


CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple industries, geography, and technology, that could be relevant to your organization.
Type: Ransomware
Target Technologies: Windows OS, Local file systems, Network shares
Introduction:
CYFIRMA Research and Advisory Team has found NBLOCK Ransomware while monitoring various underground forums as part of our Threat Discovery Process.
NBLOCK Ransomware
NBLock ransomware has been identified as a file-encrypting malware strain designed to restrict access to victim data by encrypting files and appending the “.NBLock” extension, rendering them inaccessible without a decryption key. Upon execution, the malware enumerates local files and network-accessible storage, applying encryption (explicitly referenced as AES-256 in the ransom note) and modifying file states to prevent normal access. It then drops a ransom note named “README_NBLOCK.txt” and may alter the desktop wallpaper to display an infection message, indicating successful compromise. The malware warns victims not to delete or modify a critical file (e.g., key.bin), implying the use of locally stored encryption metadata required for decryption. Communication with attackers is conducted via a Tor-based negotiation portal, indicating anonymized command-and-control interaction. Additionally, the infection may be bundled with or lead to deployment of secondary payloads such as password-stealing trojans, increasing overall impact. Distribution vectors include phishing emails, malicious attachments, cracked software, and exploit-based delivery mechanisms. There is currently no publicly available decryption tool, and payment does not guarantee recovery, as attackers retain full control over the decryption process.
Screenshot: File encrypted by the ransomware (Source: Surface Web)
The ransom note associated with NBLock ransomware, typically delivered as “README_NBLOCK.txt”, informs victims that all files have been encrypted using AES-256 encryption and are inaccessible without a decryptor controlled by the attackers. It explicitly instructs victims not to modify or delete the file key.bin, suggesting that it contains essential cryptographic material required for recovery. The note directs victims to install the Tor Browser and access a designated onion-based negotiation portal, indicating that communications are intended to be anonymous and controlled by the threat actors. The message emphasizes that only the attackers possess the decryption capability and discourages panic while simultaneously reinforcing dependency on their decryptor. Unlike more advanced ransomware families, the note does not strongly emphasize data exfiltration but focuses on encryption-based extortion and controlled negotiation. The overall structure reflects standard ransomware coercion techniques, combining technical instructions (Tor access, key preservation) with warnings designed to prevent independent recovery attempts and ensure victim compliance.
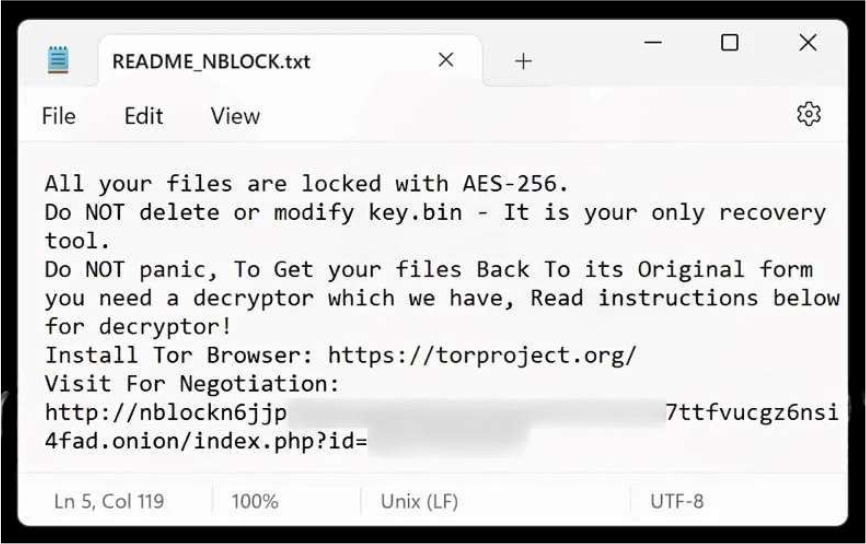
Screenshot: The appearance of NBLOCK ’s Ransom Note (Source: Surface Web)
The following are the TTPs based on the MITRE Attack Framework
| Tactic | Technique ID | Technique Name |
| Execution | T1106 | Native API |
| Persistence | T1112 | Modify Registry |
| Persistence | T1546 | Event Triggered Execution |
| Persistence | T1546.001 | Event Triggered Execution: Change Default File Association |
| Privilege Escalation | T1055 | Process Injection |
| Privilege Escalation | T1546 | Event Triggered Execution |
| Privilege Escalation | T1546.001 | Event Triggered Execution: Change Default File Association |
| Privilege Escalation | T1548 | Abuse Elevation Control Mechanism |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1027.002 | Obfuscated Files or Information: Software Packing |
| Defense Evasion | T1036 | Masquerading |
| Defense Evasion | T1055 | Process Injection |
| Defense Evasion | T1070 | Indicator Removal |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1112 | Modify Registry |
| Defense Evasion | T1202 | Indirect Command Execution |
| Defense Evasion | T1222 | File and Directory Permissions Modification |
| Defense Evasion | T1497 | Virtualization/Sandbox Evasion |
| Defense Evasion | T1548 | Abuse Elevation Control Mechanism |
| Defense Evasion | T1562 | Impair Defenses |
| Defense Evasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| Defense Evasion | T1564 | Hide Artifacts |
| Defense Evasion | T1564.003 | Hide Artifacts: Hidden Window |
| Credential Access | T1003 | OS Credential Dumping |
| Credential Access | T1552 | Unsecured Credentials |
| Credential Access | T1552.001 | Unsecured Credentials: Credentials In Files |
| Discovery | T1012 | Query Registry |
| Discovery | T1033 | System Owner/User Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1087 | Account Discovery |
| Discovery | T1497 | Virtualization/Sandbox Evasion |
| Collection | T1005 | Data from Local System |
| Collection | T1114 | Email Collection |
| Command and Control | T1071 | Application Layer Protocol |
| Command and Control | T1090 | Proxy |
| Impact | T1485 | Data Destruction |
| Impact | T1486 | Data Encrypted for Impact |
| Impact | T1490 | Inhibit System Recovery |
Relevancy and Insights:
ETLM Assessment:
CYFIRMA’s analytical assessment suggests that NBLock ransomware is likely to evolve within conventional ransomware development trajectories, with future iterations focusing on enhancing operational efficiency and resilience rather than introducing novel capabilities. Given its current implementation of AES-256 encryption, Tor-based negotiation infrastructure, and dependency on local key artifacts (e.g., key.bin), operators may improve encryption speed, expand file targeting logic (including network shares and removable media), and strengthen persistence mechanisms to ensure execution continuity across reboots. There is a realistic possibility of integrating multi-stage infection chains, where initial loaders or trojans deploy NBLock alongside credential-stealing or lateral movement tools, as already suggested by bundled malware behavior. Future variants may also incorporate double extortion mechanisms, such as data exfiltration prior to encryption, although no direct evidence confirms this capability at present. Additionally, attackers may refine delivery techniques through phishing kits, exploit kits, and malicious software bundling to increase infection rates. However, there is currently no evidence of advanced capabilities such as worm-like propagation, zero-day exploitation, or highly targeted intrusion campaigns, indicating that near-term evolution will remain incremental and aligned with opportunistic ransomware operations.
Sigma rule:
title: Shadow Copies Deletion Using Operating Systems Utilities tags:
– attack.defense-evasion
– attack.impact
– attack.t1070
– attack.t1490 logsource:
category: process_creation product: windows
detection: selection1_img:
– Image|endswith:
– ‘\powershell.exe’
– ‘\pwsh.exe’
– ‘\wmic.exe’
– ‘\vssadmin.exe’
– ‘\diskshadow.exe’
– OriginalFileName:
– ‘PowerShell.EXE’
– ‘pwsh.dll’
– ‘wmic.exe’
– ‘VSSADMIN.EXE’
– ‘diskshadow.exe’ selection1_cli:
CommandLine|contains|all:
– ‘shadow’ # will match “delete shadows” and “shadowcopy delete” and “shadowstorage”
– ‘delete’ selection2_img:
– Image|endswith: ‘\wbadmin.exe’
– OriginalFileName: ‘WBADMIN.EXE’ selection2_cli:
CommandLine|contains|all:
– ‘delete’
– ‘catalog’
– ‘quiet’ # will match -quiet or /quiet selection3_img:
– Image|endswith: ‘\vssadmin.exe’
– OriginalFileName: ‘VSSADMIN.EXE’ selection3_cli:
CommandLine|contains|all:
– ‘resize’
– ‘shadowstorage’ CommandLine|contains:
– ‘unbounded’
– ‘/MaxSize=’
condition: (all of selection1*) or (all of selection2*) or (all of selection3*) falsepositives:
– Legitimate Administrator deletes Shadow Copies using operating systems utilities for legitimate reason
– LANDesk LDClient Ivanti-PSModule (PS EncodedCommand) level: high
(Source: Surface Web)
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
Type: Information Stealer
Objectives: Data Exfiltration
Target Technology: Windows OS
Target Geography: Global
CYFIRMA collects data from various forums, based on which the trend is ascertained. We identified a few popular malwares that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week, “AZORult” malware is in focus.
Overview of Operation AZORult Malware
The malware AZORult has been identified as a serious security concern through our internal analysis. It operates in a subtle manner, attempting to blend in with normal system activity and avoid detection. The malware establishes itself without causing any immediate or visible disruption, making it difficult for users to recognize its presence. Its behavior aligns with that of a Trojan, as it performs unauthorized actions silently in the background. Over time, it maintains its presence within the system to ensure continued access. This quiet and persistent operation increases the risk of long-term compromise. Overall, it represents a significant threat due to its ability to function unnoticed while carrying out malicious activities.
Analysis further indicates that AZORult is designed to maintain continued access to the infected system. It achieves this by ensuring it can automatically run each time the system starts, allowing it to remain active over long periods. At the same time, it uses techniques to hide its true nature, making it more difficult for users and security tools to detect its presence. This combination of persistence and concealment highlights a clear intent to remain undetected.
In addition, the malware shows signs of communicating with external servers, which may allow it to send or receive data. This behavior raises concerns about the possible exposure of sensitive information, as well as the risk of further malicious actions being carried out remotely. Overall, the observed activities indicate that AZORult poses a serious risk to both system security and user data.
Attack Method
The attack methodology associated with AZORult is initiated through the execution of a file that appears legitimate, serving as the initial point of compromise. Upon execution, the malware activates and begins operating within the system by leveraging existing system components and external modules. This method enables it to execute its functionality dynamically while maintaining a low profile. In certain instances, it utilizes trusted system utilities to run or generate code, allowing its activity to blend with normal system operations and reducing the likelihood of immediate detection.
Following execution, the malware establishes persistence to ensure continued access to the compromised environment. This is achieved through modifications to key areas of the Windows Registry that control automatic program execution during system startup. In addition, it creates and stores copies of itself within commonly accessed user directories, often under misleading or inconspicuous file names. These actions enable the malware to remain active across system reboots and sustain its presence without requiring further user involvement.
To evade detection, AZORult employs a range of concealment techniques. It may disguise its operations by imitating legitimate processes and, in some cases, inject its code into trusted applications. This allows malicious activities to be carried out under the guise of normal system behavior. Furthermore, the malware incorporates obfuscation mechanisms to hide its internal structure and operational logic, thereby complicating analysis and reducing the effectiveness of traditional detection methods. Once persistence is established, the malware proceeds to communicate with external infrastructure controlled by threat actors. It utilizes standard web-based protocols, often over encrypted channels, to transmit data and receive instructions. Prior to this, it performs system reconnaissance to gather relevant information from the infected machine. The collected data is then exfiltrated to remote servers, potentially exposing sensitive information. This coordinated sequence of actions highlights a well-structured attack flow designed to maintain access, avoid detection, and facilitate unauthorized data extraction.
The following are the TTPs based on the MITRE Attack Framework for Enterprise
| Tactic | Technique ID | Technique Name |
| Execution | T1129 | Shared Modules |
| Persistence | T1112 | Modify Registry |
| T1547 | Boot or Logon Autostart Execution | |
| Privilege Escalation | T1055 | Process Injection |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| T1036 | Masquerading | |
| Discovery | ||
| T1012 | Query Registry | |
| T1057 | Process Discovery | |
| T1082 | System Information Discovery | |
| Collection | T1005 | Data from Local System |
| Command and control | T1071 | Application Layer Protocol |
INSIGHTS
A notable characteristic of AZORult is its ability to operate without drawing immediate attention. Rather than causing visible disruption or system instability, it functions in a controlled and unobtrusive manner. This approach allows malware to remain active within the environment for extended durations, reducing the likelihood of detection through user observation or routine system monitoring.
Another key observation is its deliberate effort to integrate seamlessly within the host environment. By utilizing familiar directory structures and adopting file names that resemble legitimate applications, the malware minimizes suspicion. This behavior reflects a strategic use of trusted system elements, enabling it to persist without raising immediate concerns and making identification more challenging in the absence of detailed inspection.
Furthermore, the malware’s communication with external infrastructure suggests that it operates as part of a coordinated framework rather than as an isolated instance. Its interaction with remote systems indicates a structured operation, where the infected machine serves a role within a broader malicious network. This interconnected functionality highlights the organized nature of such threats and their reliance on external coordination.
ETLM ASSESSMENT
From an ETLM perspective, threats such as AZORult are expected to increasingly challenge organizational resilience by operating in ways that are less visible yet more persistent. At the executive level, this may translate into heightened business risks related to data exposure and operational trust, even in the absence of obvious disruptions. From a technical standpoint, security teams may face growing difficulty in distinguishing malicious activity from normal system behavior as such threats continue to blend into everyday operations. At the leadership level, there may be an increased need to address employee awareness and accountability, as human interaction remains a key element in the success of such attacks. Overall, the evolving nature of these threats suggests a shift toward more discreet, long-term compromises that impact both organizational security posture and workforce reliability.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems.
YARA Rules
rule AZORult_Malware
{
meta:
description = “Detects AZORult variant using confirmed C2 indicators and hash IOC” author = “CYFIRMA”
date = “2026-04-13”
strings:
/* C2 and behavior indicators */
$c2_domain1 = “gpsindia.biz”
$c2_uri = “/crm/kha/32/index.php”
$api1 = “ip-api.com/json”
$api2 = “dotbit.me”
$mutex = “A5D09762-49414907-AA4894C3-595B189D-330970087”
$path = “AppData\\Roaming\\ProPlayer”
/* Hash IOC */
$hash_sha256 = “d792d051caa23b98f546ca5eae5200f1714d5953958729f8d841ea37a3618b8e”
condition:
uint16(0) == 0x5A4D and
(2 of ($c2_domain1, $c2_uri, $api1, $api2, $mutex, $path) or $hash_sha256)
}
Strategic Recommendations
These are high-level, long-term initiatives to strengthen organizational cybersecurity posture:
Management Recommendations
These focus on policies, procedures, and governance to ensure proper oversight and risk mitigation:
Tactical Recommendations
These are immediate, actionable steps to prevent, detect, and respond to malware at the operational level:
1. Weekly Attack Types and Trends
Key Intelligence Signals:
2. Threat Actor in Focus
APT28 (Fancy Bear): A Strategic Cyber Espionage Actor Aligned with Russian Intelligence Objectives
About the Threat Actor
Fancy Bear is a Russian state-sponsored advanced persistent threat (APT) group believed to be closely affiliated with the country’s intelligence services. Active since 2007, the group has been linked to multiple cyber operations targeting government and political entities. It is widely assessed that Fancy Bear has conducted campaigns aimed at influencing elections in various countries to support candidates aligned with Russian strategic interests.
Details on Exploited Vulnerabilities
| CVE ID | Affected Products | CVSS Score | Exploit Links |
| CVE-2023-38831 | WinRAR | 7.8 | Link |
| CVE-2023-50224 | TP-Link TL-WR841N (all firmware versions) | 6.5 | – |
| CVE-2016-5195 | Linux kernel | 7.0 | Link1, Link2, Link3, Link4, Link5, Link6 |
| CVE-2020-0688 | Microsoft Exchange | 8.8 | Link 1, Link 2 |
| CVE-2015-2545 | Microsoft Office | 7.8 | – |
| CVE-2026-21509 | Microsoft Office | 7.8 | – |
| CVE-2025-66376 | Zimbra Collaboration (ZCS) | 6.1 | – |
| CVE-2026-23760 | SmarterTools SmarterMail | 9.3 | – |
| CVE-2012-0158 | Microsoft Office | 8.8 | – |
| CVE-2023-22028 | MySQL Server | 4.9 | – |
TTPs based on MITRE ATT&CK Framework
| Tactic | ID | Technique |
| Reconnaissance | T1591 | Gather Victim Org Information |
| Reconnaissance | T1598.003 | Phishing for Information: Spearphishing Link |
| Reconnaissance | T1598 | Phishing for Information |
| Reconnaissance | T1596 | Search Open Technical Databases |
| Resource Development | T1583.001 | Acquire Infrastructure: Domains |
| Resource Development | T1583.003 | Acquire Infrastructure: Virtual Private Server |
| Resource Development | T1583.006 | Acquire Infrastructure: Web Services |
| Resource Development | T1586.002 | Compromise Accounts: Email Accounts |
| Resource Development | T1584.008 | Compromise Infrastructure: Network Devices |
| Resource Development | T1588.002 | Obtain Capabilities: Tool |
| Initial Access | T1189 | Drive-by Compromise |
| Initial Access | T1190 | Exploit Public-Facing Application |
| Initial Access | T1133 | External Remote Services |
| Initial Access | T1091 | Replication Through Removable Media |
| Initial Access | T1199 | Trusted Relationship |
| Initial Access | T1078 | Valid Accounts |
| Initial Access | T1078.004 | Valid Accounts: Cloud Accounts |
| Initial Access | T1566.001 | Phishing: Spear phishing Attachment |
| Execution | T1204.001 | User Execution: Malicious Link |
| Execution | T1203 | Exploitation for Client Execution |
| Execution | T1559.002 | Inter-Process Communication: Dynamic Data Exchange |
| Execution | T1204.002 | User Execution: Malicious File |
| Persistence | T1098.002 | Account Manipulation: Additional Email Delegate Permissions |
| Persistence | T1547.001 |
Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Persistence | T1037.001 | Boot or Logon Initialization Scripts: Logon Script (Windows) |
| Persistence | T1546.015 | Event Triggered Execution: Component Object Model Hijacking |
| Persistence | T1133 | External Remote Services |
| Persistence | T1137.002 | Office Application Startup: Office Test |
| Persistence | T1542.003 | Pre-OS Boot: Bootkit |
| Persistence | T1505.003 | Server Software Component: Web Shell |
| Persistence | T1078 | Valid Accounts |
| Persistence | T1078.004 | Valid Accounts: Cloud Accounts |
| Privilege Escalation | T1134.001 | Access Token Manipulation: Token Impersonation/Theft |
| Privilege Escalation | T1098.002 | Account Manipulation: Additional Email Delegate Permissions |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1037.001 | Boot or Logon Initialization Scripts: Logon Script (Windows) |
| Privilege Escalation | T1546.015 | Event Triggered Execution: Component Object Model Hijacking |
| Privilege Escalation | T1078.004 | Valid Accounts: Cloud Accounts |
| Defense Evasion | T1134.001 | Access Token Manipulation: Token Impersonation/Theft |
| Defense Evasion | T1564.001 | Hide Artifacts: Hidden Files and Directories |
| Defense Evasion | T1564.003 | Hide Artifacts: Hidden Window |
| Defense Evasion | T1070.001 | Indicator Removal: Clear Windows Event Logs |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1070.006 | Indicator Removal: Timestomp |
| Defense Evasion | T1036 | Masquerading |
| Defense Evasion | T1036.005 | Masquerading: Match Legitimate Resource Name or Location |
| Defense Evasion | T1027.013 | Obfuscated Files or Information: Encrypted/Encoded File |
| Defense Evasion | T1542.003 | Pre-OS Boot: Bootkit |
| Defense Evasion | T1014 | Rootkit |
| Defense Evasion | T1218.011 | System Binary Proxy Execution: Rundll32 |
| Defense Evasion | T1221 | Template Injection |
| Defense Evasion | T1550.001 | Use Alternate Authentication Material: Application Access Token |
| Defense Evasion | T1550.002 | Use Alternate Authentication Material: Pass the Hash |
| Defense Evasion | T1078.004 | Valid Accounts: Cloud Accounts |
| Credential Access | T1557.004 | Adversary-in-the-Middle: Evil Twin |
| Credential Access | T1110 | Brute Force |
| Credential Access | T1110.001 | Brute Force: Password Guessing |
| Credential Access | T1110.003 | Brute Force: Password Spraying |
| Credential Access | T1056.001 | Input Capture: Keylogging |
| Credential Access | T1040 | Network Sniffing |
| Credential Access | T1003 | OS Credential Dumping |
| Credential Access | T1003.001 | OS Credential Dumping: LSASS Memory |
| Credential Access | T1003.002 | OS Credential Dumping: Security Account Manager |
| Credential Access | T1003.003 | OS Credential Dumping: NTDS |
| Credential Access | T1528 | Steal Application Access Token |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1040 | Network Sniffing |
| Discovery | T1120 | Peripheral Device Discovery |
| Discovery | T1057 | Process Discovery |
| Lateral Movement | T1210 | Exploitation of Remote Services |
| Lateral Movement | T1091 | Replication Through Removable Media |
| Lateral Movement | T1550.001 | Use Alternate Authentication Material: Application Access Token |
| Lateral Movement | T1550.002 | Use Alternate Authentication Material: Pass the Hash |
| Collection | T1557.004 | Adversary-in-the-Middle: Evil Twin |
| Collection | T1560 | Archive Collected Data |
| Collection | T1560.001 | Archive Collected Data: Archive via Utility |
| Collection | T1119 | Automated Collection |
| Collection | T1213 | Data from Information Repositories |
| Collection | T1213.002 | Data from Information Repositories: Sharepoint |
| Collection | T1005 | Data from Local System |
| Collection | T1039 | Data from Network Shared Drive |
| Collection | T1025 | Data from Removable Media |
| Collection | T1074.001 | Data Staged: Local Data Staging |
| Collection | T1074.002 | Data Staged: Remote Data Staging |
| Collection | T1114.002 | Email Collection: Remote Email Collection |
| Collection | T1056.001 | Input Capture: Keylogging |
| Collection | T1113 | Screen Capture |
| Command and Control | T1001.001 | Data Obfuscation: Junk Data |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and Control | T1071.003 | Application Layer Protocol: Mail Protocols |
| Command and Control | T1092 | Communication Through Removable Media |
| Command and Control | T1573.001 | Encrypted Channel: Symmetric Cryptography |
| Command and Control | T1105 | Ingress Tool Transfer |
| Command and Control | T1090.001 | Proxy: Internal Proxy |
| Command and Control | T1090.002 | Proxy: External Proxy |
| Command and Control | T1090.003 | Proxy: Multi-hop Proxy |
| Command and Control | T1102.002 | Web Service: Bidirectional Communication |
| Exfiltration | T1030 | Data Transfer Size Limits |
| Exfiltration | T1048.002 | Exfiltration Over Alternative Protocol: Exfiltration Over Asymmetric Encrypted Non-C2 Protocol |
| Impact | T1498 | Network Denial of Service |
Latest Developments Observed
The threat actors are suspected of exploiting network routers to hijack DNS configurations, thereby enabling adversary-in-the-middle (AiTM) attacks and facilitating the theft of credentials, including passwords and authentication tokens. The campaign appears to adopt a broad targeting approach, initially compromising a wide pool of victims and subsequently narrowing the focus to individuals or entities of potential intelligence value at various stages of the exploitation lifecycle.
ETLM Insights
APT28, also known as Fancy Bear, is widely attributed to Russia’s military intelligence agency, the GRU. The group has been active for over a decade and is primarily focused on cyber espionage, information operations, and strategic disruption aligned with Russian geopolitical objectives.
APT28’s digital expansion reflects a deliberate and structured approach:
Based on observed activities and targeting patterns, APT28 is likely to continue advancing identity-focused intrusion techniques while leveraging distributed and obfuscated infrastructure to support intelligence collection and influence objectives. This evolving tradecraft positions the group as a persistent and high-confidence espionage threat to government and strategic organizations, with ongoing risks to sensitive communications, authentication systems, and the overall integrity of critical information assets.
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
YARA Rules
rule Multi_IOC_Threat_Detection_Cluster
{
meta:
description = “Combined IOC detection rule including domains, IPs, CVEs, and file artifacts”
author = “CYFIRMA” date = “2026-04-14”
version = “1.0”
strings:
/* Domains */
$domain1 = “zimbrasoft.com.ua” nocase
$domain2 = “rdsnets.com” nocase
$domain3 = “remotepx.net” nocase
$domain4 = “secao.org” nocase
$domain5 = “webstp.com” nocase
/* IP Addresses */
$ip1 = “64.233.180.138”
$ip2 = “91.204.161.90”
$ip3 = “172.67.165.62”
$ip4 = “208.91.197.27”
$ip5 = “208.91.197.132”
/* CVEs */
$cve1 = “CVE-2023-50224”
$cve2 = “CVE-2026-21509”
$cve3 = “CVE-2025-66376”
$cve4 = “CVE-2026-23760”
$cve5 = “CVE-2023-38831”
$cve6 = “CVE-2025-52691”
/* File Artifacts */
$file1 = “update.exe” nocase
$file2 = “3833709f-0947-4371-a557-f7a6c0f368d7.exe” nocase
$file3 = “20140702.txt.gz” nocase
$file4 = “win32 exe” nocase
condition:
any of ($domain*) or any of ($ip*) or any of ($file*) or any of ($cve*)
}
Strategic Recommendations
Management Recommendations
Tactical Recommendations
Cyber Threat Iran Persists During Fragile Ceasefire with Iran
Despite a reported ceasefire between the United States and Iran, security experts and U.S. government agencies are urging organizations to maintain a state of high alert. While the IRGC-linked group “Handala” has announced a temporary pause in targeting the U.S., intelligence reports confirm that Iranian-affiliated Advanced Persistent Threats (APTs) continue to actively compromise critical infrastructure.
As history shows, a formal ceasefire often fails to translate into a reduction of cyber activity. In fact, nation-state actors frequently utilize cyber operations to maintain hostility while enjoying “plausible deniability,” effectively operating just below the threshold of open kinetic warfare. Rather than de-escalating, it is expected that these groups will intensify efforts to infiltrate data centers, defense contractors, and technology firms involved in the conflict.
A joint advisory issued by the FBI, CISA, NSA, EPA, DOE, and U.S. Cyber Command highlights a sustained campaign targeting Industrial Control Systems (ICS). Iranian threat actors are specifically exploiting vulnerabilities in Programmable Logic Controllers (PLCs) and Supervisory Control and Data Acquisition (SCADA) systems across vital sectors, including water and wastewater systems, energy utilities, and municipal government services.
The attackers are bypassing traditional defenses by manipulating the project files and human-machine interface (HMI) displays of these systems. Their methodology includes actively targeting Rockwell Automation/Allen-Bradley products, specifically CompactLogix and Micro850 devices, while simultaneously probing Siemens S7 PLC systems. The attackers use leased, third-party-hosted infrastructure combined with legitimate configuration software to establish authorized-looking connections to the victim’s PLC.
ETLM Assessment:
The history of Iranian cyberattacks against critical infrastructure began to take a significant turn after 2010, when the sophisticated Stuxnet virus was discovered targeting Iran’s nuclear program; this prompted Tehran to invest heavily in its own offensive cyber capabilities. Since then, Iran has transformed from a regional player into a global threat that uses the digital space as an asymmetric tool of state policy. Its operations have gradually shifted from widespread website defacement to highly complex actions against Industrial Control Systems (ICS) and SCADA technologies, as demonstrated by the 2013 incident targeting a dam in New York or repeated attempts to disrupt energy and water networks in Israel and the U.S. These operations, often carried out through proxy groups, are designed to cause physical damage, instill fear, or secure a strategic advantage within the “gray zone” of conflict, where direct attribution is often difficult.
Chinese supercomputer compromised
A hacker operating under the alias “FlamingChina” has claimed responsibility for a massive data breach involving a Chinese state-run supercomputer. The intruder alleges to have exfiltrated over 10 petabytes of highly sensitive information from the National Supercomputing Center (NSCC) in Tianjin. The stolen archive reportedly contains diverse and critical research data, including advancements in aerospace engineering, military applications, bioinformatics, and fusion simulations. The breach appears to affect several high-profile Chinese entities, such as the Aviation Industry Corporation of China, the Commercial Aircraft Corporation of China, and the National University of Defense Technology. To support these claims, the hacker shared a sample of the data, which security experts suggest is authentic. The entire cache is currently being offered for sale on the dark web for several hundred thousand dollars in cryptocurrency.
ETLM Assessment:
Attributing a cyberattack of this magnitude—especially one targeting Chinese state secrets—is notoriously difficult, and the cybersecurity community remains divided on the identity of “FlamingChina.” Experts generally categorize the potential perpetrators into three main groups: state-sponsored actors (espionage), disgruntled insiders, and cybercriminal syndicates. The consensus among cybersecurity experts and intelligence analysts is that the data allegedly stolen from the National Supercomputing Center (NSCC) in Tianjin is critically sensitive. If the breach is legitimate, the vast treasure of data claimed isn’t just about volume; it is about the nature of the information stored in a facility like the NSCC. This center is not a public server; it is a pillar of China’s “Military-Civil Fusion” strategy.
Gunra Ransomware Impacts Thai Petroleum & Trading Co., Ltd.
Summary:
CYFIRMA observed in an underground forum that a company from Thailand, Thai Petroleum & Trading Co., Ltd (https[:]//www[.]tpt[.]co[.]th/th/), was compromised by Gunra Ransomware. Thai Petroleum & Trading Co., Ltd. is a company based in Thailand operating in the petroleum and energy sector. It is involved in the trading, distribution, and supply of petroleum products and related commodities. The company serves industrial and commercial clients within Thailand and potentially across Southeast Asia. It operates within the oil and gas trading industry, contributing to the regional energy supply chain. The ransomware leak indicates exposure of multiple categories of internal corporate data, including structured database files, invoice scan records, and invoice and delivery document systems (DPS), which likely contain financial transactions, billing details, and customer/vendor information. Additionally, technical files were compromised, potentially including system configurations, internal documentation, or IT-related data, along with miscellaneous (“other”) files that may store unclassified or auxiliary business information.
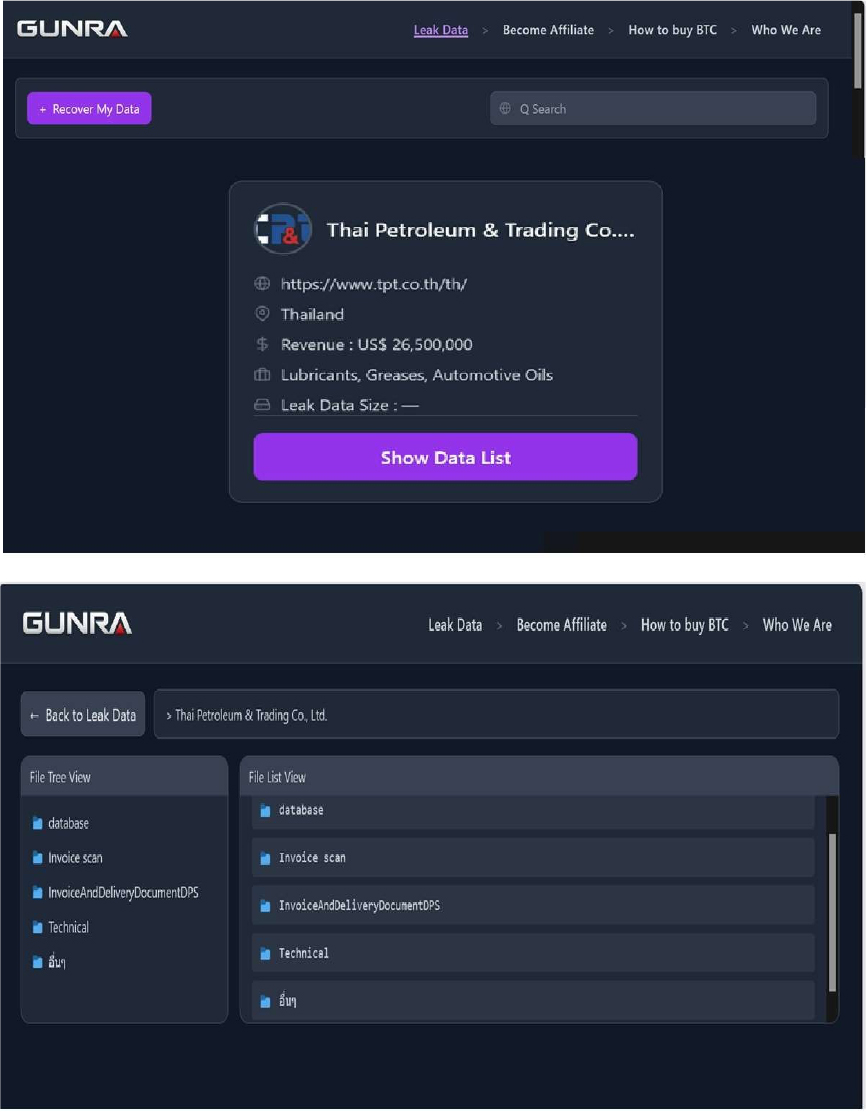
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, Gunra Ransomware is a financially motivated ransomware group that emerged in April 2025, rapidly establishing itself as a significant threat within the evolving ransomware landscape. Leveraging a double-extortion model, Gunra encrypts victim data while simultaneously exfiltrating sensitive information to pressure organizations into paying ransom demands.
The Gentlemen Ransomware Impacts Aichi Electric Co., Ltd
Summary:
CYFIRMA observed in an underground forum that a company from Japan, Aichi Electric Co., Ltd(https[:]//www[.]aichidenki[.]jp/), was compromised by the Gentlemen Ransomware. Aichi Electric Co., Ltd., founded in 1942 and headquartered in Kasugai, Aichi Prefecture, Japan, is a publicly listed manufacturer of power equipment and industrial motors. The company produces transformers, distribution switchgear, control systems, and various motors for electric power infrastructure, serving utilities and industries across Japan and internationally. The compromised data includes confidential and sensitive information belonging to the organization.
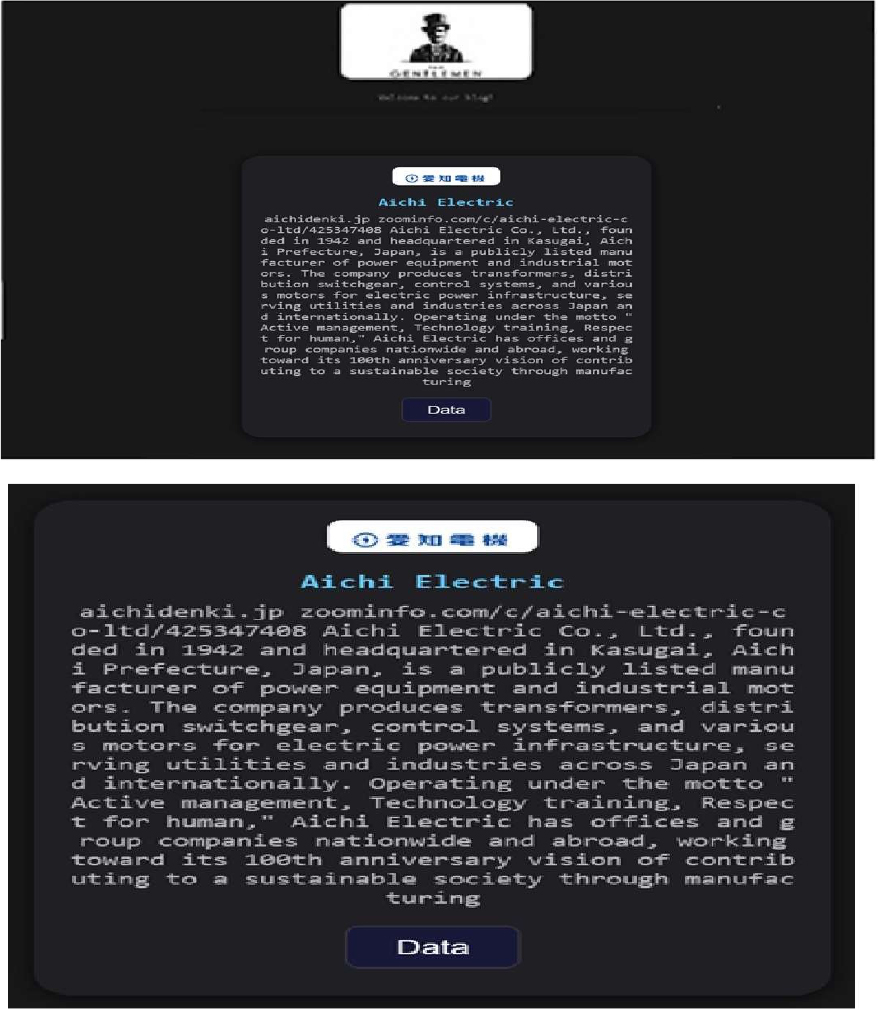
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, the Gentlemen Ransomware is a highly adaptive and globally active threat that leverages dual-extortion tactics, combining data theft with file encryption. The group employs advanced evasion and persistence techniques, supports cross-platform and scalable ransomware deployment, and conducts targeted attacks across multiple industries and geographic regions. This combination of capabilities makes it a significant risk to enterprise cybersecurity defenses, particularly for organizations with limited detection and incident-response maturity.
Vulnerability in Apache ActiveMQ
Relevancy & Insights:
The vulnerability exists due to code injection in the Jolokia JMX-HTTP bridge and exposed ActiveMQ MBeans when handling authenticated exec operations with a crafted discovery URI.
Impact: A remote user can invoke BrokerService.addNetworkConnector(String) or BrokerService.addConnector(String) to execute arbitrary code.
The issue is exposed through the web console endpoint at /api/jolokia/, and exploitation causes remote Spring XML application context loading via the VM transport’s brokerConfig parameter before configuration validation completes.
Affected Products:
https[:]//github[.]com/KONDORDEVSECURITYCORP/CVE-2026-34197
Recommendations:
Monitoring and Detection:
Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies due to a range of vulnerabilities. The following are the top 5 most affected technologies.

ETLM Assessment
Vulnerability in Apache ActiveMQ introduces significant risks to enterprise environments that rely on messaging systems for communication between distributed applications and services. As ActiveMQ is widely used in enterprise architectures and integration pipelines, exploitation of this vulnerability could allow attackers to execute arbitrary code and compromise message flow integrity. Organizations leveraging messaging middleware must ensure timely patching and strict input validation mechanisms to prevent unauthorized access and maintain system reliability. Addressing this vulnerability is essential to protecting communication channels and ensuring the stability of enterprise application ecosystems.
DragonForce Ransomware attacked and published the data of Vietnam Fortress Tools JSC
Summary:
Recently, we observed that DragonForce Ransomware attacked and published the data of Vietnam Fortress Tools JSC (www[.]fortresstools[.]com[.]vn) on its dark web website. Vietnam Fortress Tools JSC, established in 2006, is a leading manufacturer of gardening tools, with over 90% of its products exported to North America and Europe. The company offers a diverse range of gardening tools that meet international standards at competitive prices. The ransomware leak indicates the compromise of a wide range of internal corporate data, including executive and administrative documents (Ban Giam Doc), pricing and quotation files (Don Gia FTVN), and ERP system attachments, which likely contain operational and transactional records. Additionally, bill of materials (BOM) data suggests exposure of product structure and manufacturing details, while HR-related data (employee pictures and records) points to potential leakage of personally identifiable information (PII). Financial records such as accounting data (Ke Toan 2024) and inventory/logistics information (Kho Fortress) were also affected, along with artwork/design files and business-related documents, indicating a comprehensive breach of financial, operational, technical, and employee-sensitive data, posing risks of financial fraud, intellectual property theft, and privacy violations.
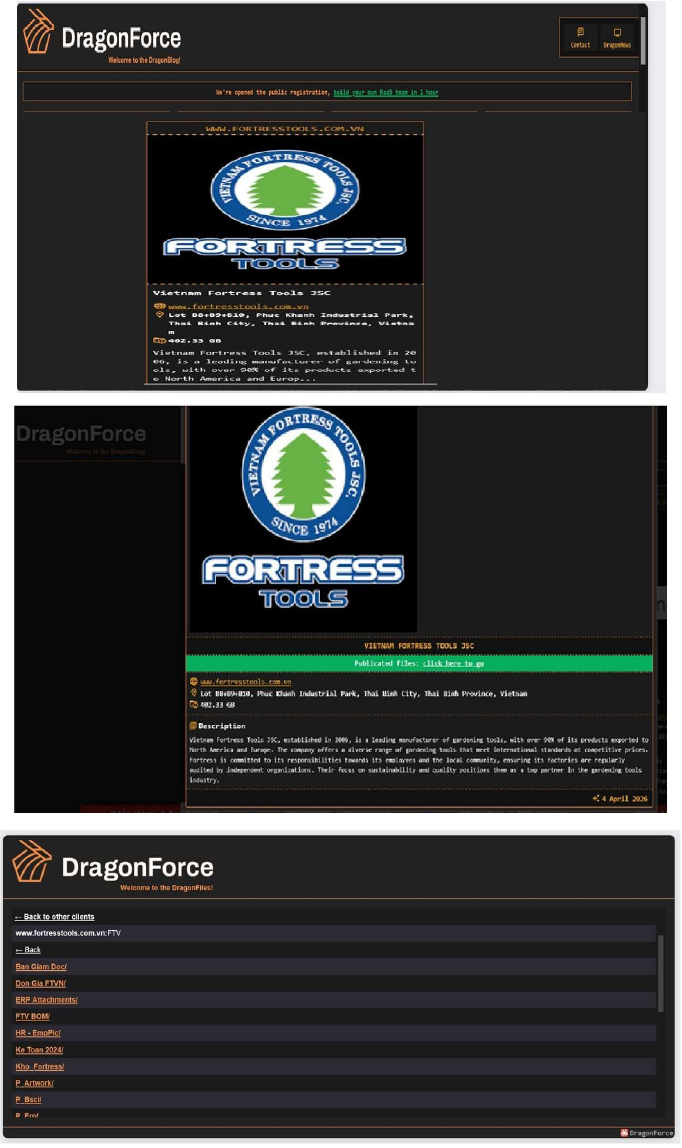
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, DragonForce represents a significant threat in the ransomware landscape due to its advanced operational methods and extensive use of modified ransomware tools. As it continues to target high-profile organizations globally, ongoing vigilance and proactive cybersecurity strategies will be essential for mitigating risks associated with this formidable threat actor. Organizations should remain alert to the evolving tactics employed by groups like DragonForce to protect their sensitive data and maintain operational integrity.
Carwah Data Advertised on a Leak Site
The data leak, which was posted by an actor on a cybercrime forum, targets individuals who have used the application to rent vehicles across the Kingdom of Saudi Arabia.
The allegedly compromised data encompasses 26,078 customer profiles and 6,824 driver’s licenses. According to the actor, the exposed information includes:
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
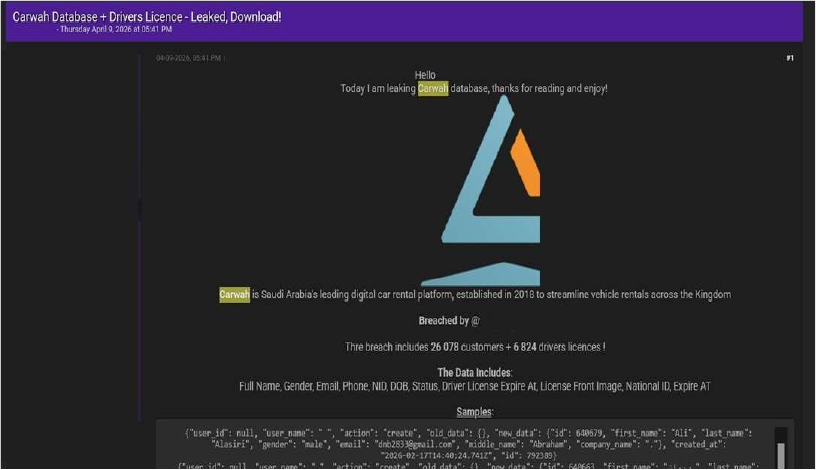
Source: Underground Forums
Kasikornbank (KBank) Customer Data Advertised on a Leak Site
According to the post, the dataset contains creditor and customer-related financial and personal information, presented as structured and ready for exploitation. The actor also offers samples and additional details upon request, indicating potential commercialization of the dataset.
Dataset Description
The threat actor claims the dataset includes comprehensive banking and customer records, likely extracted in January 2026, covering multiple regional branches.
The data appears to be highly structured, with predefined fields and consistent formatting, suggesting extraction from an internal database or CRM system.
Dataset Structure Overview
1. Banking & Organizational Data
This section includes internal banking and branch-related information:
2. Customer Identification Data
This segment contains personally identifiable information (PII) of customers:
3. Contact & Personal Information
Detailed contact and demographic data is included:
4. Account & Financial Metadata
This section provides customer financial and account-related attributes:
Sample Evidence
The forum post includes sample records in structured (JSON-like/PHP array) format, demonstrating:
Sale Details
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
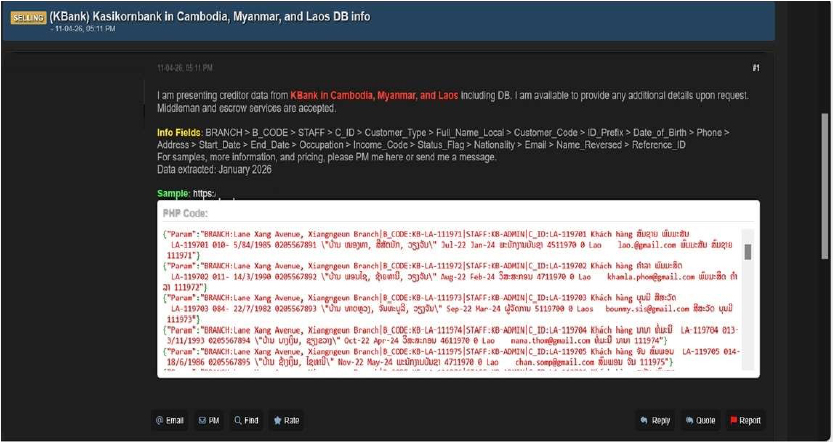
Source: Underground Forums
Relevancy & Insights:
Financially motivated cybercriminals are continuously looking for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to gain access and steal valuable data. Subsequently, the stolen data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor “Spirigatito” is assessed as an active and capable entity focused on data-leak operations, with credible sources linking them to multiple incidents involving unauthorized system access and the distribution or sale of stolen data on dark web platforms. These activities highlight the evolving cyber threat landscape driven by underground criminal networks and emphasize the need for organizations to strengthen cybersecurity through continuous monitoring, enhanced threat intelligence, and proactive defenses to safeguard sensitive data and critical systems.
Recommendations: Enhance the cybersecurity posture by:
The CYFIRMA research team identified a post on a dark web forum by a threat actor operating under the alias “sexybroker”, claiming to sell a large-scale passport dataset allegedly sourced from a Vietnam-based flight booking system.
The actor advertises the dataset as fresh, exclusive, and non-resold, containing passport images and associated contact information of global travelers. The data is positioned as highly valuable for identity exploitation and fraud-related activities.
Dataset Description
According to the forum post:
The dataset is described as complete passport scans combined with personal contact details, significantly increasing its exploitation value.
Dataset Structure Overview
1. Passport Data (Highly Sensitive Identity Data)
This segment allegedly contains:
2. Contact Information
3. Geographic Coverage
The actor claims the dataset spans global travelers, including:
Sample Evidence
The post includes multiple external image links (JPEG files) allegedly showing:
Sale Details
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
Source: Underground Forums
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
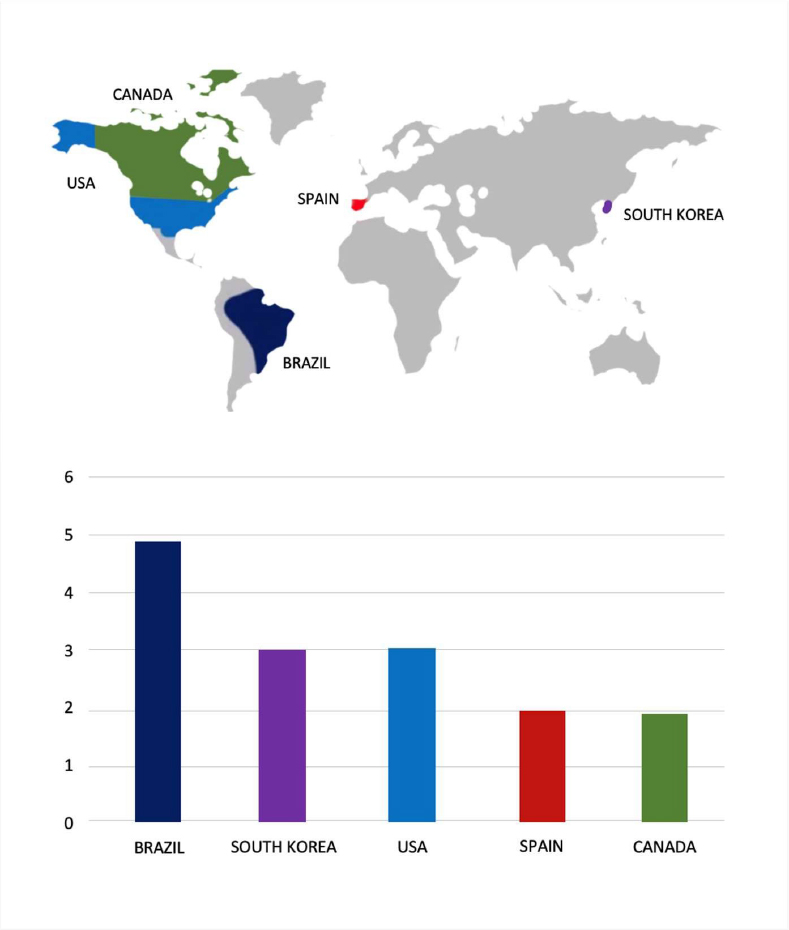
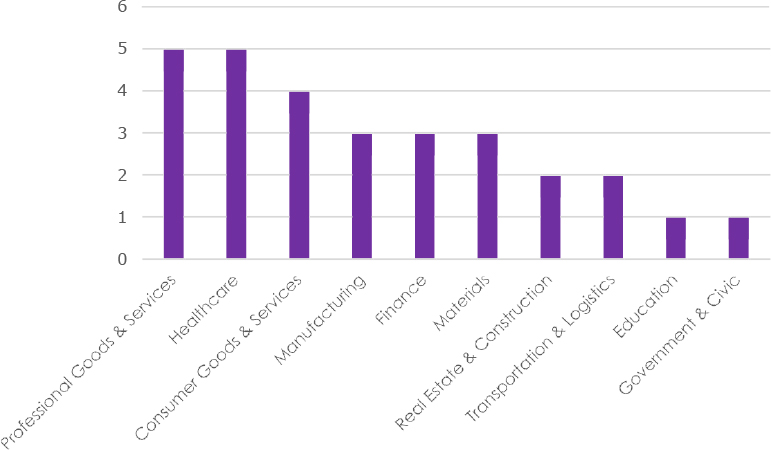
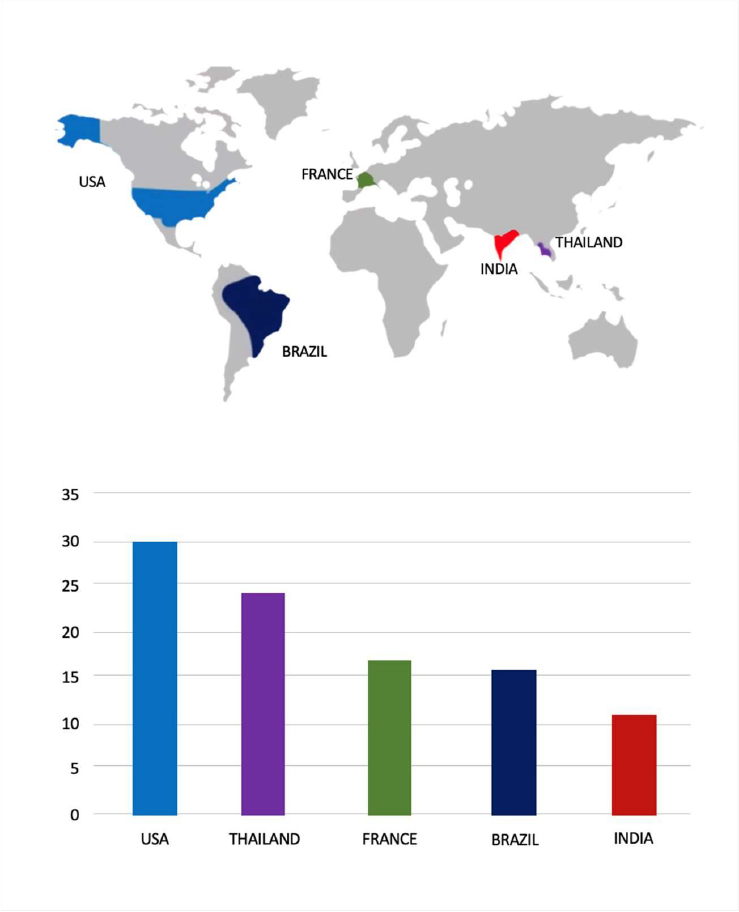
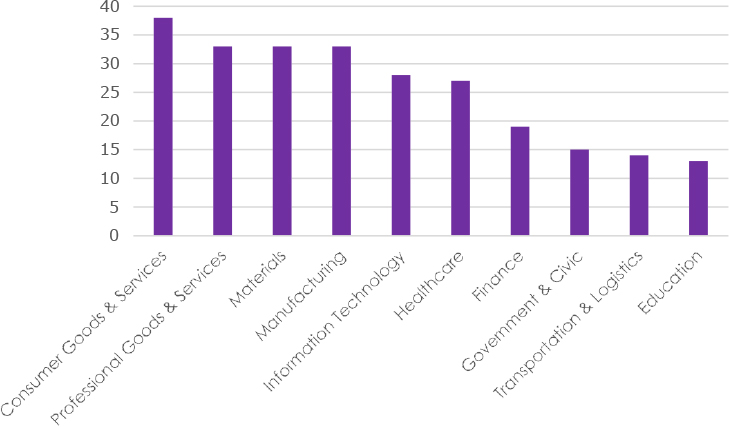
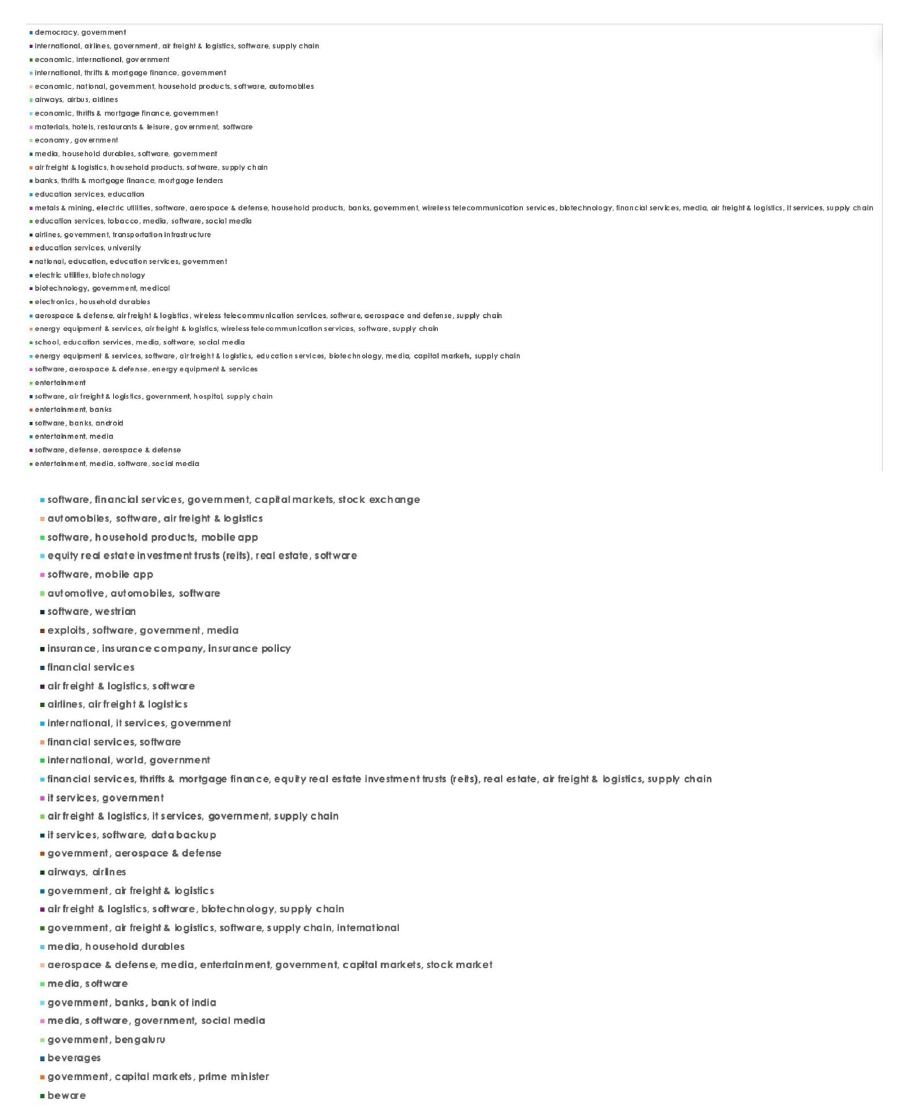
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
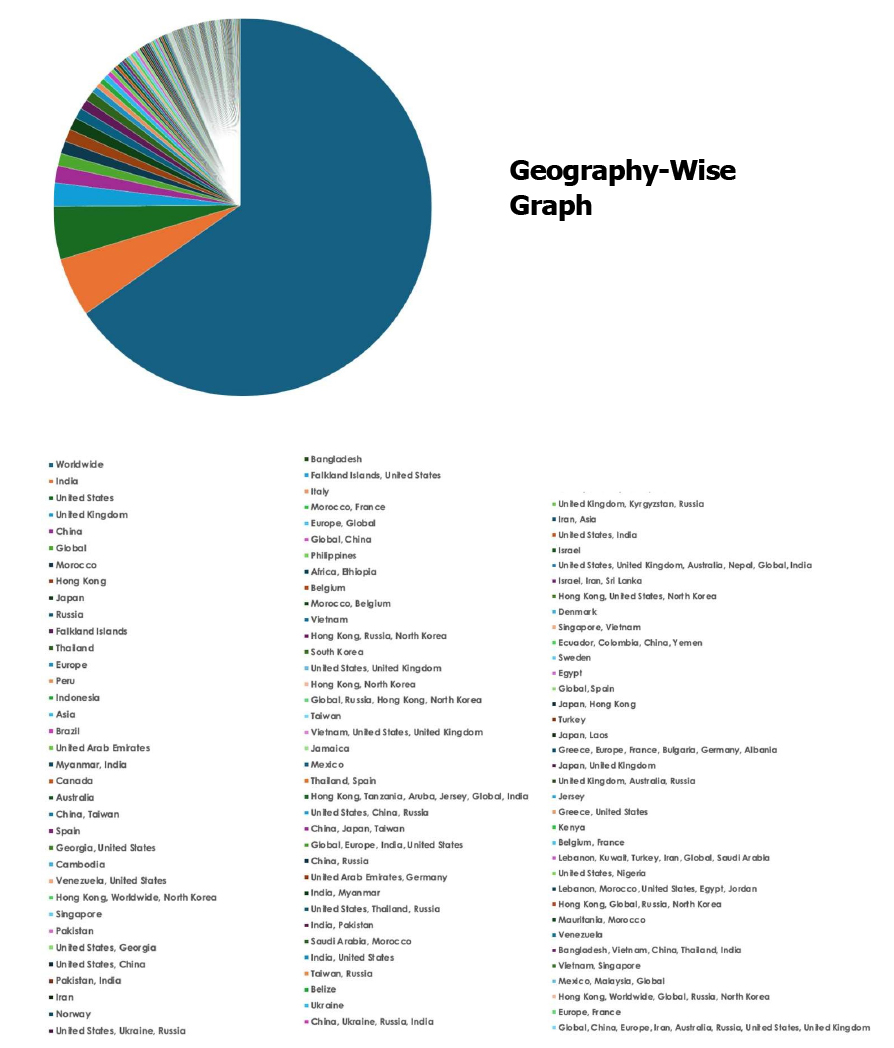
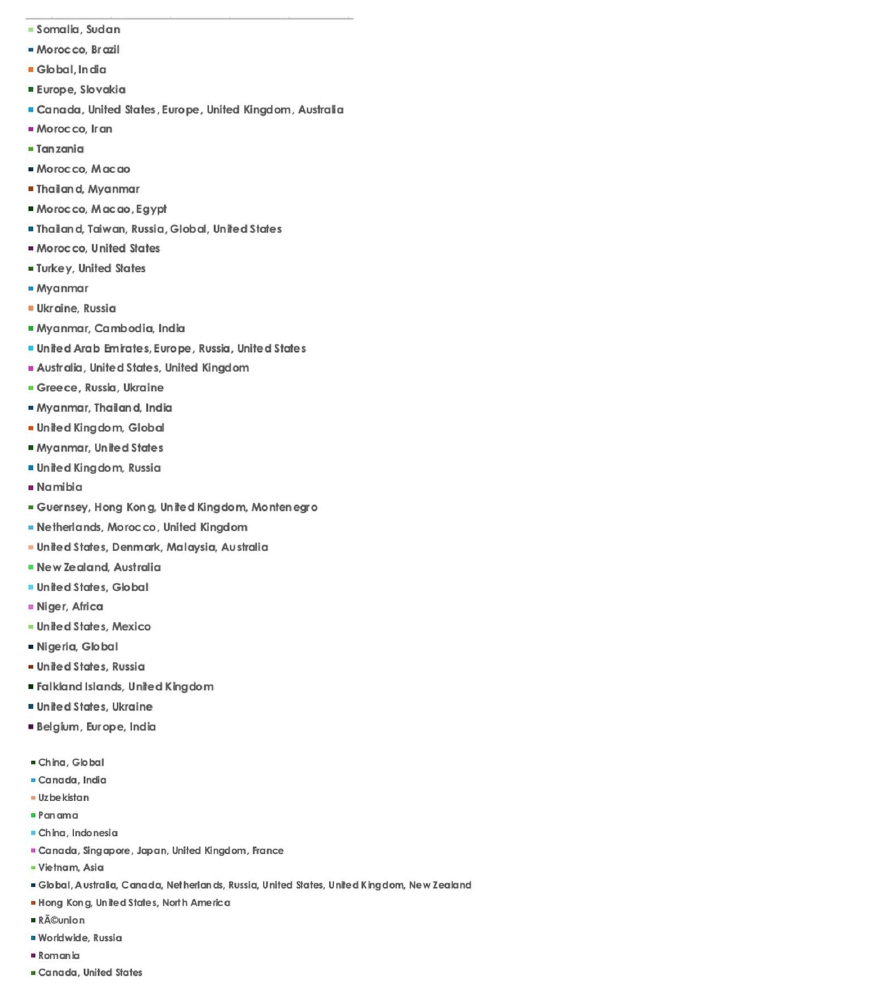
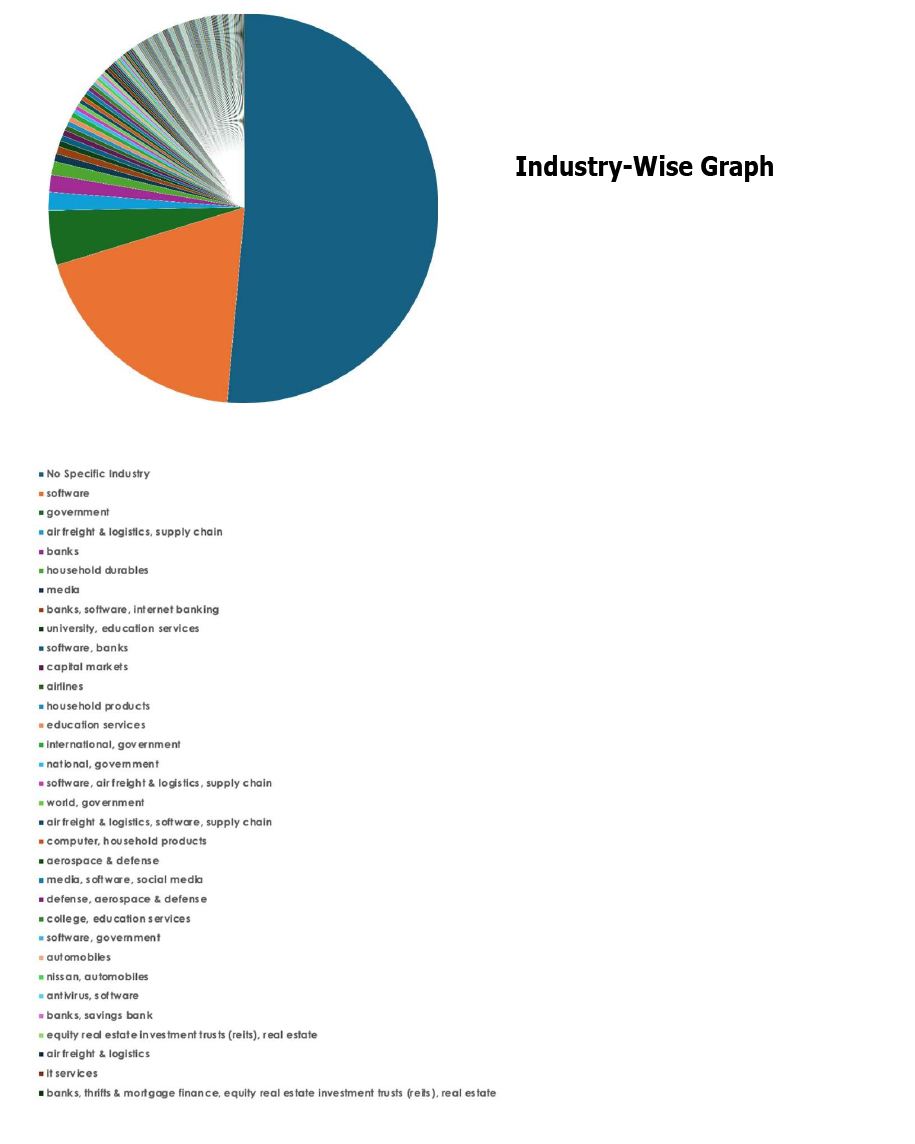
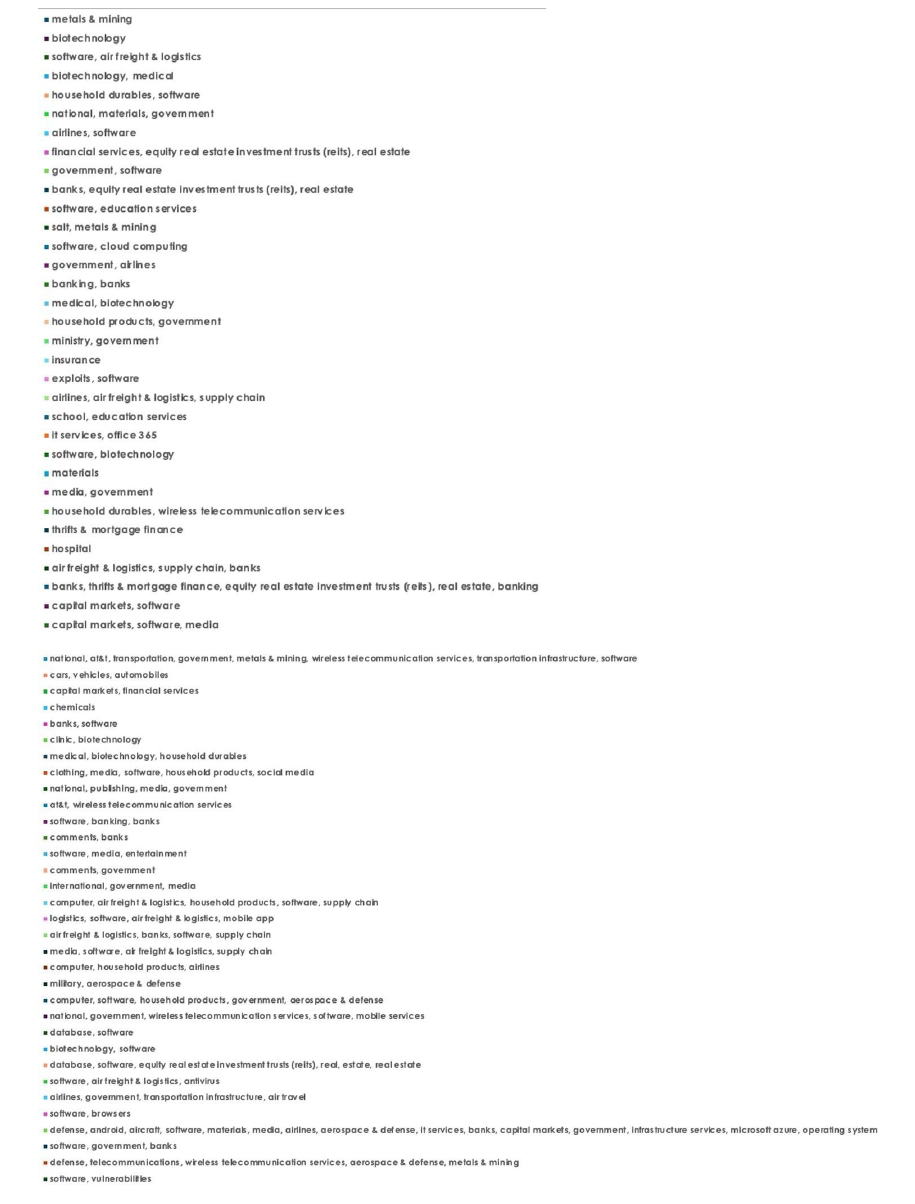
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.