomes in favor of the Russian government.
Details on Exploited Vulnerabilities
| CVE ID | Affected Products | CVSS Score | Exploit Links |
| CVE-2023-38831 | WinRAR | 7.8 | Link |
| CVE-2021- 4034 | pkexec application | 7.8 | Link 1, Link 2 |
| CVE-2016- 5195 | Linux kernel | 7.0 | Link1, Link2, Link3, Link4, Link5, and Link6 |
| CVE-2020- 0688 | Microsoft Exchange | 8.8 | Link 1 and Link 2 |
| CVE-2015- 2545 | Microsoft Office | 7.8 | – |
| CVE-2025-66376 | Zimbra Collaboration | 6.1 | – |
TTPs based on MITRE ATT&CK Framework
| Tactic | ID | Technique |
| Reconnaissance | T1591 | Gather Victim Org Information |
| Reconnaissance | T1598.003 | Phishing for Information: Spear phishing Link |
| Reconnaissance | T1598 | Phishing for Information |
| Reconnaissance | T1596 | Search Open Technical Databases |
| Resource Development | T1583.001 | Acquire Infrastructure: Domains |
| Resource Development | T1583.003 | Acquire Infrastructure: Virtual Private Server |
| Resource Development | T1583.006 | Acquire Infrastructure: Web Services |
| Resource Development | T1586.002 | Compromise Accounts: Email Accounts |
| Resource Development | T1584.008 | Compromise Infrastructure: Network Devices |
| Resource Development | T1588.002 | Obtain Capabilities: Tool |
| Initial Access | T1189 | Drive-by Compromise |
| Initial Access | T1190 | Exploit Public-Facing Application |
| Initial Access | T1133 | External Remote Services |
| Initial Access | T1091 | Replication Through Removable Media |
| Initial Access | T1199 | Trusted Relationship |
| Initial Access | T1078 | Valid Accounts |
| Initial Access | T1078.004 | Valid Accounts: Cloud Accounts |
| Initial Access | T1566.001 | Phishing: Spear phishing Attachment |
| Execution | T1204.001 | User Execution: Malicious Link |
| Execution | T1203 | Exploitation for Client Execution |
| Execution | T1559.002 | Inter-Process Communication: Dynamic Data Exchange |
| Execution | T1204.002 | User Execution: Malicious File |
| Persistence | T1098.002 | Account Manipulation: Additional Email Delegate Permissions |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Persistence | T1037.001 | Boot or Logon Initialization Scripts: Logon Script (Windows) |
| Persistence | T1546.015 | Event Triggered Execution: Component Object Model Hijacking |
| Persistence | T1133 | External Remote Services |
| Persistence | T1137.002 | Office Application Startup: Office Test |
| Persistence | T1542.003 | Pre-OS Boot: Bootkit |
| Persistence | T1505.003 | Server Software Component: Web Shell |
| Persistence | T1078 | Valid Accounts |
| Persistence | T1078.004 | Valid Accounts: Cloud Accounts |
| Privilege Escalation | T1134.001 | Access Token Manipulation: Token Impersonation/Theft |
| Privilege Escalation | T1098.002 | Account Manipulation: Additional Email Delegate Permissions |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1037.001 | Boot or Logon Initialization Scripts: Logon Script (Windows) |
| Privilege Escalation | T1546.015 | Event Triggered Execution: Component Object Model Hijacking |
| Privilege Escalation | T1078.004 | Valid Accounts: Cloud Accounts |
| Defense Evasion | T1134.001 | Access Token Manipulation: Token Impersonation/Theft |
| Defense Evasion | T1564.001 | Hide Artifacts: Hidden Files and Directories |
| Defense Evasion | T1564.003 | Hide Artifacts: Hidden Window |
| Defense Evasion | T1070.001 | Indicator Removal: Clear Windows Event Logs |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1070.006 | Indicator Removal: Timestomp |
| Defense Evasion | T1036 | Masquerading |
| Defense Evasion | T1036.005 | Masquerading: Match Legitimate Resource Name or Location |
| Defense Evasion | T1027.013 | Obfuscated Files or Information: Encrypted/Encoded File |
| Defense Evasion | T1542.003 | Pre-OS Boot: Bootkit |
| Defense Evasion | T1014 | Rootkit |
| Defense Evasion | T1218.011 | System Binary Proxy Execution: Rundll32 |
| Defense Evasion | T1221 | Template Injection |
| Defense Evasion | T1550.001 | Use Alternate Authentication Material: Application Access Token |
| Defense Evasion | T1550.002 | Use Alternate Authentication Material: Pass the Hash |
| Defense Evasion | T1078.004 | Valid Accounts: Cloud Accounts |
| Credential Access | T1557.004 | Adversary-in-the-Middle: Evil Twin |
| Credential Access | T1110 | Brute Force |
| Credential Access | T1110.001 | Brute Force: Password Guessing |
| Credential Access | T1110.003 | Brute Force: Password Spraying |
| Credential Access | T1056.001 | Input Capture: Keylogging |
| Credential Access | T1040 | Network Sniffing |
| Credential Access | T1003 | OS Credential Dumping |
| Credential Access | T1003.001 | OS Credential Dumping: LSASS Memory |
| Credential Access | T1003.002 | OS Credential Dumping: Security Account Manager |
| Credential Access | T1003.003 | OS Credential Dumping: NTDS |
| Credential Access | T1528 | Steal Application Access Token |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1040 | Network Sniffing |
| Discovery | T1120 | Peripheral Device Discovery |
| Discovery | T1057 | Process Discovery |
| Lateral Movement | T1210 | Exploitation of Remote Services |
| Lateral Movement | T1091 | Replication Through Removable Media |
| Lateral Movement | T1550.001 | Use Alternate Authentication Material: Application Access Token |
| Lateral Movement | T1550.002 | Use Alternate Authentication Material: Pass the Hash |
| Collection | T1557.004 | Adversary-in-the-Middle: Evil Twin |
| Collection | T1560 | Archive Collected Data |
| Collection | T1560.001 | Archive Collected Data: Archive via Utility |
| Collection | T1119 | Automated Collection |
| Collection | T1213 | Data from Information Repositories |
| Collection | T1213.002 | Data from Information Repositories: Sharepoint |
| Collection | T1005 | Data from Local System |
| Collection | T1039 | Data from Network Shared Drive |
| Collection | T1025 | Data from Removable Media |
| Collection | T1074.001 | Data Staged: Local Data Staging |
| Collection | T1074.002 | Data Staged: Remote Data Staging |
| Collection | T1114.002 | Email Collection: Remote Email Collection |
| Collection | T1056.001 | Input Capture: Keylogging |
| Collection | T1113 | Screen Capture |
| Command and Control | T1001.001 | Data Obfuscation: Junk Data |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and Control | T1071.003 | Application Layer Protocol: Mail Protocols |
| Command and Control | T1092 | Communication Through Removable Media |
| Command and Control | T1573.001 | Encrypted Channel: Symmetric Cryptography |
| Command and Control | T1105 | Ingress Tool Transfer |
| Command and Control | T1090.001 | Proxy: Internal Proxy |
| Command and Control | T1090.002 | Proxy: External Proxy |
| Command and Control | T1090.003 | Proxy: Multi-hop Proxy |
| Command and Control | T1102.002 | Web Service: Bidirectional Communication |
| Exfiltration | T1030 | Data Transfer Size Limits |
| Exfiltration | T1048.002 | Exfiltration Over Alternative Protocol: Exfiltration Over Asymmetric Encrypted Non-C2 Protocol |
| Impact | T1498 | Network Denial of Service |
Latest Developments Observed
The threat actor is suspected to have conducted a targeted phishing campaign leveraging a cross-site scripting (XSS) vulnerability in Zimbra Collaboration (CVE- 2025-66376) to compromise a Ukrainian government entity. The campaign appears to be aimed at exfiltrating sensitive information from the targeted systems.
ETLM Insights
Fancy Bear, aka APT28, represents a highly agile, geopolitically driven threat actor, requiring organisations to adopt a predictive, intelligence-led defence strategy focused on early warning, campaign tracking, and proactive threat mitigation.
Operationally, the actor demonstrates the capability to conduct long-term intelligence collection campaigns as well as timed disruptive or destructive operations. These activities are often closely aligned with geopolitical objectives and may be synchronised with offline military or diplomatic developments, amplifying their strategic impact.
The actor’s behaviour is underpinned by the following core strategic drivers: Geopolitical Objectives Over Financial Gains: Operations are primarily driven by national strategic interests rather than monetary motives, with a focus on intelligence collection, influence, and disruption.
Maximising Strategic Impact with Plausible Deniability: Campaigns are designed to achieve high-impact outcomes while maintaining ambiguity, often leveraging covert infrastructure, proxy actors, and obfuscation techniques to avoid direct attribution.
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
YARA Rules
rule APT28_Zimbra_XSS_Exploit
{
meta:
description = “Detects XSS exploitation patterns targeting Zimbra” author = “CYFIRMA”
date = “2026-03-23”
strings:
$x1 = “<script>” nocase
$x2 = “document.cookie” ascii
$x3 = “onerror=” ascii
$x4 = “onload=” ascii
$x5 = “fetch(” ascii
$x6 = “XMLHttpRequest” ascii
$x7 = “atob(” ascii
$x8 = “eval(” ascii condition:
4 of ($x*)
}
rule APT28_Zimbra_XSS_Payload
{
meta:
description = “Detects XSS/injection payloads targeting Zimbra (APT28 activity)” author = “CYFIRMA”
date = “2026-03-23”
strings:
$xss1 = “<script>” ascii nocase
$xss2 = “document.cookie” ascii
$xss3 = “XMLHttpRequest” ascii
$xss4 = “atob(” ascii
$xss5 = “fetch(” ascii
$xss6 = “eval(” ascii
$xss7 = “onerror=” ascii
$xss8 = “String.fromCharCode” ascii condition:
5 of ($xss*)
}
Strategic Recommendations
Management Recommendations
Tactical Recommendations
EU sanctions Chinese and Iranian companies for aiding cyberattacks
The European Union has imposed sanctions on two Chinese companies and one Iranian firm, along with two individuals, for their involvement in cyberattacks targeting EU member states and partners.
The measures target China-based Integrity Technology Group and Anxun Information Technology (also known as iSoon), as well as the Iran-based company Emennet Pasargad. The EU also sanctioned the two co-founders of Anxun Information Technology.
According to EU officials, Integrity Technology Group provided technical support that enabled the compromise of more than 65,000 devices across six EU member states between 2022 and 2023, while Anxun Information Technology supplied hacking services aimed at critical infrastructure and key state functions in EU countries and beyond. Meanwhile, Emennet Pasargad unlawfully accessed a French subscriber database, attempted to sell the stolen data on the dark web, and carried out disinformation operations – including hacking advertising billboards – during the 2024 Paris Olympics. It was also linked to other disruptive cyber activities, such as interfering with a Swedish SMS service.
As a result of the sanctions, the listed entities and individuals face an asset freeze. EU citizens and companies are prohibited from providing them with funds, financial assets, or economic resources. The two individuals are also subject to a travel ban, preventing them from entering or transiting through EU territory.
ETLM Assessment
Both China and Iran have conducted aggressive cyber operations against the European Union and its member states. Both states increasingly rely on the private sector to conduct or support these campaigns, allowing a degree of plausible deniability while scaling operations beyond direct government agencies. In China, nominally private cybersecurity companies like iSoon and Integrity Tech operate as “hack-for-hire” contractors for the Ministry of Public Security (MPS) and Ministry of State Security (MSS), developing tools, providing infrastructure, and executing intrusions on behalf of the state in exchange for contracts. In Iran, companies such as Emennet Pasargad function as extensions of the Islamic Revolutionary Guard Corps (IRGC), blending commercial hacking services with state-directed espionage, data theft, and influence operations. This outsourcing model helps both regimes expand their cyber reach while complicating attribution and international responses.
Iran’s cyber operations continue despite strikes on infrastructure
US and Israeli strikes on Iran’s Ministry of Intelligence and Security (MOIS) in late February and early March 2026 reportedly killed two key figures tied to the country’s state-backed cyber operations and bombed out the infrastructure used by Iranian intelligence agencies’ cyber campaigns. Yet affiliated hacking groups have continued their activities. Among those killed were Mohammad Mehdi Farhadi Ramin, who was charged by the US Justice Department in 2020 for hacking American aerospace and defense firms, and Seyed Yahya Hosseiny Panjaki, a senior MOIS intelligence official linked by the FBI to cyberattacks and terror plots. Panjaki reportedly oversaw the MOIS unit responsible for directing state-affiliated hacktivist groups, including the notorious Handala. Despite these leadership losses, Iran’s cyber capabilities have proven resilient due to their decentralized structure. Handala has since claimed responsibility for a major disruptive attack on US medtech giant Stryker, while another MOIS-linked group carried out operations against Albanian targets. Western governments, organizations, and critical infrastructure operators should remain on high alert for sustained Iranian cyber threats amid the ongoing conflict.
ETLM Assessment:
Iran’s cyber operations have remained active despite the loss of senior MOIS leaders because of the highly decentralized structure of its cyber capabilities. Rather than relying on a single centralized command, Iran has built a network of semi-autonomous hacking groups, hacktivist personas (such as Handala), and external proxies that operate with significant independence. This distributed model allows individual units to continue planning and executing attacks – even when leadership is disrupted, or domestic internet infrastructure is damaged – using pre-positioned tools, alternative communications like Starlink, and delegated authority. As a result, the elimination of key figures has slowed coordination but has not shut down the overall cyber campaign.
Space Bears Ransomware Impacts Bonheure Corporation
Summary:
CYFIRMA observed in an underground forum that a company from Japan, Bonheure Corporation (https[:]//bonheure[.]co[.]jp/), was compromised by Space Bears Ransomware. Bonheure Corporation is a Japan-based company operating primarily in the entertainment and leisure industry, specifically within the amusement parks and arcades sector. The compromised data includes confidential and sensitive information belonging to the organization.
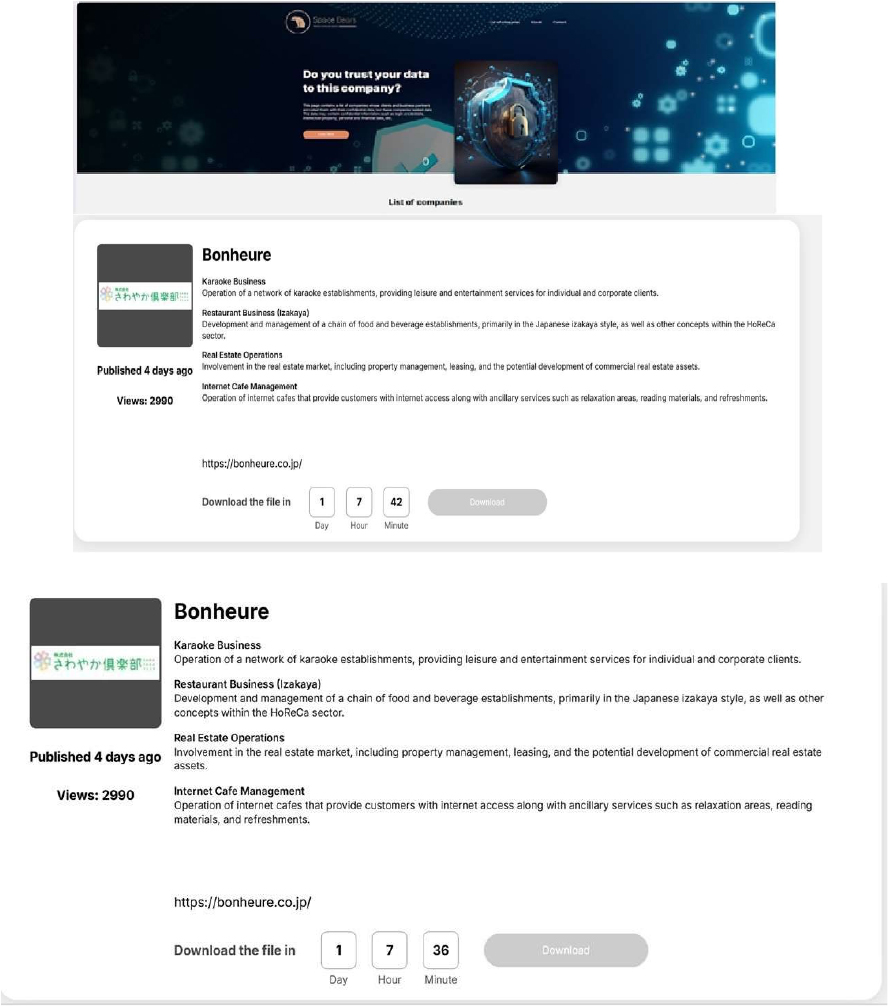
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, Space Bears ransomware represents a significant threat in the evolving landscape of cybercrime. With its aggressive tactics, association with established ransomware operations like Phobos, and focus on double extortion, organizations are advised to bolster their cybersecurity measures to mitigate risks associated with such attacks. Continuous monitoring of this group’s activities will be essential for understanding their methods and potential impact on various sectors.
The Gentlemen Ransomware Impacts Medicus Shuppan
Summary:
CYFIRMA observed in an underground forum that a company from Japan, Medicus Shuppan (https[:]//www[.]medica[.]co[.]jp/), was compromised by the Gentlemen Ransomware. Medicus Shuppan is dedicated to providing enjoyable learning experiences for healthcare professionals through a variety of products and services, including seminar books and digital content. The company aims to support the education of medical practitioners and contribute to the future of healthcare. They also focus on sustainability and creating valuable content that serves as a backbone in the medical field. Their intended clients include healthcare professionals, authors, and bookstores. The data, which has been breached, has not yet appeared on the leak site, indicating that negotiations between the affected party and the ransomware group may be underway. The compromised data includes confidential and sensitive information belonging to the organization.

Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, the Gentlemen Ransomware is a highly adaptive and globally active threat that leverages dual-extortion tactics, combining data theft with file encryption. The group employs advanced evasion and persistence techniques, supports cross-platform and scalable ransomware deployment, and conducts targeted attacks across multiple industries and geographic regions. This combination of capabilities makes it a significant risk to enterprise cybersecurity defenses, particularly for organizations with limited detection and incident-response maturity.
Vulnerability in E-Mail MFA Provider
Relevancy & Insights:
The vulnerability exists since the affected extension fails to properly reset the generated MFA code after successful authentication.
Impact:
A remote user can bypass authentication and gain access to the target system.
Affected Products:
https[:]//typo3[.]org/security/advisory/typo3-ext-sa-2026-007/
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
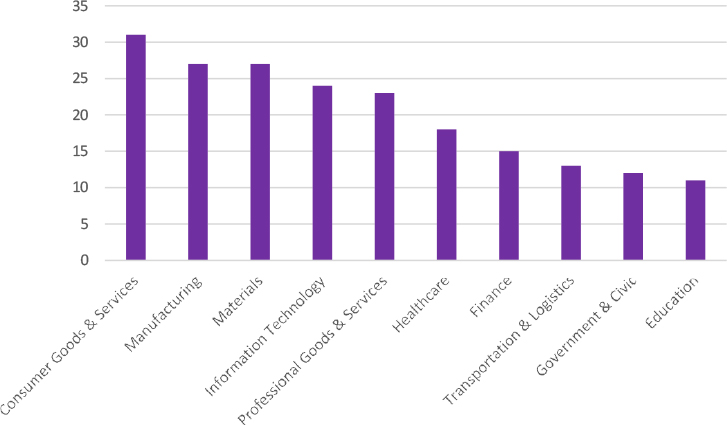
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies due to a range of vulnerabilities. The following are the top 5 most affected technologies.
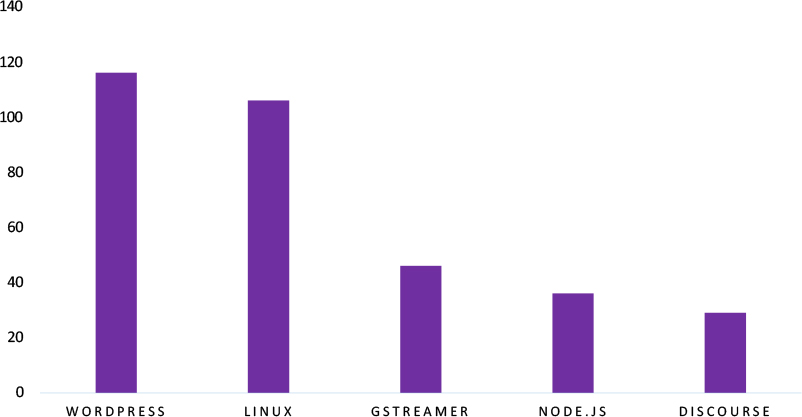
ETLM Assessment
Vulnerability in the E-Mail MFA Provider introduces significant risks to identity and access management systems that rely on multi-factor authentication to secure user accounts and critical services. As MFA mechanisms are widely deployed across enterprise applications, cloud platforms, and authentication infrastructures, exploitation of this vulnerability could allow attackers to bypass authentication controls and gain unauthorized access to protected systems. Organizations leveraging MFA-based authentication frameworks must ensure timely patching and continuous monitoring of authentication processes to detect abnormal access attempts. Addressing this vulnerability is essential to maintaining the integrity of authentication mechanisms and safeguarding sensitive organizational resources across industries and geographic regions.
Killsec Ransomware attacked and published the data of Meena Health
Summary:
Recently, we observed that Killsec Ransomware attacked and published the data of Meena Health(www[.]meena-health[.]com) on its dark web website. Meena Health is a healthcare service provider and medical group operating in the Hospitals & Healthcare industry, primarily based in Saudi Arabia. The compromised data appears to consist of highly sensitive healthcare and patient-related information, indicating a breach of medical records. The exposed dataset includes structured directories, such as laboratory results, radiology reports, prescriptions, and sick leave documents, suggesting unauthorized access to an internal medical records system. The leaked files likely contain Protected Health Information (PHI), including patient identities, diagnostic results, treatment details, and official medical documents issued by healthcare providers.
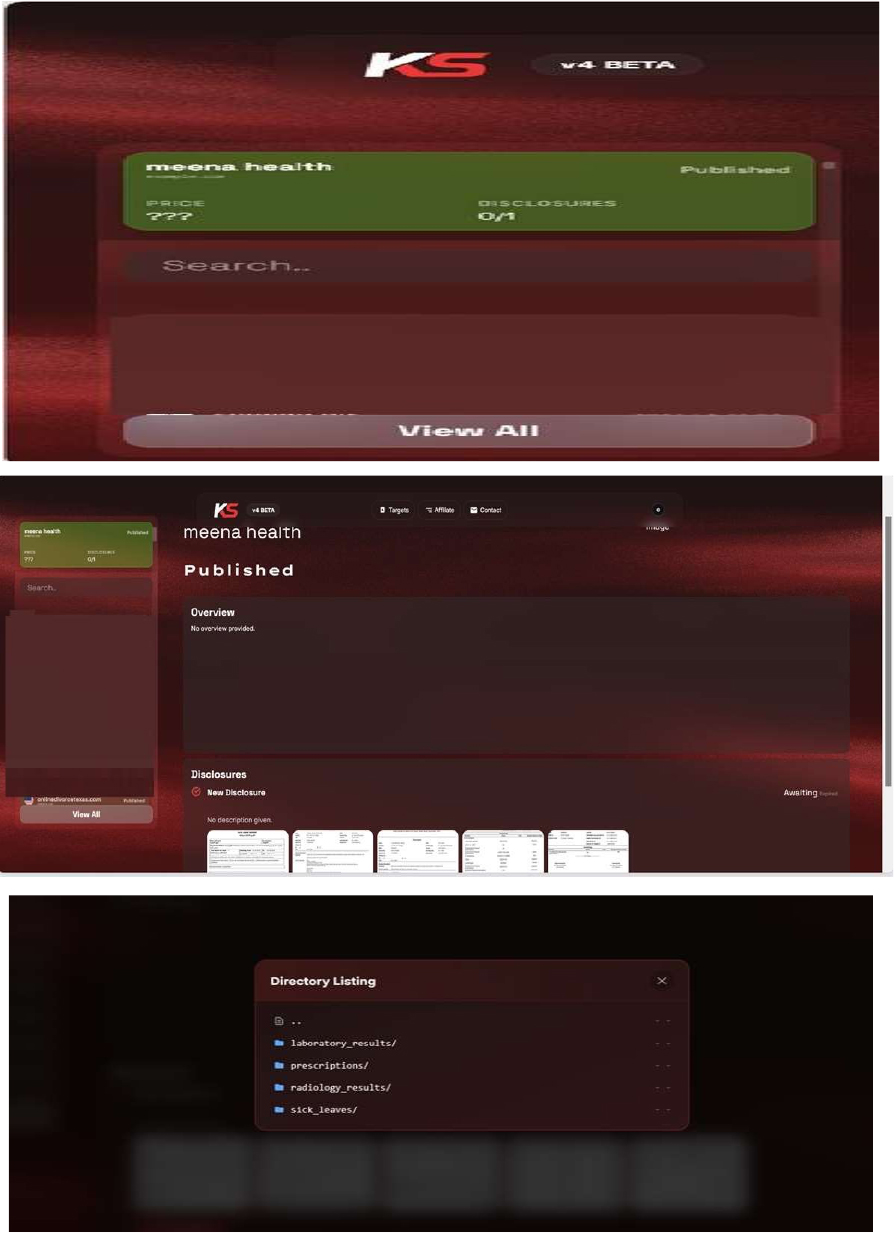
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
Koiride Data Advertised on a Leak Site
Summary:
The CYFIRMA research team identified a post on a dark web forum by a threat actor using the alias “stalker8083”, claiming to be in possession of a large dataset allegedly associated with Koiride[.]com, a provider of airport transfer and transportation services, which has allegedly been compromised in a massive data breach. The incident involves an unidentified individual who recently posted on a cybercrime forum, claiming to possess a database containing 47 million rows of sensitive company information and offering it for sale for $1,000.
The allegedly compromised data encompasses extensive records pertaining to both drivers and passengers. According to the actor, the exposed information includes:
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
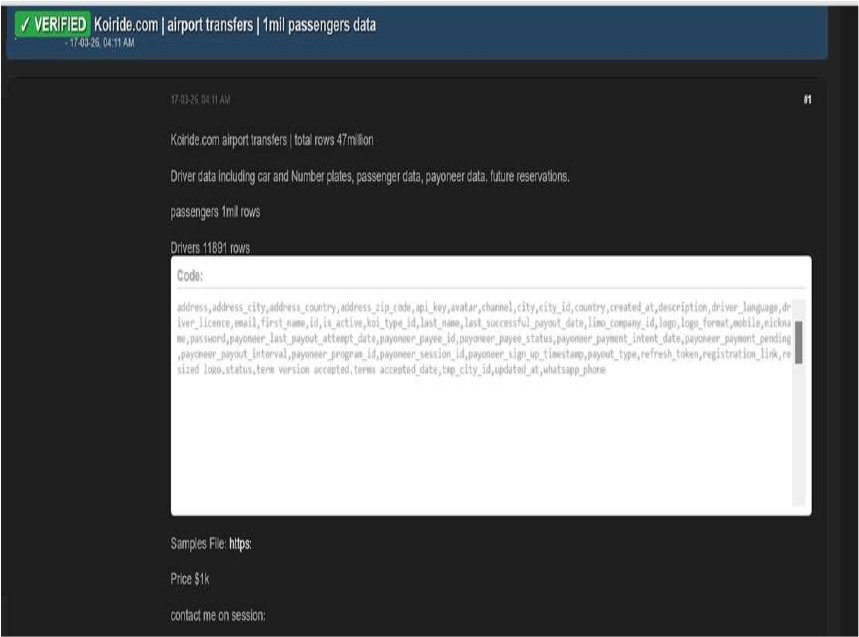
Source: Underground Forums
Usha International Limited Data Advertised on a Leak Site
Summary: The CYFIRMA research team identified a post on a dark web forum by a threat actor operating under the alias “Alpha02z”, advertising the sale of a database allegedly belonging to Usha International Limited, a major Indian consumer durables and manufacturing company. The threat actor claims that the dataset contains sensitive employee and infrastructure-related information and is being offered for sale at a price of $10,000 USD. The post suggests that the data is being sold as a one-time transaction, indicating exclusivity and potential urgency for buyers.
According to the forum post, the dataset includes a wide range of personally identifiable information (PII) and employee-related records, such as:
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
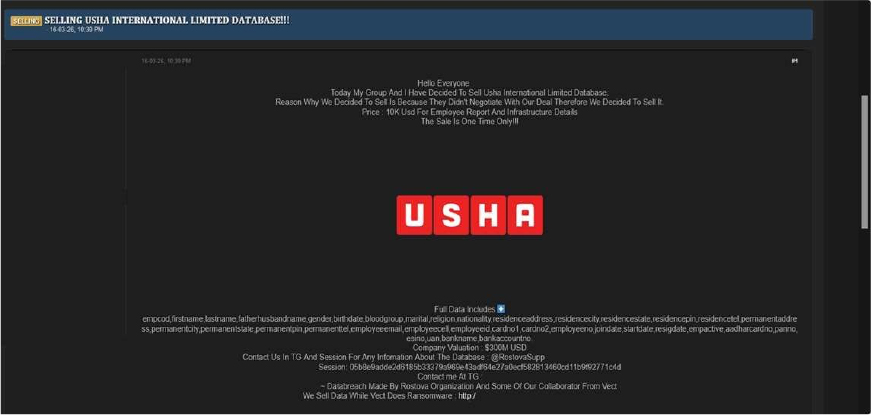
Source: Underground Forums
Relevancy & Insights:
Financially motivated cybercriminals are continuously looking for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to gain access and steal valuable data. Subsequently, the stolen data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor operating under the alias “Alpha02z” is considered an active entity within underground cybercriminal forums, primarily engaged in the sale and distribution of allegedly compromised data. Various reports link this actor to multiple incidents involving claimed unauthorized access to organizational systems and the advertisement of stolen datasets on dark web marketplaces. Their activities reflect the ongoing and evolving nature of cyber threats originating from such platforms, where sensitive information is monetized. These developments emphasize the need for organizations to strengthen their cybersecurity posture through continuous monitoring, the use of advanced threat intelligence, and the implementation of proactive security measures to safeguard critical data and infrastructure.
Recommendations: Enhance the cybersecurity posture by:
The CYFIRMA research team identified a post on a dark web forum advertising an alleged data breach involving E-accounting[.]co[.]kr, a South Korea-based SaaS company. The post was published by a threat actor using the alias “888”, who claims responsibility for compromising the organization and exfiltrating its source code. The actor is offering the data for download, including a sample file, indicating an attempt to distribute or monetize the stolen information.
Details of the Alleged Compromise According to the forum post:
The post includes references to downloadable content, suggesting that the data is already accessible to other threat actors.
Type of Compromised Data
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
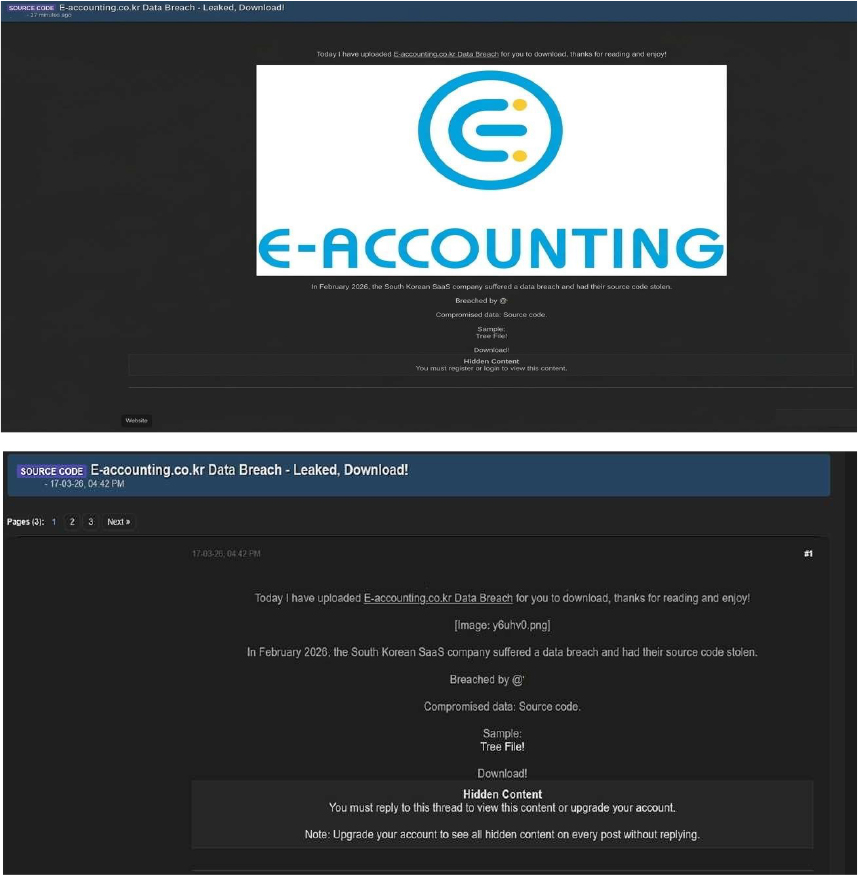
Source: Underground Forums
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
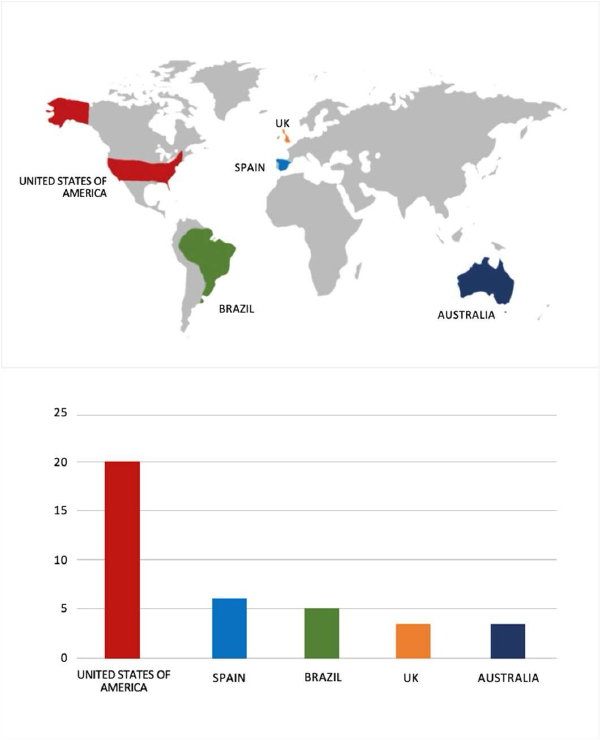
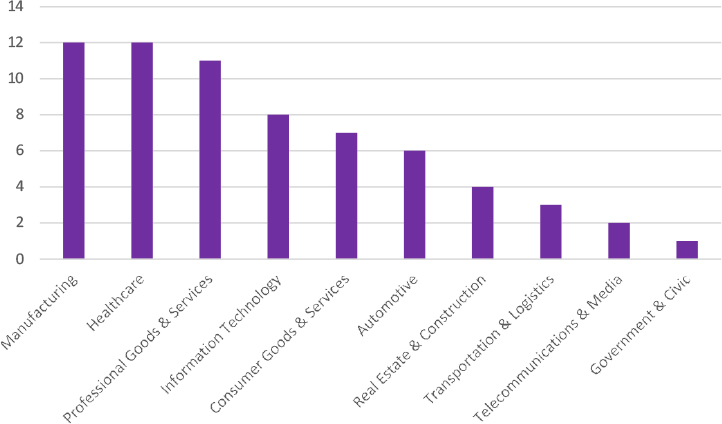
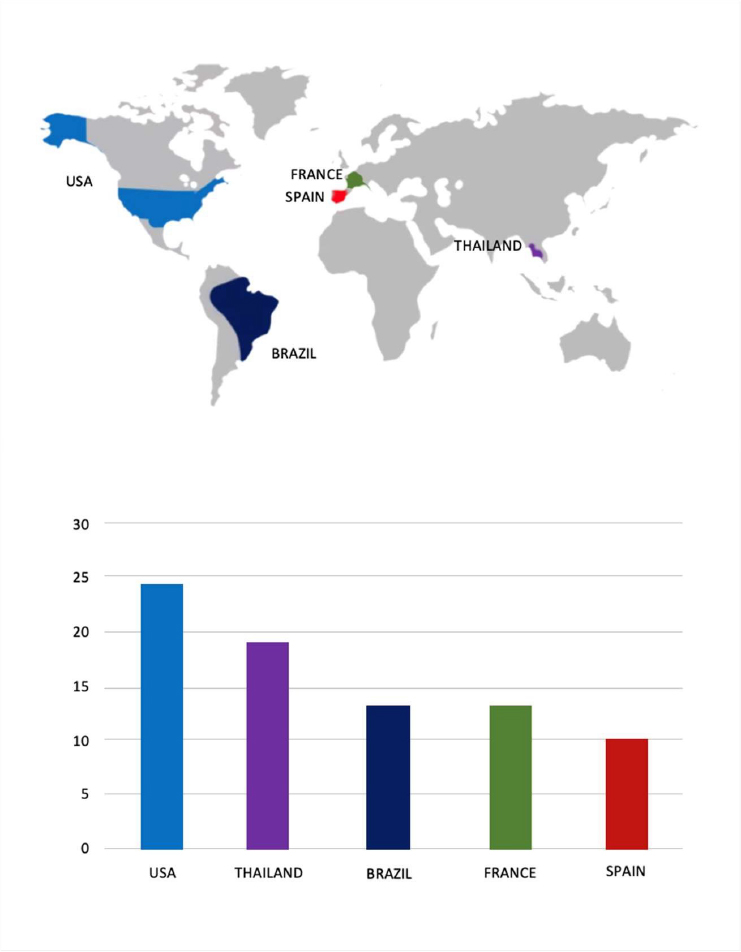
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
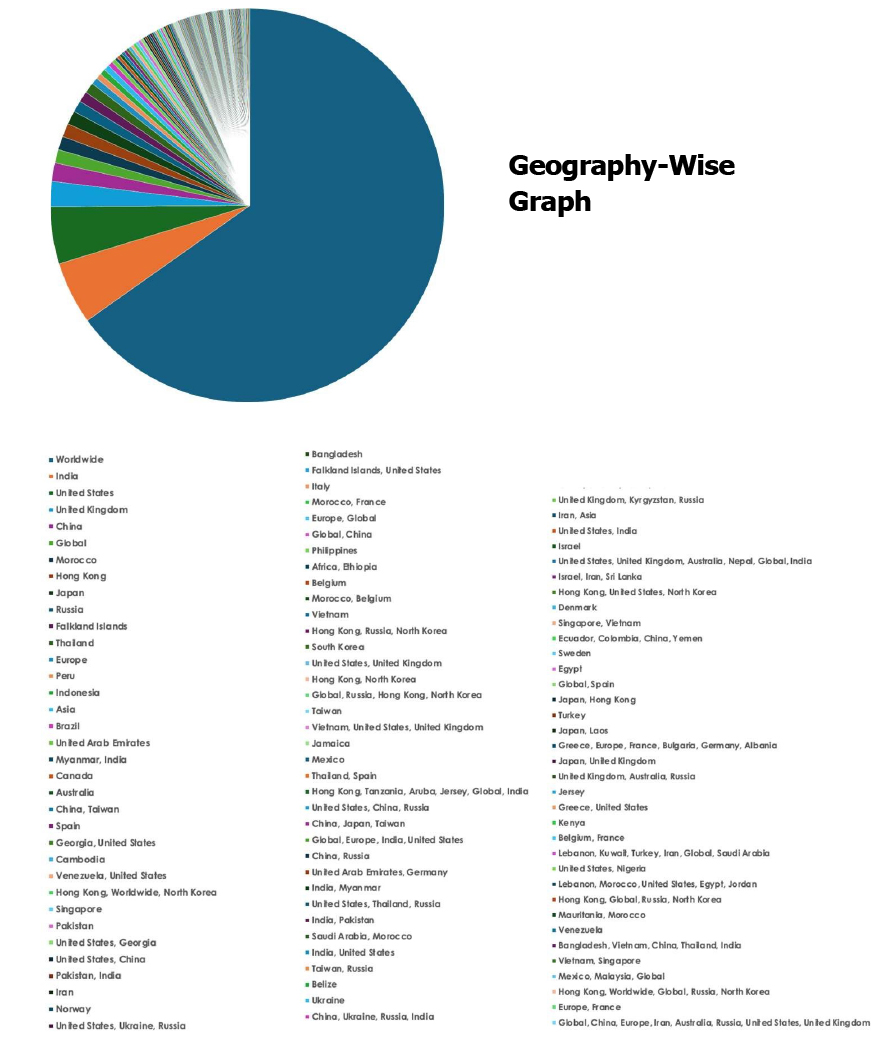
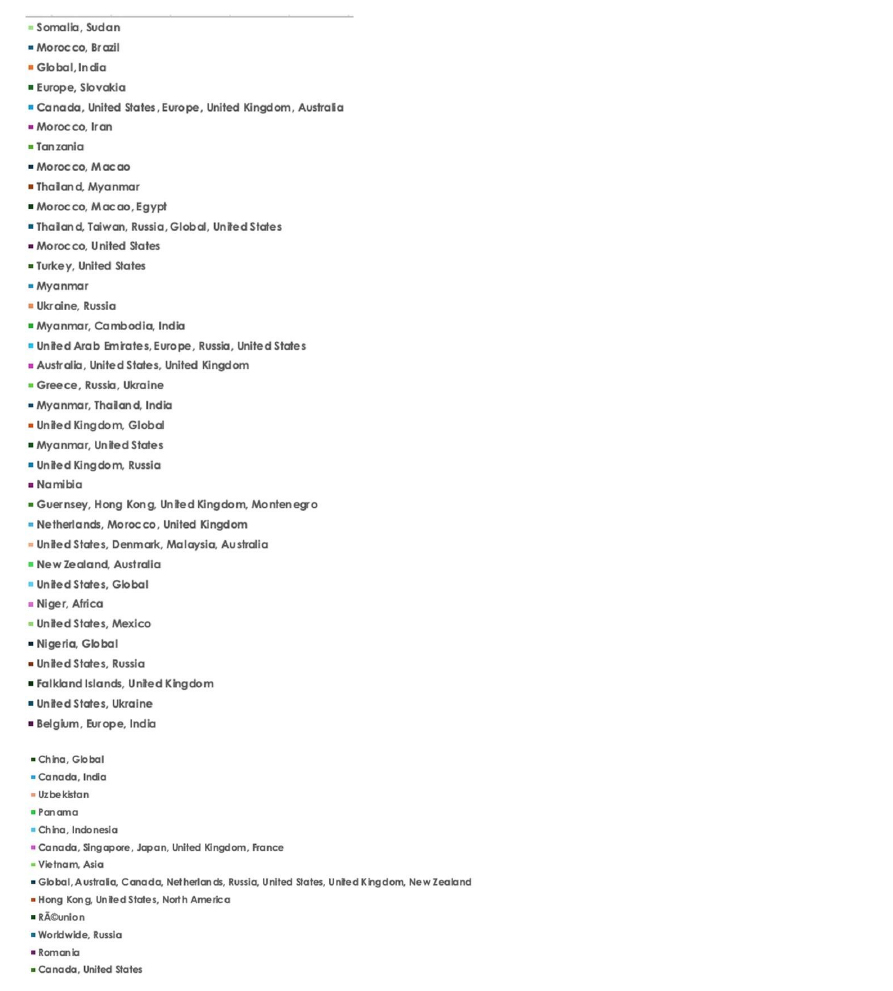
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.