


CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple – industries, geography, and technology – that could be relevant to your organization.
Type: Ransomware
Target Technologies: Windows OS
Target Geographies: Australia, Belgium, Canada, Germany, Italy, Japan, New Zealand, United Kingdom, United States
Target Industries: Auto Components, Automobiles, Education Services, Machinery, Software, Technology Hardware, Storage & Peripherals
Target Technologies: Remote Desktop Software, Virtual Private Network (VPN) Solutions, Virtualization Management Tools, Virtualization Security Solutions, operating systems
Introduction:
CYFIRMA Research and Advisory Team has observed SafePay Ransomware while monitoring various underground forums as part of our Threat Discovery Process.
SafePay Ransomware
Safepay (also written SafePay) is a centralized, non-RaaS ransomware operation that emerged around September–October 2024 and has remained highly active into early 2026, conducting disciplined, high-tempo double-extortion campaigns primarily against organizations in developed economies, especially the United States and Germany, while deliberately avoiding CIS-region systems through locale checks. The group gains initial access mainly via exploitation of misconfigured or weakly secured remote access infrastructure, such as VPN gateways, firewalls, RDP services, and exposed edge devices, often leveraging valid credentials, MFA bypass conditions, or public-facing service vulnerabilities.
Once inside, operators rapidly execute a structured intrusion playbook: privilege escalation, Active Directory and SMB share enumeration (including tools like ShareFinder), lateral movement via PsExec, WinRM, RDP, or RMM software, such as ScreenConnect, data staging and archiving (e.g., WinRAR), and exfiltration prior to encryption. The ransomware is typically deployed as a DLL executed through LOLBins like regsvr32.exe or rundll32.exe, encrypting files with a .safepay extension and dropping readme_safepay.txt ransom notes, while aggressively deleting shadow copies, disabling recovery mechanisms, and terminating security tools to inhibit restoration. Operational patterns and tradecraft show strong overlap with post-Conti and LockBit ecosystems, though no confirmed affiliation exists, suggesting experienced operators running a tightly controlled campaign model with rapid compromise-to-encryption timelines and structured leak-site pressure via Tor infrastructure.
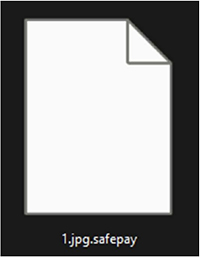
Screenshot: File encrypted by the ransomware (Source: Surface Web)
The SafePay ransomware ransom note informs victims that their corporate network has been compromised due to alleged “security misconfigurations,” critical files have been encrypted and renamed with the .safepay extension, and sensitive data has been exfiltrated to attacker-controlled infrastructure. Rather than specifying encryption algorithms or a fixed ransom amount in the note itself, the operators direct victims to initiate contact through a Tor-based portal (with references to backup links, a leak blog, and even a TON site) within 14 days to begin negotiations. The message threatens public disclosure of stolen data if contact is not established, followed by a countdown prior to publication, thereby leveraging reputational, legal, and regulatory pressure. It frames payment as a “mutually beneficial solution,” promising deletion of stolen data and provision of a decryption key, while asserting the group’s “reputation” as assurance of compliance. The note employs classic double-extortion coercion tactics, encryption, data theft, deadline enforcement, and public leak threats designed to induce urgency and compel negotiation, without offering any verifiable guarantee that decryption or data deletion will actually occur after payment.
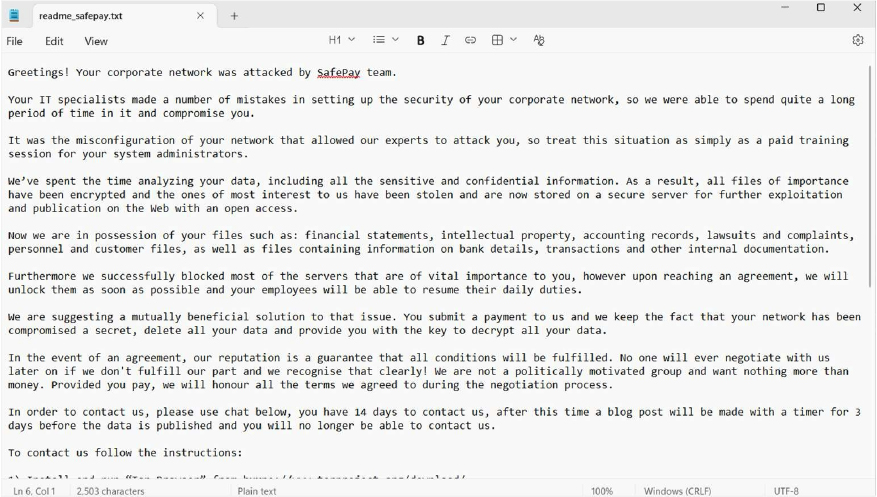
Screenshot: The appearance of SafePay Ransom Note (Source: Dark Web)
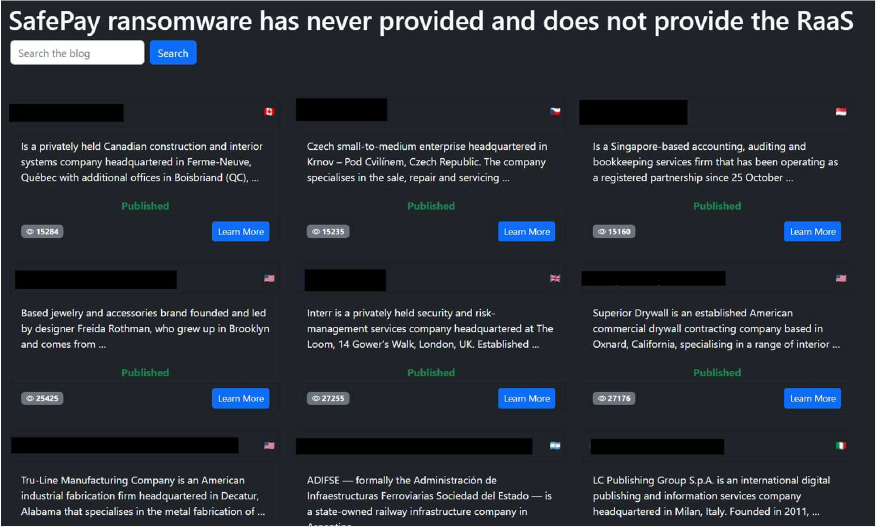
Screenshot: The appearance of SafePay Data Leak Site (Source: Dark Web)
The following are the TTPs based on the MITRE Attack Framework
| Tactic | Technique ID | Technique Name |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1129 | Shared Modules |
| Persistence | T1574 | Hijack Execution Flow |
| Privilege Escalation | T1574 | Hijack Execution Flow |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1027.002 | Obfuscated Files or Information: Software Packing |
| Defense Evasion | T1027.005 | Obfuscated Files or Information: Indicator Removal from Tools |
| Defense Evasion | T1070 | Indicator Removal |
| Defense Evasion | T1070.006 | Indicator Removal: Timestomp |
| Defense Evasion | T1218 | System Binary Proxy Execution |
| Defense Evasion | T1218.010 | System Binary Proxy Execution: Regsvr32 |
| Defense Evasion | T1218.011 | System Binary Proxy Execution: Rundll32 |
| Defense Evasion | T1574 | Hijack Execution Flow |
| Credential Access | T1056 | Input Capture |
| Discovery | T1057 | Process Discovery |
| Discovery | T1082 | System Information Discovery |
| Collection | T1056 | Input Capture |
| Command and Control | T1071 | Application Layer Protocol |
Relevancy and Insights:
I. The ransomware primarily targets Windows OS, which is utilised by enterprises in a variety of diligence.
II. Persistence: The ransomware exhibits continuity mechanisms to ensure its survival and ongoing vicious conditioning within the compromised terrain. This could involve creating autostart entries or modifying system settings to maintain a base and grease unborn attacks.
III. User Input Checks: The ransomware is also performing checks on user input. This behaviour implies that the ransomware may have the ability to interact with the user or receive commands in some way. It could be looking for specific inputs or triggers to initiate its encryption process or carry out other malicious activities. This behaviour indicates a level of sophistication and interactivity in the ransomware’s design.
IV. The use of idle periods may indicate that the ransomware is designed to operate more stealthily, waiting for the computer to be idle before encrypting files or performing other malicious activities.
ETLM Assessment:
CYFIRMA’s assessment indicates that SafePay ransomware is likely to continue evolving as a structured double-extortion operation, focusing on strengthening its data exfiltration processes, leak-site infrastructure, and negotiation mechanisms rather than introducing fundamentally new tactics. Based on its current ransom note structure emphasizing prolonged network access, server disruption, staged public disclosure timelines, and multi-channel communication via Tor and TON (Telegram Open Network), the group may formalize its extortion workflow by standardizing victim portals, improving data leak publication procedures, enhancing backup destruction techniques, and refining negotiation messaging to increase payment rates. Future activity may also involve more consistent lateral movement, persistence, and enterprise-wide impact to reinforce coercive leverage. However, unless supported by significant technical innovation or demonstrable operational sophistication, SafePay’s evolution is expected to remain incremental, centered on improving reliability, psychological pressure, and monetization efficiency rather than materially expanding its tactical capabilities.
Sigma rule:
title: SafePay Ransomware Suspicious Execution and Defense Evasion Activity tags:
– attack.execution
– attack.defense-evasion
– attack.t1218.010
– attack.t1218.011
– attack.t1070.006
– attack.t1027 logsource:
category: process_creation product: windows
detection:
selection_proxy_regsvr32: Image|endswith: ‘\regsvr32.exe’ CommandLine|contains:
– ‘.dll’
– ‘/s’
selection_proxy_rundll32: Image|endswith: ‘\rundll32.exe’ CommandLine|contains: ‘.dll’
selection_shadowcopy_delete: CommandLine|contains|all:
– ‘vssadmin’
– ‘delete’
– ‘shadows’
selection_wmic_shadowcopy: CommandLine|contains|all:
– ‘wmic’
– ‘shadowcopy’
– ‘delete’
selection_backup_catalog_delete: CommandLine|contains|all:
– ‘wbadmin’
– ‘delete’
– ‘catalog’
selection_service_kill: CommandLine|contains:
– ‘taskkill /f’
– ‘net stop’
condition: 1 of selection_proxy_* or 1 of selection_shadowcopy_* or selection_backup_catalog_delete or selection_service_kill
falsepositives:
– Legitimate administrative activity involving backup deletion
– Software deployment using regsvr32 or rundll32
– IT maintenance operations level: high (Source: Surface Web)
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
Type: Information stealer| Objectives: Data Exfiltration | Target Technology: Windows OS | Target Geography: Global
CYFIRMA collects data from various forums, based on which the following malware has been observed. The identified malware has been ascertained to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week, “Vidar Malware” is in focus.
Overview of Operation Vidar Malware
A recently identified and ongoing malware campaign has revealed the emergence of a new variant of the Vidar information-stealing malware, characterized by deliberate efforts to evade detection and mislead security analysts. The threat actors are distributing malicious files that impersonate legitimate software by adopting trusted application names and icons, thereby increasing the probability of user interaction and execution. This social engineering approach enables the malware to appear benign during initial inspection, facilitating unauthorized system compromise while delaying recognition of the threat.
A notable feature of this campaign is the intentional inflation of the malicious file size through the inclusion of extraneous data appended to the executable. The resulting files, exceeding 800 MB in size, are designed to disrupt automated analysis environments, degrade the performance of security tools, and complicate manual reverse-engineering efforts. Such manipulation serves to obscure the embedded malicious components and prolong the time required for effective investigation, ultimately enhancing the attackers’ ability to operate undetected for extended periods.
Although the delivery mechanism incorporates advanced evasion techniques, the operational objective remains consistent with information-stealing malware campaigns, namely the compromise of victim systems and the unauthorized extraction of sensitive data to attacker-controlled infrastructure. Observed indicators also suggest potential links to external communication channels, including references to accounts associated with Telegram, which may facilitate coordination or distribution activities. Collectively, this campaign underscores the continued evolution of commodity malware, where adversaries increasingly combine deception, scale manipulation, and covert communication methods to enhance effectiveness and persistence.
Overall, this campaign illustrates how modern malware operations are increasingly designed to evade both users and security defenses through deception and manipulation rather than overtly aggressive techniques. By disguising malicious files as legitimate software and artificially inflating their size to complicate analysis, the attackers demonstrate a strategic focus on misdirection and persistence. This approach emphasizes the growing risk associated with downloading software from untrusted or unofficial sources, as even seemingly authentic applications may conceal hidden threats. It reinforces the importance of verifying software authenticity, maintaining updated security controls, and exercising caution before executing unfamiliar files, particularly when they originate from unverified distribution channels.
Attack Method
The attack methodology associated with this Vidar malware variant demonstrates a structured approach that integrates deception, controlled execution, and external communication to facilitate unauthorized data acquisition while minimizing the likelihood of detection. The malicious file is presented as legitimate software, thereby encouraging user execution and enabling the threat to establish itself within the system environment without immediate suspicion. Following execution, the malware utilizes standard Windows system functionalities to manage memory operations, initiate and control threads, and interact with core operating system components. By relying on commonly used system processes, malicious activity is more likely to blend with normal application behavior, complicating behavioral analysis and detection by security mechanisms.
A central element of the attack involves the establishment of outbound communication with attacker-controlled infrastructure to support command-and-control operations and data exfiltration. Network indicators associated with the activity include communication attempts directed toward the external IP address 49[.]13[.]36[.]31, which is geographically located in Germany, indicating the presence of a remote server used for operational management. Through this channel, malware can transmit collected information and potentially receive further instructions or updates. Additional references to external coordination channels, including accounts associated with Telegram and the Steam community, suggest the integration of supplementary communication mechanisms that may assist in campaign coordination or distribution efforts.
Collectively, the observed attack method reflects an evolution in commodity malware operations, wherein adversaries employ legitimate system capabilities, deceptive presentation techniques, and geographically distributed infrastructure to maintain persistence and operational control. This combination of covert execution and structured remote communication enhances the attackers’ ability to sustain activity over extended periods while complicating incident response and forensic investigation.
The following are the TTPs based on the MITRE Attack Framework for Enterprise
| Tactic (ID) | Technique ID | Technique Name |
| Execution | T1204.002 | User Execution: Malicious File |
| T1106 | Native API | |
| Persistence | T1547 | Boot or Logon Autostart Execution |
| Defense Evasion | T1036 | Masquerading |
| T1027 | Obfuscated/Compressed Files and Information | |
| T1140 | Deobfuscate/Decode Files or Information | |
| T1055 | Process Injection | |
| T1497 | Virtualization/Sandbox Evasion | |
| Discovery | T1082 | System Information Discovery |
| T1012 | Query Registry | |
| Collection | T1005 | Data from Local System |
| Credential Access | T1555 | Credentials from Password Stores |
| Command and control | T1071.001 | T1573 |
| Application Layer Protocol: Web Protocols | Encrypted Channel | |
| Exfiltration | T1041 | Exfiltration Over C2 Channel |
INSIGHTS
The malware demonstrates a strong reliance on appearance and presentation to avoid early suspicion. By imitating legitimate software and modifying visible file characteristics, the attackers increase the chances that users will trust and execute the file. This indicates that deception plays an important role alongside technical methods in the overall operation.
The behavior observed after execution appears controlled and deliberate rather than aggressive or disruptive. The malware performs its activities in a way that does not immediately interfere with normal system usage, which helps it remain less noticeable. This measured approach allows the malicious processes to operate quietly within the environment.
There are also indications that the activity is supported by an organized external infrastructure rather than being an isolated incident. The presence of coordinated communication elements suggests structured management behind the campaign. This reflects an operation that is planned and maintained with a level of consistency typical of established threat activities.
ETLM ASSESSMENT
From a broader risk and threat-management perspective, this activity demonstrates how modern malware campaigns increasingly rely on credibility, timing, and user interaction rather than overt technical exploitation alone. By blending malicious intent with seemingly legitimate content or processes, attackers can delay detection and extend the duration of compromise, which complicates investigation and response efforts for organizations. Such incidents may also originate outside controlled enterprise environments but later intersect with workplace systems through credential reuse or connected devices, creating indirect exposure pathways. Over time, these patterns can place additional pressure on security teams, influence resource allocation decisions, and reshape how organizations evaluate user-driven risks within their overall cybersecurity posture.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems.
YARA Rules
rule Vidar_Malware_String_IOCs
{
meta:
description = “Detects Vidar malware-based IOCs and infrastructure indicators” author = “CYFIRMA”
date = “2026-02-23”
strings:
/* Malware Sample Hashes */
$hash_1 =
“89bb701065ed4a6b036223a7752c1cf45c7d32a7a466fc3f1b2013f2736a15cb”
$hash_2 =
“b31b28326d4f69fb1de99ab9f3f880996e08cf7fd9347b2eb17c49e797547ed2”
/* telegram account link & C2 Indicators */
$telegram_url = “https://telegram.me/dead1cf”
$steamcommunity_url =
“https://steamcommunity.com/profiles/76561198767911792”
$c2_ip = “49.13.36.31”
condition:
any of ($hash_*) or any of ($telegram_url, $steamcommunity_url, $c2_ip)
}
Strategic Recommendations
Management Recommendations
Tactical Recommendations
Key Intelligence Signals:
Lazarus Group: Strategic shift from conventional attacks
About the Threat Actor
Lazarus Group, active since at least 2009, is a highly sophisticated cybercriminal organization reportedly linked to the North Korean government and known to the U.S. government as Hidden Cobra. Members are believed to be affiliated with Lab 110, a unit of DPRK military intelligence.
The group is capable of rapidly developing and evolving malware and exploits and has recently focused on targeting cryptocurrency exchanges. Lazarus Group operates in at least two subdivisions: Andariel, targeting the South Korean government and organizations, and Bluenoroff, focused on financial gain and global espionage.
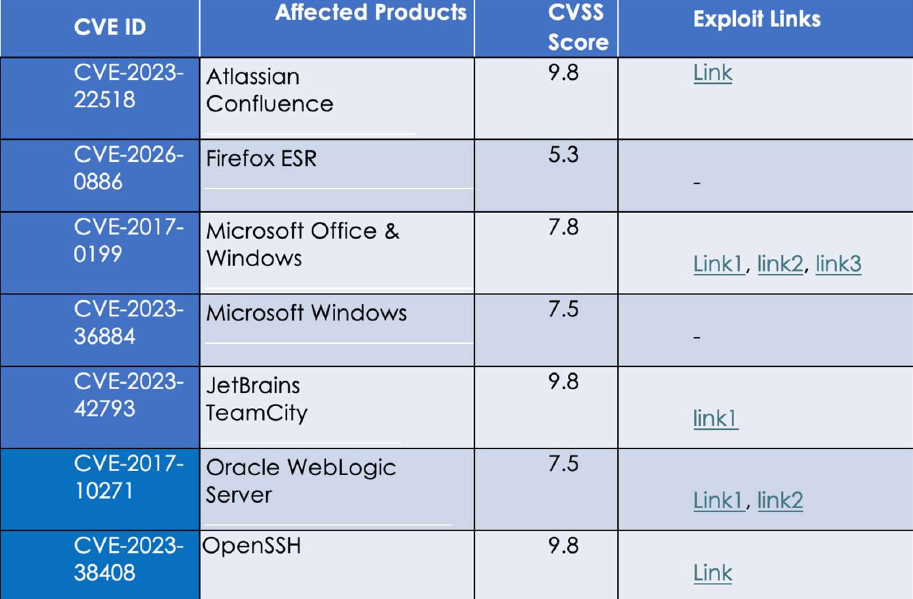
Details on Exploited Vulnerabilities
TTPs based on MITRE ATT&CK Framework
| Tactic | ID | Technique |
| Reconnaissance | T1591 | Gather Victim Org Information |
| Reconnaissance | T1591.004 | Gather Victim Org Information: Identify Roles |
| Reconnaissance | T1589.002 | Gather Victim Identity Information: Email Addresses |
| Reconnaissance | T1593.001 | Search Open Websites/Domains: Social Media |
| Resource Development | T1608.001 | Stage Capabilities: Upload Malware |
| Resource Development | T1608.002 | Stage Capabilities: Upload Tool |
| Resource Development | T1587.001 | Develop Capabilities: Malware |
| Resource Development | T1587.002 | Develop Capabilities: Code Signing Certificates |
| Resource Development | T1583.001 | Acquire Infrastructure: Domains |
| Resource Development | T1583.004 | Acquire Infrastructure: Server |
| Resource Development | T1583.006 | Acquire Infrastructure: Web Services |
| Resource Development | T1584.001 | Compromise Infrastructure: Domains |
| Resource Development | T1584.004 | Compromise Infrastructure: Server |
| Resource Development | T1585.001 | Establish Accounts: Social Media Accounts |
| Resource Development | T1585.002 | Establish Accounts: Email Accounts |
| Resource Development | T1588.002 | Obtain Capabilities: Tool |
| Resource Development | T1588.003 | Obtain Capabilities: Code Signing Certificates |
| Resource Development | T1588.004 | Obtain Capabilities: Digital Certificates |
| Initial Access | T1189 | Drive-by Compromise |
| Initial Access | T1566.001 | Phishing: Spear phishing Attachment |
| Initial Access | T1566.002 | Phishing: Spear phishing Link |
| Initial Access | T1566.003 | Phishing: Spear phishing via Service |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
| Execution | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Execution | T1106 | Native API |
| Execution | T1204.001 | User Execution: Malicious Link |
| Execution | T1204.002 | User Execution: Malicious File |
| Execution | T1203 | Exploitation for Client Execution |
| Execution | T1059.003 | Command and Scripting Interpreter: Windows Command Shell |
| Execution | T1047 | Windows Management Instrumentation |
| Execution | T1059.005 | Command and Scripting Interpreter: Visual Basic |
| Persistence | T1505.004 | Server Software Component: IIS Components |
| Persistence | T1542.003 | Pre-OS Boot: Bootkit |
| Persistence | T1574.001 | Hijack Execution Flow: DLL |
| Persistence | T1574.013 | Hijack Execution Flow: KernelCallbackTable |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Persistence | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Persistence | T1098 | Account Manipulation |
| Persistence | T1547.009 | Boot or Logon Autostart Execution: Shortcut Modification |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1098 | Account Manipulation |
| Privilege Escalation | T1547.009 | Boot or Logon Autostart Execution: Shortcut Modification |
| Privilege Escalation | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1055.001 | Process Injection: Dynamic-link Library Injection |
| Privilege Escalation | T1574.001 | Hijack Execution Flow: DLL |
| Privilege Escalation | T1574.013 | Hijack Execution Flow: KernelCallbackTable |
| Privilege Escalation | T1134.002 | Access Token Manipulation: Create Process with Token |
| Privilege Escalation | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Defense Evasion | T1134.002 | Access Token Manipulation: Create Process with Token |
| Defense Evasion | T1218 | System Binary Proxy Execution |
| Defense Evasion | T1218.005 | System Binary Proxy Execution: Mshta |
| Defense Evasion | T1218.010 | System Binary Proxy Execution: Regsvr32 |
| Defense Evasion | T1218.011 | System Binary Proxy Execution: Rundll32 |
| Defense Evasion | T1620 | Reflective Code Loading |
| Defense Evasion | T1070 | Indicator Removal |
| Defense Evasion | T1070.003 | Indicator Removal: Clear Command History |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1070.006 | Indicator Removal: Timestomp |
| Defense Evasion | T1202 | Indirect Command Execution |
| Defense Evasion | T1036.003 | Masquerading: Rename Legitimate Utilities |
| Defense Evasion | T1036.004 | Masquerading: Masquerade Task or Service |
| Defense Evasion | T1036.005 | Masquerading: Match Legitimate Resource Name or Location |
| Defense Evasion | T1036.008 | Masquerading: Masquerade File Type |
| Defense Evasion | T1027.002 | Obfuscated Files or Information: Software Packing |
| Defense Evasion | T1027.007 | Obfuscated Files or Information: Dynamic API Resolution |
| Defense Evasion | T1027.009 | Obfuscated Files or Information: Embedded Payloads |
| Defense Evasion | T1027.013 | Obfuscated Files or Information: Encrypted/Encoded File |
| Defense Evasion | T1542.003 | Pre-OS Boot: Bootkit |
| Defense Evasion | T1220 | XSL Script Processing |
| Defense Evasion | T1055.001 | Process Injection: Dynamic-link Library Injection |
| Defense Evasion | T1497.003 | Virtualization/Sandbox Evasion: Time Based Evasion |
| Defense Evasion | T1622 | Debugger Evasion |
| Defense Evasion | T1140 | Deobfuscate/Decode Files or Information |
| Defense Evasion | T1564.001 | Hide Artifacts: Hidden Files and Directories |
| Defense Evasion | T1221 | Template Injection Authentication Process: Conditional Access Policies |
| Defense Evasion | T1574.001 | Hijack Execution Flow: DLL |
| Defense Evasion | T1574.013 | Hijack Execution Flow: KernelCallbackTable |
| Defense Evasion | T1497.001 | Virtualization/Sandbox Evasion: System Checks |
| Defense Evasion | T1553.002 | Subvert Trust Controls: Code Signing |
| Defense Evasion | T1078 | Valid Accounts |
| Defense Evasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| Defense Evasion | T1562.004 | Impair Defenses: Disable or Modify System Firewall |
| Defense Evasion | T1656 | Impersonation |
| Credential Access | T1056.001 | Input Capture: Keylogging |
| Credential Access | T1110.003 | Brute Force: Password Spraying |
| Credential Access | T1557.001 | Adversary-in-the-Middle: LLMNR/NBT-NS Poisoning and SMB Relay |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1497.001 | Virtualization/Sandbox Evasion: System Checks |
| Discovery | T1497.003 | Virtualization/Sandbox Evasion: Time Based Evasion |
| Discovery | T1087.002 | Account Discovery: Domain Account |
| Discovery | T1010 | Application Window Discovery |
| Discovery | T1046 | Network Service Discovery |
| Discovery | T1622 | Debugger Evasion |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1012 | Query Registry |
| Discovery | T1614.001 | System Location Discovery: System Language Discovery |
| Discovery | T1016 | System Network Configuration Discovery |
| Discovery | T1049 | System Network Connections Discovery |
| Discovery | T1033 | System Owner/User Discovery |
| Discovery | T1124 | System Time Discovery |
| Lateral Movement | T1021.002 | Remote Services: SMB/Windows Admin Shares |
| Lateral Movement | T1021.001 | Remote Services: Remote Desktop Protocol |
| Lateral Movement | T1021.004 | Remote Services: SSH |
| Lateral Movement | T1534 | Internal Spear phishing |
| Collection | T1056.001 | Input Capture: Keylogging |
| Collection | T1560 | Archive Collected Data |
| Collection | T1560.001 | Archive Collected Data: Archive via Utility |
| Collection | T1560.002 | Archive Collected Data: Archive via Library |
| Collection | T1560.003 | Archive Collected Data: Archive via Custom Method |
| Collection | T1557.001 | Adversary-in-the-Middle: LLMNR/NBT-NS Poisoning and SMB Relay |
| Collection | T1005 | Data from Local System |
| Collection | T1074.001 | Data Staged: Local Data Staging |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and Control | T1571 | Non-Standard Port |
| Command and Control | T1132.001 | Data Encoding: Standard Encoding |
| Command and Control | T1001.003 | Data Obfuscation: Protocol or Service Impersonation |
| Command and Control | T1573.001 | Encrypted Channel: Symmetric Cryptography |
| Command and Control | T1090.001 | Proxy: Internal Proxy |
| Command and Control | T1090.002 | Proxy: External Proxy |
| Command and Control | T1008 | Fallback Channels |
| Command and Control | T1105 | Ingress Tool Transfer |
| Command and Control | T1104 | Multi-Stage Channels |
| Command and Control | T1102.002 | Web Service: Bidirectional Communication |
| Exfiltration | T1041 | Exfiltration Over C2 Channel |
| Exfiltration | T1567.002 | Exfiltration Over Web Service: Exfiltration to Cloud Storage |
| Exfiltration | T1048.003 | Exfiltration Over Alternative Protocol: Exfiltration Over Unencrypted Non-C2 Protocol |
| Impact | T1561.001 | Disk Wipe: Disk Content Wipe |
| Impact | T1561.002 | Disk Wipe: Disk Structure Wipe |
| Impact | T1489 | Service Stop |
| Impact | T1485 | Data Destruction |
| Impact | T1529 | System Shutdown/Reboot |
| Impact | T1491.001 | Defacement: Internal Defacement |
Latest Developments Observed
The threat actor is suspected of leveraging a BeaverTail malware variant as part of the Contagious Interview campaign, targeting IT professionals working in the cryptocurrency, Web3, and artificial intelligence sectors. The campaign appears aimed at compromising developers and engineers to steal financial information and other sensitive data.
ETLM Insights
The Lazarus Group, a North Korea–aligned state-sponsored threat actor, is suspected to be carrying out sustained and targeted campaigns against software developers employed by cryptocurrency exchanges, blockchain initiatives, Web3 startups, and fintech organizations. Rather than directly targeting heavily secured exchange infrastructure, the group increasingly focuses on compromising individual developers and leveraging their trusted access to penetrate corporate environments and manipulate cryptocurrency transactions.
This approach reflects a strategic shift from conventional exchange-focused attacks to a human-centric supply chain intrusion model.
Looking ahead, Lazarus Group is expected to continue functioning as a state- directed revenue and intelligence apparatus, combining financially motivated operations, primarily cryptocurrency theft, with broader strategic espionage objectives. The group’s operations are likely to grow more sophisticated, patient, and cross-sector in scope. Financially driven cyber activity will remain persistent and operationally prioritized, with campaigns designed to be structured, scalable, and revenue-optimized rather than opportunistic.
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
YARA Rules
rule Threat_Actor_Indicators_Generic
{
meta:
description = “Detects files containing CVE strings, suspicious domains, IPs, or known filenames/hashes linked to recent threat activity”
author = “CYFIRMA” date = “2026-02-24”
confidence = “high (IOC-based detection)”
strings:
// CVEs observed
$cve1 = “CVE-2023-38408” ascii nocase
$cve2 = “CVE-2017-10271” ascii nocase
$cve3 = “CVE-2023-22518” ascii nocase
$cve4 = “CVE-2017-0199” ascii nocase
$cve5 = “CVE-2023-36884” ascii nocase
$cve6 = “CVE-2023-42793” ascii nocase
$cve7 = “CVE-2026-0886” ascii nocase
// Domains
$domain1 = “knightsbridge-dex.vercel.app” ascii nocase
$domain2 = “tetrismic.vercel.app” ascii nocase
$domain3 = “mocki.io” ascii nocase
$domain4 = “sellinicapital.com” ascii nocase
$domain5 = “presentations.life” ascii nocase
// IPs
$ip1 = “141.193.213.20” ascii
$ip2 = “188.165.53.185” ascii
$ip3 = “199.59.148.209” ascii
$ip4 = “119.28.118.4” ascii
$ip5 = “118.70.180.174” ascii
// Files / hashes
$file1 = “win32.exe” ascii nocase
$file2 = “hrm3jvh9v.dll” ascii nocase
$file3 = “eqfvkn” ascii nocase
$sha256_1 = “00000077553a5b27a610ac98f29563bbd6e0decc020c2d49e4fa0d89197e7fd8” ascii
condition:
// Trigger if multiple indicator types appear (reduces noise) (
1 of ($domain*) and 1 of ($ip*)
)
or (
1 of ($file*, $sha256_*) and 1 of ($cve*)
)
or (
2 of ($domain*, $ip*, $file*, $sha256_*, $cve*)
)
}
Strategic Recommendations
Management Recommendations
Tactical Recommendations
China’s Typhoons keep targeting American critical infrastructure
The FBI continues to warn that China’s Salt Typhoon espionage operation remains a serious and active danger to U.S. telecommunications networks. FBI Deputy Assistant Director for Cyber Intelligence stressed that “we must clearly understand the threat from Salt Typhoon actors—along with the broader Chinese intelligence apparatus and its supporting systems—is still very much alive and ongoing.” In other news, researchers recently reported that China’s Volt Typhoon campaign is still deeply entrenched inside
U.S. infrastructure.
Volt Typhoon—which focuses on pre-positioning and battlespace preparation inside vital utility sectors, remains highly active, continuing to map, infiltrate, and establish persistent footholds not only across American infrastructure but also among their allies. It is a distinct possibility that a significant number of these compromises may never be detected.
ETLM Assessment:
As noted in this CYFIRMA report, the above campaigns mark a significant evolution in China’s cyber strategy, from economic espionage to politically driven operations that threaten Western critical infrastructure. Salt Typhoon’s infiltration of telecommunications networks and Volt Typhoon’s sabotage preparations in U.S. sectors like energy and transportation reveal China’s intent to dominate cyberspace, exploiting vulnerabilities in the U.S.’s fragmented cybersecurity framework. These campaigns, leveraging sophisticated techniques and plausible deniability, pose significant risks to national security, from compromised communications to potential disruptions of military and civilian operations. The structural advantages of China’s authoritarian cyberdefense model, contrasted with the U.S.’s decentralized approach, underscore the challenges of securing privately owned systems against a state- backed actor with vast resources.
The Netherlands warns of escalating Russian cyber operations
Dutch intelligence services have issued a stark warning that Russia is ramping up its hybrid warfare tactics—including cyberattacks, acts of sabotage, and clandestine influence efforts—across Europe as part of preparations for an extended standoff with the West.
In a combined evaluation from the General Intelligence and Security Service (AIVD) and the Military Intelligence and Security Service (MIVD), the agencies noted: “Russia has demonstrated not only its ability to endure heavy casualties in Ukraine but has actually strengthened and restructured its military. Moreover, Russian forces are gearing up for the potential of direct confrontation with NATO and are engaging in deliberate actions to probe the West’s readiness to intensify the conflict.”
ETLM Assessment:
In a view repeatedly corroborated by CYFIRMA as well as the published findings of the Dutch intelligence, an outright military showdown between Russia and NATO is still viewed as improbable, but it needs to be emphasized that these hybrid methods enable Moscow to sow disruption and exert pressure on Western societies and decision-making without crossing into all-out warfare and thus limiting its political costs. Russia is not likely to ease its cyber campaign in the coming months as its war in Ukraine is coming to a halt, to the contrary.
NightSpire Ransomware Impacts Makimura Co., Ltd.
Summary:
CYFIRMA observed in an underground forum that a company from Japan, Makimura Co., Ltd. (https[:]//makimura[.]co[.]jp/), was compromised by NightSpire Ransomware. Makimura Co., Ltd. is a Japanese textile trading company founded in 1904, specializing in high-quality fabrics and product development for the apparel industry. It focuses on men’s and ladies’ fashion fabrics, business/school uniforms, OEM/ODM production, and overseas sales to luxury brands in Europe and New York. The compromised dataset includes internal records, financial information, client lists, and other confidential and sensitive data belonging to the organization.
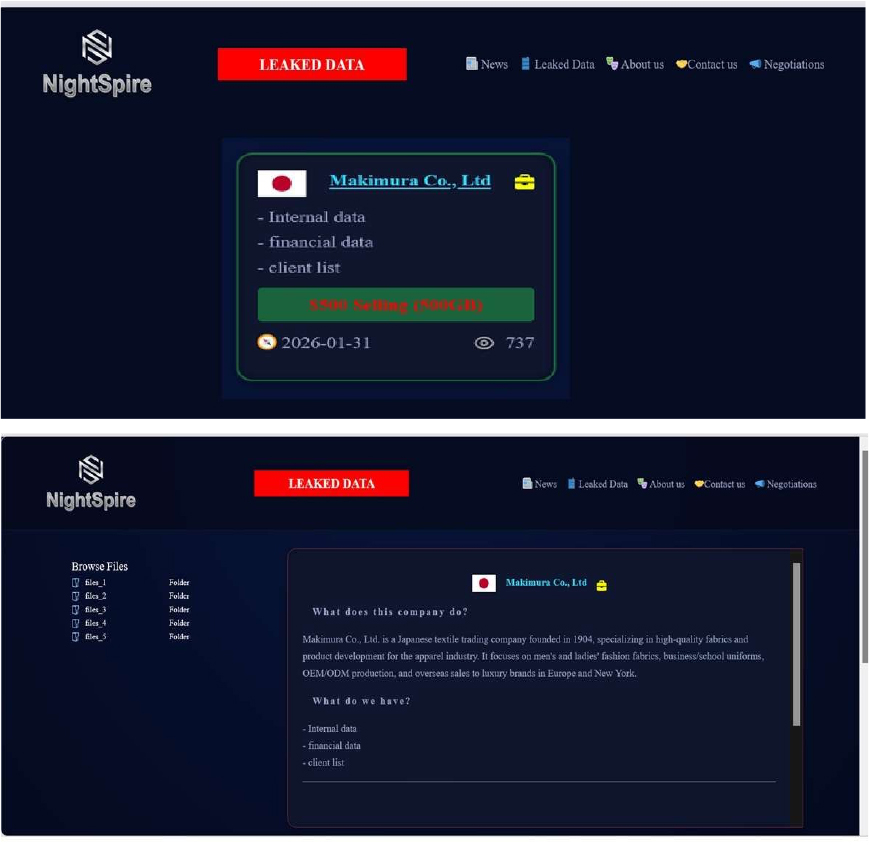
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, NightSpire is a ransomware group that emerged in early 2025, marking itself as a formidable player in the rapidly evolving ransomware landscape. Despite its recent appearance, NightSpire has already gained attention for its aggressive tactics and well-structured operations.
The Gentlemen Ransomware Impacts Sawafi
Summary: CYFIRMA observed in an underground forum that a company from Saudi Arabia, Sawafi(https[:]//www[.]sawafi[.]com/), was compromised by the Gentlemen Ransomware. Sawafi is a Saudi Arabian company specializing in drilling, completions, and production services tailored to enhance oil and gas performance. The data, which has been breached, has not yet appeared on the leak site, indicating that negotiations between the affected party and the ransomware group may be underway. The compromised data includes confidential and sensitive information belonging to the organization.
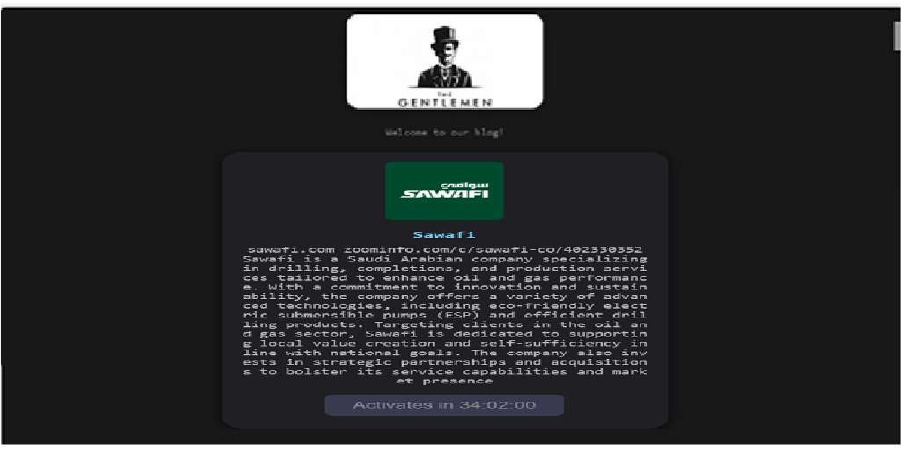
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, the Gentlemen Ransomware is a highly adaptive and globally active threat that leverages dual-extortion tactics, combining data theft with file encryption. The group employs advanced evasion and persistence techniques, supports cross-platform and scalable ransomware deployment, and conducts targeted attacks across multiple industries and geographic regions. This combination of capabilities makes it a significant risk to enterprise cybersecurity defenses, particularly for organizations with limited detection and incident-response maturity.
Vulnerability in SAIL
Attack Type: Vulnerabilities & Exploits
Target Technology: Image Processing Libraries / Universal Components
Vulnerability CVE-2026-27168
CVSS Base Score: 8.8 Source
Vulnerability Type: Heap-based buffer overflow
Summary:
The vulnerability allows a remote attacker to execute arbitrary code on the target system.
Relevancy & Insights:
The vulnerability exists due to a boundary error in Sail- codecs-xwd. A remote attacker on the local network can pass specially crafted data to the application, trigger a heap-based buffer overflow, and execute arbitrary code on the target system.
Impact:
Successful exploitation of this vulnerability may result in complete compromise of the vulnerable system.
Affected Products:
https[:]//github.com/HappySeaFox/sail/security/advisories/GHSA-3g38-x2pj- mv55/#poc
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
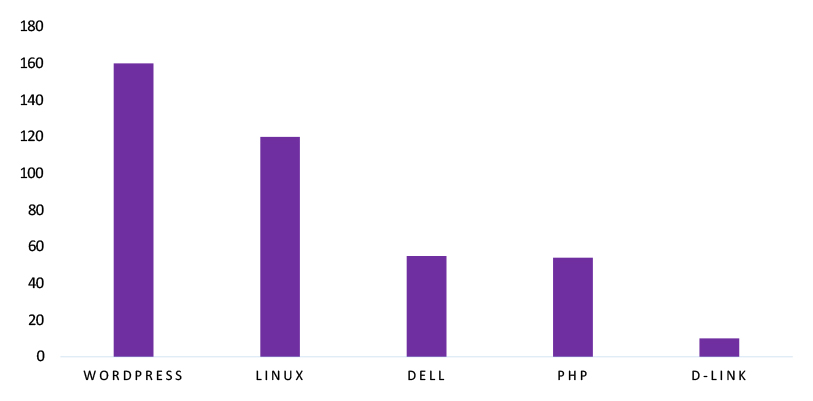
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies due to a range of vulnerabilities. The following are the top 5 most affected technologies.
ETLM Assessment
Vulnerability in SAIL introduces significant security risks to systems relying on this image processing library for parsing and handling user-supplied image files. Since SAIL is integrated across various applications and platforms, exploitation can impact multiple industries, including digital content management, media software, embedded systems, and enterprise applications that process untrusted image inputs. Ensuring the security of SAIL is critical for maintaining the integrity of image parsing workflows, preventing remote code execution, and safeguarding system stability across different environments. Therefore, addressing this vulnerability is essential to ensuring secure image processing operations, preventing compromise through malicious media files, and protecting systems across diverse sectors and geographic regions.
Space Bears Ransomware attacked and published the data of PT Darma Henwa Tbk Threat Actor: Space Bears Ransomware
Attack Type: Ransomware
Objective: Data Leak, Financial Gains Target Technology: Web Applications Target Industry: Mining
Target Geography: Indonesia
Business Impact:
Operational Disruption, Data Loss, Financial Loss, Potential Reputational Damage
Summary:
Recently, we observed that Space Bears Ransomware attacked and published the data of PT Darma Henwa Tbk(https[:]//www[.]ptdh[.]co[.]id/) on its dark web website. PT Darma Henwa Tbk is a company that specializes in mining support and excavation activities. It provides services such as metal fabrication, machinery repair, and equipment leasing. The company also engages in road and railroad construction, as well as building and civil construction. The ransomware incident resulted in the exposure of sensitive data, including employee personal information, contracts and client records, financial reports and audit documents, project and development details, Outlook email communications, and internal security reports.
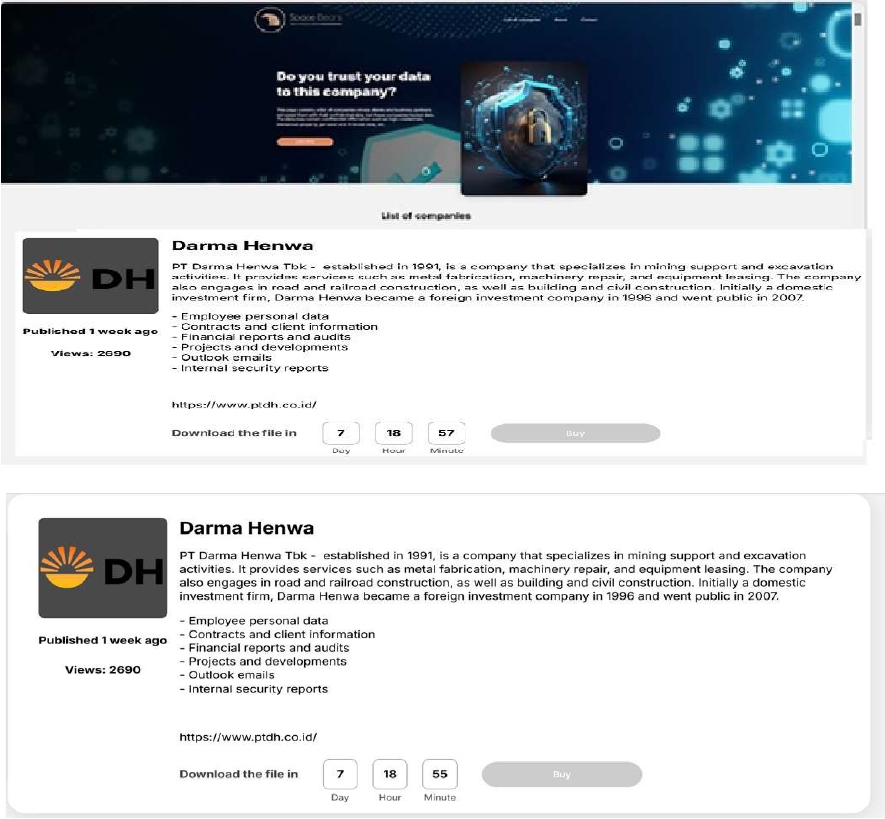
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, Space Bears ransomware represents a significant threat in the evolving landscape of cybercrime. With its aggressive tactics, association with established ransomware operations like Phobos, and focus on double extortion, organizations are advised to bolster their cybersecurity measures to mitigate risks associated with such attacks. Continuous monitoring of this group’s activities will be essential for understanding their methods and potential impact on various sectors.
Osaka Prefectural Government Data Advertised on a Leak Site Attack Type: Data leak
Target Industry: Government Target Geography: Japan Objective: Financial Gains
Business Impact: Data Loss, Reputational Damage
Summary:
The CYFIRMA research team has identified a post published on a well-known underground hacking forum by a threat actor operating under the alias “TelephoneHooliganism.” The actor is advertising the sale of a dataset allegedly originating from the Osaka Prefectural Government, associated with the official domain pref[.]Osaka[.]lg[.]jp.
According to the forum post, the dataset contains approximately 685,000 records comprising personal and contact data, including employee and administrative information. The actor claims the data is organized into structured sections reflecting internal operational categories.
The threat actor describes the dataset as structured into three primary categories:
1. Contacts
This section allegedly contains public service employee contact records used for internal and external communications. The fields listed in the forum post include:
2. Payroll Records
The second dataset section reportedly contains payroll and compensation information for administrative and budgeting purposes, including:
3. Service Requests
This portion allegedly includes records of citizen-initiated service requests and administrative cases handled by prefectural offices. Fields referenced include:
The actor “TelephoneHooliganism” is offering the dataset for sale at a stated price of USD 950. The post includes sample file links to substantiate the claim and indicates willingness to conduct transactions via private messaging or escrow services.
The authenticity of the breach claim remains unverified at the time of reporting, as the information currently originates solely from the threat actor’s forum post.
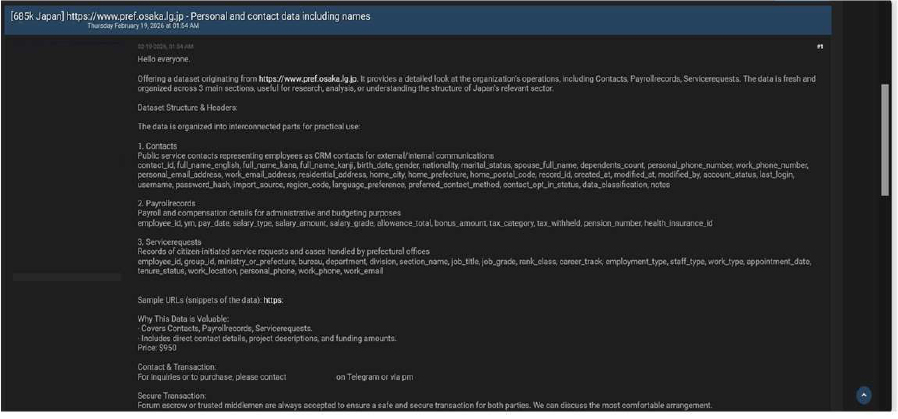
Source: Underground Forums
ETLM Assessment:
The threat actor operating under the alias “TelephoneHooliganism” is assessed to be an active and technically capable group focused on data-leak operations. Multiple reliable sources have linked the group to several cybersecurity incidents involving unauthorized system intrusions and the advertisement or sale of exfiltrated information on dark web marketplaces.
Almutawa, Tanmia, and Bin Omairah’s Data Advertised on a Leak Site
Attack Type: Data leak
Target Industry: Construction & Engineering, Procurement & Construction,
Target Geography: Saudi Arabia
Objective: Data Theft, Financial Gains
Business Impact: Data Loss, Reputational Damage
Summary:
The CYFIRMA research team has identified a post published on a dark web forum by a user operating under the alias “Ryhem,” advertising the sale of allegedly stolen data from three companies described as contractors for Saudi Aramco.
The threat actor claims to be selling a consolidated dataset containing sensitive corporate, personnel, and infrastructure-related information. The total advertised data volume is approximately 15 GB, with an asking price of USD 40,000.
Allegedly Affected Organisations
The forum post references the following entities as impacted contractors:
The actor further states that, following negotiations with one of the companies, its data was removed from the sale listing. However, no verifiable evidence supporting this claim has been provided.
Description of the Alleged Compromised Data According to the forum post, the dataset includes:
1. Personnel and HR Records
2. Corporate and Administrative Documents
3. Infrastructure and Technical Data
The post includes preview images that appear to show engineering schematics, identification documents, and internal documentation to substantiate the claim.
Additionally, the threat actor states that a sample file containing data of approximately 1,000 personnel records is available for verification purposes.
The actor “Ryhem” is offering the data for USD 40,000 and provides external download links and encrypted contact channels for negotiation. The post encourages potential buyers to initiate contact via private messaging or secure communication platforms.
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
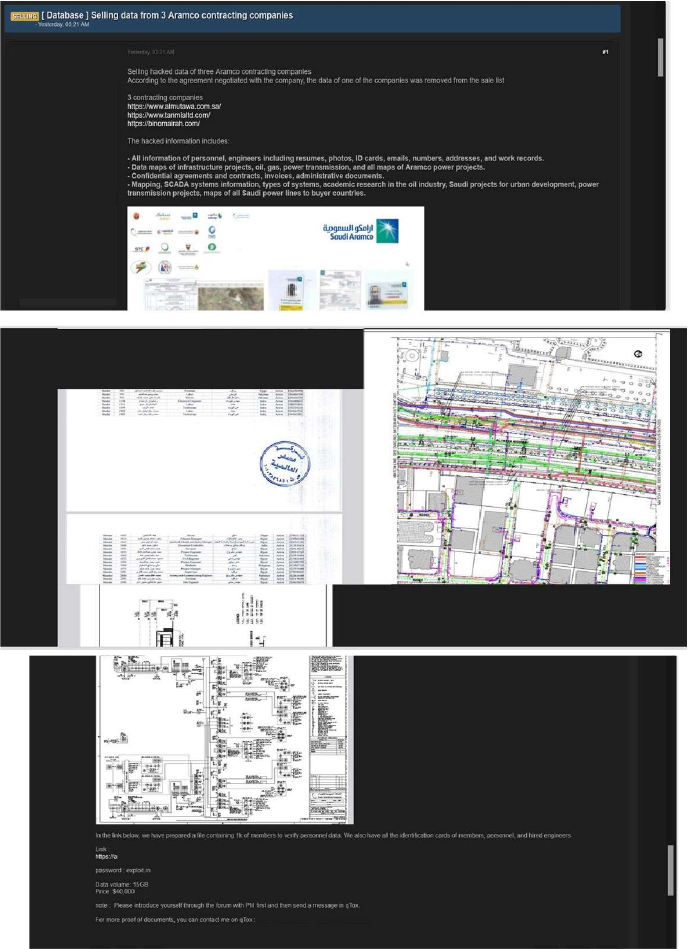
Source: Underground Forums
Relevancy & Insights:
Financially motivated cybercriminals are continuously looking for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to gain access and steal valuable data. Subsequently, the stolen data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor operating under the alias “TelephoneHooliganism” is assessed to be an active and technically capable group focused on data-leak operations. Multiple reliable sources have linked the group to several cybersecurity incidents involving unauthorized system intrusions and the advertisement or sale of exfiltrated information on dark web marketplaces.
The group’s activities reflect the ongoing and increasingly complex threat landscape driven by underground cybercriminal ecosystems. These developments emphasize the urgent need for organizations to strengthen their security posture through continuous monitoring, integration of actionable threat intelligence, and implementation of proactive defensive measures to safeguard sensitive information and critical infrastructure.
Recommendations: Enhance the cybersecurity posture by:
The CYFIRMA research team has identified a post published on a well-known underground hacking forum by a user operating under the alias “TelephoneHooliganism.” The threat actor is advertising the sale of a dataset allegedly originating from the Bangkok Metropolitan Administration (BMA), associated with the official domain Bangkok[.]go[.]th.
According to the forum post, the dataset contains approximately 137,000 user contact records, including email addresses and phone numbers. The actor claims that the data is structured and categorized across multiple operational areas related to city administration and public services.
Details of the Alleged Dataset
The threat actor states that the dataset is organized into three primary sections:
1. Citizen Contact Records
The dataset allegedly includes citizen contact details used for municipal communication. The fields referenced in the post include:
2. City Service Booking Records
This section reportedly contains information related to citizen requests and bookings for city services, including:
3. Public Health Clinic Records
The post also claims the inclusion of sensitive healthcare-related data from public health clinics within the city. Alleged fields include:
The actor “TelephoneHooliganism” is offering the dataset for sale at a stated price of USD 1,200 and has shared sample file links to support the claim. The post suggests a willingness to use escrow or intermediaries for transaction purposes.
The structured nature of the described dataset, including CRM-related fields and internal record identifiers, may indicate potential unauthorized access to backend administrative systems rather than a simple surface-level scrape.
The authenticity of the breach claim remains unverified at the time of reporting, as the information currently originates solely from the threat actor’s forum post.
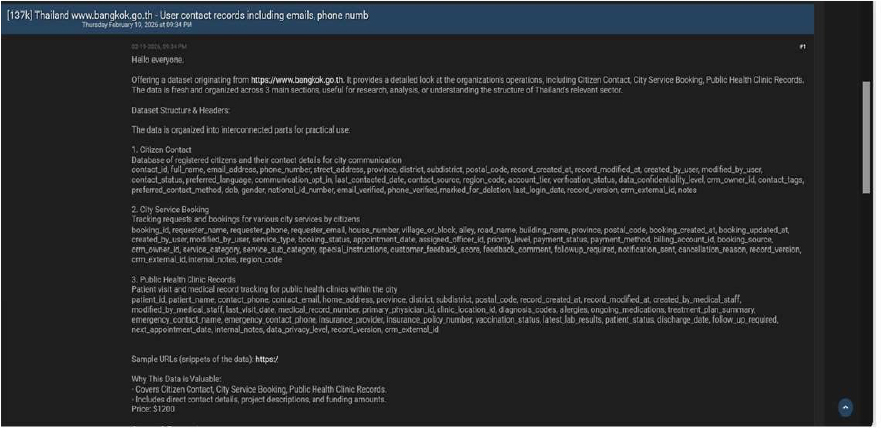
Source: Underground Forums
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
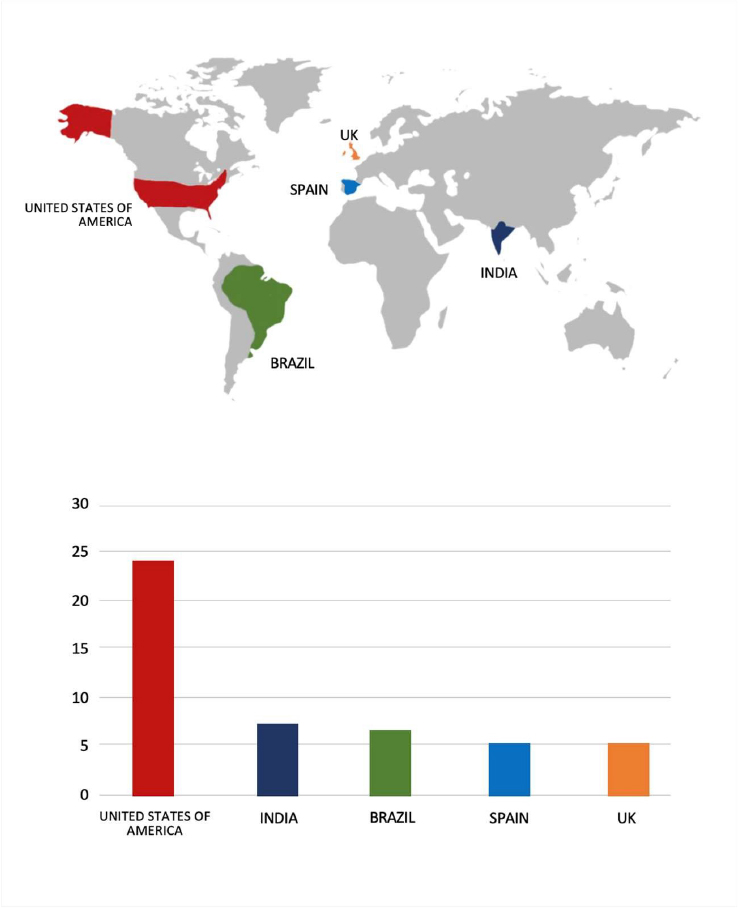
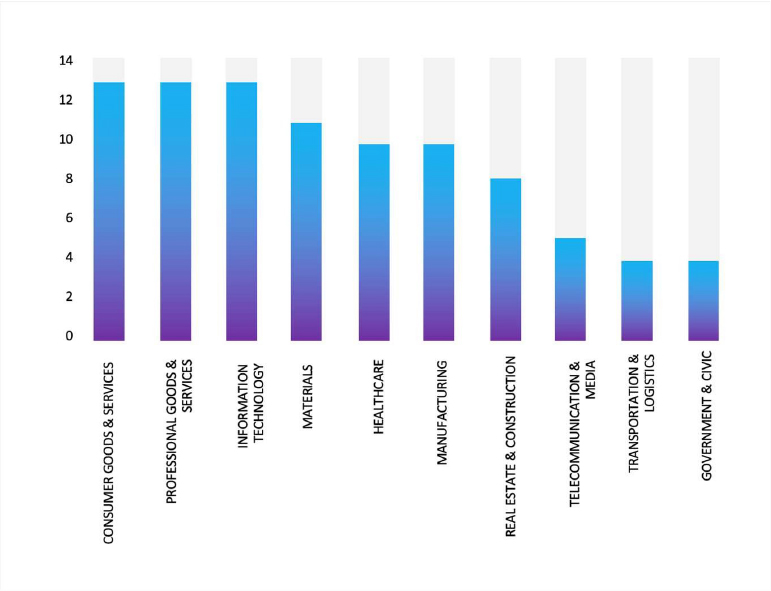
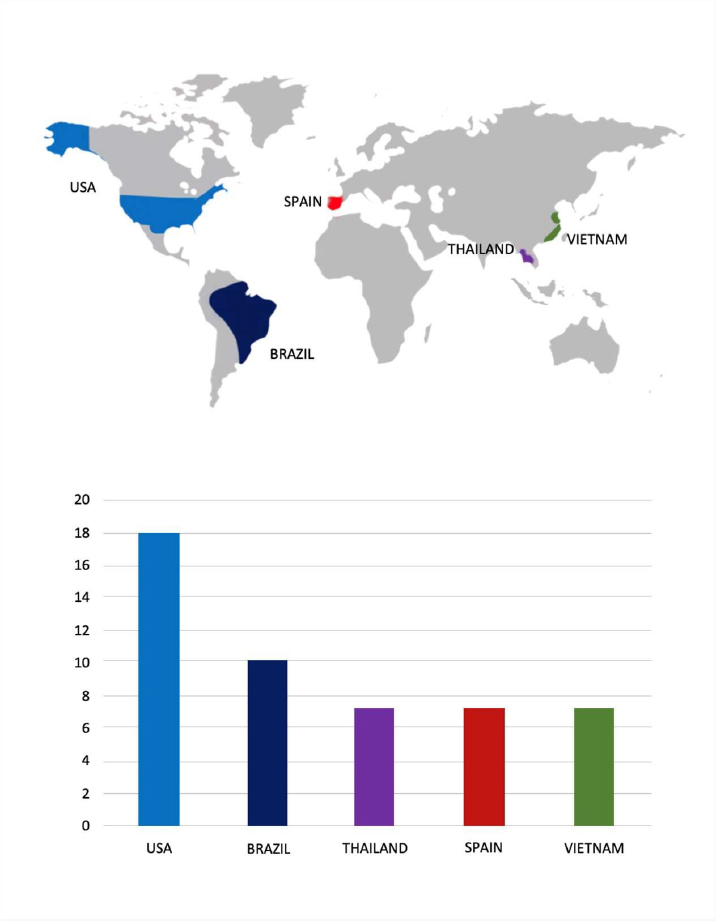
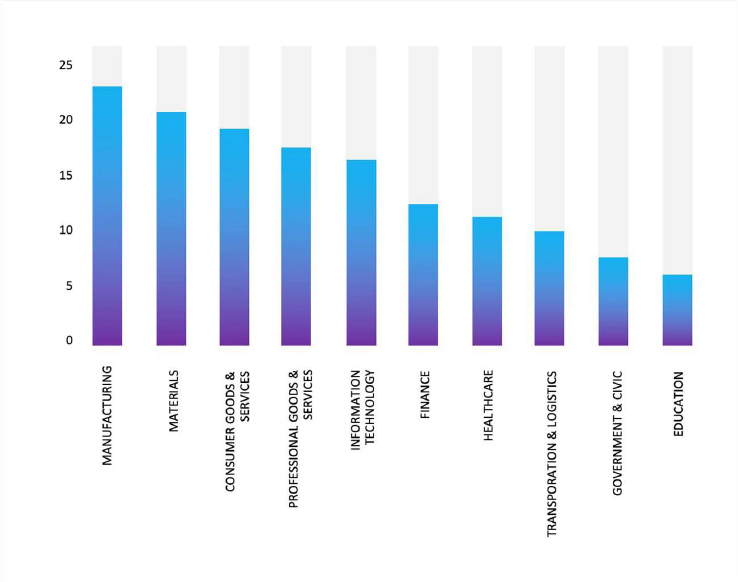
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
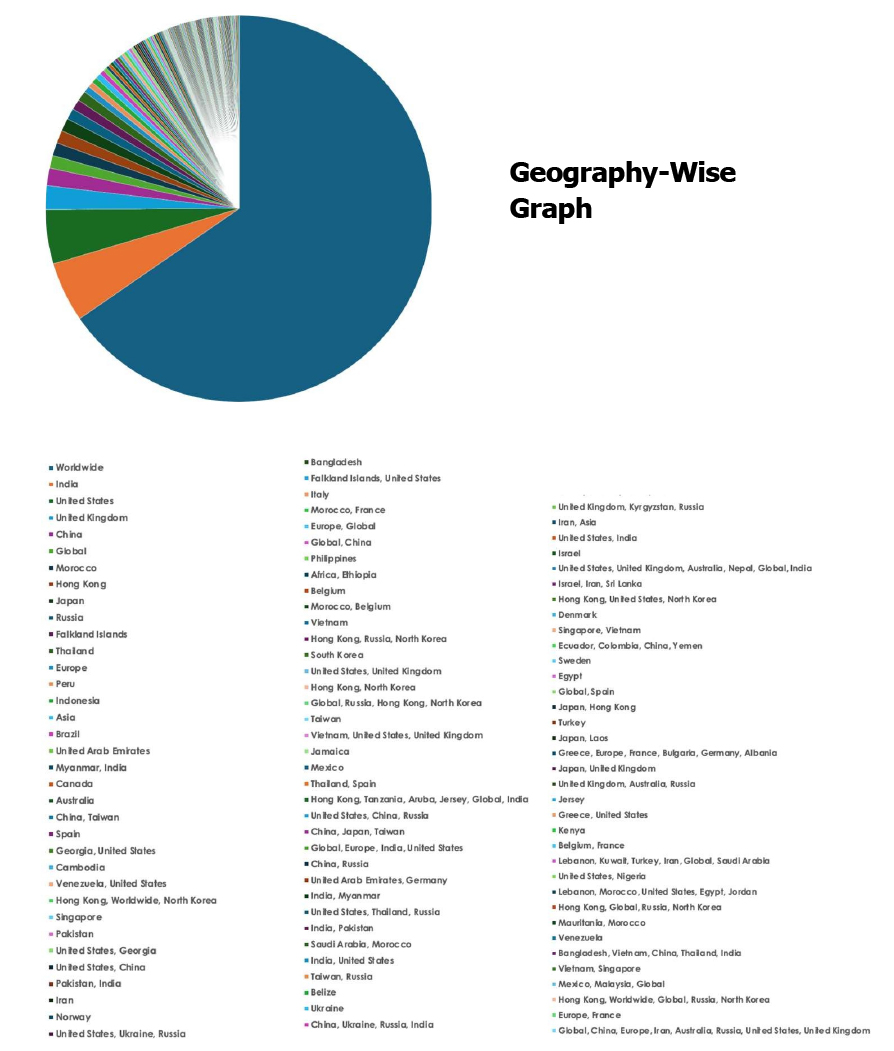
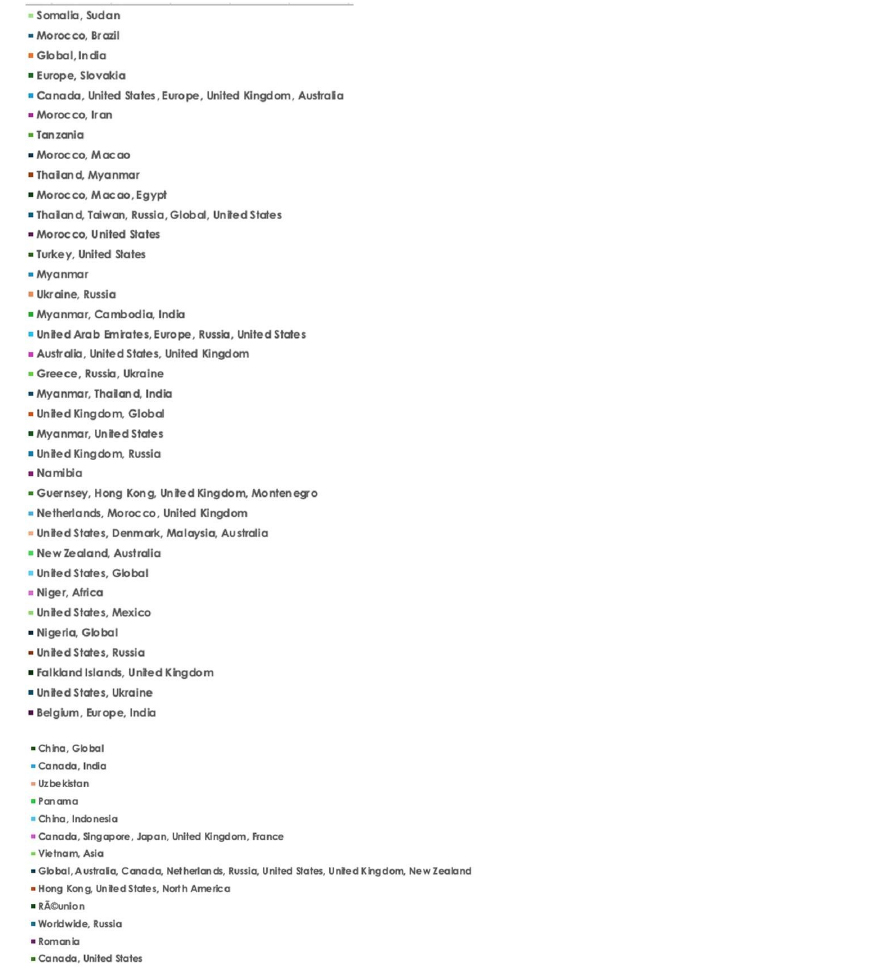
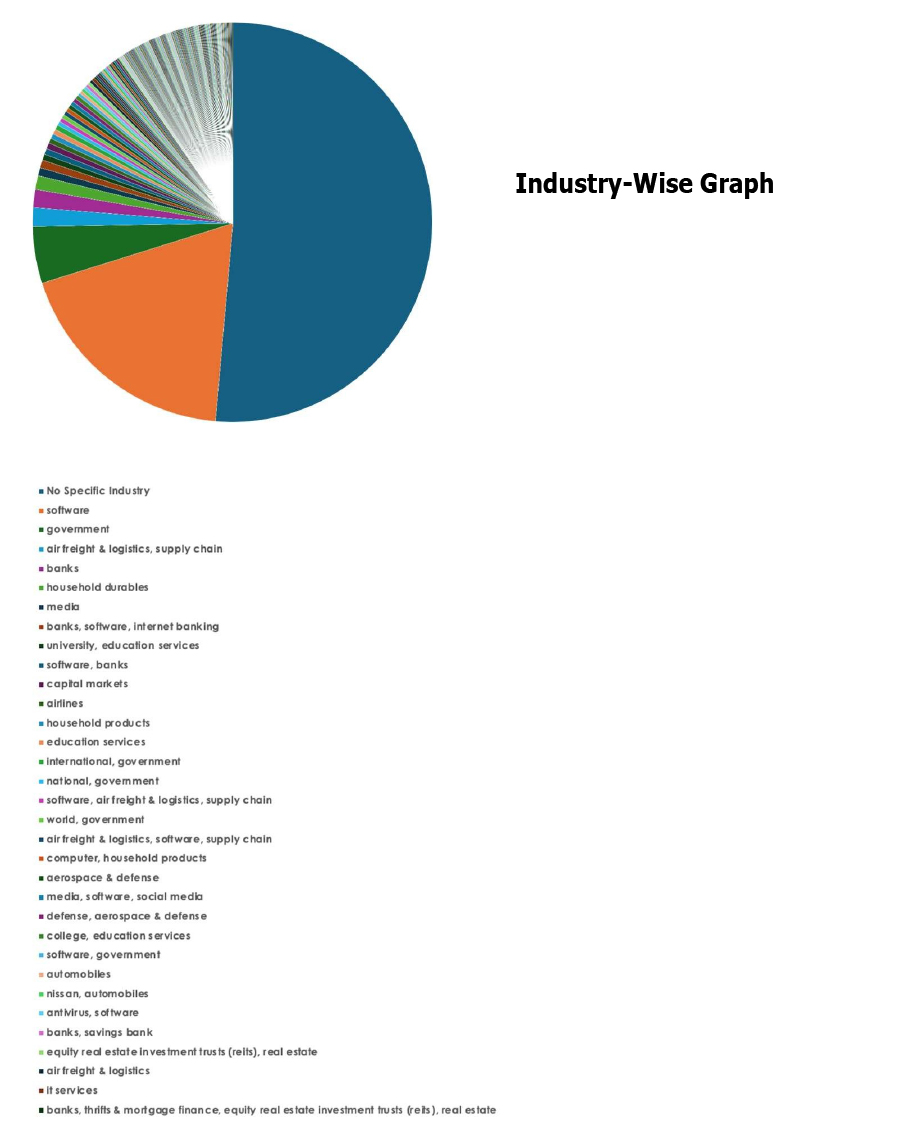
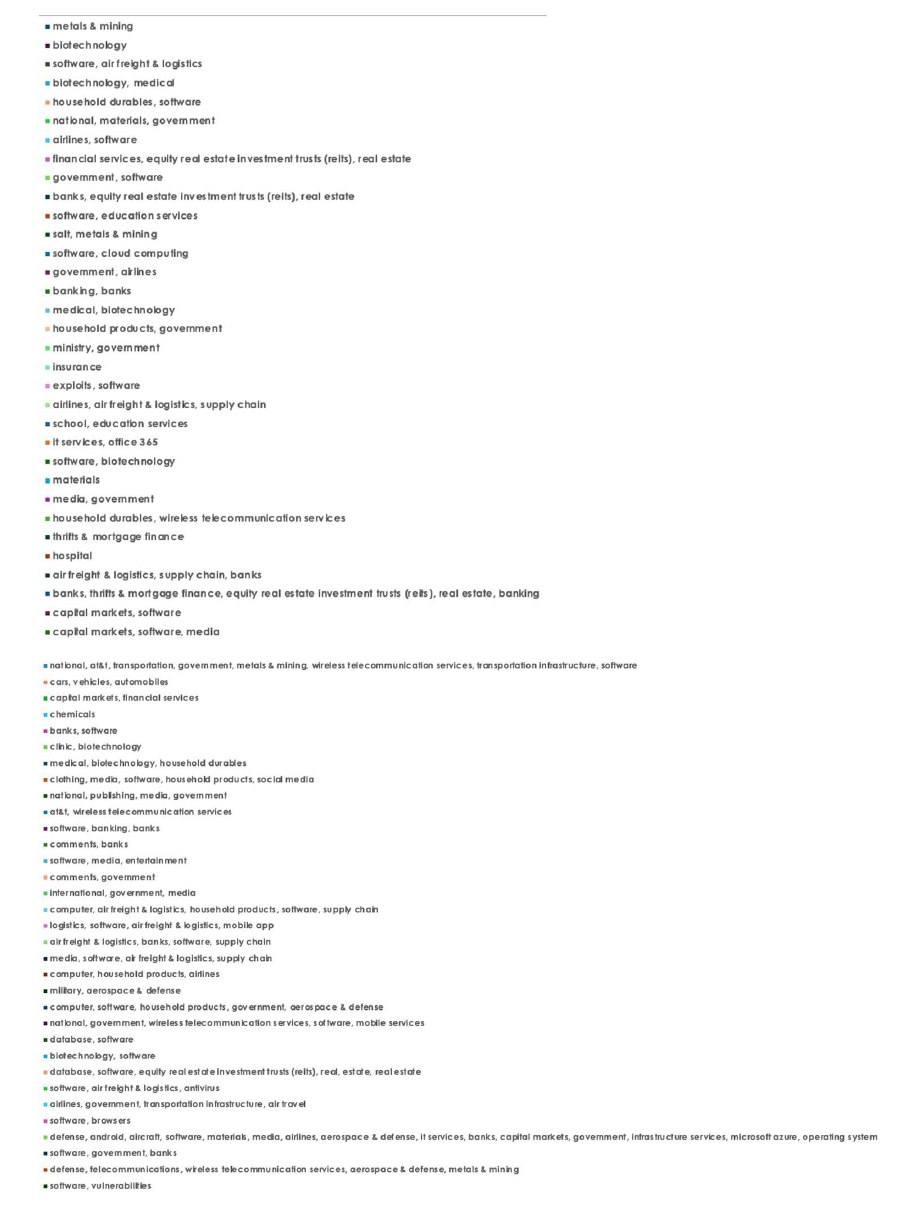
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.