


The CYFIRMA Industries Report delivers original cybersecurity insights and telemetry- driven statistics of global industries, covering one sector each week for a quarter. This report focuses on the manufacturing industry, presenting key trends and statistics in an engaging infographic format.
Welcome to CYFIRMA infographic industry report, where we delve into the external threat landscape of the manufacturing industry over the past three months. This report provides valuable insights and data-driven statistics, delivering a concise analysis of attack campaigns, phishing telemetry, and ransomware incidents targeting the manufacturing industry.
We aim to present an industry-specific overview in a convenient, engaging, and informative format. Leveraging our cutting-edge platform telemetry and the expertise of our analysts, we bring you actionable intelligence to stay ahead in the cybersecurity landscape.
The manufacturing industry organizations were involved in 37 out of the 72 observed campaigns (51%) during the same time period, which is a significant number compared to other industries.
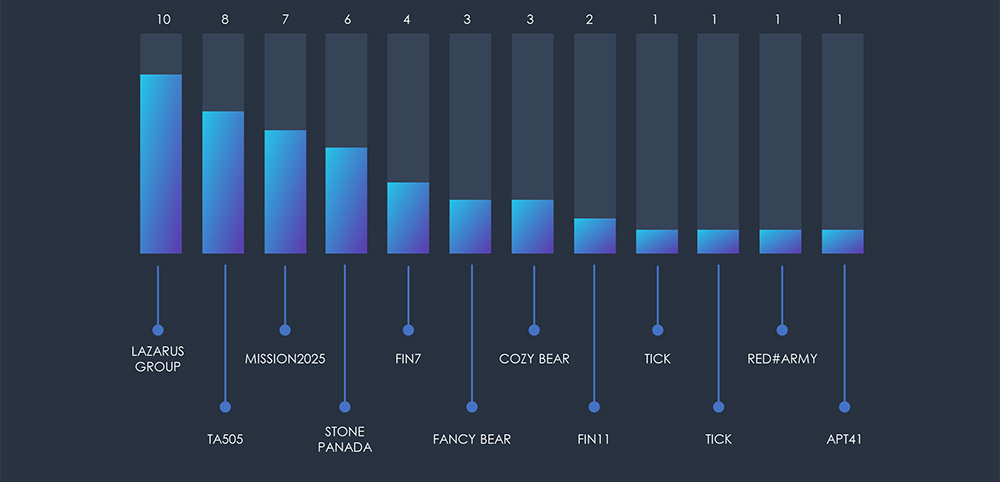
The noticeable increase in campaign activity during June and July aligns with the discovery of the Barracuda ESG vulnerability. There was also a higher level of activity from the Lazarus Group and a series of ransomware incidents involving the threat actors FIN7, FIN11, and TA505.

Alongside Lazarus Group, FIN7, FIN11, and TA505, there are multiple suspected threat actors, including various APTs tied to the Chinese nexus of nation-state activity, notably Stone Panda. It’s important to highlight that MISSION2025 serves as a central point for Chinese APT operations, with several instances of “Pandas” suspected to overlap with it.
The attack campaigns that focus on organizations in the manufacturing sector align with the strategic objectives of the nation-state APTs in question. Among the regions targeted, European Union (EU) countries emerge as the primary focal point, trailed by Japan and the USA. This trend mirrors the distribution of the manufacturing industry across these nations.
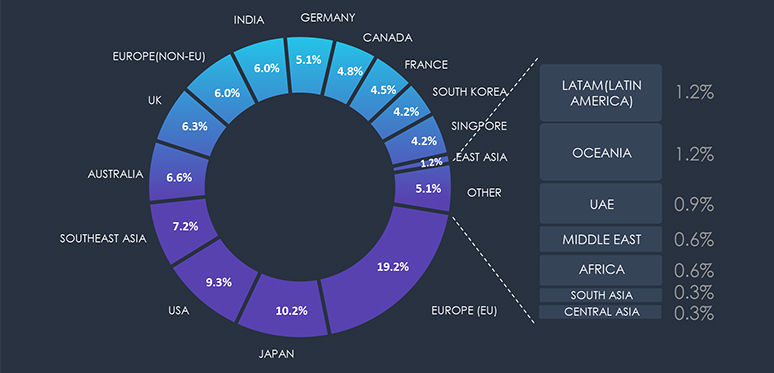
Due to the overlapping nature of monitoring telemetry, further breakdown beyond the top 10 countries is calculated for regions rather than individual countries to maintain clarity.
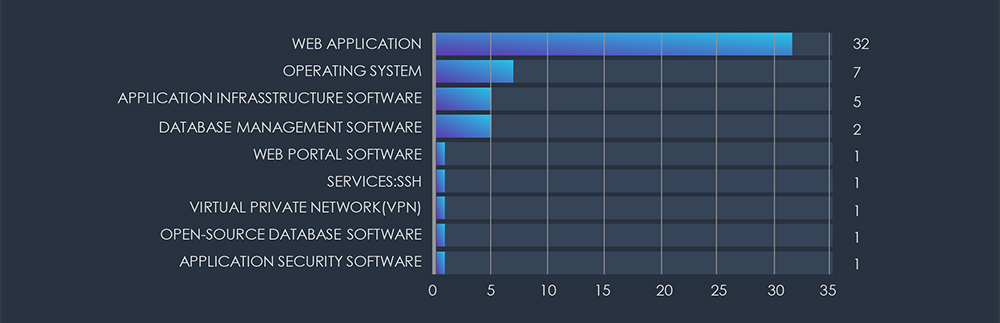
Examining the targeted technologies, it’s evident that APTs primarily center their attention on exploiting Web Applications, rendering them the primary focal point of their attacks. Subsequently, Operating Systems also emerge as notable targets, underscoring their persistent vulnerabilities. Furthermore, databases and remote access solutions are subject to their attacks as well.
Phishing campaigns explicitly targeting or impersonating the manufacturing industry are rare. Manufacturing is heavily targeted through tailored spear-phishing by APTs and Ransomware gangs, but they are seldomly involved in entire campaigns as they do not present a good lure due to the nature of their business.
Over the past 3 months, CYFIRMA’s telemetry recorded only 19 phishing attacks out of a total of 224,591 making up 0.0084% of all phishing attack campaigns observed. Number is so small we do not track manufacturing as category in the chart below.
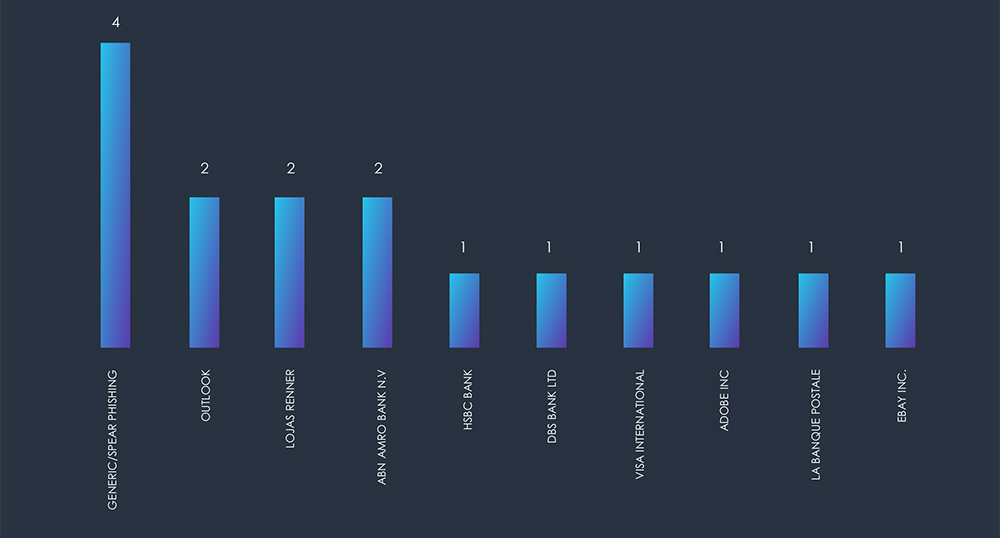
Out of 19 observed phishing attacks only 3 were impersonating manufacturing brands.

Besides generic phishing, including Outlook and Adobe, local banks appear to be a popular phishing lure in spear-phishing attempts on businesses.
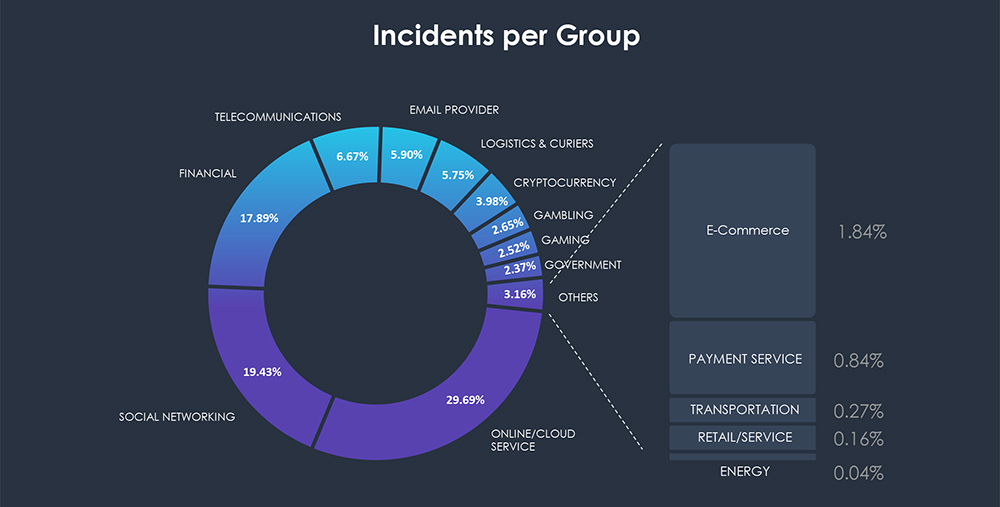
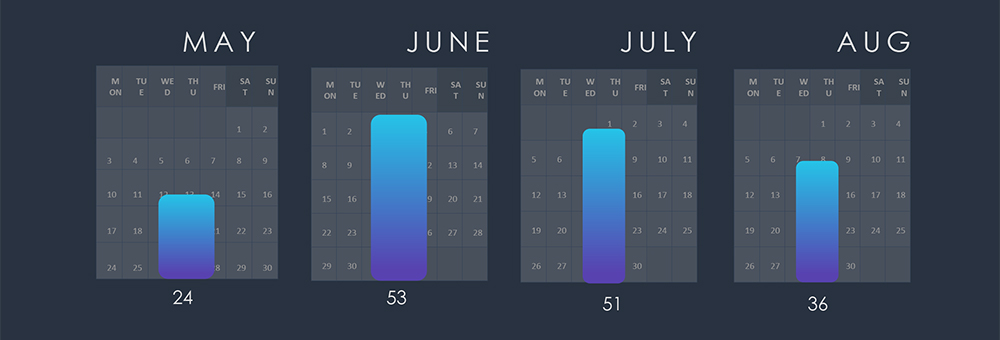
In the past 90 days, CYFIRMA has identified 164 verified ransomware victims within the manufacturing industry sectors. This accounts for 10.6% of the total of 1,541 ransomware incidents during the same period. In other words, every tenth ransomware victim is a manufacturing business.
Chart below shows consistently high numbers of attacks, when adjusted for partial months in May and August.
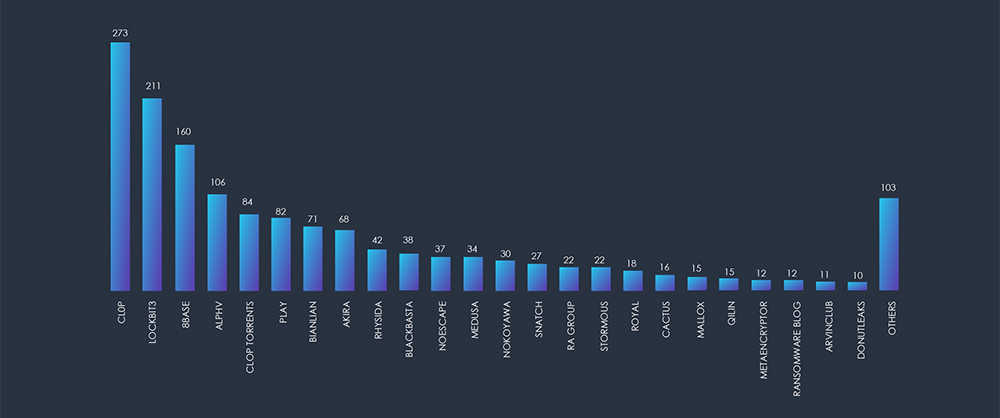
Cl0p gang is taking the lead as shown in the breakdown chart below. Note that Cl0p and Cl0p Torrents are separately tracked, adding to 34 total victims. Additionally, the chart highlights that the major groups, namely Lockbit3, Play, 8Base, ALPHV etc. are accountable for majority of the attacks. In total there were 25 different ransomware gangs reporting manufacturing victims in last 90 days.
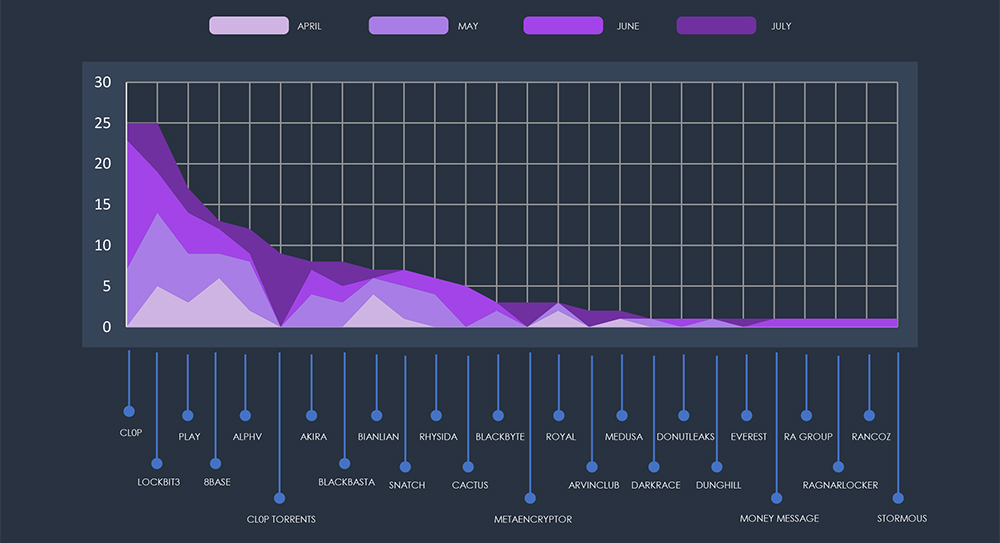
The subsequent chart underscores the dominance of major ransomware gangs, with the top 5 accounting for 61% of all victims. Simultaneously, the chart illustrates how the collective activity of smaller groups contributes to a substantial number of victims.
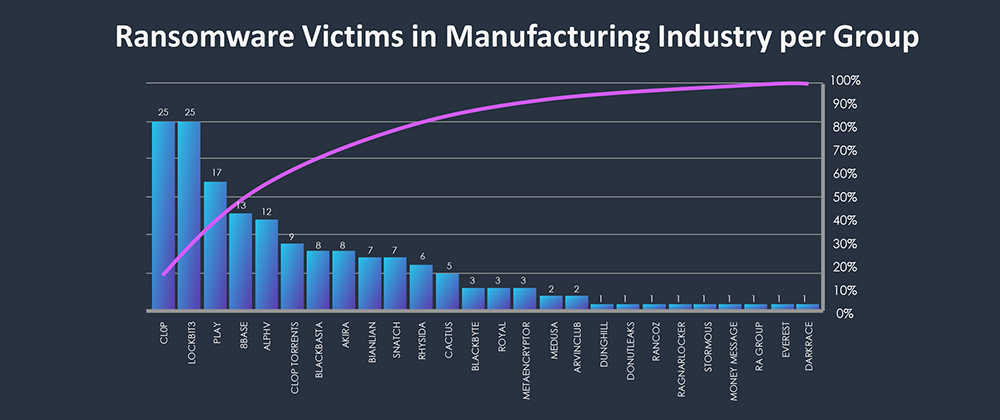
From 46 gangs active in past 90 days, 25 recorded verified manufacturing victims. This is significant portion compared to other industries. Average gang participation is between 12-15 for industry.
Share of groups targeting manufacturing align with total numbers of reported victims per gang.
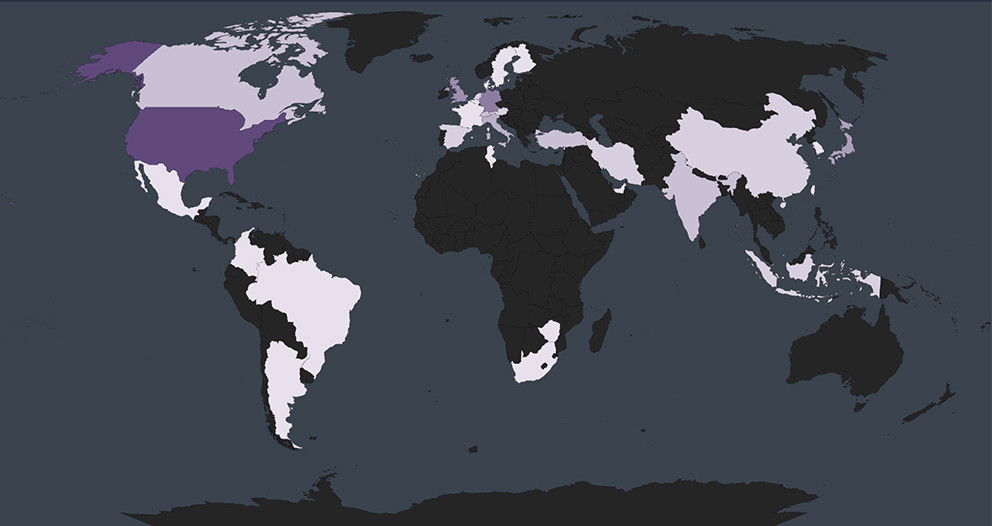
Global Spread – Out of the 164 victims identified, the United States emerges as the most affected with 86 victims. Following are countries known for their robust manufacturing – Germany (15 victims), UK (8 victims), Japan (6 victims) and Italy (5 victims)
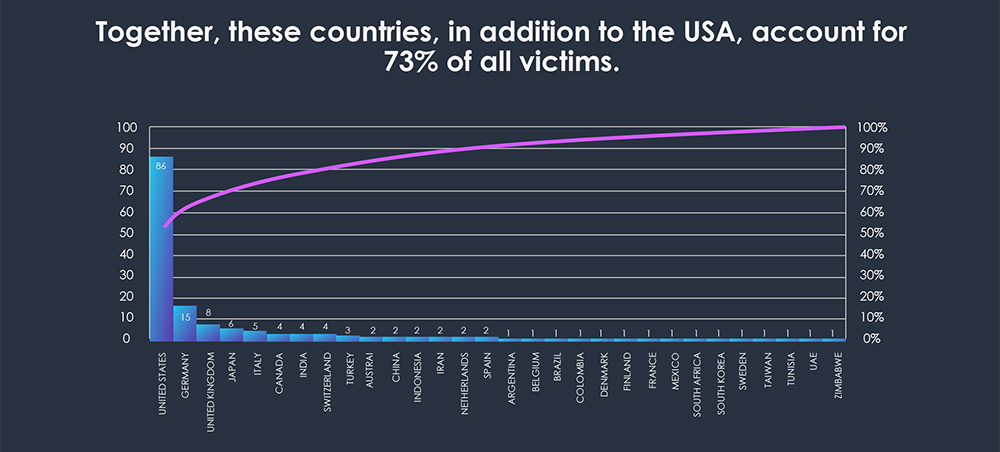
Geographical Vulnerability – The distribution of victims serves as a reminder that no region is exempt from ransomware threats. Cyber attackers have the capability to breach and target vulnerable organizations globally. This trend indicates that many threat actors prioritize exploiting vulnerabilities within organizations, regardless of their geographical locations.
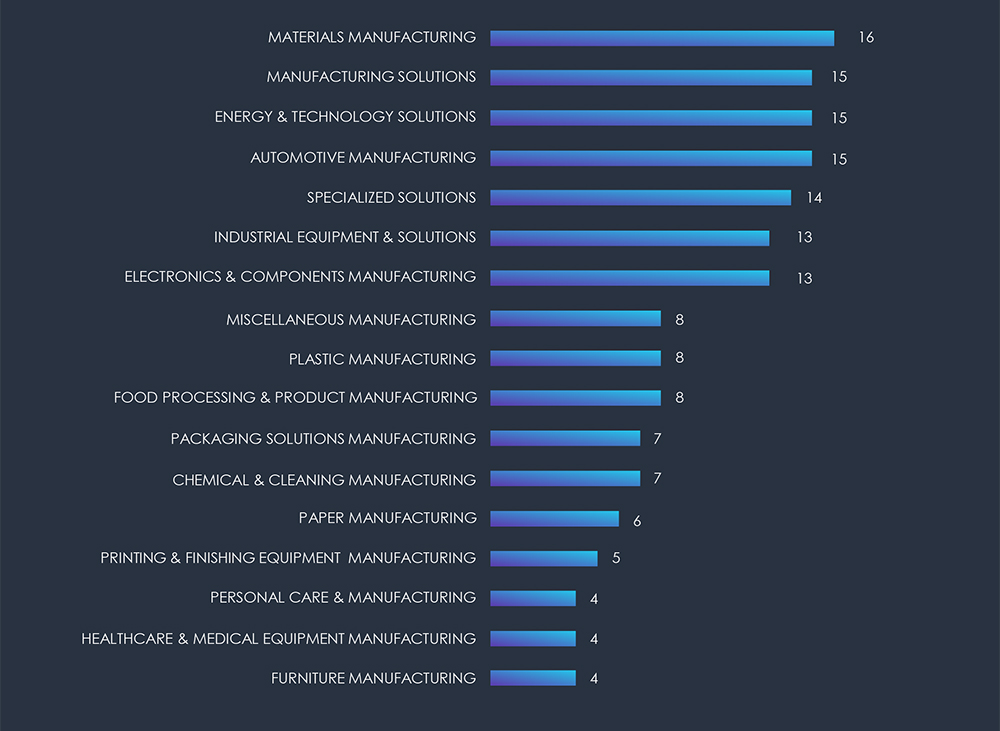
The chart below illustrates the distribution of ransomware incidents over the past 90 days, portraying a diverse array of sectors within manufacturing.
The manufacturing industry stands out as a particularly vulnerable sector, frequently falling prey to ransomware attacks and being a prime target for nation-state APTs engaged in espionage campaigns.
This susceptibility is not merely speculative; our data telemetry underlines this concern. Statistical analysis showns that 1 in every 10 victims of ransomware incidents operates within the manufacturing sector.
Due to the nature of manufacturing business, it does not make for a good phishing lure, hence businesses are rarely impersonated. However regional banking organizations are popular impersonation choice to spear-phish manufacturing businesses.
In essence, the manufacturing industry confronts a unique and pronounced cyber threat landscape, characterized by an elevated vulnerability to ransomware assaults and a discernible interest from nation-state actors.