


CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple – industries, geography, and technology – that could be relevant to your organization.
Type: Ransomware
Target Technologies: Windows
Introduction
CYFIRMA Research and Advisory Team has found LockBeast Ransomware while monitoring various underground forums as part of our Threat Discovery Process.
LockBeast Ransomware
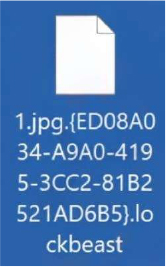
Researchers identified LockBeast as a ransomware variant designed to encrypt user data and extort payment through threats of both data loss and exposure. Once executed, it locks files using strong cryptographic algorithms, appends a victim specific identifier along with the “.lockbeast” extension, and generates a ransom note titled README.TXT. The operators behind this malware also claim to have exfiltrated sensitive data during the attack, combining encryption with data theft to increase pressure on victims.
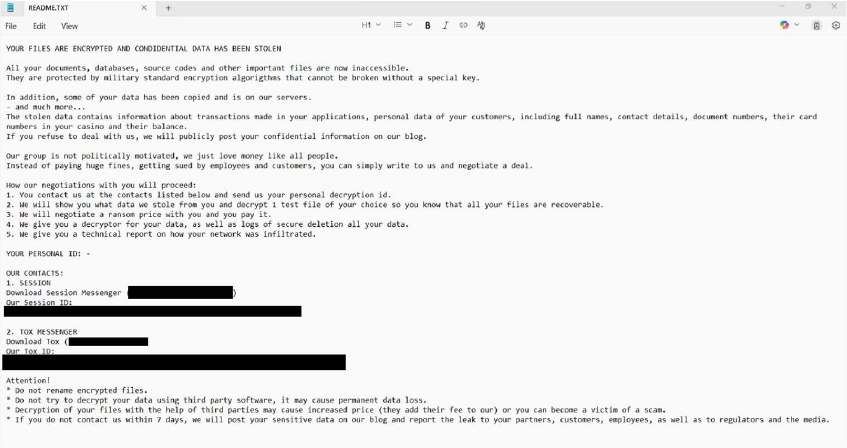
The ransom note informs victims that documents, databases, source code, and other critical files have been encrypted and that confidential information such as transaction records, personal data, and card details have been stolen. Victims are instructed to contact the attackers through privacy-focused messengers (Session and Tox) and warned not to rename encrypted files or attempt third-party decryption. A strict seven-day deadline is imposed, after which the attackers threaten to publicly release the stolen information. This combination of encryption and data leak threats forms the basis of LockBeast’s double-extortion strategy.
Following are the TTPs based on the MITRE Attack Framework
| Tactic | Technique ID | Technique Name |
| Execution | T1129 | Shared Modules |
| T1059 | Command and Scripting Interpreter | |
| T1047 | Windows Management Instrumentation | |
| Privilege Escalation | T1134 | Access Token Manipulation |
| Defense Evasion | T1027.005 | Obfuscated Files or Information: Indicator Removal from Tools |
| T1222 | File and Directory Permissions Modification | |
| T1134 | Access Token Manipulation | |
| Credential Access | T1056.001 | Input Capture: Keylogging |
| Discovery | T1082 | System Information Discovery |
| T1057 | Process Discovery | |
| T1518 | Software Discovery | |
| T1135 | Network Share Discovery | |
| T1083 | File and Directory Discovery | |
| T1007 | System Service Discovery | |
| T1614.001 | System Location Discovery : System Language Discovery | |
| T1087 | Account Discovery | |
| T1033 | System Owner/User Discovery | |
| Collection | T1056.001 | Input Capture: Keylogging |
| T1074 | Data Staged |
Relevancy and Insights:
ETLM Assessment:
CYFIRMA’s analysis highlights that LockBeast ransomware operates with a clear focus on control and intimidation. Beyond file encryption and ransom demands, its operators design the campaign to exert psychological pressure by combining data denial with reputational threats. The attackers frame negotiations as a structured process, offering limited proof of decryption and stolen data access to build credibility, while simultaneously warning of severe consequences if victims delay contact. This approach ensures that the pressure is constant, and victims feel cornered into compliance.
The ransom communication is tightly managed, relying on anonymous messengers like Session and Tox, which reduces exposure to the attackers and limits the victim’s ability to trace interactions. The seven-day deadline is not only a technical point but also a strategic element, reinforcing urgency and limiting decision-making time for the target organization. This demonstrates an operational model where timing, communication control, and leverage of stolen information are central to the attack’s impact. In the future, LockBeast could evolve by adopting additional anonymized communication channels, expanding its targeting scope across industries, and incorporating more aggressive leak site strategies to amplify pressure on victims.
Sigma rule:
title: Uncommon File Created In Office Startup Folder tags:
– attack.resource-development
– attack.t1587.001 logsource:
product: windows category: file_event
detection: selection_word_paths:
– TargetFilename|contains: ‘\Microsoft\Word\STARTUP’
– TargetFilename|contains|all:
– ‘\Office’
– ‘\Program Files’
– ‘\STARTUP’
filter_exclude_word_ext: TargetFilename|endswith:
– ‘.docb’ # Word binary document introduced in Microsoft Office 2007
– ‘.docm’ # Word macro-enabled document; same as docx, but may contain macros and scripts
– ‘.docx’ # Word document
– ‘.dotm’ # Word macro-enabled template; same as dotx, but may contain macros and scripts
– ‘.mdb’ # MS Access DB
– ‘.mdw’ # MS Access DB
– ‘.pdf’ # PDF documents
– ‘.wll’ # Word add-in
– ‘.wwl’ # Word add-in selection_excel_paths:
– TargetFilename|contains: ‘\Microsoft\Excel\XLSTART’
– TargetFilename|contains|all:
– ‘\Office’
– ‘\Program Files’
– ‘\XLSTART’
filter_exclude_excel_ext: TargetFilename|endswith:
– ‘.xll’
– ‘.xls’
– ‘.xlsm’
– ‘.xlsx’
– ‘.xlt’
– ‘.xltm’
– ‘.xlw’ filter_main_office_click_to_run:
Image|contains: ‘:\Program Files\Common Files\Microsoft Shared\ClickToRun\’
Image|endswith: ‘\OfficeClickToRun.exe’ filter_main_office_apps:
Image|contains:
– ‘:\Program Files\Microsoft Office\’
– ‘:\Program Files (x86)\Microsoft Office\’ Image|endswith:
– ‘\winword.exe’
– ‘\excel.exe’
condition: ((selection_word_paths and not filter_exclude_word_ext) or (selection_excel_paths and not filter_exclude_excel_ext)) and not 1 of filter_main_*
falsepositives:
– False positive might stem from rare extensions used by other Office utilities. level: highlevel: high (Source: Surface Web)
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems.
STRATEGIC RECOMMENDATION
MANAGEMENT RECOMMENDATION
TACTICAL RECOMMENDATION
Type: Loader| Objectives: Malware Distribution |Target Technology: Windows OS |Target Geographies: Taiwan, Mexico
CYFIRMA collects data from various forums based on which the trend is ascertained. We identified a few popular malwares that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week “QuirkyLoader” is trending.
About Malware QuirkyLoader
Researchers have identified QuirkyLoader, a newly emerging malware loader that has been active since late 2024, which enables cybercriminals to deliver a wide range of threats such as infostealers and remote access trojans. The tool’s key strength is its versatility, serving as a multi-purpose delivery channel for diverse malware families such as Agent Tesla, AsyncRAT, FormBook, MassLogger, Remcos, Rhadamanthys, and Snake Keylogger. Its reach has already extended beyond borders, with campaigns in July 2025 targeting Taiwan with Snake Keylogger and Mexico with Remcos RAT and AsyncRAT, demonstrating how the same tool can support very different attack strategies. The infection chain typically begins with a malicious email attachment that conceals harmful code within legitimate files, allowing attackers to trick victims into triggering the loader.
Once triggered, QuirkyLoader initiates a hidden process that ultimately delivers the final malicious payload, with its design making it appear more like legitimate software and therefore harder to detect.
Attack Method
The attack sequence begins with a carefully crafted email containing a malicious archive disguised as a legitimate file. When opened, this archive leverages a trusted application as cover, discreetly loading hidden malicious components to be loaded without raising suspicion. These components then deploy the final payload by injecting it into trusted system processes, allowing the malware to blend seamlessly into the operating environment. QuirkyLoader strengthens this process with uncommon decryption methods and a loader design that closely resembles genuine software, making it more difficult for security tools to detect. This layered approach not only increases the chances of successful infection but also provides attackers with a dependable method for deploying a wide range of malware families across targeted systems.
Following are the TTPs based on the MITRE Attack Framework
| Tactic | Technique ID | Technique Name |
| Initial Access | T1566.001 | Phishing: Spearphishing Attachment |
| Execution | T1203 | Exploitation for Client Execution |
| Persistence | T1112 | Modify Registry |
| Persistence | T1542.003 | Pre-OS Boot: Bootkit |
| Persistence | T1574.001 | Hijack Execution Flow: DLL |
| Privilege Escalation | T1055 | Process Injection |
| Privilege Escalation | T1574.001 | Hijack Execution Flow: DLL |
| Defense Evasion | T1014 | Rootkit |
| Defense Evasion | T1055 | Process Injection |
| Defense Evasion | T1112 | Modify Registry |
| Defense Evasion | T1221 | Template Injection |
| Defense Evasion | T1497 | Virtualization/Sandbox Evasion |
| Defense Evasion | T1542.003 | Pre-OS Boot: Bootkit |
| Defense Evasion | T1564.001 | Hide Artifacts: Hidden Files and Directories |
| Defense Evasion | T1574.001 | Hijack Execution Flow: DLL |
| Discovery | T1018 | Remote System Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1497 | Virtualization/Sandbox Evasion |
| Discovery | T1518.001 | Software Discovery: Security Software Discovery |
| Command and Control | T1071 | Application Layer Protocol |
| Command and Control | T1573 | Encrypted Channel |
| Impact | T1496 | Resource Hijacking |
INSIGHTS
ETLM ASSESSMENT
From the ETLM perspective, CYFIRMA anticipates that QuirkyLoader’s emergence signals a future in which malware loaders will play a pivotal role in shaping the broader threat landscape, serving as foundational tools for increasingly coordinated and large-scale cybercrime operations. What may originate as localized campaigns has the potential to rapidly expand across regions, elevating risks from isolated incidents to global challenges. As these loaders become more adaptable and sophisticated, they will foster a dynamic and unpredictable environment, where threats continually evolve and reemerge in new forms, creating sustained uncertainty for the digital ecosystem.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems.
YARA Rule
rule QuirkyLoader_Indicators
{
meta:
description = “Detects QuirkyLoader malware indicators” author = “CYFIRMA”
malware_family = “QuirkyLoader” strings:
// SHA256 File Hashes
$sha256_hash_1 = “011257eb766f2539828bdd45f8aa4ce3c4048ac2699d988329783290a7b4a0d3”
$sha256_hash_2 = “0ea3a55141405ee0e2dfbf333de01fe93c12cf34555550e4f7bb3fdec2a7673b”
$sha256_hash_3 = “a64a99b8451038f2bbcd322fd729edf5e6ae0eb70a244e342b2f8eff12219d03”
$sha256_hash_4 = “9726e5c7f9800b36b671b064e89784fb10465210198fbbb75816224e85bd1306”
$sha256_hash_5 = “a1994ba84e255eb02a6140cab9fc4dd9a6371a84b1dd631bd649525ac247c111”
$sha256_hash_6 = “d954b235bde6ad02451cab6ee1138790eea569cf8fd0b95de9dc505957c533cd”
$sha256_hash_7 = “5d5b3e3b78aa25664fb2bfdbf061fc1190310f5046d969adab3e7565978b96ff”
$sha256_hash_8 = “6f53c1780b92f3d5affcf095ae0ad803974de6687a4938a2e1c9133bf1081eb6”
$sha256_hash_9 = “ea65cf2d5634a81f37d3241a77f9cd319e45c1b13ffbaf5f8a637b34141292eb”
$sha256_hash_10 = “1b8c6d3268a5706fb41ddfff99c8579ef029333057b911bb4905e24aacc05460”
$sha256_hash_11 = “d0a3a1ee914bcbfcf709d367417f8c85bd0a22d8ede0829a66e5be34e5e53bb9”
$sha256_hash_12 = “b22d878395ac2f2d927b78b16c9f5e9b98e006d6357c98dbe04b3fd78633ddde”
$sha256_hash_13 = “a83aa955608e9463f272adca205c9e1a7cbe9d1ced1e10c9d517b4d1177366f6”
$sha256_hash_14 = “3391b0f865f4c13dcd9f08c6d3e3be844e89fa3afbcd95b5d1a1c5abcacf41f4”
$sha256_hash_15 = “b2fdf10bd28c781ca354475be6db40b8834f33d395f7b5850be43ccace722c13”
$sha256_hash_16 = “bf3093f7453e4d0290511ea6a036cd3a66f456cd4a85b7ec8fbfea6b9c548504”
$sha256_hash_17 = “97aee6ca1bc79064d21e1eb7b86e497adb7ece6376f355e47b2ac60f366e843d”
$sha256_hash_18 = “b42bc8b2aeec39f25babdcbbdaab806c339e4397debfde2ff1b69dca5081eb44”
$sha256_hash_19 = “5aaf02e4348dc6e962ec54d5d31095f055bd7fb1e58317682003552fd6fe25dc”
$sha256_hash_20 = “8e0770383c03ce69210798799d543b10de088bac147dce4703f13f79620b68b1”
$sha256_hash_21 = “049ef50ec0fac1b99857a6d2beb8134be67ae67ae134f9a3c53699cdaa7c89ac”
$sha256_hash_22 = “cba8bb455d577314959602eb15edcaa34d0b164e2ef9d89b08733ed64381c6e0”
// Domains
$domain_1 = “catherinereynolds.info”
$domain_2 = “mail.catherinereynolds.info”
// IP Addresses
$ip_1 = “157.66.22.11”
$ip_2 = “103.75.77.90”
$ip_3 = “161.248.178.212”
condition:
any of ($ip*) or
any of ($domain*) or any of ($sha256*)
}
STRATEGIC:
MANAGEMENT:
TACTICAL RECOMMENDATIONS
Key Intelligence Signals:
Silk Typhoon (HAFNIUM): A Deep Dive into China-Linked Cyber Operations
About the Threat Actor
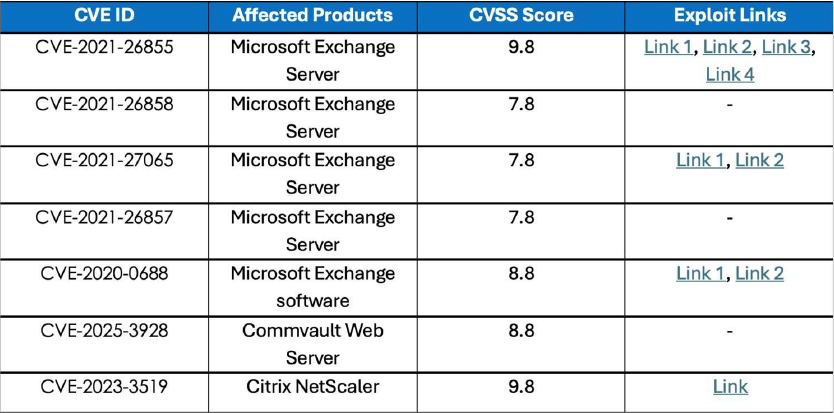
Silk Typhoon, also known as HAFNIUM, is a Chinese state-sponsored cyber espionage group first recognized as active in January 2021. The group focuses on stealing sensitive information for state-level espionage and has targeted sectors like higher education, military defense, IT, health, government, and critical infrastructure worldwide. They became widely known for a high-profile attack on Microsoft Exchange Server in early 2021, exploiting zero-day vulnerabilities to install backdoors and steal data.
Previously, the group has compromised victims by targeting vulnerabilities in internet- facing servers and has leveraged legitimate open-source frameworks—such as Covenant—for command-and-control operations. Once inside a network, HAFNIUM typically exfiltrates data to public file-sharing platforms like MEGA. When it comes to campaigns unrelated to these vulnerabilities, Microsoft has observed HAFNIUM interacting with victim Office 365 tenants. Even though they are unsuccessful in compromising customer accounts, this kind of reconnaissance activity enables the adversary to identify more details about their targets’ environments.
Details on Exploited Vulnerabilitie
TTPs based on MITRE ATT&CK Framework
| Tactic | ID | Technique |
| Reconnaissance | T1589.002 | Gather Victim Identity Information: Email Addresses |
| Reconnaissance | T1592.004 | Gather Victim Host Information: Client Configurations |
| Reconnaissance | T1590 | Gather Victim Network Information |
| Reconnaissance | T1590.005 | Gather Victim Network Information: IP Addresses |
| Reconnaissance | T1593.003 | Search Open Websites/Domains: Code Repositories |
| Resource Development | T1583.003 | Acquire Infrastructure: Virtual Private Server |
| Resource Development | T1583.005 | Acquire Infrastructure: Botnet |
| Resource Development | T1583.006 | Acquire Infrastructure: Web Services |
| Resource Development | T1584.005 | Compromise Infrastructure: Botnet |
| Initial Access | T1199 | Trusted Relationship |
| Initial Access | T1190 | Exploit Public-Facing Application |
| Initial Access | T1078.003 | Valid Accounts: Local Accounts |
| Initial Access | T1078.004 | Valid Accounts: Cloud Accounts |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
| Execution | T1059.003 | Command and Scripting Interpreter: Windows Command Shell |
| Persistence | T1136.002 | Create Account: Domain Account |
| Persistence | T1098 | Account Manipulation |
| Persistence | T1078.003 | Valid Accounts: Local Accounts |
| Persistence | T1505.003 | Server Software Component: Web Shell |
| Persistence | T1078.003 | Valid Accounts: Local Accounts |
| Persistence | T1078.004 | Valid Accounts: Cloud Accounts |
| Privilege Escalation | T1078.003 | Valid Accounts: Local Accounts |
| Privilege Escalation | T1078.004 | Valid Accounts: Cloud Accounts |
| Privilege Escalation | T1098 | Account Manipulation |
| Privilege Escalation | T1068 | Exploitation for Privilege Escalation |
| Defense Evasion | T1564.001 | Hide Artifacts: Hidden Files and Directories |
| Defense Evasion | T1070.001 | Indicator Removal: Clear Windows Event Logs |
| Defense Evasion | T1218.011 | System Binary Proxy Execution: Rundll32 |
| Defense Evasion | T1550.001 | Use Alternate Authentication Material: Application Access Token |
| Defense Evasion | T1078.003 | Valid Accounts: Local Accounts |
| Defense Evasion | T1078.004 | Valid Accounts: Cloud Accounts |
| Credential Access | T1110.003 | Brute Force: Password Spraying |
| Credential Access | T1555.006 | Credentials from Password Stores: Cloud Secrets Management Stores |
| Credential Access | T1003.001 | OS Credential Dumping: LSASS Memory |
| Credential Access | T1003.003 | OS Credential Dumping: NTDS |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1018 | Remote System Discovery |
| Discovery | T1016 | System Network Configuration Discovery |
| Discovery | T1016.001 | System Network Configuration Discovery: Internet Connection Discovery |
| Discovery | T1033 | System Owner/User Discovery |
| Lateral Movement | T1550.001 | Use Alternate Authentication Material: Application Access Token |
| Collection | T1560.001 | Archive Collected Data: Archive via Utility |
| Collection | T1119 | Automated Collection |
| Collection | T1530 | Data from Cloud Storage |
| Collection | T1213.002 | Data from Information Repositories: Sharepoint |
| Collection | T1005 | Data from Local System |
| Collection | T1114.002 | Email Collection: Remote Email Collection |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and Control | T1132.001 | Data Encoding: Standard Encoding |
| Command and Control | T1105 | Ingress Tool Transfer |
| Command and Control | T1095 | Non-Application Layer Protocol |
| Exfiltration | T1567.002 | Exfiltration Over Web Service: Exfiltration to Cloud Storage |
Latest Developments Observed
The threat actor is suspected of targeting government, technology, academic, legal, and professional services entities in North America by exploiting n-day and zero-day vulnerabilities, including CVE-2023-3519 affecting Citrix NetScaler products and CVE-2025- 3928 affecting Commvault Web Server. The motive is likely driven by intelligence- collection objectives to gain access to sensitive information.
ETLM Insights
Silk Typhoon is a highly sophisticated, state-linked Chinese advanced persistent threat (APT) group that has evolved traditional espionage tactics by focusing on stealth-driven, supply-chain–oriented compromises. The group demonstrates the ability to exploit trusted IT partners, maintain a low operational footprint with minimal forensic evidence, and seamlessly pivot across both on-premises and cloud environments—significantly elevating its risk profile.
Unlike ransomware operators, Silk Typhoon avoids overt disruptions. Instead, it selectively exfiltrates sensitive data and may discreetly approach victims with offers to suppress disclosure, effectively combining espionage with covert extortion. The group’s operations often target industrial and government networks, leveraging persistent, low-noise intrusions. Notably, it frequently removes forensic artefacts to obscure detection and rapidly re-establishes access even after remediation efforts, underscoring its resilience and advanced tradecraft.
YARA Rules
rule SilkTyphoon_IOC_Detection
{
meta:
author = “CYFIRMA”
description = “Detects references to Hafnium-associated CVEs, IPs, and domains” date = “2025-08-25”
threat_actor = “Silk Typhoon (HAFNIUM)” strings:
// CVE references
$cve1 = “CVE-2021-26855”
$cve2 = “CVE-2021-26858”
$cve3 = “CVE-2021-27065”
$cve4 = “CVE-2021-26857”
$cve5 = “CVE-2020-0688”
$cve6 = “CVE-2025-3928”
$cve7 = “CVE-2023-3519”
// IP addresses
$ip1 = “111.7.96.137”
$ip2 = “111.7.96.133”
$ip3 = “36.32.3.73”
$ip4 = “36.32.3.35”
$ip5 = “71.6.135.131”
$ip6 = “80.82.77.139”
$ip7 = “36.32.3.180”
// Domains
$domain1 = “rambler.ru”
$domain2 = “remotewd.com”
$domain3 = “wikipedia.org”
$domain4 = “soundsgroovyobx.com” condition:
any of ($cve*) or any of ($ip*) or any of ($domain*)
}
Recommendations Strategic
Management
Tactical
North Korean hackers targeting embassies
Researchers are monitoring a North Korea-linked spear phishing campaign targeting European embassies and foreign ministries in Seoul. The phishing emails included PDF attachments crafted to deploy XenoRAT malware, utilizing the GitHub API for command- and-control. The campaign shares similarities with prior Kimsuky APT activities, but timing patterns suggest the threat actors may be based in China. This could indicate North Korean operatives working from China, a Chinese APT mimicking Kimsuky tactics, or a joint operation using Chinese resources for DPRK intelligence goals. The researchers attribute the campaign to Kimsuky with medium confidence, noting the operators likely operate from China.
ETLM Assessment:
North Korean IT workers, often posing as legitimate remote employees, have been reported to operate from China to generate revenue for the regime. These workers, sometimes linked to hacking groups, engage in activities like app development and web scraping while secretly conducting cyberattacks. For example, a 2023 report noted that North Korean hackers receive vocational training in Shenyang to deploy malware, enhancing their capabilities before returning to North Korea or operating from Chinese outposts. The city of Shenyang has been noted as a hub for such activities due to its proximity to North Korea and internet access. However, in this case, the attacks seem to present a classic case of cyber espionage, and it is not clear if it presents a case of North Korean hackers using Chinese infrastructure, a joint project with China, or a case of Chinese hackers hiding their activity behind known North Korean TTPs.
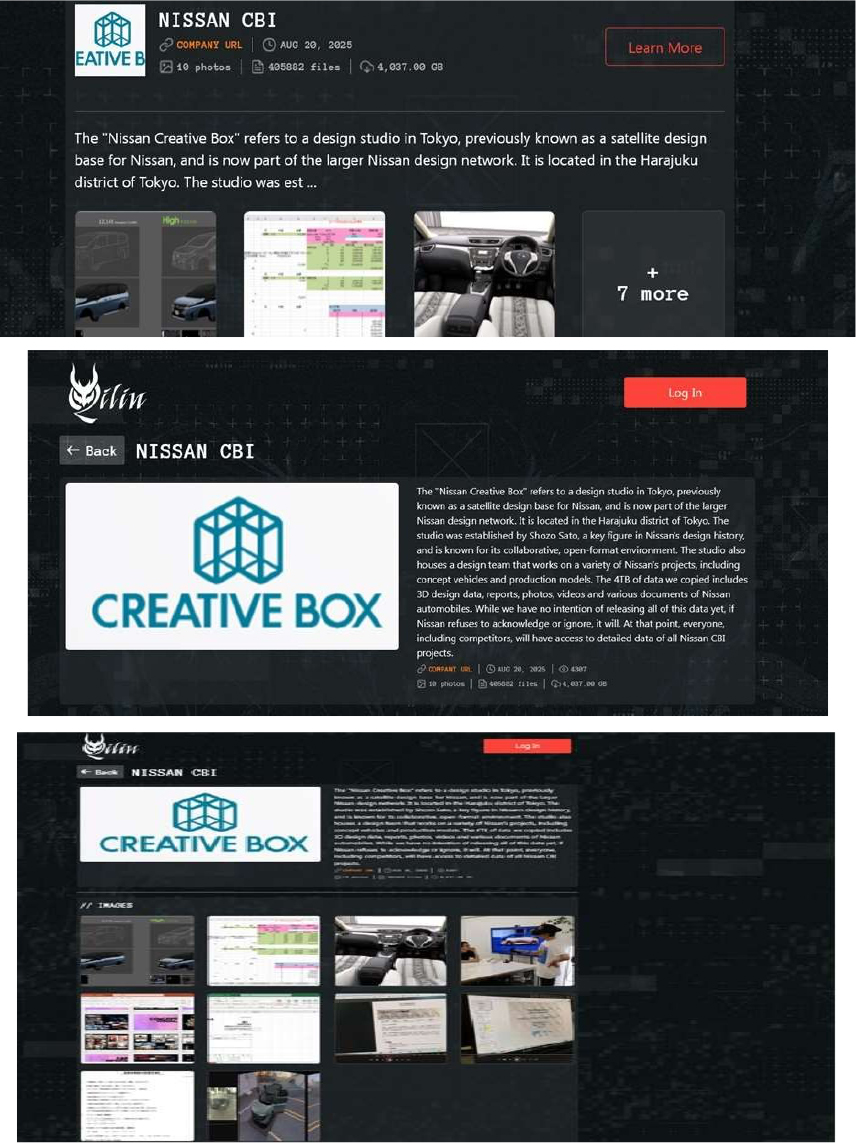
Qilin Ransomware Impacts Nissan CBI
Summary:
From the External Threat Landscape Management (ETLM) Perspective, CYFIRMA observed in an underground forum that a company from Japan, Nissan CBI, was compromised by Qilin Ransomware. The “Nissan Creative Box” refers to a design studio in Tokyo, previously known as a satellite design base for Nissan, and is now part of the larger Nissan design network. The studio also houses a design team that works on a variety of Nissan’s projects, including concept vehicles and production models. The ransomware group claims to have exfiltrated 4TB of data, including 3D design files, reports, photographs, videos, and various documents pertaining to Nissan automobiles.
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, Qilin ransomware poses a significant threat to organizations of all sizes. Its evolving tactics, including double extortion (data encryption and leak threats), cross-platform capabilities (Windows and Linux, including VMware ESXi), and focus on speed and evasion, make it a particularly dangerous actor.
World Leaks Ransomware Impacts Nikke Co., Ltd.
Summary:
From the External Threat Landscape Management (ETLM) Perspective, CYFIRMA observed in an underground forum that a company from Japan, Nikke Co., Ltd (https[:]//www[.]nikke[.]co[.]jp/), was compromised by World Leaks Ransomware. Nikke Co., Ltd. (The Japan Wool Textile Co., Ltd.), headquartered in Tokyo, is a leading global textile maker specializing in wool spinning, weaving, dyeing, and the development of high-performance, eco-friendly fabrics. The company has diversified into branded apparel, biotech-driven fiber innovation, real estate leasing, and digital manufacturing via IoT. The compromised data consists of confidential and sensitive information related to the organization.
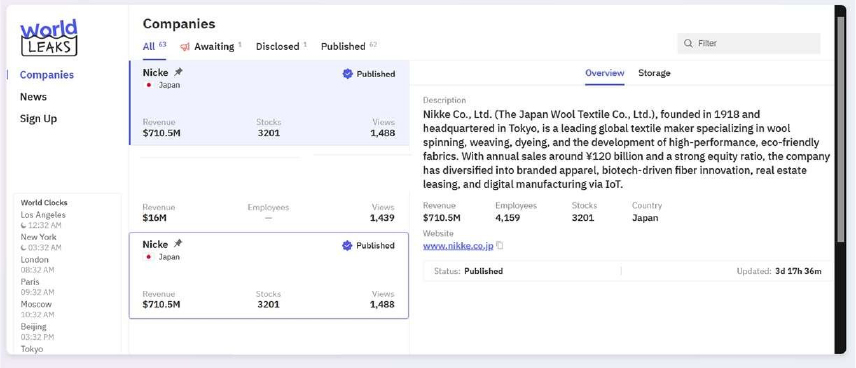
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, World Leaks represents the newest phase in ransomware evolution—moving towards data-centric, extortion-only operations led by established cybercriminal actors, with significant implications for organizations’ digital risk profiles.
Vulnerability in Intel PROSet/Wireless WiFi
Relevancy & Insights:
The vulnerability exists due to an improper condition check.
Impact:
A remote attacker on the local network can send specially crafted data to the application and perform a denial of service (DoS) attack.
Affected Products:
https[:]//www[.]intel[.]com/content/www/us/en/security- center/advisory/intel-sa-01292.html
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
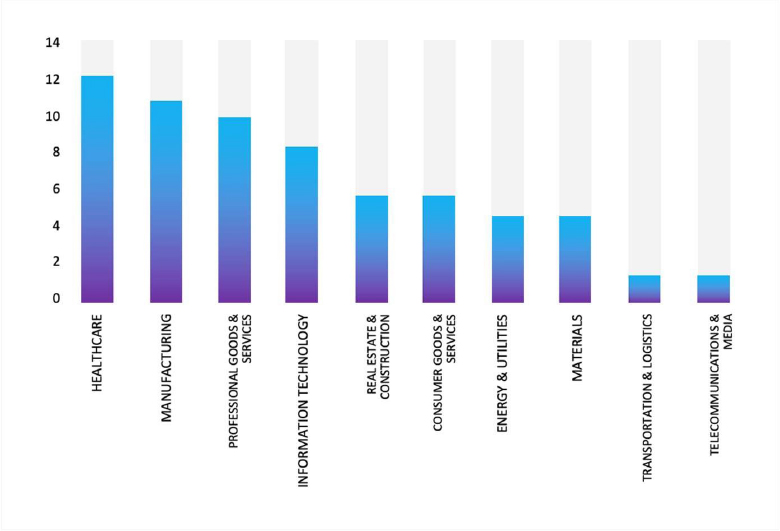
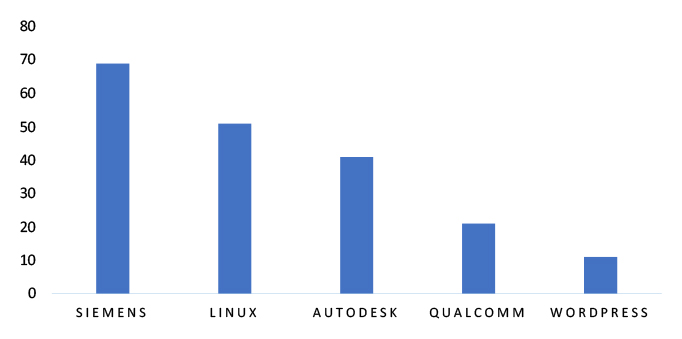
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies due to a range of vulnerabilities. The following are the top 5 most affected technologies
ETLM Assessment
Vulnerabilities in Intel PROSet/Wireless WiFi software can be critical because this suite manages wireless network connections and drivers on Intel-based systems. Exploitation could allow attackers to escalate privileges, execute arbitrary code, or disrupt wireless connectivity, potentially exposing sensitive data or enabling lateral movement in enterprise networks. This affects a broad user base, including home users, enterprises, and industries relying on Intel wireless adapters for connectivity.
Regularly updating Intel PROSet/Wireless drivers, following Intel security advisories, and limiting unnecessary administrative privileges are essential to reduce the risk of compromise.
Crypto24 Ransomware attacked and published the data of Palmgold Management Sdn Bhd
Summary:
Recently, we observed that Crypto24 Ransomware attacked and published the data of the Palmgold Management Sdn Bhd (https[:]//palmgold-mgmt[.]com/) on its dark web website. Palmgold Management Sdn Bhd is a leading Malaysian gambling company. The ransomware attack on Palmgold Management resulted in a significant breach of 500GB of the company’s most sensitive and business-critical data. The stolen information originated from both the Casino and Credit divisions.
The breach of the Casino Division exposed the full operational database of over 60,000 members, which contained a wealth of information, including personally identifiable information (PII), jackpot and play history, betting patterns, and machine configurations. Also compromised were internal analytics from Power BI dashboards, confidential finance, HR, and IT documents, and the complete contents of scanner shares from all company branches. Furthermore, the attackers gained access to proprietary operational logic, such as promotion formulas, game- specific revenue models, slot machine volatility settings, player-tier betting analytics, risk thresholds, fraud alert triggers, and blacklist criteria. The Credit Division’s breach was equally severe, with the attackers obtaining all customer Know Your Customer (KYC) information and detailed banking and cash transaction records.
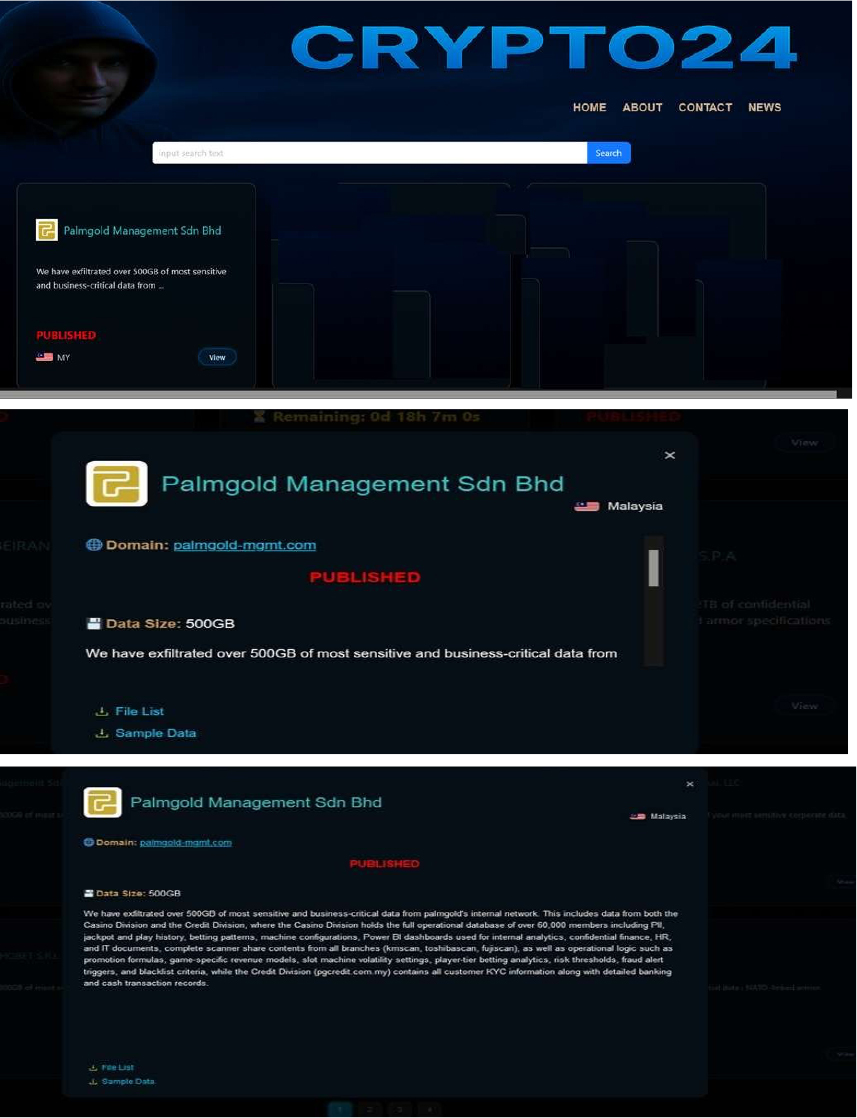
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, Crypto24 is a high-profile ransomware group known for rapid, high-volume data theft, fast encryption, and aggressive pressure tactics that combine classic ransom demands with sensitive data leaks.
Organizations in Asia have been primary targets, with attacks resulting in the exfiltration and exposure of terabytes of sensitive information. Recovery without payment is rarely feasible, underscoring the need for robust defense and backup strategies.
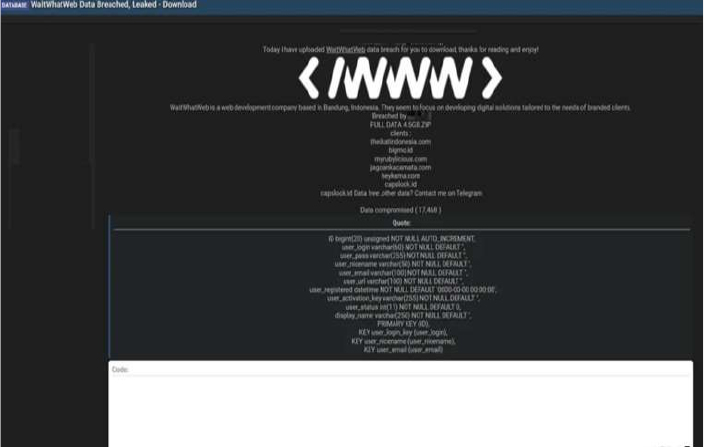
Indonesian Web Development Firm ‘Wait What Web’ Data Advertised on a Leak Site
Summary:
The CYFIRMA Research team observed that a threat actor has allegedly leaked the database of Wait What Web, a web development company based in Bandung, Indonesia. The company, which specializes in creating digital solutions for branded clients, was targeted in a recent cyberattack, with the data subsequently published on a dark web forum for download. The full dataset is said to be 4.5 GB and allegedly contains records for 17,468 users.
The compromised data appears to stem from a user database and includes a variety of sensitive personal information. The threat actor also listed several domains, purportedly belonging to clients of Wait What Web, suggesting their information may also be impacted by this breach. The leaked information allegedly includes:
Saudi Arabian Tech Company DIGO’s Data advertised on a Leak Site
Summary:
The CYFIRMA Research team has identified a threat actor, “N1KA,” who has allegedly leaked the database of DIGO[.]SA, a digital marketing and web services company based in Riyadh, Saudi Arabia. The data was posted on a dark web forum, exposing sensitive information. DIGO[.]SA, which specializes in developing digital technologies and innovative projects for the Saudi market, is now at the center of a significant data security incident. The breach reportedly contains information related to both clients and job applicants, highlighting the potential impact on individuals who have interacted with the company.
The compromised database allegedly contains 11,621 rows of data. An analysis of the leaked sample reveals two separate datasets. One set contains a list of email addresses, while the other includes highly sensitive personal information seemingly from job applications. The exposure of this data could lead to various malicious activities, including phishing attacks, identity theft, and other forms of fraud targeting the individuals whose information was compromised.
The leaked data allegedly includes the following:
Relevancy & Insights:
Financially motivated cybercriminals are continuously scouring for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to illicitly gain access and steal valuable data. Subsequently, the pilfered data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor identified as “N1KA” has recently gained attention as a highly active group specializing in data leaks. Reliable sources have connected the group to multiple security breaches involving unauthorized system access and the attempted sale of exfiltrated data on dark web marketplaces. N1KA’s ongoing operations highlight the evolving and persistent nature of cyber threats emerging from underground forums. These incidents underscore the critical importance for organizations to strengthen their cybersecurity posture through continuous monitoring, advanced threat intelligence, and proactive defense strategies to protect sensitive data and infrastructure.
Recommendations: Enhance the cybersecurity posture by:
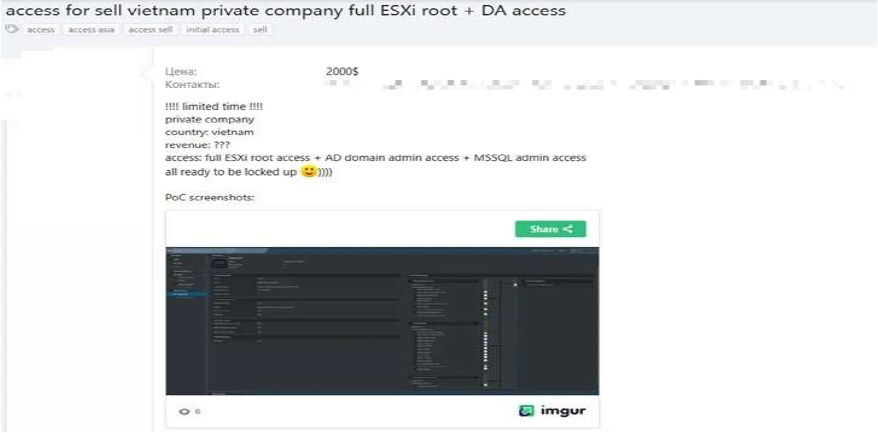
The CYFIRMA Research team observed that a threat actor is allegedly selling what they describe as “full ESXi root + DA access” to a Vietnamese private company.
According to a post on a cybercrime forum dated August 25, 2025, the initial access broker is offering complete administrative control over the company’s network for $2,000. The seller did not name the company but provided screenshots of an internal IT environment as proof of their claims to potential buyers.
The package for sale allegedly includes the highest level of privileges, specifically full root access to VMware ESXi servers and Domain Administrator (DA) credentials for the Active Directory, in addition to MSSQL admin access. This level of compromise would grant a buyer total control, enabling them to exfiltrate sensitive corporate data, conduct espionage, or deploy ransomware. The seller suggested this last possibility, noting in their post that the network is “all ready to be locked up.”
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
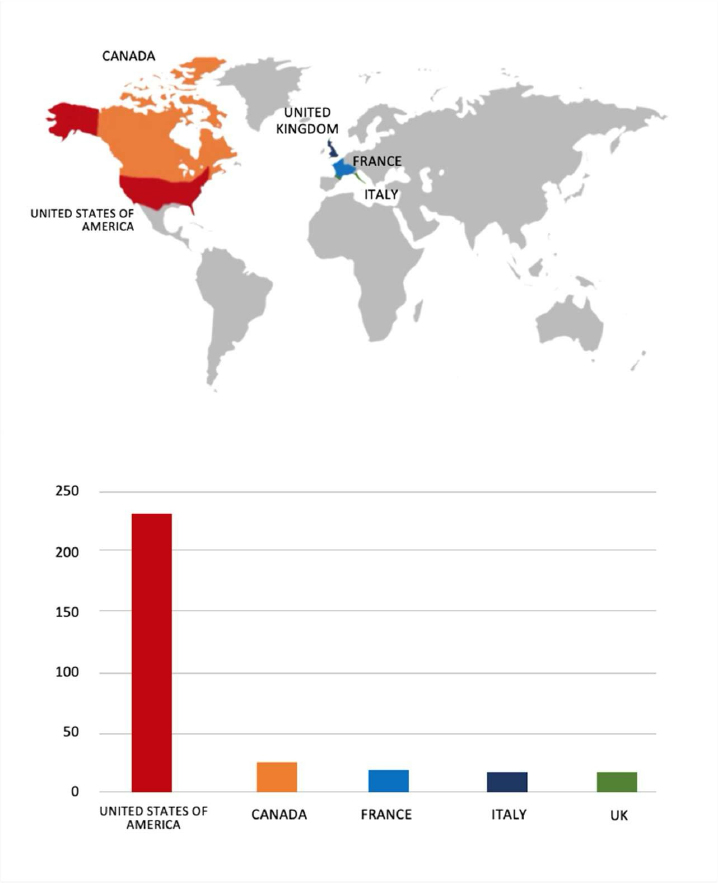
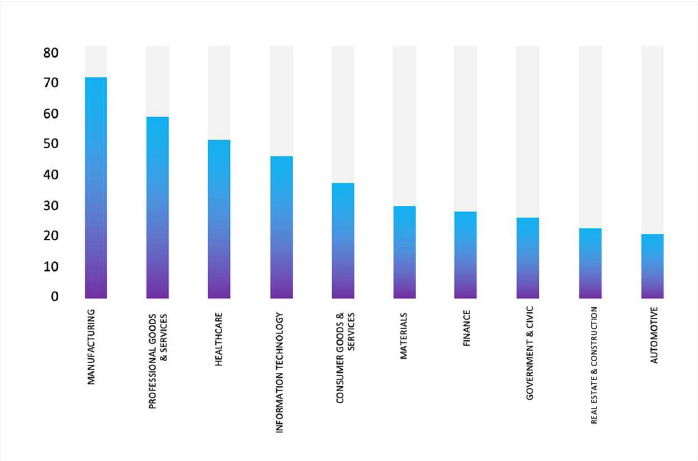
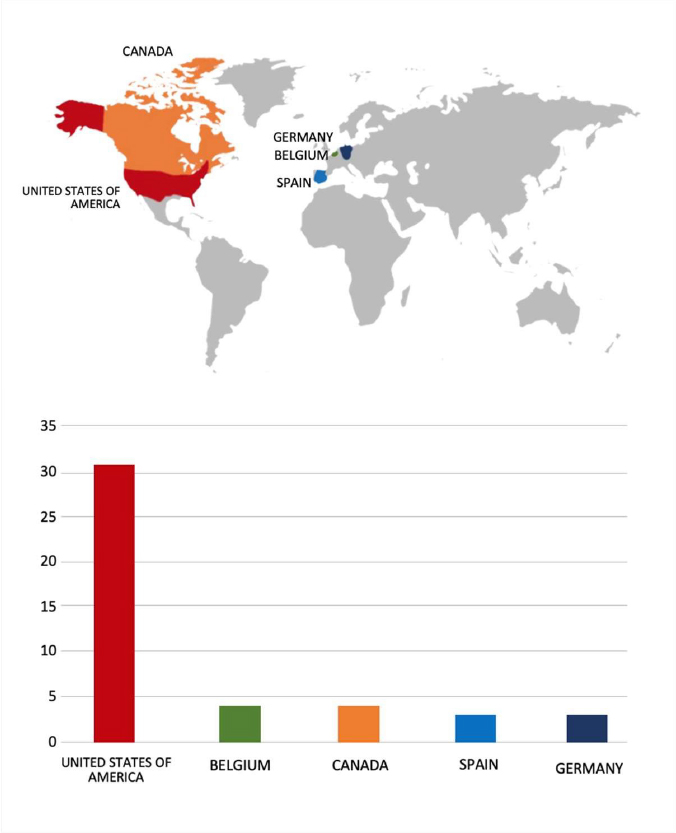
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.