


Suspected Threat Actors: Lazarus Group
The North Korean state-sponsored threat actor Lazarus group, was observed trying to compromise security researchers with a trojanized pirated version of the IDA Pro – an interactive disassembler popular among researchers for reverse engineering applications. As per researchers, the threat actor bundled the original IDA Pro 7.5 with two of the malicious components. The first component is an internal module named “win_fw.dll” which executes during installation of the application and eventually loads a second component called “idahelper.dll” from the IDA plugins folder on the infected system. Once executed successfully, the binary “idahelper.dll” then connects to the remote server “www[.]devguardmap[.]org” to retrieve further payloads. The domain itself has been previously linked to a similar North Korea-backed campaign targeting security professionals earlier this March.
In the past, North Korean threat actors were observed creating fake profiles/companies and leveraging social media extensively to lure victims to their cleverly crafted social engineering techniques. One such campaign – Operation Dream Job suspected to be carried out by threat actor Lazarus Group. Upon initial compromise of the victims, the suspected threat actors potentially use their systems to gain access to the network of the organization, carry out a lateral movement, implant malware, and possibly exfiltrate sensitive details. The threat actors could use the details to sell to competitors for financial gains or work in alignment with their government’s political and economic interests.
Researchers have observed JVCKENWOOD Corporation (www.jvckenwood.com) being impacted by the Conti ransomware group. As per the advertisement published on Conti’s dedicated leak site (DLS), approximately 112 gigabytes of potentially sensitive data claimed to have been exfiltrated by the ransomware group. At the time of our researchers’ observation, the ransomware group has not published samples of exfiltrated data, however, the data is expected to be leaked in the future.
The following screenshot was observed published on the dark web:
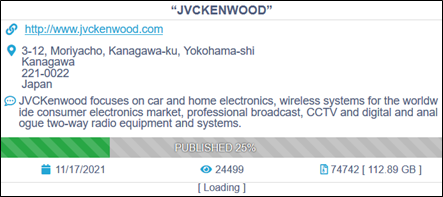
Source: Darkweb
Researchers have associated three vulnerabilities being exploited by the Conti ransomware operators which include CVE-2020-0796 affecting Microsoft products, and CVE-2018-13374 & CVE-2018-13379 existing in Fortinet’ FortiOS.
Researchers also believe that the Russian APT group Wizard Spider uses the Conti ransomware in its attacks.
The stolen data is first made available for sale to potential buyers. As the ransom payment gets delayed the ransomware operators resort to publishing parts of the data as time goes on. Ultimately, if no ransom is paid and the data is not purchased, the data is released to the public for free for everyone to download.
While most ransomware providers often put a lot of effort to establish their reputation and attempt to maintain some level of integrity likely to encourage and facilitate ransomware payments, Conti has shown atypical behavior. In recent cases, Conti did not keep up the promise after ransom payments were received from victims.
Last month, the Conti ransomware group appeared to alter its ransomware business plan by selling access to the infiltrated victim’s network. Researchers have pointed out that many of the ransomware groups are finding it hard to maintain their DLS and some are leveraging public file sharing services such mega[.]nz. However, hosting leaked data on the clear web has its downsides and such content gets taken down in a couple of days. In addition, due to Tor’s architecture, the download speed is considerably slower, and the datasets are often large. The DLS also leaves the ransomware group vulnerable to attacks. The REvil representatives recently revealed that their data-leak site was “hijacked”.
It is suspected that these difficulties are discouraging ransomware groups to continue the use of DLS style of ransomware operations and we may see more creative solutions to overcome these challenges.
Researchers highlight that some of the world’s major organizations across various sectors, including Fortune 500 and Global 500 are failing to prevent Magecart attacks. Concerning Magecart attacks, the researchers analyzed approximately 30,000 vulnerabilities in the last two years and uncovered significant weaknesses in modern security platforms as well as processes to identify and mitigate these attacks. They also noted critical security lapses where enterprises failed to disclose details on vulnerabilities and exploits found alongside their supply chain to their customers.
At least one of the top five enterprises in many verticals including retail, insurance, financial services, pharmaceuticals, media, security, and others were found to be either vulnerable or abused.
More than 1000 online shops are vulnerable, exposing their customers to skimming.
Some vulnerable or abused organizations do use anti-Magecart solutions, but these could be bypassed.
Vendor infrastructure exposes many other connected organizations to Magecart, yet vendors often fail to inform them about it early enough so they could take preventative action.
Magecart, an umbrella term for various threat actor groups targeting compromise e-commerce websites with digital skimming, e-skimming, or form jacking techniques on checkout pages to steal financial and personal data. The Magecart attackers are known to be innovative by creatively using previous techniques with new coding and tactics. They have often remained successful in evolving their TTPs, bypassing detection by automated security scanners and presenting challenges to defenders.
Most recently, the Magecart threat actor groups used browser scripts to evade detection. By leveraging an extra browser process to ensure the victim’s machine is not running under a virtual machine – they excluded researchers and sandbox environments and only allowed real victims to be targeted by the skimmer.
Researchers highlight while various Magecart threat actor groups may have different strategies to breach a website, most focus on the weakest link – the third-party vendors. They avoid directly breaching a target and delivering malicious code via a third party. Since almost any website uses one or more third-party solutions, they also lose control over the security of their website as well as increasing their attack surface.
Researchers have revealed details on a vulnerability in Intel Processors that affects laptops, cars, and embedded systems. The vulnerability tracked as CVE-2021-0146 has been discovered in Pentium, Celeron, and Atom processors of the Apollo Lake, Gemini Lake, and Gemini Lake Refresh platforms. These chips power laptops, mobile devices, embedded systems, medical devices, and a variety of internet of things (IoT) offerings. The flaw arises from a debugging or testing functionality with excessive privileges, allowing attackers to read encrypted files.
An exploit would allow the attacker to extract an affected device’s encryption key and gain access to data. One such example of a real attack scenario includes lost or stolen devices that contain encrypted confidential information.
Researchers highlight the vulnerability is particularly concerning because it facilitates the extraction of the root encryption key used in Intel’s Platform Trust Technology and Enhanced Privacy ID technologies, which are used to protect digital content from illegal copying.