

The CYFIRMA research team has identified an infostealer builder known as ‘Blank Grabber’ while monitoring threat actor discussions. It was released in 2022, however since then, it has been frequently updated – with 85 contributions to the project in the last one month alone. The infostealer targets Windows operating systems and possesses a wide range of capabilities aimed at stealing sensitive information from unsuspecting users (including Discord tokens, Steam and Epic sessions, browser data such as passwords, cookies, and history, as well as various other credentials and system information). The tool is also equipped with features to evade detection, disable security measures, and maintain persistence on compromised systems. Once deployed, the Blank Grabber can result in unauthorized access and theft of valuable information, including user credentials, intellectual property, and sensitive data, with potential damage, including financial losses, reputational harm, and compromised business operations.
Blank Grabber was being vouched for by an experienced black hat malware developer/reverse engineer, who is a part of the “Stealer Developers” community. The developer of this infostealer has kept the project ‘open source’, which means that the priority of the operator is developing a reputation in the industry, rather than financial gains. The CYFIRMA research team has noted that threat actors have added this infostealer to their malware arsenal and are launching campaigns in the wild to compromise suitable targets. In this research report, we will talk about the capabilities of this malware and what organizations must do to proactively prevent these threats.
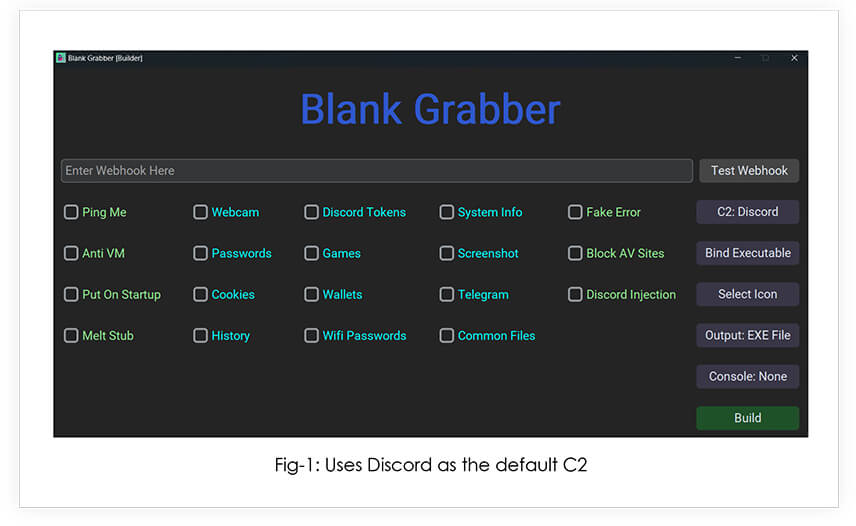
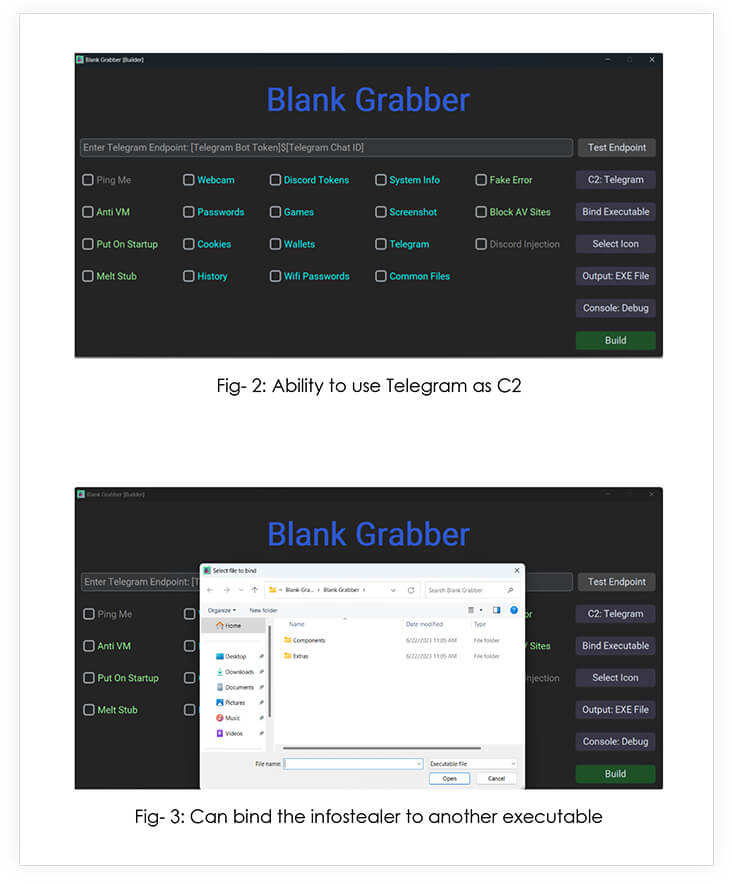
The builder code is a batch script that checks for the presence of Python and several Python libraries and installs them if they are not found. The script then starts the Python script gui.py (the builder GUI).
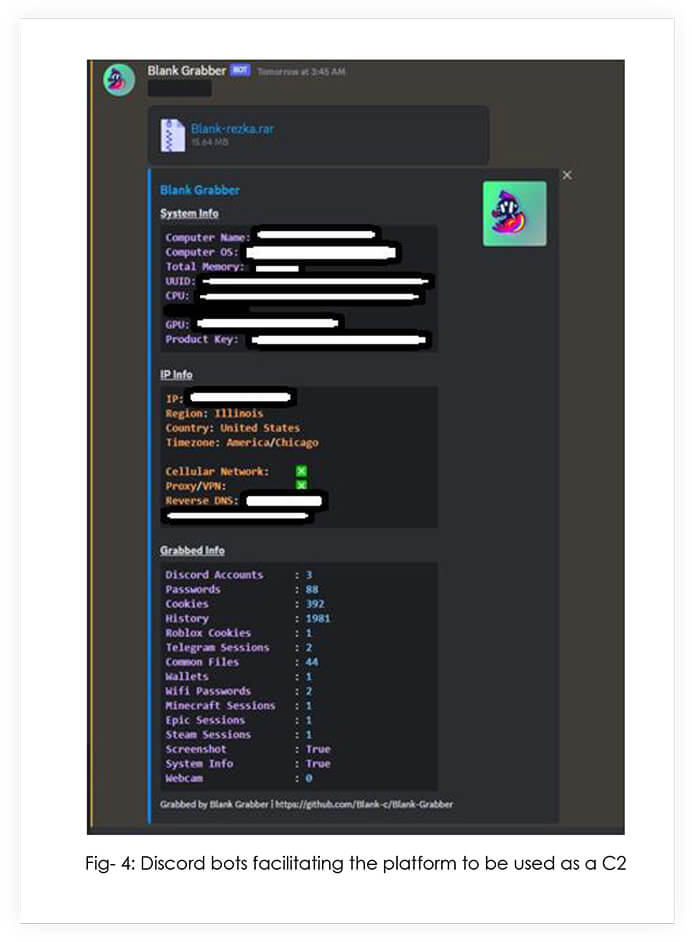
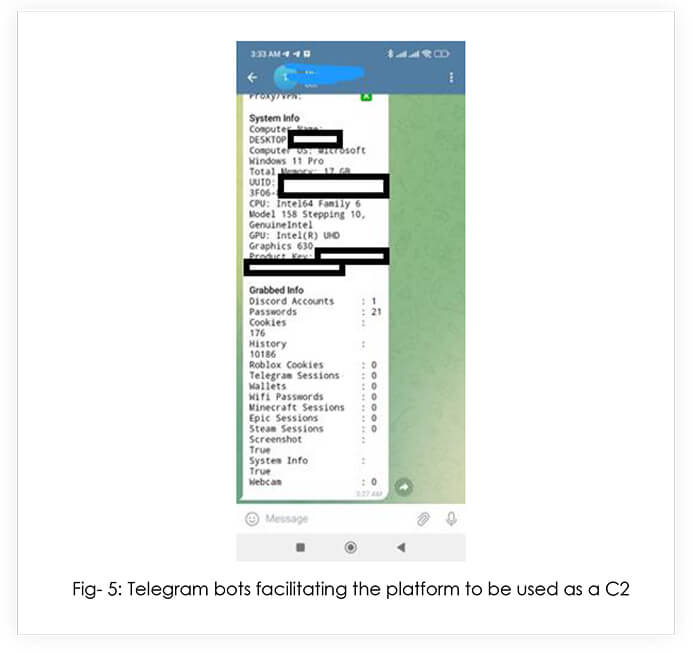
Upon execution, the infostealer harvests all the data, compresses it and sends it over to the C2 as a password protected .rar file that has a hardcoded password.
Below are some of the key features of the infostealer:
Threat Actor Profile: The operators behind the Blank Grabber infostealer are advanced and skilled malware developers, possessing a deep understanding of evasion techniques and data exfiltration methods. Their motivation is likely to build a rapport within the cybercriminal community as an entry strategy to a larger threat actor group.
Threat Landscape: The threat landscape for information stealers like the Blank Grabber is evolving and increasingly sophisticated. Cybercriminals continuously develop and distribute such tools to exploit vulnerabilities in systems and applications. The widespread use of social engineering, phishing, and malware distribution techniques amplify the risk of users inadvertently downloading and executing such stealers. Threat actors may leverage underground markets and forums to sell stolen information or use it for further malicious activities. The infostealer is being maintained by multiple developers, including the creator using the alias “Blank” and a developer/admin of BlackForums, known as “Astounding”. It is worth noting that a black hat group known as “Threatsec” is affiliated with Blackforums, so it is likely that they have employed this stealer in their malware arsenal.
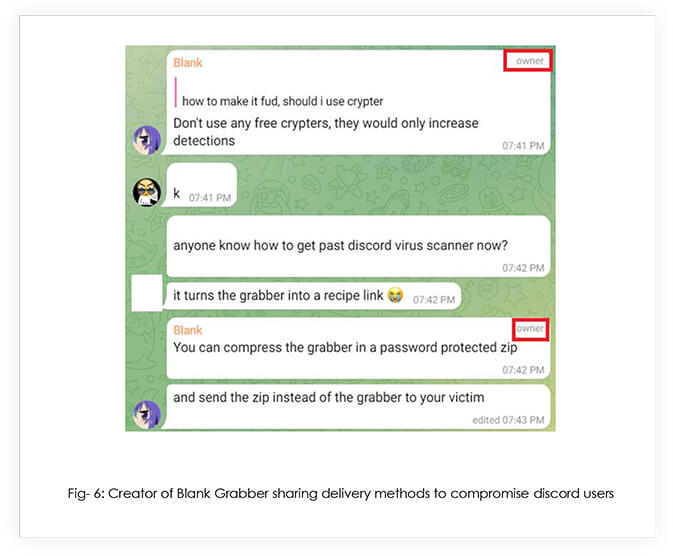
Victimology: As the malware has been gifted to the cybercriminal community by the developers, absolutely anyone is able to deploy it. Threat actors are already using the infostealer for exfiltrating data from unsuspecting users, as well as binding it with their own malware.
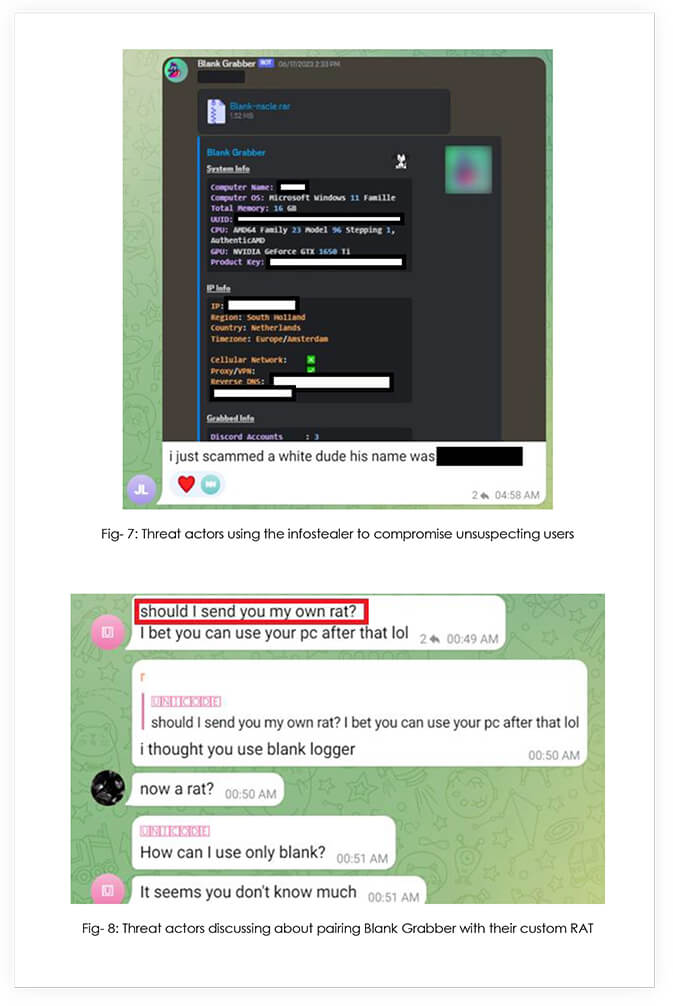
Note: CYFIRMA team was able to get the RAT being discussed above. The malware is being detected by only 1 out of 69 AV vendors. Kindly refer to the IOCs section for hash values of the RAT.
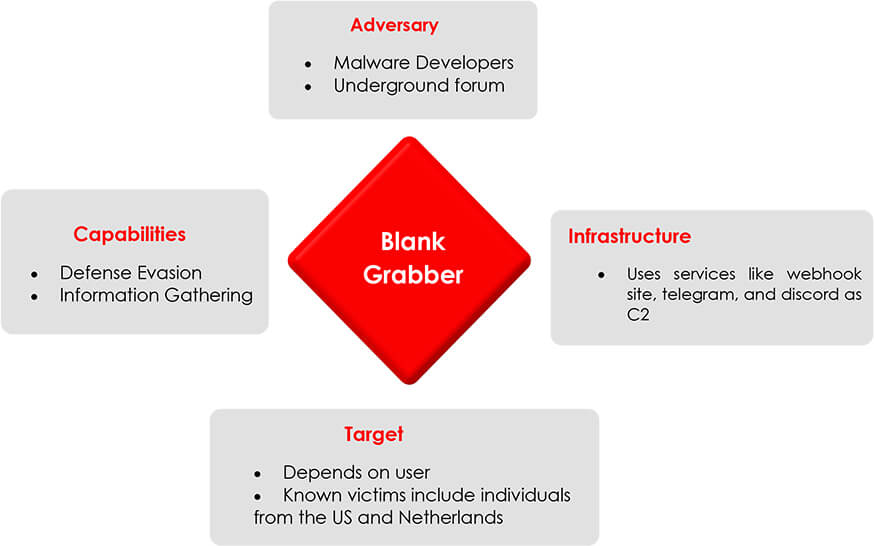
Impact Assessment: The impact of the Blank Grabber infostealer can be severe for organizations. It has the potential to compromise sensitive information, including user credentials, intellectual property, and financial data. The theft of such information can lead to financial losses, reputational damage, regulatory non-compliance, and legal consequences. Additionally, the deployment of the stealer can disrupt business operations, compromise network security, and undermine customer trust. Timely detection, effective incident response, and preventive measures are crucial to minimizing the impact of such threats.
The Blank Grabber infostealer represents a significant and evolving threat in today’s external threat landscape. Its advanced capabilities (including data exfiltration, system compromise, and evasion techniques) pose a grave risk to organizations and individuals alike, and the implications of falling victim are severe, from financial losses and reputational damage, to legal consequences and compromised business operations. Mitigating this threat requires a multi-faceted approach, including robust endpoint protection, employee awareness training, secure configurations, and incident response planning. Continual vigilance, proactive security measures, and staying informed about emerging threats are essential in safeguarding against infostealers like the Blank Grabber.
| No. | Indicator | Type | Comments |
| 1 | 7b026e20696754040ff390afa8356b6b | md5 | Compiled Malware |
| 2 | 4949588f7ee9ce7bc4a8408982865e1a5192284c | sha1 | Compiled Malware |
| 3 | 094e9745af4bf22f6ce77e3f23b722edd03e447f3810ee66de64cf5ce32f1a9e | sha256 | Compiled Malware |
| 4 | 5ade6e0edac7caf4c1913d717009f954 | md5 | Compiled Malware |
| 5 | 6b871b4522ab28435635aeb316b47254c4e20ea7 | sha1 | Compiled Malware |
| 6 | 1196c0ab10592a87191900cafe69b19e6c44f16252236d9290d5b63747876b4d | sha256 | Compiled Malware |
| 7 | 8efb75694b0150fd63d1e097b0340048 | md5 | Builder |
| 8 | 40c06827cb7aab0287ac60b2d884521ebdc87cf2 | sha1 | Builder |
| 9 | ca63867458c6dbd78c68612106068ee6dd786852fc6c7bb488840045d983c134 | sha256 | Builder |
| 10 | e1c8233b71f5b4befa0605a036c2439f | md5 | RAT used with Blank Grabber |
| 11 | 3c1ed3b56c662706f8817e62cd2f9c4466596d9a | sha1 | RAT used with Blank Grabber |
| 12 | 7a0fa7427224a98c57c65175eff4d069d4776e8aa3e2ba84f1ac53c169548ae8 | sha256 | RAT used with Blank Grabber |
title: Product Reconnaissance via Wmic.EXE status: experimental
description: Detects the execution of WMIC in order to get a list of firewall and antivirus software
author: CYFIRMA_RESEARCH date: 2023/07/06
tags:
– attack.execution
– attack.t1047 logsource:
category: process_creation
product: windows detection:
selection_img:
– Image|endswith: ‘\wmic.exe’ – OriginalFileName: ‘wmic.exe’
selection_cli: CommandLine|contains: ‘Product’
condition: all of selection_* falsepositives:
– Unknown level: medium
title: Disable Windows Defender Functionalities Via Registry Keys status: experimental
description: Detects when attackers or tools disable Windows Defender functionalities via the windows registry
date: 2022/08/01 modified: 2023/05/10 tags:
– attack.defense_evasion
– attack.t1562.001 logsource:
product: windows
category: registry_set detection:
selection_main: EventType: SetValue TargetObject|contains:
– ‘\SOFTWARE\Microsoft\Windows Defender\’
– ‘\SOFTWARE\Policies\Microsoft\Windows Defender Security Center\’ – ‘\SOFTWARE\Policies\Microsoft\Windows Defender\’
selection_dword_1: TargetObject|endswith:
– ‘\DisableAntiSpyware’
– ‘\DisableAntiVirus’
– ‘\Real-Time Protection\DisableBehaviorMonitoring’
– ‘\Real-Time Protection\DisableIntrusionPreventionSystem’ – ‘\Real-Time Protection\DisableIOAVProtection’
– ‘\Real-Time Protection\DisableOnAccessProtection’
– ‘\Real-Time Protection\DisableRealtimeMonitoring’
– ‘\Real-Time Protection\DisableScanOnRealtimeEnable’ – ‘\Real-Time Protection\DisableScriptScanning’
– ‘\Reporting\DisableEnhancedNotifications’
– ‘\SpyNet\DisableBlockAtFirstSeen’
Details: ‘DWORD (0x00000001)’ selection_dword_0:
TargetObject|endswith:
– ‘\App and Browser protection\DisallowExploitProtectionOverride’
– ‘\Features\TamperProtection’
– ‘\MpEngine\MpEnablePus’
– ‘\PUAProtection’
– ‘\Signature Update\ForceUpdateFromMU’
– ‘\SpyNet\SpynetReporting’
– ‘\SpyNet\SubmitSamplesConsent’
– ‘\Windows Defender Exploit Guard\Controlled Folder Access\EnableControlledFolderAccess’
Details: ‘DWORD (0x00000000)’
condition: selection_main and 1 of selection_dword_*
falsepositives:
– Administrator actions via the Windows Defender interface
level: high
| Sr. No | Tactics | Techniques | Procedures |
| 1 | TA0002- Execution | T1047: Windows Management Instrumentation |
|
| T1059: Command and Scripting Interpreter |
|
||
| T1129: Shared Modules |
|
||
| 2 | TA0003- Persistence | T1574.002: DLL Side-Loading | Tries to load missing DLLs |
| 3 | TA0004- Privilege Escalation | T1574.002: DLL Side-Loading | Tries to load missing DLLs |
| 4 | TA0005- Defense Evasion | T1027: Obfuscated Files or Information |
|
| T1027.002: Software Packing |
|
||
| T1070.006: Timestomp | Binary contains a suspicious time stamp | ||
| T1112: Modify Registry | Uses reg.exe to modify the Windows registry | ||
| T1497: Virtualization/Sandbox Evasion |
|
||
| T1562.001: Disable or Modify Tools |
|
||
| T1574.002: DLL Side-Loading | Tries to load missing DLLs | ||
| 5 | TA0006- Credential Access | T1003: OS Credential Dumping | Tries to harvest and steal browser information (history, passwords, etc) |
| T1056: Input Capture | Creates a DirectInput object (often for capturing keystrokes) | ||
| 6 | TA0007- Discovery | T1010: Application Window Discovery | Sample monitors Window changes (e.g. starting applications) |
| T1016: System Network Configuration Discovery | Checks the online ip address of the machine | ||
| T1018: Remote System Discovery | Reads the hosts file | ||
| T1057: Process Discovery |
|
||
| T1082: System Information Discovery |
|
||
| T1083: File and Directory Discovery |
|
||
| T1497: Virtualization/Sandbox Evasion |
|
||
| T1518.001: Security Software Discovery |
|
||
| 7 | TA0009- Collection | T1005: Data from Local System |
|
| T1056: Input Capture |
|
||
| T1115: Clipboard Data |
|
||
| 8 | TA0011- Command and Control | T1071: Application Layer Protocol |
|
| T1095: Non-Application Layer Protocol |
|
||
| T1105: Ingress Tool Transfer |
|
||
| T1573: Encrypted Channel |
|