Suspected Threat Actors: Gamaredon (aka Gamaredon Group, Armageddon)
The Ukrainian Security Service (SSU) has recently disclosed the real identities of five members of the Gamaredon APT group – allegedly involved in cyberattacks against its government agencies – and linked to the Crimean branch of the Russian Federal Security Service (FSB). As per the officials, Gamaredon operating from the city of Sevastopol, Crimea, however, acted on orders from the FSB Center for Information Security (aka Center 18) in Moscow – a known FSB’s cyber operations hub. According to SSU, the threat actor group has carried approximately 5,000 cyberattacks against Ukrainian entities, targeting critical infrastructure (power plants, water facilities), harvesting classified information from government agencies, conducting misinformation campaigns, and disrupting IT systems. The five individuals have been described as “officers of the ‘Crimean’ FSB, as well as traitors who sided with the enemy during the occupation of the peninsula in 2014.”
Researchers highlight those previous reports from multiple cyber-security researchers have linked the Gamaredon to a suspected Russian government entity, the SSU reports marks the first time that the Gamaredon group has been linked to the FSB.
Reports from earlier this year containing new evidence described the Russia-linked threat actor Gamaredon as a hacker-for-hire group that offers its services to other APT actor groups. The group is considered to be highly active and has been exposed several times, however, it continues to operate and collaborate with other threat actor groups.
The TTPs employed by Gamaredon are commonly observed in the cyber crimeware world. The SSU report also reveals the group lacks complexity in terms of architecture and implementation, the tools leveraged are not sophisticated but proven to be quite effective.
The researchers once again found CDSL (Central Depository Services Limited) exposing sensitive personal and financial data of approximately 43.9 million investors that were previously reported by the same researchers. The exposed data was of individuals who did their market securities KYC. CDSL’s CVL (CDSL Ventures Limited) is one of the top KYC registration agencies. The exposure was due to an authorization vulnerability in one of the public CDSL’s KYC API. The exposed data is said to have included full name, PAN, gender, marital status, father/spouse’s full name, Date of Birth, nationality, residential address, permanent address, contact number(s), email address, occupation details, and sensitive financial details.
As per the researchers, the nature of data exposed is extremely sensitive and therefore valuable to attackers who can leverage this type of data for a range of malicious activities against individuals and organizations. The exposed data is virtually a treasure trove for cybercriminals and aid in phishing, Business Email Compromise (BEC), extortion calls, and a range of online scams such as income tax refund scams.
Researchers also suspect the data may also be used to influence the Indian share market by spreading misinformation. Armed with exposed investor details, it would be fairly easier for malicious actors to disrupt and manipulate the share markets
The incidents highlight the importance of securing critical information. Organizations are susceptible to cyber-attacks targeting their critical data. Organizations should take appropriate security measures to protect such data as it is one of the major gold mines for hackers if they get access to them. The attackers are likely to re-purpose the data, sell to potential competitors for financial gains, and may utilize the exfiltrated data to perform tailored attacks targeting affected users for further exploitation.
At the start of September, researchers revealed details of about a set of 16 vulnerabilities collectively called BrakTooth that impact the Bluetooth software stack that ships with SoC boards from several popular vendors. These vulnerabilities have also released both the test kit and full exploit code. As per researchers, the flaw affects approximately 1,400 chipsets used in billions of devices such as smartphones, personal computers, toys, internet-of-things (IoT) devices, and industrial equipment – that rely on Bluetooth Classic (BT). Initially, a group of 16 vulnerabilities was disclosed which now counts up to 22. The PoC has been made available on GitHub and requires an off-the-shelf ESP32 board, custom Link Manager Protocol (LMP) firmware and a computer to run the PoC tool.
Since the disclosure of these vulnerabilities, subsequent research revealed additional vulnerable devices for example iPhones, Macbooks, Microsoft Surface laptops, Dell desktop PCs and laptops, Sony and Oppo smartphones, audio devices from Walmart, and Panasonic among other devices. While some of the vulnerabilities were patched, however, the researchers highlight it is highly probable that many other products (beyond the 1400 entries initially observed) are affected by BrakTooth. This includes including BT system-on-chips (SoCs), BT modules, or additional BT end products.
DC RAT is a new commodity remote access trojan (RAT) seen in the wild since 2019. The RAT is spread via a Word Document that contains a malicious VBA script. The RAT is written in C#. The functionalities of this RAT are:
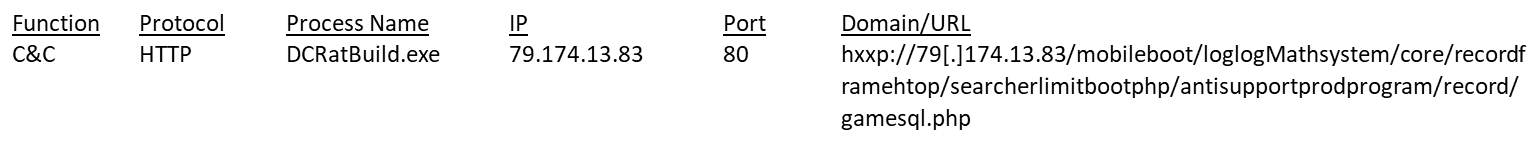
Blacklisted URL: hxxp://79[.]174.13.83/mobileboot/loglogMathsystem/core/recordframehtop/searcherlimitbootphp/antisupportprodprogram/record/gamesql.php
Risk Score: 10
Confidence Level: High
Associated Malware: DCRAT (Dark Crystal RAT)
Function: DCRAT C&C
ITW Associations: Multiple
Associated Hash (MD5): a34646571ad75adc271ad82ed1c7b17f
File Name: DCRatBuild.exe
File name: DCRatBuild.exe
MD5: a34646571ad75adc271ad82ed1c7b17f
SHA1: e7a3a315663615467dad88461d400fa948952353
SHA256: eefa40668ca7dbe2ba10f46451549055273d9764b75446360e8a962038b7c014
Kernel32.dll
gdiplus.dll
DCRatBuild.exe
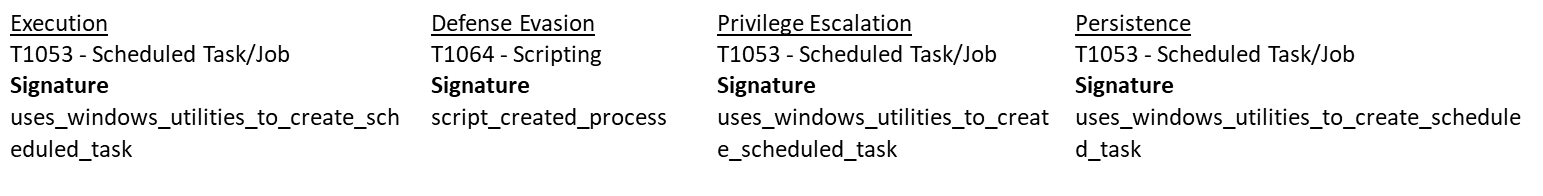
– Uses Task Scheduler to run other applications (Malicious)
– Connects to CnC server (Malicious)
– DCRAT was detected (Malicious)
– Reads the computer name (Suspicious)
– Checks supported languages (Suspicious)
– Executable content was dropped or overwritten (Suspicious)
– Creates files in the user directory (Suspicious)
–Writes files like Keylogger logs (Suspicious)