


CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple – industries, geography, and technology – that could be relevant to your organization.
Type: Ransomware
Target Technologies: Windows
Target Industries: Real Estate and Retail
Target Countries: Mexico, Egypt
Introduction
CYFIRMA Research and Advisory Team has observed Payload Ransomware while monitoring various underground forums as part of our Threat Discovery Process.
Payload Ransomware
Payload is a file-encrypting ransomware that appends the “.payload” extension to compromised data and drops a ransom note named RECOVER_payload.txt. It employs a double-extortion model, claiming to exfiltrate sensitive information and threatening public disclosure if the victim fails to initiate negotiations within a defined timeframe. Victims are instructed to access a Tor-based portal to communicate with the attackers and are offered limited free file decryption as proof of capability. The malware avoids encrypting critical system directories and executable file types to maintain system stability, ensuring the victim can still access the ransom instructions and complete payment.

Screenshot of files encrypted by the ransomware (Source: Surface Web)
Before initiating encryption, the ransomware performs extensive defensive evasion and impact-maximization actions. It deletes shadow copies to prevent file restoration, clears event logs, disables security monitoring through in-memory patching, and terminates backup services and productivity applications to unlock open files. It also enumerates network shares for lateral encryption, supports multi-threaded execution for speed optimization, and selects encryption routines based on processor capabilities, ultimately using ChaCha20 for file encryption with Curve25519 for key exchange. To reduce forensic artifacts, it relaunches itself in hidden mode and leverages NTFS alternate data streams for self-deletion, leaving behind only encrypted files and ransom notes.
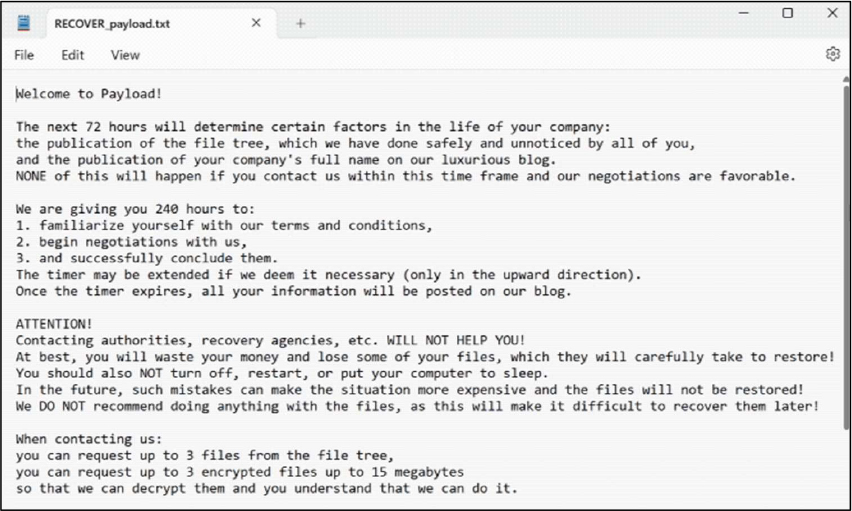
The appearance of the Payload Ransomware ransom note (RECOVER_payload.txt) (Source: Surface Web)
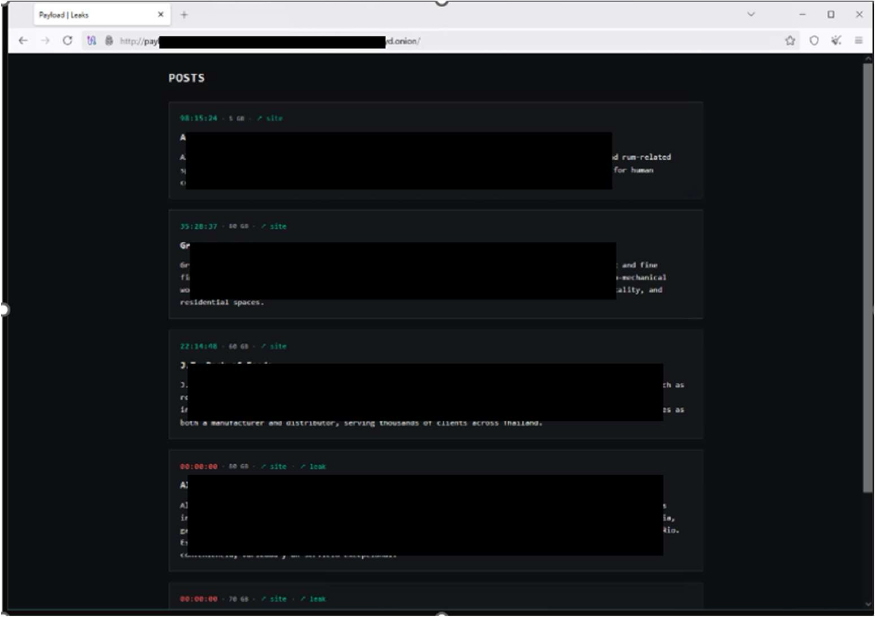
The appearance of the Payload Ransomware’s victim blog (Source: Surface Web)
The following are the TTPs based on the MITRE Attack Framework
| Tactic | Technique ID | Technique Name |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1106 | Native API |
| Execution | T1129 | Shared Modules |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation |
T1055 | Process Injection |
| Privilege Escalation |
T1543.003 | Create or Modify System Process: Windows Service |
| Defense Evasion | T1027.002 | Obfuscated Files or Information: Software Packing |
| Defense Evasion | T1027.005 | Obfuscated Files or Information: Indicator Removal from Tools |
| Defense Evasion | T1027.009 | Obfuscated Files or Information: Embedded Payloads |
| Defense Evasion | T1055 | Process Injection |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1202 | Indirect Command Execution |
| Defense Evasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| Defense Evasion | T1562.006 | Impair Defenses: Indicator Blocking |
| Defense Evasion | T1564.003 | Hide Artifacts: Hidden Window |
| Defense Evasion | T1564.004 | Hide Artifacts: NTFS File Attributes |
| Credential Access | T1056 | Input Capture |
| Discovery | T1057 | Process Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1518 | Software Discovery |
| Discovery | T1614 | System Location Discovery |
| Collection | T1056 | Input Capture |
| Collection | T1074 | Data Staged |
| Command and Control |
T1071 | Application Layer Protocol |
| Command and Control |
T1090 | Proxy |
| Impact | T1486 | Data Encrypted for Impact |
| Impact | T1489 | Service Stop |
| Impact | T1490 | Inhibit System Recovery |
Relevancy and Insights:
ETLM Assessment:
CYFIRMA’s assessment indicates that this ransomware currently functions as a structured and operationally disciplined double-extortion threat. In its present form, it encrypts victim files and appends a distinct extension while simultaneously deploying a ransom note that directs victims to a negotiation portal hosted over an anonymity network. Beyond encryption, it undertakes multiple pre-encryption impact-maximization steps, including deleting volume shadow copies to inhibit recovery, clearing Windows event logs to reduce forensic visibility, terminating backup and security-related services, and stopping user applications to ensure file accessibility for encryption. It also demonstrates network awareness by enumerating accessible drives to broaden its reach. The malware employs a hybrid cryptographic model, using symmetric encryption for data locking and asymmetric key exchange for secure key management, and incorporates a self-deletion routine to remove its executable after execution, thereby minimizing artifacts on disk.
Looking forward, CYFIRMA assesses that this ransomware has the potential to mature into a more sophisticated, enterprise-grade intrusion toolset. Future iterations may integrate automated lateral movement capabilities, credential harvesting, and pre-encryption data exfiltration workflows to strengthen extortion leverage. The operators could adopt intermittent or partial encryption strategies to evade behavioral detection systems while accelerating execution speed in large environments. Enhanced anti-analysis features such as sandbox detection, virtualization checks, and deeper in-memory obfuscation may also be introduced to counter evolving endpoint defenses. Additionally, the threat actors may expand their targeting scope to include cloud infrastructure, virtualized workloads, and backup repositories, increasing operational impact and negotiation pressure. Such developments would signal a transition from opportunistic ransomware activity toward more coordinated and strategically executed cyber extortion campaigns.
Sigma rule:
title: Shadow Copies Deletion Using Operating Systems Utilities description: Shadow Copies deletion using operating systems utilities tags:
– attack.defense-evasion
– attack.impact
– attack.t1070
– attack.t1490 logsource:
category: process_creation product: windows
detection: selection1_img:
– Image|endswith:
– ‘\powershell.exe’
– ‘\pwsh.exe’
– ‘\wmic.exe’
– ‘\vssadmin.exe’
– ‘\diskshadow.exe’
– OriginalFileName:
– ‘PowerShell.EXE’
– ‘pwsh.dll’
– ‘wmic.exe’
– ‘VSSADMIN.EXE’
– ‘diskshadow.exe’ selection1_cli:
CommandLine|contains|all:
– ‘shadow’ # will match “delete shadows” and “shadowcopy delete” and “shadowstorage”
– ‘delete’ selection2_img:
– Image|endswith: ‘\wbadmin.exe’
– OriginalFileName: ‘WBADMIN.EXE’ selection2_cli:
CommandLine|contains|all:
– ‘delete’
– ‘catalog’
– ‘quiet’ # will match -quiet or /quiet selection3_img:
– Image|endswith: ‘\vssadmin.exe’
– OriginalFileName: ‘VSSADMIN.EXE’ selection3_cli:
CommandLine|contains|all:
– ‘resize’
– ‘shadowstorage’ CommandLine|contains:
– ‘unbounded’
– ‘/MaxSize=’
condition: (all of selection1*) or (all of selection2*) or (all of selection3*) falsepositives:
– Legitimate Administrator deletes Shadow Copies using operating systems utilities for legitimate reason
– LANDesk LDClient Ivanti-PSModule (PS EncodedCommand) level: high
(Source: Surface Web)
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
Type: Information stealer (RAT)| Objectives: Data Exfiltration | Target Technology:
Android | Target Industry: Finance| Target Geography: Russia
CYFIRMA collects data from various forums based on which the trend is ascertained. We identified a few popular malware that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week, “TaxiSpy RAT” is in focus.
Overview of Operation TaxiSpy RAT Malware
TaxiSpy RAT is a highly advanced Android banking malware specifically engineered to target Russian financial users. The threat combines traditional banking trojan capabilities with full Remote Access Trojan (RAT) functionality, enabling attackers to conduct comprehensive surveillance and financial fraud operations. Its primary objective is to intercept banking credentials, capture one-time passwords (OTPs), monitor financial applications, and remotely control infected devices. The malware demonstrates a clear regional focus, particularly targeting Russian banking institutions such as Alfa-Bank, while leveraging stealth techniques to remain undetected on compromised devices.
TaxiSpy RAT employs layered persistence, aggressive permission abuse, and runtime obfuscation to evade analysis and detection. By integrating native code routines, encrypted configuration storage, Firebase-based push communication, and WebSocket-driven remote control, the malware enables real-time screen monitoring, SMS interception, keylogging, and lock-screen PIN capture. Its ability to disguise itself, suppress notifications, and maintain continuous background execution makes it a significant financial threat to affected users and institutions. Overall, TaxiSpy represents a financially motivated, infrastructure-backed Android threat designed for sustained access, credential theft, and remote exploitation within a targeted geographic ecosystem.
Attack Method
TaxiSpy RAT operates through a structured infection and control process designed to achieve complete device compromise and financial exploitation. Once installed, the application immediately attempts to set itself as the default SMS handler. If the user grants this request, the malware gains extensive control over SMS functionality, including reading incoming messages, sending SMS, and intercepting one-time passwords (OTPs). It further abuses Accessibility Service permissions to observe on-screen activity, capture user inputs, automate actions, and hinder removal attempts. To maintain long-term presence on the device, the malware registers boot receivers, schedules alarms and background jobs, initiates persistent foreground services, and requests exemptions from battery optimization mechanisms.
A notable aspect of the malware’s design is its reliance on a native library (libsysruntime.so) to store and execute sensitive logic. Instead of embedding critical configuration details directly in the main application code, the operators conceal command and control (C2) addresses, Firebase credentials, bot identifiers, and campaign-specific worker keys within the native binary. These values are encrypted using customized XOR routines with rolling keys and non-linear memory access patterns. The encrypted data is only decrypted at runtime, which significantly complicates static analysis and helps the malware evade detection by security tools. Once operational, the application communicates with its hardcoded C2 server using HTTP POST requests and WebSocket connections.
After establishing communication, TaxiSpy performs detailed device reconnaissance. It collects system information, such as device model, operating system version, SIM data, and a complete list of installed applications. The malware specifically checks for banking, government, marketplace, and cryptocurrency applications, using decrypted package lists to identify high-value targets. When a banking application or the device lock screen is active, it captures keystrokes, intercepts PIN entries, and extracts OTPs from SMS and notifications using pattern-matching techniques. The harvested information, including messages, contacts, call logs, clipboard data, and application Metadata is systematically transmitted to dedicated C2 endpoints.
In addition to passive data theft, TaxiSpy enables active remote control. By leveraging Accessibility and MediaProjection APIs, the malware establishes VNC-like functionality through WebSocket communication, allowing operators to stream the device screen and monitor user interactions in real time. Firebase Cloud Messaging is also integrated as an auxiliary command channel, enabling push-based instructions and background activation. This combination of encrypted configuration storage, persistent execution mechanisms, structured data exfiltration, and real-time remote access forms a comprehensive attack framework aimed at credential theft
The following are the TTPs based on the MITRE Attack Framework for Enterprise
| Tactic (ID) | Technique ID | Technique Name |
| Initial Access | T1660 | Phishing |
| T1541 | Foreground Persistence | |
| Persistence | T1603 | Scheduled Task/Job |
| Privilege Escalation | T1626.001 | Abuse Elevation Control Mechanism: Device Administrator Permissions |
| T1628 | Hide Artifacts | |
| T1628:002 | Hide Artifacts: User Evasion | |
| T1629.001 | Impair Defenses: Prevent Application Removal | |
| Defense Evasion | T1516 | Input Injection |
| T1414 | Clipboard Data | |
| Credential Access | T1417.001 | Input Capture: Keylogging |
| T1420 | File and Directory Discovery | |
| T1430 | Location Tracking | |
| T1418 | Software Discovery | |
| T1426 | System Information Discovery | |
| Discovery | T1422 | System Network Configuration Discovery |
| T1636:001 | Protected User Data: Calendar Entries | |
| T1636:002 | Protected User Data: Call Log | |
| T1636:003 | Protected User Data: Contact List | |
| T1636:004 | Protected User Data: SMS Messages | |
| T1417 | Input Capture | |
| T1513 | Screen Capture | |
| Collection | T1512 | Video Capture |
| T1437 | Application Layer Protocol | |
| T1437.001 | Application Layer Protocol: Web Protocols | |
| T1521 | Encrypted Channel | |
| T1521.003 | Encrypted Channel: SSL Pinning | |
| Command and control | T1481 | Web Service |
| Exfiltration | T1646 | Exfiltration Over C2 Channel |
INSIGHTS
The malware reflects a clearly defined and selective target strategy rather than indiscriminate distribution. Its focus on specific financial and high-value applications suggests that the operators have carefully identified their intended victim base. This indicates that the campaign is structured around financial prioritization, with deliberate attention given to users who present greater monetary opportunities.
The operational structure behind the activity suggests coordination and organized management. The presence of distinct campaign identifiers implies that multiple actors may operate under a shared infrastructure while maintaining separation of activity. This arrangement reflects a controlled environment where operations are monitored and managed systematically rather than conducted randomly.
The overall behavior emphasizes sustained oversight instead of rapid or disruptive action. The activity appears designed to maintain ongoing awareness of user interactions, particularly those involving financial applications. This measured and supervisory approach highlights an intent to observe and control victim activity discreetly, reinforcing the structured nature of the operation.
ETLM ASSESSMENT
The analyzed application reflects a highly targeted, industry-specific threat primarily impacting users within the local banking ecosystem, including major financial institutions and widely used banking applications. Its design, permission model, and operational behavior indicate deliberate alignment with this demographic while minimizing exposure outside the intended region.
Distribution appears to leverage social engineering, repackaged applications, and localized delivery channels, supported by automated build processes that enable scalable deployment. The campaign is financially motivated, focusing on credential theft, interception of verification codes (e.g., OTPs), and remote device control— suggesting a structured and organized operation designed to maintain persistent access and facilitate fraudulent transactions.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems.
YARA Rules
rule TaxiSpy_RAT_Android
{
meta:
description = “Detection rule for TaxiSpy RAT Android banking malware (Russian- targeted variant)”
author = “CYFIRMA” date = “2026-03-03”
strings:
/* Malware Sample Hash */
$hash_1 =
“67d5d8283346f850eb560f10424ea5a9ccdca5e6769fbbbf659a3e308987cafd”
/* C2 Indicator */
$c2_ip = “193.233.112.229”
/* Worker Key */
$worker_key = “9bc096a5f4ec7ba133d743cbaf4b8a2e”
/* XOR Key Arrays (Native Obfuscation Indicators) */
$xor_key_1 = { 3A 7F B2 1D E9 54 C8 6B }
$xor_key_2 = { B2 1F CC E3 6A 7E 71 F4 0A C0 1D 78 7B 4B 1B 15 2A 2F 24 20 33 1C }
condition:
any of ($hash_*) or any of ($c2_ip, $worker_key, $xor_key_*)
}
Strategic Recommendations
Management Recommendations
Tactical Recommendations
Key Intelligence Signals:
FishMonger (aka Earth Lusca): Espionage-Driven Cyber Activity Briefing
About the Threat Actor
FishMonger (aka Earth Lusca) is a China-linked threat actor active since 2019 that focuses primarily on cyber-espionage against government, media, telecommunications, academic, and religious organizations, while also conducting financially motivated campaigns targeting cryptocurrency platforms. The group leverages tooling and tradecraft like APT41 and the Winnti Group cluster, but is assessed to operate independently from the Winnti Umbrella.
Details on Exploited Vulnerabilities
| CVE ID | Affected Products | CVSS Score | Exploit Links |
| CVE-2024-21412 | Internet Shortcut Files Security | 8.1 | – |
| CVE-2016-5195 | Linux kernel | 7.0 | Link1, link2, link3, link4, link5, link6 |
| CVE-2023-32315 | Openfire | 7.5 | Link |
| CVE-2024-23897 | Jenkins | 9.8 | Link1, link2 |
| CVE-2022-21587 | Oracle Web Applications | 9.8 | link |
| CVE-2021-22555 | Linux | 7.8 | Link1, link2, link3, link4, link5 |
TTPs based on MITRE ATT&CK Framework
| Tactic | ID | Technique |
| Reconnaissance | T1595.002 | Active Scanning: Vulnerability Scanning |
| Resource Development | T1608.001 | Stage Capabilities: Upload Malware |
| Resource Development | T1583.001 | Acquire Infrastructure: Domains |
| Resource Development | T1583.004 | Acquire Infrastructure: Server |
| Resource Development | T1583.006 | Acquire Infrastructure: Web Services |
| Resource Development | T1584.004 | Compromise Infrastructure: Server |
| Resource Development | T1584.006 | Compromise Infrastructure: Web Services |
| Resource Development | T1588.002 | Obtain Capabilities: Tool |
| Resource Development | T1588.001 | Obtain Capabilities: Malware |
| Initial Access | T1189 | Drive-by Compromise |
| Initial Access | T1566.002 | Phishing: Spear phishing Link |
| Initial Access | T1190 | Exploit Public-Facing Application |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
| Execution | T1059.007 | Command and Scripting Interpreter: JavaScript |
| Execution | T1047 | Windows Management Instrumentation |
| Execution | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Execution | T1204.002 | User Execution: Malicious File |
| Execution | T1204.001 | User Execution: Malicious Link |
| Execution | T1059.005 | Command and Scripting Interpreter: Visual Basic |
| Execution | T1059.006 | Command and Scripting Interpreter: Python |
| Persistence | T1547.012 | Boot or Logon Autostart Execution: Print Processors |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Persistence | T1574.001 | Hijack Execution Flow: DLL |
| Persistence | T1112 | Modify Registry |
| Persistence | T1098.004 | Account Manipulation: SSH Authorized Keys |
| Persistence | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Privilege Escalation | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Privilege Escalation | T1098.004 | Account Manipulation: SSH Authorized Keys |
| Privilege Escalation | T1548.002 | Abuse Elevation Control Mechanism: Bypass User Account Control |
| Privilege Escalation | T1547.012 | Boot or Logon Autostart Execution: Print Processors |
| Privilege Escalation | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1574.001 | Hijack Execution Flow: DLL |
| Defense Evasion | T1140 | Deobfuscate/Decode Files or Information |
| Defense Evasion | T1548.002 | Abuse Elevation Control Mechanism: Bypass User Account Control |
| Defense Evasion | T1574.001 | Hijack Execution Flow: DLL |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1036.005 | Masquerading: Match Legitimate Resource Name or Location |
| Defense Evasion | T1027.003 | Obfuscated Files or Information: Steganography |
| Defense Evasion | T1218.005 | System Binary Proxy Execution: Mshta |
| Defense Evasion | T1112 | Modify Registry |
| Credential Access | T1003.001 | OS Credential Dumping: LSASS Memory |
| Credential Access | T1003.006 | OS Credential Dumping: DCSync |
| Discovery | T1482 | Domain Trust Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1049 | System Network Connections Discovery |
| Discovery | T1007 | System Service Discovery |
| Discovery | T1018 | Remote System Discovery |
| Discovery | T1016 | System Network Configuration Discovery |
| Discovery | T1033 | System Owner/User Discovery |
| Lateral Movement | T1210 | Exploitation of Remote Services |
| Collection | T1056.001 | Input Capture: Keylogging |
| Command and Control | T1090 | Proxy |
| Exfiltration | T1567.002 | Exfiltration Over Web Service: Exfiltration to Cloud Storage |
Latest Developments Observed
The threat actor is suspected of expanding beyond traditional cyber-espionage to conduct financially motivated campaigns targeting cryptocurrency payment platforms and cryptocurrency exchanges. These campaigns appear aimed at generating revenue while maintaining ongoing intelligence collection operations against government and civil society-linked organizations.
ETLM Insights
FishMonger (aka Earth Lusca) is assessed as a China-aligned cyber-espionage actor whose primary objective is sustained intelligence collection rather than short-term disruption or purely financial gain.
Operationally, FishMonger prioritizes stealth, persistence, and infrastructure hygiene across enterprise and research networks. The group demonstrates a preference for exploiting newly disclosed vulnerabilities in internet-facing services to establish initial access, followed by long-dwell intrusions supported by custom loaders, backdoors, and web shells. Its use of domain masquerading, frequent command-and-control rotation, and low-volume staged exfiltration indicates an emphasis on remaining covert to preserve intelligence collection opportunities over extended periods rather than achieving immediate disruptive effects.
Based on observed tradecraft and targeting patterns, FishMonger is likely to continue focusing on its targets to sustain long-term access for strategic intelligence purposes. This positions the group as a persistent espionage threat to organizations involved in governance, emerging technology development, and policy formation, with continued risk to the confidentiality of sensitive research, communications, and strategic planning information.
YARA Rules
rule EarthLusca_FishMonger_IOC_Detection
{
meta:
description = “Detects FishMonger (aka Earth Lusca) malware and infrastructure based on known IOCs”
author = “CYFIRMA”
threat_actor = “FishMonger / Earth Lusca” last_updated = “2026-03-03”
confidence = “IOC-based detection”
strings:
/* IP Addresses */
$ip1 = “104.21.71.224”
$ip2 = “101.200.63.187”
$ip3 = “61.238.103.165”
$ip4 = “162.33.178.23”
$ip5 = “78.141.202.70”
/* Domains */
$d1 = “api.googleauthenticatoronline.com”
$d2 = “tfirsdaily.store”
$d3 = “softupdate.xyz”
$d4 = “gtlgtdl.store”
$d5 = “support.helpkaspersky.top”
/* File names / hashes / paths */
$f1 = “elf205abe6c8c2be8ebb8e03eaf7b025f4”
$f2 = “24de00559463ef4103032e24c58ce35d.virus”
$f3 = “2317d3e14ab214f06ae38a729524646971e21b398eda15cc9deb8b00b231abc3.exe”
$f4 = “mustangpanda_20230922”
$f5 = “c:\\users\\user\\appdata\\local\\temp\\a1qngbu4.l2b\\mustangpanda_20230922”
/* ELF marker */
$elf_magic = { 7F 45 4C 46 }
condition:
1 of ($ip*) or 1 of ($d*) or 1 of ($f*) or
$elf_magic
}
Strategic Recommendations
Management Recommendations
Tactical Recommendations
The opening cyber salvo in the Iran War
As fighter jets and cruise missiles targeted IRGC command centers on February 28, 2026, a simultaneous digital offensive reportedly plunged Iran into near-total communications paralysis. This cyber dimension unfolded alongside Israel’s Operation Roaring Lion and the U.S.’s Operation Epic Fury, creating a “parallel front” that severely disrupted the regime’s internal coordination and public messaging.
Iran experienced a dramatic nationwide internet blackout, with independent monitor NetBlocks reporting connectivity dropping to just 4% of normal levels starting around 07:00 UTC that day—later flatlining near 1% in subsequent updates. The disruption, which has persisted for over 48 hours in many areas, severely limited information flow, government operations, and potential civilian coordination amid the strikes. While some analysts attribute this partly to regime-imposed shutdowns (a tactic Iran has used before to control unrest or prevent leaks during crises, as seen in the 2025 Israel- Iran clashes), others point to large-scale cyberattacks contributing to or exploiting the collapse, targeting telecom infrastructure, critical services, and command networks. The offensive also struck the regime’s propaganda apparatus: State-run news agency IRNA (Islamic Republic News Agency) went offline for extended periods, crippling official narratives.
Tasnim (media house closely tied to the Iranian Revolutionary Guards) faced major disruptions, with reports of hacks that replaced content with subversive anti-regime messages directed at Supreme Leader Ali Khamenei (who was later confirmed killed in the early strikes).
These cyber intrusions aligned with broader psychological operations, including the compromise of popular apps like BadeSaba (a prayer/calendar tool with millions of users), which pushed notifications urging security forces to defect, disarm, and join civilians—messages like “It’s time for reckoning” and “Help has arrived!” aimed at sowing internal discord. Attribution remains challenging in the fog of war, but it is safe to assume the most disruptive elements in the cyber campaign can be attributed to governmental agencies from the USA and Israel.
ETLM Assessment:
The limited nature of the previous round of American strikes on the Iranian nuclear programme in June meant that the US has not deployed every capability it had at hand – and is now likely using a wider spectrum of cyber tools, usage of which will likely surface in the coming days. Meanwhile, Iran’s degraded central command structure may lead to more decentralized, unpredictable actions led by proxies and loosely affiliated hacktivists operating via platforms like Telegram. This could accelerate low-to-medium sophistication attacks in the short term, filling the gap left by disrupted regime coordination and aiming to impose costs, signal defiance, and complicate any de-escalation efforts. Organizations in defense, critical infrastructure, finance, energy, and government sectors—particularly those with ties to the U.S. or Israel—are urged to heighten vigilance, patch vulnerabilities, and monitor for indicators of compromise from known Iranian-linked actors.
Chinese espionage campaign found using Google Sheets
Google has announced a major disruption of a long-running, sophisticated cyber espionage campaign attributed to a suspected Chinese state-linked threat actor tracked as UNC2814 (also known as Gallium), which has been active since at least 2017. The operation targeted at least 53 organizations across 42 countries, with suspected activity extending to at least 20 more nations. The victims primarily included government entities and global telecommunications providers spanning Africa, Asia, the Americas, Europe, and beyond—highlighting a nearly decade-long effort to establish persistent access for intelligence collection and surveillance. Some of the data stolen includes sensitive personal information such as full names, phone numbers, dates of birth, voter IDs, and national IDs in at least one documented case.
ETLM Assessment:
UNC2814 operates distinctly from other high-profile Chinese-linked actors like Salt Typhoon, with no observed overlap in victims, tactics, or infrastructure. The group is described as both prolific and elusive, often gaining initial footholds by compromising web servers and edge systems. While the disruption significantly hampers UNC2814’s current operations, researchers caution that the actor is likely to aggressively attempt to rebuild its global footprint.
INC Ransomware Impacts JA Akita Kita Life Service, K.K
Summary:
CYFIRMA observed in an underground forum that a company from Japan, JA Akita Kita Life Service, K.K (https[:]//ja-akitakita-ls[.]jp/), was compromised by INC Ransomware. JA Akita Kita Life Service, K.K. is a Japanese firm providing energy and lifestyle services. The compromised dataset includes internal records, financial information, client lists, and other confidential and sensitive data belonging to the organisation. The Total size of compromised data is approximately 43.1GB
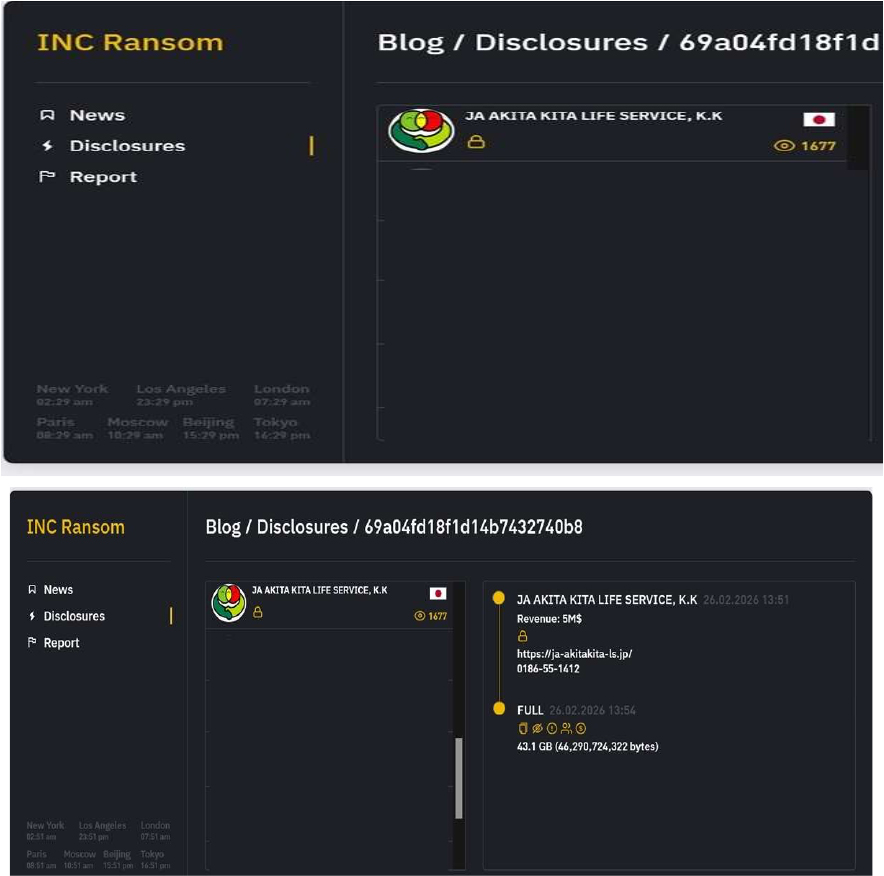
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
Based on recent assessments by CYFIRMA, INC Ransomware represents a significant threat within the evolving landscape of ransomware attacks. Its use of strong encryption methods and double extortion tactics highlights the increasing sophistication of cybercriminal operations. Organizations are advised to enhance their cybersecurity measures by implementing robust defenses against phishing attacks, maintaining updated security protocols, and monitoring for unusual network activity to mitigate risks associated with this and other ransomware variants. Continuous vigilance is essential to protect against the threats posed by emerging ransomware groups like INC Ransomware.
The Gentlemen Ransomware Impacts Sando Tech
Summary:
CYFIRMA observed in an underground forum that a company from Japan, Sando Tech(https[:]//www[.]sando[.]co[.]jp/), was compromised by the Gentlemen Ransomware. Sando Tech specialises in the development, design, manufacturing, and sales of machinery. The company offers a range of products, including testing machines, repair services, and consumable parts orders. The data, which has been breached, has not yet appeared on the leak site, indicating that negotiations between the affected party and the ransomware group may be underway. The compromised data includes confidential and sensitive information belonging to the organization.
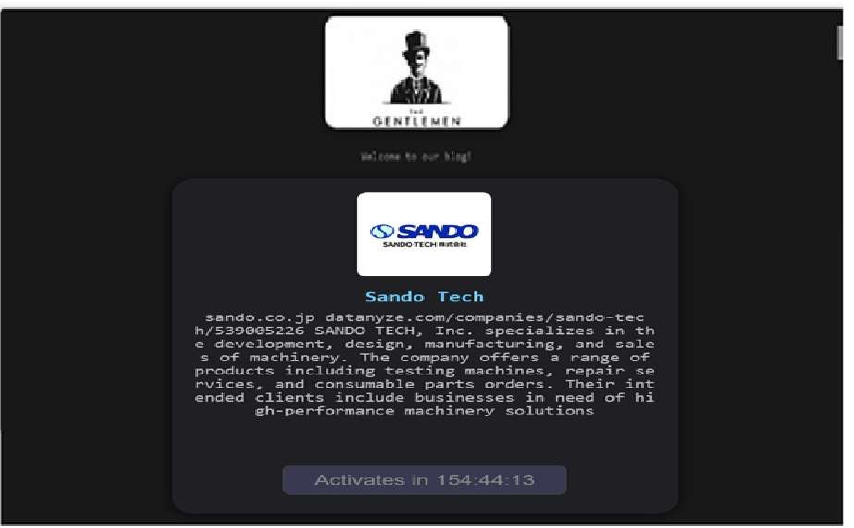
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, the Gentlemen Ransomware is a highly adaptive and globally active threat that leverages dual-extortion tactics, combining data theft with file encryption. The group employs advanced evasion and persistence techniques, supports cross-platform and scalable ransomware deployment, and conducts targeted attacks across multiple industries and geographic regions. This combination of capabilities makes it a significant risk to enterprise cybersecurity defenses, particularly for organizations with limited detection and incident-response maturity.
Vulnerability in Docker Desktop
Summary:
The vulnerability allows a remote user to bypass implemented security restrictions.
Relevancy & Insights:
The vulnerability exists due to insufficient input validation.
Impact:
A remote user can perform runtime flag injection and escalate privileges on the system.
Affected Products:
https[:/]/docs[.]docker[.]com/security/security-announcements/#docker- desktop-4620-security-update-cve-2026-28400
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
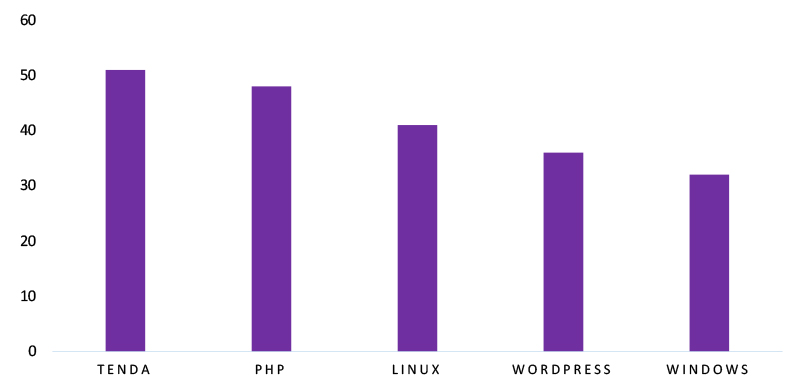
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies due to a range of vulnerabilities. The following are the top 5 most affected technologies.
ETLM Assessment
Vulnerability in Docker Desktop introduces significant security risks to development environments, containerized workflows, and integrated DevOps pipelines. As Docker Desktop is widely used across enterprises, cloud-native teams, and software engineering environments, exploitation of this command injection flaw can impact numerous industries globally. Ensuring the security of Docker Desktop is crucial for maintaining the integrity of local development ecosystems, protecting container orchestration processes, and preventing unauthorized command execution on host systems. Therefore, addressing this vulnerability is essential to safeguarding development workstations, securing container environments, and ensuring operational reliability across diverse sectors and geographic regions.
Space Bears Ransomware attacked and published the data of Kymco (Kwang Yang Motor Co., Ltd.)
Summary:
Recently, we observed that Space Bears Ransomware attacked and published the data of Kymco (Kwang Yang Motor Co., Ltd.) (https[:]//www[.]kymco[.]com[.]tw) on its dark web website. Kymco (Kwang Yang Motor Co., Ltd.) – Taiwanese company founded in 1963, specializing in the production of motorcycles, scooters, and electric vehicles. It is known for offering a wide range of high-quality products, from small scooters to sport motorcycles and e-bikes. The company actively integrates innovative technologies, including electric drivetrains and advanced control systems, positioning itself as a leader in the market. Kymco also has a strong global presence, exporting its products to over 100 countries. Additionally, the company is committed to developing eco-friendly transportation solutions, such as electric scooters and e-bikes. The ransomware incident resulted in the exposure of sensitive data, including Patent and Innovation Data, Financial Data, Customer and Partner Data, 3D models of developments, Schematics and test results, and much more.
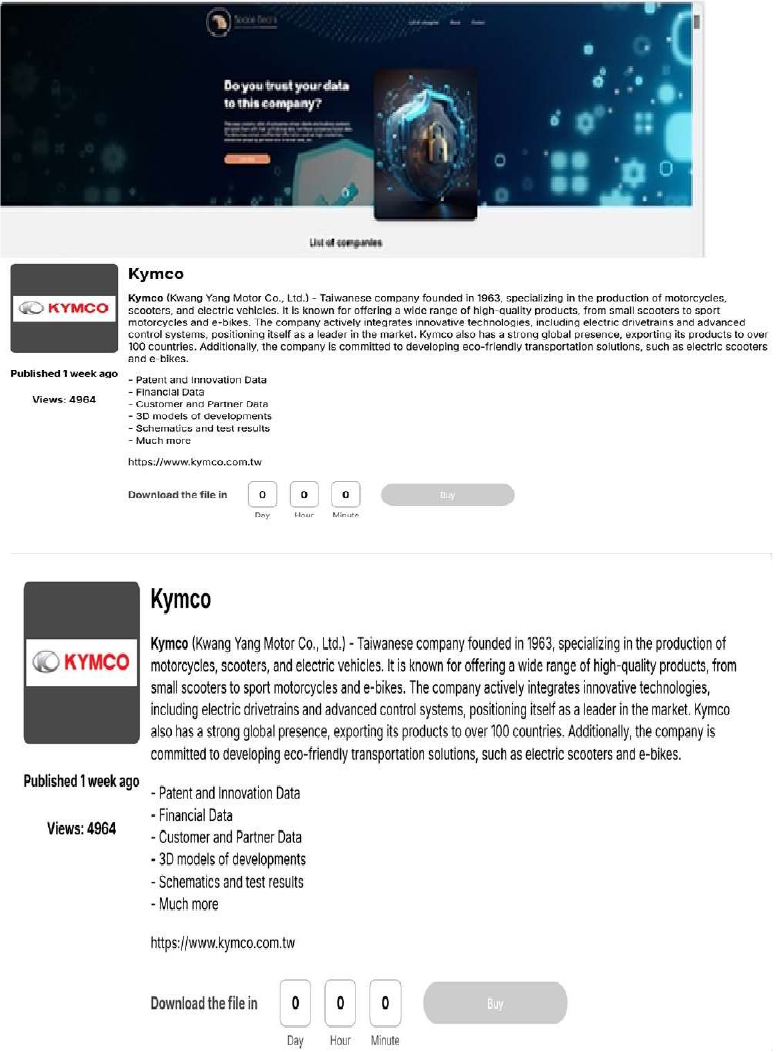
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, Space Bears ransomware represents a significant threat in the evolving landscape of cybercrime. With its aggressive tactics, association with established ransomware operations like Phobos, and focus on double extortion, organizations are advised to bolster their cybersecurity measures to mitigate risks associated with such attacks. Continuous monitoring of this group’s activities will be essential for understanding their methods and potential impact on various sectors.
Bahrain’s National Security Agency Data Advertised on a Leak Site
Summary: The CYFIRMA research team has identified a post published on a well- known hacking forum by a threat actor operating under the alias “TheAshborn”, claiming responsibility for a data breach involving the National Security Agency of Bahrain (NSA[.]gov[.]bh), based in Bahrain.
According to the forum post, the actor alleges that they gained access to the agency’s email server and exfiltrated approximately 200 GB of data, reportedly including email communications and internal correspondence from around 50 user accounts. The actor claims to possess the full dataset within their database and has offered it for sale on the forum.
The post includes references to external file-sharing links (presumably as proof samples) and indicates a sale price of USD 2,500 in cryptocurrency. The threat actor specifies “No Telegram – No TOX – Just Session,” providing a session-based contact string for negotiation. The post also advises potential buyers to use an escrow service for a secure transaction.
Based on the description provided in the forum listing, the allegedly compromised data may include:
At this stage, the authenticity of the breach claim remains unverified, as the information originates solely from the threat actor’s forum post. There has been no publicly confirmed statement from the affected organization validating the incident at the time of reporting.
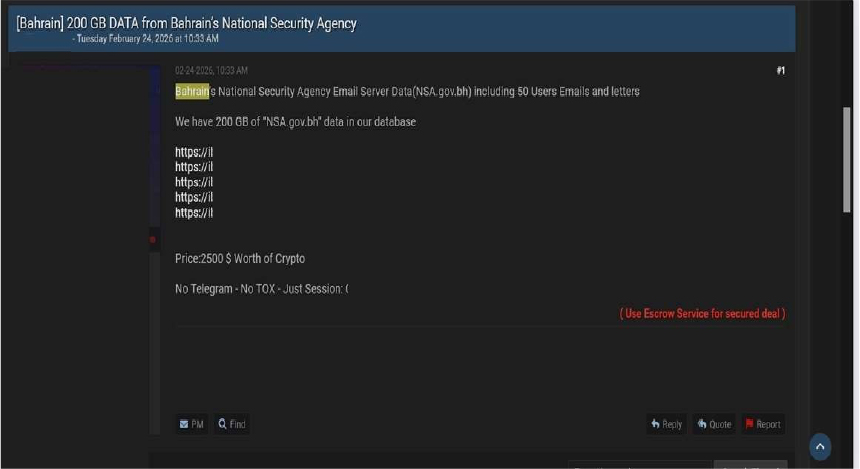
Source: Underground Forums
Malaysia Government Data Advertised on a Leak Site
Summary: The CYFIRMA research team has identified a post published on a well- known hacking forum by a threat actor operating under the alias “TheAshborn”, advertising the sale of multiple alleged Malaysian government databases under the title “[Malaysia] GOV DBs for sale 2025.”
According to the forum post, the actor claims to possess databases allegedly exfiltrated from several Malaysian government entities, including:
The threat actor claims that the alleged data includes extensive personnel information, particularly referencing employee-related records, such as:
The post states that proof of the data will only be shared with customers who are ready to pay, indicating a controlled disclosure model commonly used in underground marketplaces. The actor specifies communication restrictions (“No Telegram – No TOX – Just Session”) and provides a session-based contact string for negotiation. Additionally, the post suggests using an escrow service for secure transactions.
At this stage, the authenticity of the breach claims remains unverified, as the information is based solely on the threat actor’s forum advertisement. No official confirmation from the referenced Malaysian government entities has been identified at the time of this reporting.
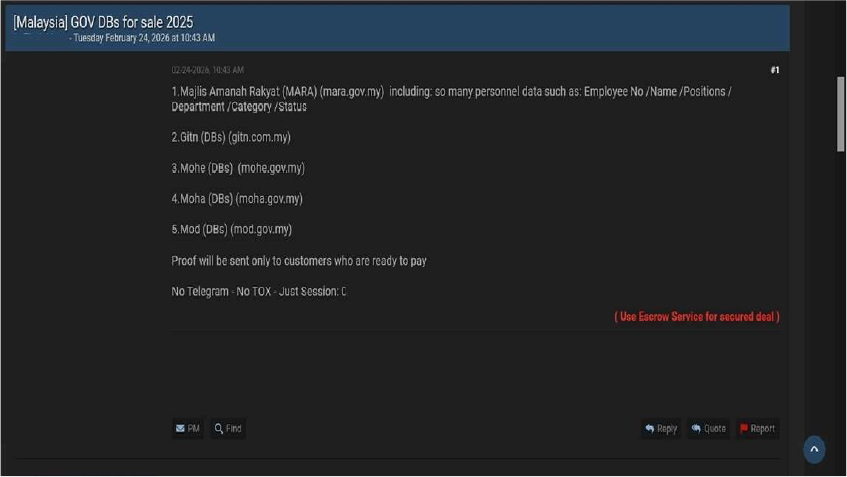
Source: Underground Forums
Relevancy & Insights:
Financially motivated cybercriminals are continuously looking for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to gain access and steal valuable data. Subsequently, the stolen data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor known by the alias “TheAshborn” is assessed to be a recently emerged but highly active and capable entity, primarily engaged in data-leak operations. The group’s activity highlights the persistent and fast-evolving cyber threat landscape, driven by underground criminal ecosystems. This development underscores the urgent need for organizations to reinforce their cybersecurity posture through continuous monitoring, improved threat intelligence capabilities, and proactive defensive strategies to protect sensitive information and critical infrastructure.
Recommendations: Enhance the cybersecurity posture by:
The CYFIRMA research team has identified a post published in an underground cybercrime forum’s auction section by a threat actor using the alias “Ragnarok.” The listing is titled “East Asia ~60B” and was posted approximately two hours prior to capture.
According to the threat actor, the offering allegedly involves access to an international company with operational presence across multiple East Asian regions, specifically referencing Taiwan (TW), Hong Kong (HK), Japan (JP), Korea (KR), and Singapore (SG). The actor claims the company is widely recognized, though no explicit organization name is disclosed in the listing.
The post advertises the following alleged access details:
Pricing Structure
Additionally, the post states that a guarantor (escrow) service would be at the buyer’s expense.
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
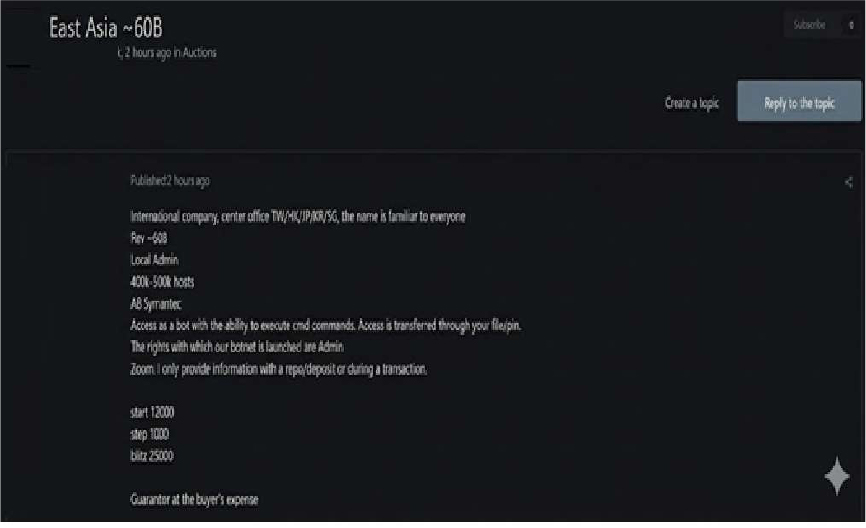
Source: Underground Forums
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
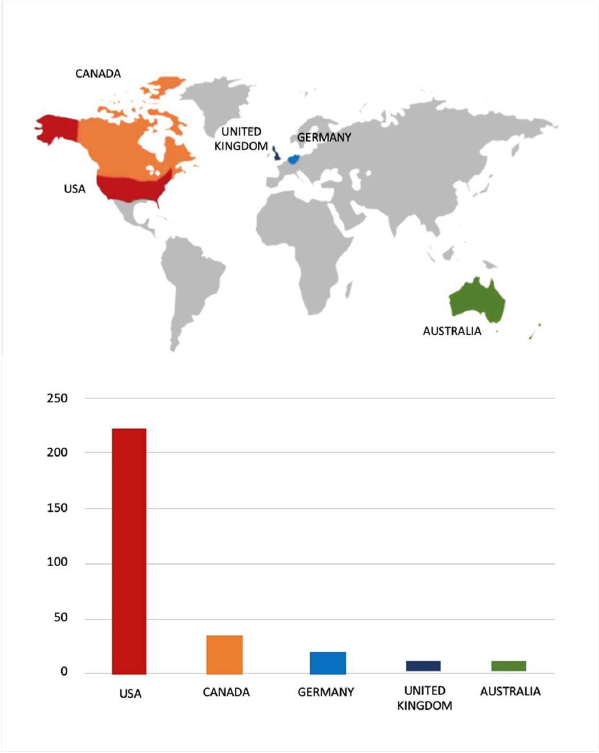
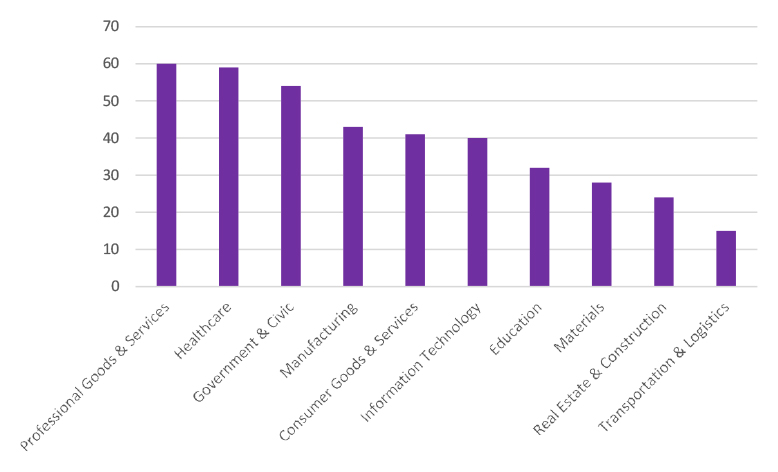
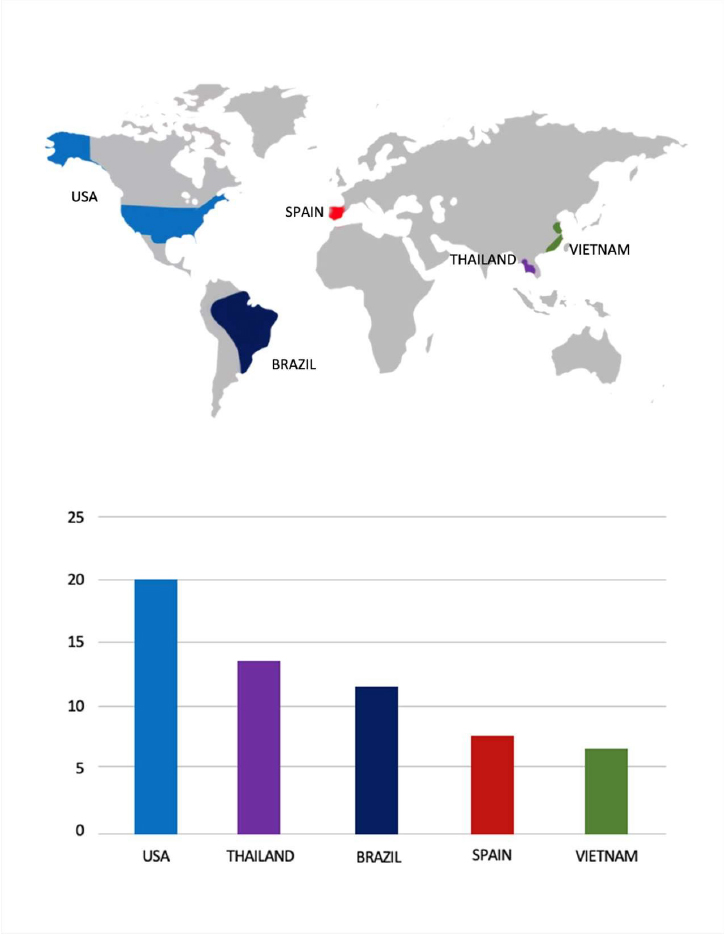
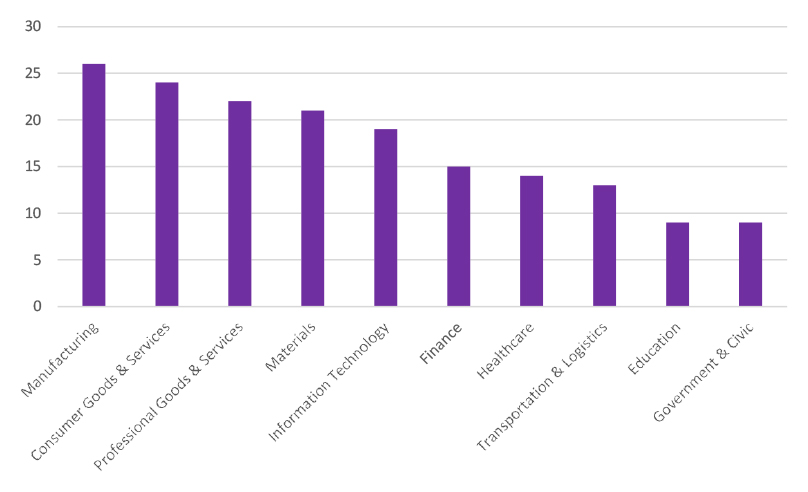
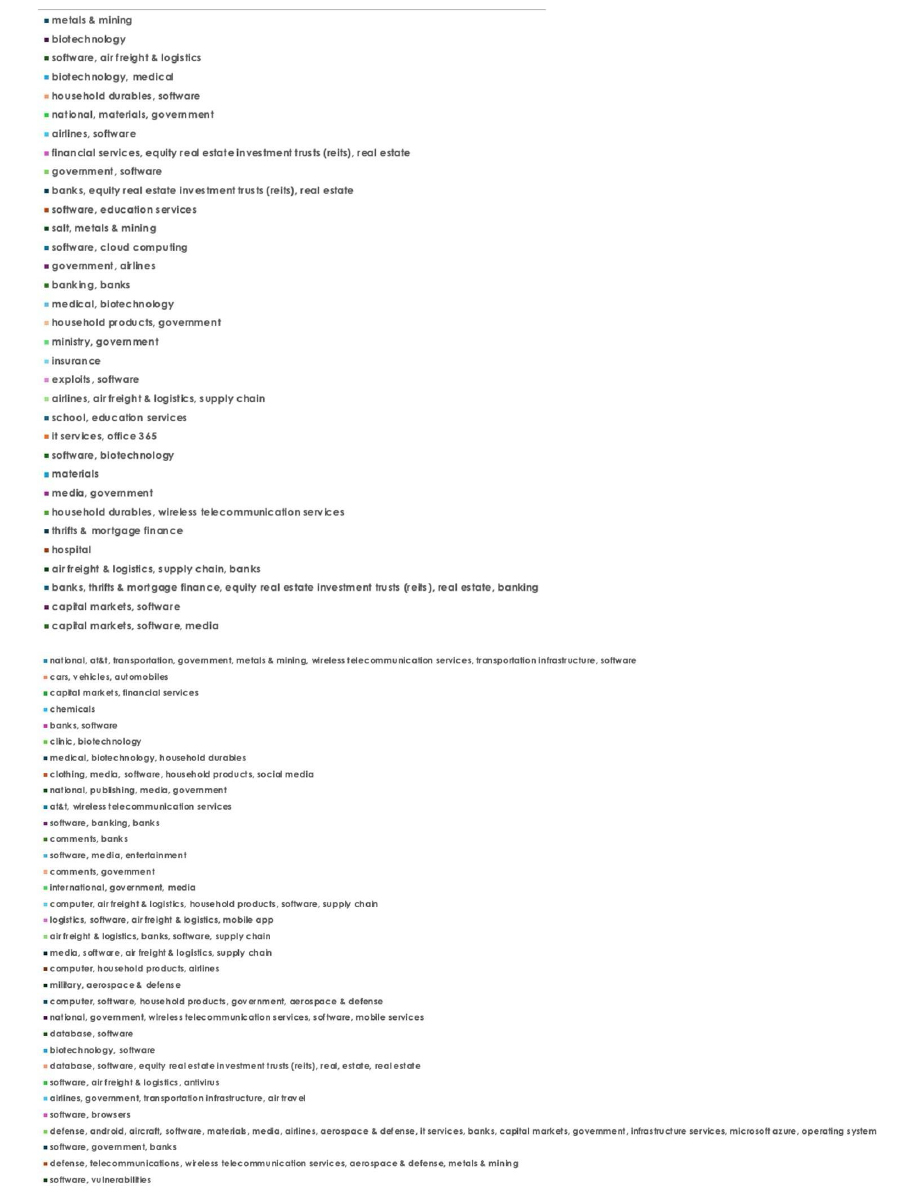
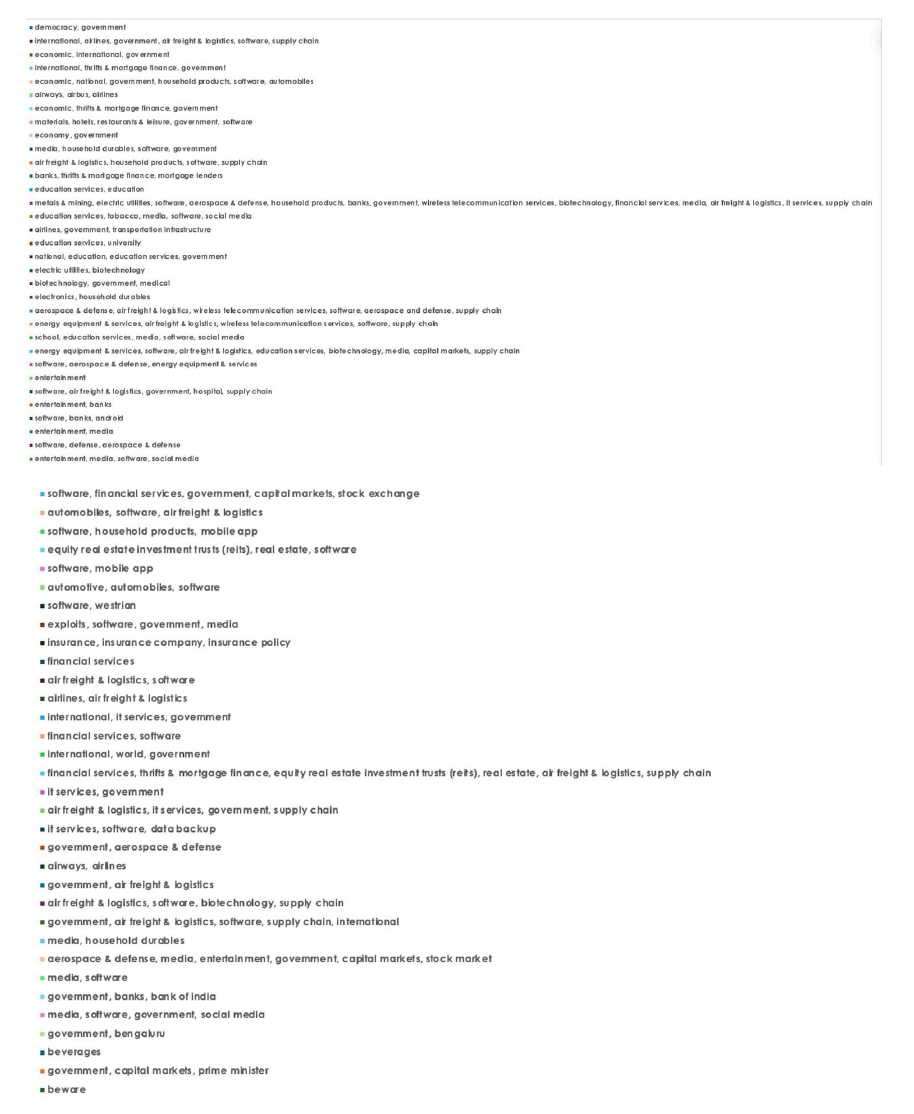
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
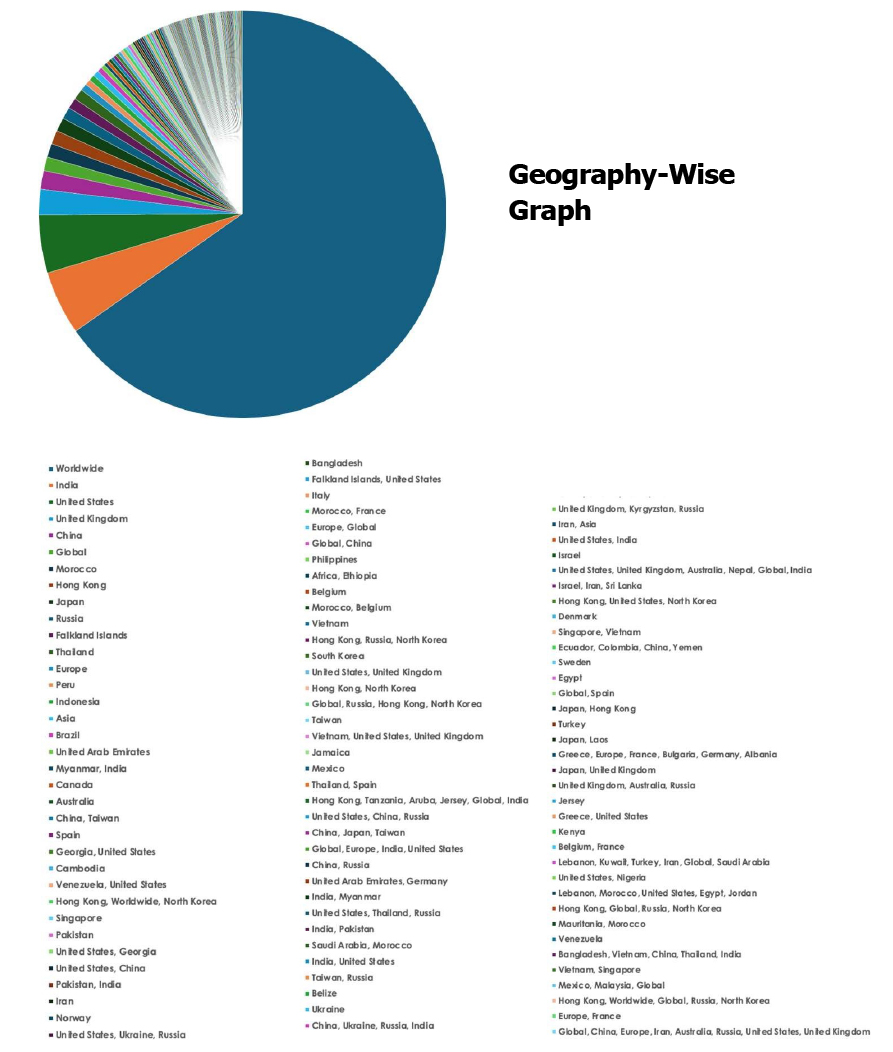
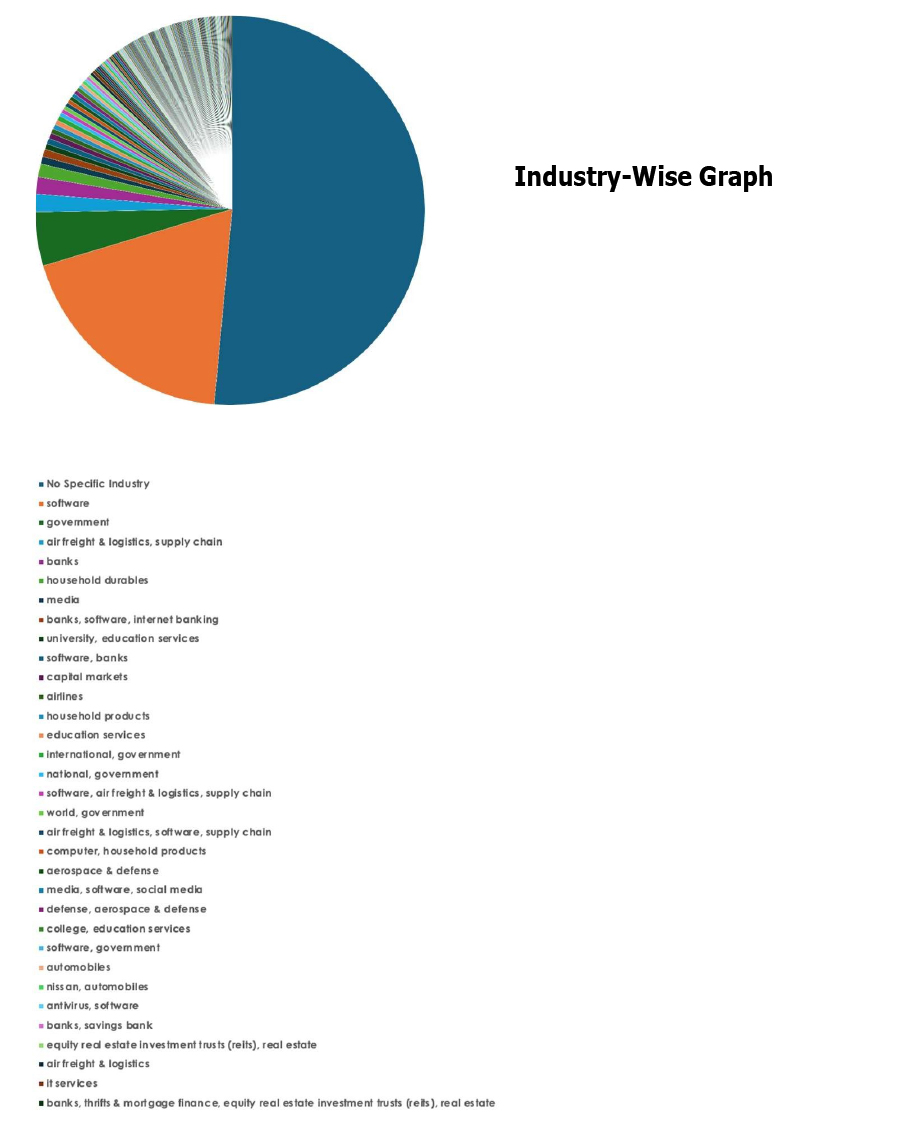
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.