


CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple – industries, geography, and technology – that could be relevant to your organization.
Type: Ransomware
Target Technologies: Windows & Linux/ESXi
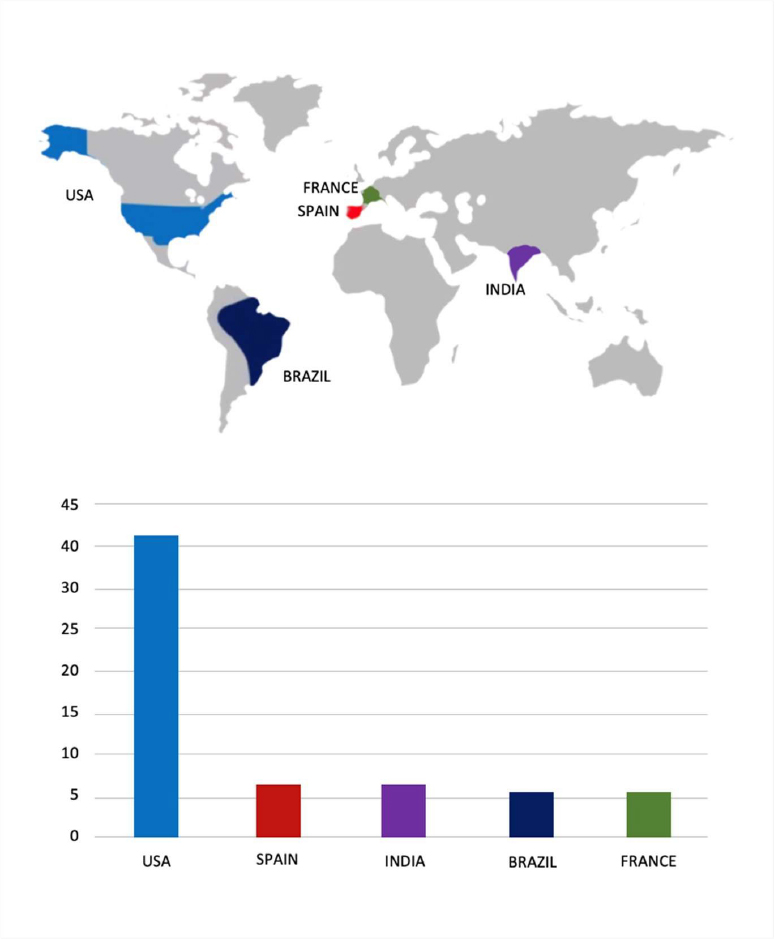
Target Countries: Brazil, United States, India, South Africa, Egypt, Spain, Colombia, Italy, Namibia
Target Industries: Manufacturing, Education, Healthcare, Technology, Energy
Introduction
CYFIRMA Research and Advisory Team has found Vect Ransomware while monitoring various underground forums as part of our Threat Discovery Process.
Vect Ransomware
Researchers have identified Vect as a ransomware threat that compromises systems by encrypting files, modifying system settings, and enforcing extortion through ransom demands. After infection, it renames encrypted files by appending a “.vect” extension, alters the desktop wallpaper, and drops a ransom note (“!!!_READ_ME_!!!.txt”) that directs victims to anonymous communication channels. The note claims that files are encrypted using the ChaCha20 algorithm and that sensitive data, such as databases and backups, has been exfiltrated. Victims are pressured to pay for a decryption tool and are warned against modifying files or using third-party recovery methods, with threats of permanent data loss and public exposure.

Screenshot of files encrypted by the ransomware (Source: Surface Web)
From an operational standpoint, Vect has evolved into a ransomware-as-a-service model, allowing affiliates to deploy the malware while sharing profits with the operators. It utilizes a custom-built C++ codebase and targets both Windows and Linux/ESXi systems, indicating cross-platform capability. Its attack workflow includes initial access via phishing, stolen credentials, or exposed remote services like RDP and VPN, followed by execution through command-line interpreters and persistence mechanisms such as scheduled tasks. The malware employs privilege escalation and credential dumping to expand access, while conducting system and network discovery to identify valuable assets and shared resources.
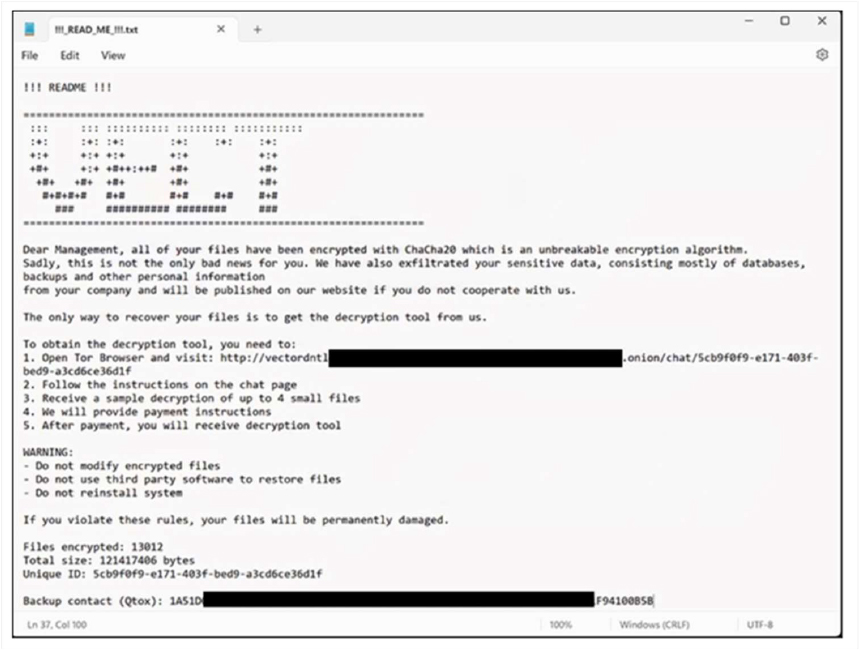
The appearance of the Vect Ransomware ransom note (“!!!_READ_ME_!!!.txt”) (Source: Surface Web)
Technically, Vect demonstrates advanced defense evasion and impact techniques. It can force systems into Safe Mode to bypass security controls, disable protective tools, and terminate critical services, including backups, to inhibit recovery. Lateral movement is achieved through remote services like SMB and WinRM, enabling propagation across networks. Data is collected locally and from shared drives, then exfiltrated through encrypted channels over anonymized infrastructure before encryption is executed. Command-and-control communication is maintained via encrypted protocols, and the malware’s final impact includes file encryption, service disruption, and prevention of system recovery, aligning with a structured “exfiltration, encryption, and extortion” attack model.
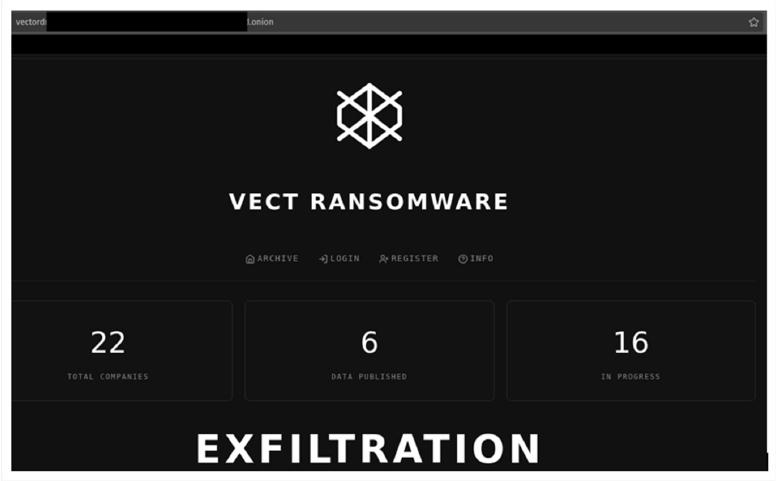
The appearance of the Data leak site of Vect Ransomware
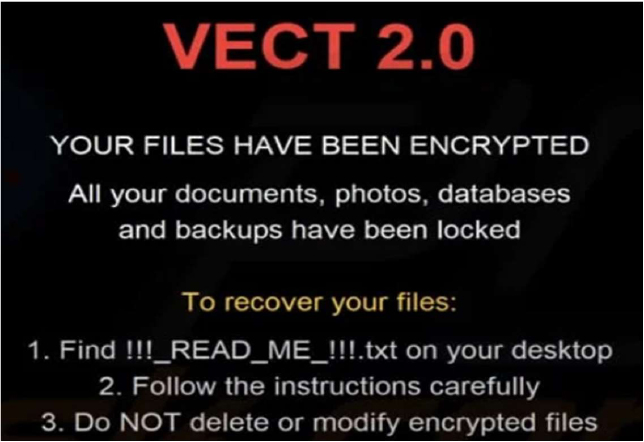
The appearance of Wallpaper after encryption of Vect Ransomware
The following are the TTPs based on the MITRE Attack Framework
| Tactic | Technique ID | Technique Name |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1129 | Shared Modules |
| Persistence | T1112 | Modify Registry |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1055.003 | Process Injection: Thread Execution Hijacking |
| Privilege Escalation | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Defense Evasion | T1027.005 | Obfuscated Files or Information: Indicator Removal from Tools |
| Defense Evasion | T1055.003 | Process Injection: Thread Execution Hijacking |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1112 | Modify Registry |
| Defense Evasion | T1202 | Indirect Command Execution |
| Defense Evasion | T1497 | Virtualization/Sandbox Evasion |
| Defense Evasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| Defense Evasion | T1564.003 | Hide Artifacts: Hidden Window |
| Defense Evasion | T1620 | Reflective Code Loading |
| Discovery | T1007 | System Service Discovery |
| Discovery | T1016.001 | System Network Configuration Discovery: Internet Connection Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1135 | Network Share Discovery |
| Discovery | T1497 | Virtualization/Sandbox Evasion |
| Discovery | T1518 | Software Discovery |
| Collection | T1113 | Screen Capture |
| Impact | T1489 | Service Stop |
Relevancy and Insights:
ETLM Assessment:
CYFIRMA’s assessment indicates Vect is a technically capable ransomware with cross-platform functionality, supporting both Windows and Linux/ESXi environments through a custom C++ codebase. It demonstrates mature operational tradecraft, including Safe Mode execution, security control impairment, and coordinated file encryption combined with data exfiltration. The ransomware follows a structured attack lifecycle, beginning with initial access via phishing, stolen credentials, or exposed remote services, and progressing through privilege escalation, credential dumping, and lateral movement using protocols such as SMB and WinRM. It conducts extensive system and network discovery before executing its payload, selectively encrypting, deleting, or hiding files while appending the “.vect” extension. Its command-and-control communications are maintained over encrypted and anonymized channels, and its operators enforce ransom payments through privacy-focused cryptocurrency while leveraging a dedicated leak site to pressure victims through public data exposure.
The same assessment indicates that Vect is positioned to evolve into a more scalable and resilient threat, particularly due to its ransomware-as-a-service model and structured affiliate recruitment. Its current architecture and operational discipline suggest continued refinement in automation, targeting efficiency, and evasion capabilities, including improved mechanisms for bypassing endpoint detection and response systems. The use of anonymized infrastructure, encrypted peer-to-peer communication, and exclusive reliance on hidden services indicates a deliberate focus on operational security that is likely to persist and strengthen. Additionally, its established “exfiltration, encryption, extortion” model and active data leak practices suggest a continued emphasis on multi-layered coercion techniques. As affiliate adoption grows, the threat surface is expected to expand across sectors and geographies, supported by modular tooling, consistent attack methodologies, and ongoing enhancements to its infrastructure and negotiation mechanisms.
Sigma rule:
title: New RUN Key Pointing to Suspicious Folder tags:
– attack.privilege-escalation
– attack.persistence
– attack.t1547.001 logsource:
category: registry_set product: windows
detection: selection_target:
TargetObject|contains:
– ‘\Software\Microsoft\Windows\CurrentVersion\Run’
– ‘\Software\WOW6432Node\Microsoft\Windows\CurrentVersion\Run’
– ‘\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run’ selection_suspicious_paths_1:
Details|contains:
– ‘:\Perflogs’
– :\ProgramData’
– ‘:\Windows\Temp’
– ‘:\Temp’
– ‘\AppData\Local\Temp’
– ‘\AppData\Roaming’
– ‘:\$Recycle.bin’
– ‘:\Users\Default’
– ‘:\Users\public’
– ‘%temp%’
– ‘%tmp%’
– ‘%Public%’
– ‘%AppData%’ selection_suspicious_paths_user_1:
Details|contains: ‘:\Users\’ selection_suspicious_paths_user_2:
Details|contains:
– ‘\Favorites’
– ‘\Favourites’
– ‘\Contacts’
– ‘\Music’
– ‘\Pictures’
– ‘\Documents’
– ‘\Photos’
filter_main_windows_update:
TargetObject|contains: ‘\Microsoft\Windows\CurrentVersion\RunOnce\’ Image|startswith: ‘C:\Windows\SoftwareDistribution\Download\’ Details|contains|all:
– ‘rundll32.exe ‘
– ‘C:\WINDOWS\system32\advpack.dll,DelNodeRunDLL32’ Details|contains:
– ‘\AppData\Local\Temp\’
– ‘C:\Windows\Temp\’ filter_optional_spotify:
Image|endswith:
– ‘C:\Program Files\Spotify\Spotify.exe’
– ‘C:\Program Files (x86)\Spotify\Spotify.exe’
– ‘\AppData\Roaming\Spotify\Spotify.exe’ TargetObject|endswith:
‘SOFTWARE\Microsoft\Windows\CurrentVersion\Run\Spotify’ Details|endswith: ‘Spotify.exe –autostart –minimized’
condition: selection_target and (selection_suspicious_paths_1 or (all of selection_suspicious_paths_user_* )) and not 1 of filter_main_* and not 1 of filter_optional_*
falsepositives:
– Software using weird folders for updates level: high
(Source: Surface Web)
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
Type: Clipper| Objectives: Data Exfiltration | Target Technology: Windows OS |
Target Geography: Global
CYFIRMA collects data from various forums based on which the trend is ascertained. We identified a few popular malwares that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week, “Efimer Clipper” malware is in focus.
Overview of Operation Efimer Clipper Malware
Efimer is a multi-component malware threat that has developed into a broad campaign targeting both individual users and organizational environments through deceptive delivery methods and social engineering. Initially observed spreading via compromised WordPress websites, the campaign later expanded to include phishing emails posing as legal notices related to alleged trademark violations. These messages encourage recipients to open a malicious attachment containing a script that, once executed, installs the malware silently on the system and initiates its activities without obvious signs of compromise.
After execution, Efimer primarily functions as a cryptocurrency-focused Trojan with clipboard-monitoring capabilities. It observes clipboard activity to identify cryptocurrency wallet addresses, mnemonic seed phrases, and other related data. When such information is detected, the malware exfiltrates the data and replaces copied wallet addresses with attacker-controlled alternatives, enabling fraudulent redirection of funds. Communication with its command-and-control infrastructure occurs through the Tor network, which helps conceal network activity and reduces the likelihood of straightforward detection.
In addition to direct data theft, Efimer incorporates auxiliary scripts that extend its operational reach and persistence. These components are capable of brute-forcing credentials for WordPress sites to facilitate further distribution, harvesting email addresses to support additional malicious email campaigns, and executing tasks received from its operators. The combination of deceptive distribution techniques, modular functionality, and continued evolution has enabled Efimer to affect a significant number of systems across multiple regions.
Attack Method
The Efimer infection chain begins with social engineering or malicious content hosted on compromised websites, where victims are persuaded to execute a seemingly legitimate archive or media-related file. The delivered payload commonly includes a Windows Script File (WSF) or executable that performs an initial privilege check by attempting write access to protected system locations. Based on the privilege level, the script establishes persistence either through scheduled tasks or registry autorun entries and immediately modifies Windows Defender exclusion policies to shield its working directories and key processes from security inspection.
Once persistence is secured, the malware deploys its primary controller script into a public directory and initiates communication with its command-and-control infrastructure through a locally installed Tor proxy. Rather than embedding direct networking code, Efimer leverages legitimate utilities such as curl, wscript, PowerShell, and cmd.exe to blend malicious traffic with normal system activity. A uniquely generated GUID is used to identify the infected host, and periodic beaconing is controlled by an internal timer to avoid generating suspicious network patterns. The controller can receive instructions dynamically from the C2 server, including JavaScript payloads that are executed in memory using evaluation functions.
A core component of the attack focuses on clipboard monitoring and cryptocurrency manipulation. The malware continuously inspects the clipboard content for wallet addresses and mnemonic seed phrases. When identified, this data is written in a temporary file, exfiltrated to the C2 server via Tor, and then removed to erase evidence. Simultaneously, wallet addresses copied by the user are replaced with attacker-controlled addresses that closely resemble the original through character-matching logic, increasing the likelihood that the victim will not notice the substitution. In parallel, the malware captures screenshots using hidden PowerShell commands to provide a visual context of user activity during sensitive operations.
Efimer’s capabilities extend beyond individual host compromise. Additional scripts delivered through C2 commands enable large-scale WordPress credential brute-forcing, email address harvesting from websites, and automated spam distribution. These scripts operate concurrently in multiple processes, maintain internal tracking of attacked domains, and avoid repetition through object-based locking mechanisms. This modular design allows the attackers to use infected machines as part of a distributed infrastructure for further propagation, making Efimer not only a data-stealing Trojan but also a platform for sustained malicious operations.
The following are the TTPs based on the MITRE Attack Framework for Enterprise
| Tactic | Technique ID | Technique Name |
| Execution | T1047 | Windows Management Instrumentation |
| T1053 | Scheduled Task/Job | |
| T1059 | Command and Scripting Interpreter | |
| T1129 | Shared Modules | |
| Privilege Escalation | T1055 | Process Injection |
| T1134 | Access Token Manipulation | |
| T1548 | Abuse Elevation Control Mechanism | |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| T1036 | Masquerading | |
| T1070 | Indicator Removal | |
| T1140 | Deobfuscate/Decode Files or Information | |
| T1202 | Indirect Command Execution | |
| T1218 | System Binary Proxy Execution | |
| T1497 | Virtualization/Sandbox Evasion | |
| T1562 | Impair Defenses | |
| T1564 | Hide Artifacts | |
| Discovery | T1012 | Query Registry |
| T1016 | System Network Configuration Discovery | |
| T1057 | Process Discovery | |
| T1518.001 | Software Discovery: Security Software Discovery | |
| T1082 | System Information Discovery | |
| T1083 | File and Directory Discovery | |
| Command and control | T1071 | Application Layer Protocol |
| T1095 | Non-Application Layer Protocol | |
| Impact | T1485 | Data Destruction |
INSIGHTS
The malware demonstrates a convergence of multiple malicious objectives within a single framework. Beyond clipboard manipulation for cryptocurrency theft, the infected system is leveraged to support additional activities, such as credential harvesting, content distribution, and infrastructure support for further campaigns. This reflects an operational design, where each compromised device contributes to several layers of attacker activity rather than serving a single purpose.
Its operational pattern shows a clear preference for using legitimate system utilities and standard directories to execute malicious tasks. By relying on familiar tools and expected system behaviour, the malware minimizes the presence of overtly suspicious artifacts, allowing its actions to blend into routine processes and reducing the likelihood of immediate detection.
The campaign also reveals how compromised hosts are systematically repurposed to expand the attacker’s reach. Infected machines participate in discovering new targets, distributing malicious materials, and collecting valuable data such as website credentials and email addresses. This structured reuse of victim systems indicates an organized approach in which each infection strengthens and sustains the broader malicious ecosystem.
ETLM ASSESSMENT
From an ETLM perspective, this malware pattern points toward a future in which endpoint compromises are no longer isolated incidents but become quiet entry points into broader malicious infrastructures. Infection methods that rely on familiar user actions and routine digital workflows are likely to grow more refined, making harmful activity appear indistinguishable from normal system use. As attackers continue to align their techniques with everyday tools, web content, and communication platforms, employees may unknowingly initiate threats through actions that seem entirely legitimate. Over time, such approaches could allow covert control and data misuse to persist without obvious disruption, complicating both detection and response. For organizations, the cumulative effect may be an increasing challenge in maintaining confidence in standard digital operations, as even ordinary interactions could be subtly leveraged to support concealed cyber intrusions.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems.
YARA Rules
rule Efimer_Clipper
{
meta:
description = “Detects Efimer Clipper malware based on hash, files, PowerShell commands, registry modifications, mutex, and network indicators”
author = “CYFIRMA” date = “2026-03-30”
strings:
/* Malware Sample Hashes */
$hash_1 =
“382b3cfb2c94415156443a00d95174e3cfbe75c6975e3cb1e609bd78d71d8b1b”
/* Suspicious Files */
$file1 = “common.dat.exe”
$file2 = “VCRUNTIME140.dll”
$file3 = “VCRUNTIME140_1.dll”
/* Suspicious PowerShell exclusion commands */
$ps1 = /powershell\s+-Command\s+”Add-MpPreference\s+-ExclusionPath\s+’C:\\Users\\<USER>\\AppData\\Local\\Temp'”
$ps2 = /powershell\s+-Command\s+”Add-MpPreference\s+-ExclusionPath\s+’C:\\Users\\<USER>\\Desktop'”
$ps3 = /powershell\s+-Command\s+”Add-MpPreference\s+-ExclusionProcess\s+’C:\\Windows\\System32\\clip.exe'”
/* Registry Keys */
$reg1 = “HKEY_CURRENT_USER\\Software\\Microsoft\\.NETFramework”
$reg2 = “HKEY_CURRENT_USER\\Software\\Microsoft\\Command Processor”
$reg3 = “HKEY_CURRENT_USER\\Software\\Microsoft\\Windows Script Host\\Settings”
/* Mutex */
$mutex = “Global\\OneSettingQueryMutex”
condition:
any of ($hash_*) or any of ($file*) or any of ($ps*) or any of ($reg*) or $mutex
}
Strategic Recommendations
These are high-level, long-term initiatives to strengthen organizational cybersecurity posture:
Management Recommendations
These focus on policies, procedures, and governance to ensure proper oversight and risk mitigation:
Tactical Recommendations
These are immediate, actionable steps to prevent, detect, and respond to malware at the operational level:
Key Intelligence Signals:
Red Menshen: Advanced China-Nexus Threat Actor
About the Threat Actor
Red Menshen is a China-linked advanced threat actor active since at least 2021, known for deploying highly stealthy “digital sleeper cells” within telecommunications networks. Its campaigns are designed to enable high-level espionage, including targeted intrusions into government networks. The group is assessed to be an APT conducting cyber espionage operations using custom-developed tools.
TTPs based on MITRE ATT&CK Framework
| Tactic | ID | Technique |
| Initial Access | T1190 | Exploit Public-Facing Application |
| Initial Access | T1078 | Valid Accounts |
| Execution | T1059 | Command and Scripting Interpreter |
| Persistence | T1547 | Boot or Logon Autostart Execution |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Persistence | T1078 | Valid Accounts |
| Privilege Escalation | T1547 | Boot or Logon Autostart Execution |
| Privilege Escalation | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1078 | Valid Accounts |
| Privilege Escalation | T1068 | Exploitation for Privilege Escalation |
| Defense Evasion | T1480 | Execution Guardrails |
| Defense Evasion | T1078 | Valid Accounts |
| Defense Evasion | T1564.004 | Hide Artifacts: NTFS File Attributes |
| Defense Evasion | T1036 | Masquerading |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1070 | Indicator Removal |
| Credential Access | T1056 | Input Capture |
| Credential Access | T1110 | Brute Force |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1018 | Remote System Discovery |
| Lateral Movement | T1021.004 | Remote Services: SSH |
| Lateral Movement | T1570 | Lateral Tool Transfer |
| Collection | T1005 | Data from Local System |
| Collection | T1056 | Input Capture |
| Collection | T1119 | Automated Collection |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and Control | T1095 | Non-Application Layer Protocol |
| Command and Control | T1572 | Protocol Tunneling |
| Command and Control | T1001 | Data Obfuscation |
| Command and Control | T1105 | Ingress Tool Transfer |
| Exfiltration | T1041 | Exfiltration Over C2 Channel |
Latest Developments Observed
The threat actor is suspected of conducting a long-term espionage campaign by infiltrating telecom networks, primarily across the Middle East and Asia. The attackers are leveraging BPFdoor variants, embedding implants deeper into the computing stack by targeting operating system kernels and infrastructure platforms, rather than relying solely on user-space malware. The intent appears to be strategic positioning, maintaining a high level of stealth to evade detection while enabling prolonged, persistent surveillance over an extended period.
ETLM Insights
The threat actor, assessed to be a China-linked advanced persistent threat, demonstrates a strategic focus on long-term intelligence collection, infrastructure-level persistence, and covert access to national communication systems. Its operations emphasize positioning within telecom backbone and signaling infrastructure to gain deep visibility into subscriber data, mobility patterns, and cross-border communications, rather than pursuing immediate disruption or financial objectives.
Operationally, the actor is known to:
The actor’s behaviour reflects three core strategic drivers:
Looking ahead, the threat actor is likely to further advance its capabilities by strengthening protocol-level manipulation, expanding into 5G and cloud-native telecom architectures, and adopting more advanced evasion and encryption techniques. Future operations are expected to focus on deeper integration within signaling ecosystems and the abuse of legitimate network processes to sustain persistent, scalable, and difficult-to-detect access across global telecommunications infrastructure.
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
YARA Rules
RedMenshen_ELF_Sample
{
meta:
description = “Detects ELF samples with specific hash-like filenames” author = “CYFIRMA”
reference = “User-provided sample” date = “2026-03-31”
strings:
$elf_magic = { 7F 45 4C 46 } // ELF header
$filename1 = “elf93f4262fce8c6b4f8e239c35a0679fbbbb722141b95a5f2af53a2bcafe4edd1c”
$filename2 = “93f4262fce8c6b4f8e239c35a0679fbbbb722141b95a5f2af53a2bcafe4edd1c”
condition:
$elf_magic at 0 and any of ($filename*)
}
Strategic Recommendations
Management Recommendations
Tactical Recommendations
Iranian hackers claim breach of FBI director’s email, phishing surges
The US Federal Bureau of Investigation (FBI) has confirmed a breach of FBI Director Kash Patel’s personal email account. The agency stated that the compromised data is “historical in nature and involves no government information. “The Iran-linked hacking group Handala claimed responsibility for the breach and published photos and emails allegedly stolen from the account. The emails date from between 2010 and 2019 and include a mix of personal and professional correspondence.
Meanwhile, cybersecurity researchers are tracking a sharp rise in phishing and malware activity targeting organizations in Gulf countries amid the ongoing conflict in Iran. Malicious email campaigns have increased by approximately 130% since February 28th. Activity doubled within days of the conflict’s start and peaked at nearly four times baseline levels. Researchers noted that the campaigns appear to be sustained and coordinated, with attackers adjusting tactics in real time to exploit heightened regional tensions and business disruptions.
ETLM Assessment:
Handala presents itself as an independent hacktivist collective, but cybersecurity experts and the US government assess that the group is tied to Iranian intelligence services, specifically operating under the direction of Iran’s Ministry of Intelligence and Security (MOIS). The group has become significantly more active since the outbreak of the current conflict; Handala also claimed responsibility for a disruptive cyberattack against a major US medical technology company earlier last month.
Although state-sponsored cyber operations are occurring alongside the conflict, much of the observed phishing and malware activity is financially motivated. Criminal threat actors are exploiting fear and uncertainty across the region.
NightSpire Ransomware Impacts OTNet Co., Ltd.
Summary:
CYFIRMA observed in an underground forum that a company from Japan, OTNet Co., Ltd. (https[:]//www[.]otnet[.]co[.]jp/), was compromised by NightSpire Ransomware. OTNet Co., Ltd is a telecommunications company based in Okinawa, Japan, specializing in broadband, fiber optic networks, and related services across Okinawa Island. It operates as a power utility-affiliated carrier (NCC) providing high-reliability infrastructure for sectors like public services, finance, healthcare, and education. The compromised data includes confidential and sensitive information belonging to the organization.

Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, NightSpire is a ransomware group that emerged in early 2025, marking itself as a formidable player in the rapidly evolving ransomware landscape. Despite its recent appearance, NightSpire has already gained attention for its aggressive tactics and well-structured operations.
The Gentlemen Ransomware Impacts Omikenshi
Summary:
CYFIRMA observed in an underground forum that a company from Japan, Omikenshi (https[:]//omikenshi[.]co[.]jp/), was compromised by the Gentlemen Ransomware. Omikenshi specializes in the production of textiles, including cotton and yarn, as well as advanced processing technologies. The company also offers a range of lifestyle products, cosmetics, and software development services. The data, which has been breached, has not yet appeared on the leak site, indicating that negotiations between the affected party and the ransomware group may be underway. The compromised data includes confidential and sensitive information belonging to the organization.
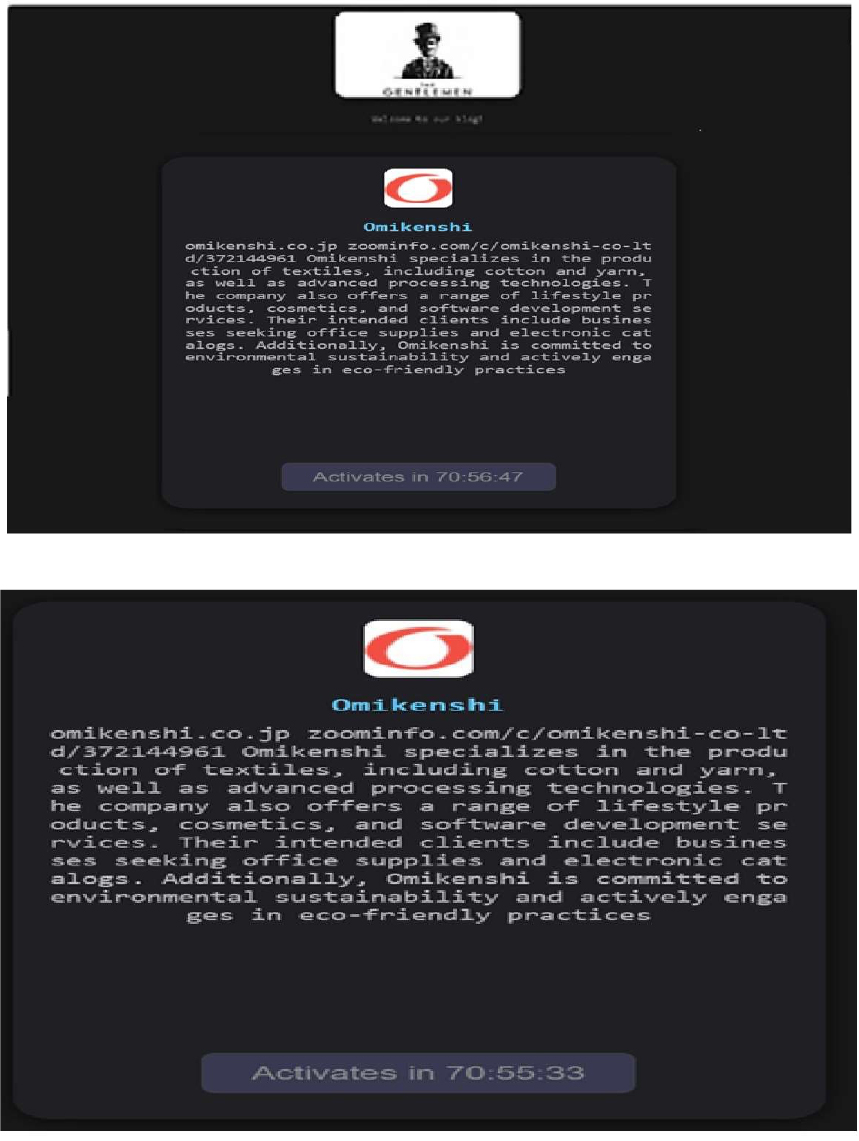
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, the Gentlemen Ransomware is a highly adaptive and globally active threat that leverages dual-extortion tactics, combining data theft with file encryption. The group employs advanced evasion and persistence techniques, supports cross-platform and scalable ransomware deployment, and conducts targeted attacks across multiple industries and geographic regions. This combination of capabilities makes it a significant risk to enterprise cybersecurity defenses, particularly for organizations with limited detection and incident-response maturity.
Vulnerability in Netty
Relevancy & Insights:
The vulnerability exists due to improper validation of HTTP requests within chunked transfer encoding extension values.
Impact:
A remote attacker can send a specially crafted HTTP request to the server and smuggle arbitrary HTTP headers.
Affected Products:
https[:]//github[.]com/netty/netty/security/advisories/GHSA-pwqr-wmgm-9rr8/#poc
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
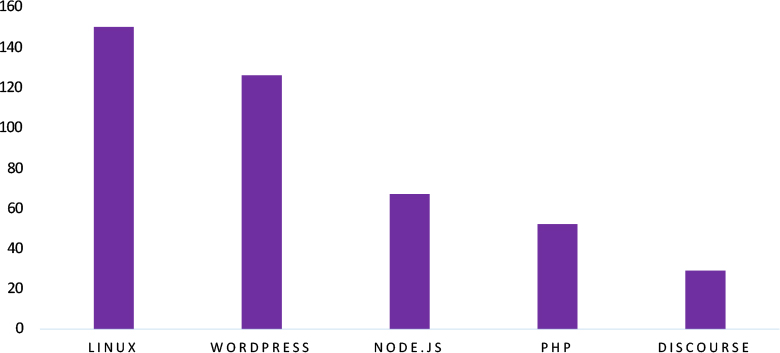
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies due to a range of vulnerabilities. The following are the top 5 most affected technologies.
ETLM Assessment
Vulnerability in the Netty framework introduces significant risks to applications that rely on high-performance network communication for handling HTTP requests and backend services. As Netty is widely used across enterprise environments, cloud-native applications, and microservices architectures, exploitation of this vulnerability could allow attackers to manipulate request processing and bypass security controls. Organizations leveraging Netty-based applications must ensure timely patching and implement robust request validation and monitoring mechanisms to detect suspicious traffic patterns. Addressing this vulnerability is essential to maintaining the integrity of application communication layers and safeguarding critical infrastructure across industries and geographic regions.
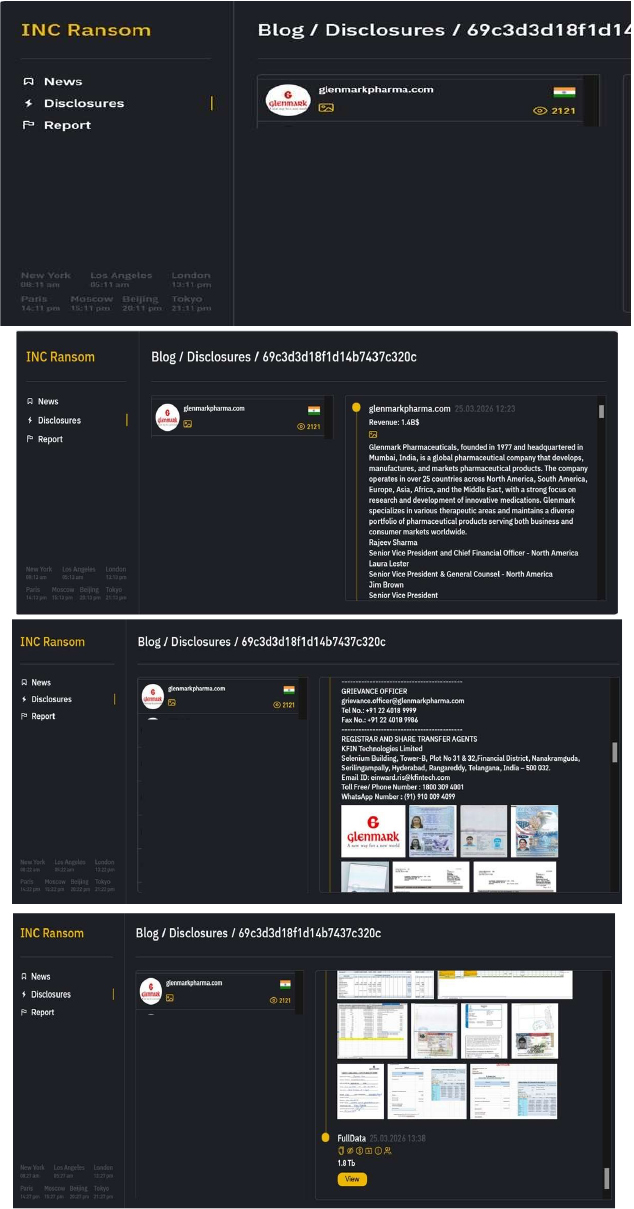
INC Ransomware attacked and published the data of Glenmark Pharmaceuticals
Summary:
Recently, we observed that INC Ransomware attacked and published the data of Glenmark Pharmaceuticals(https[:]//glenmarkpharma[.]com/) on its dark web website. Glenmark Pharmaceuticals, founded in 1977 and headquartered in Mumbai, India, is a global pharmaceutical company that develops, manufactures, and markets pharmaceutical products. The company operates in over 25 countries across North America, South America, Europe, Asia, Africa, and the Middle East, with a strong focus on research and development of innovative medications. Glenmark specializes in various therapeutic areas and maintains a diverse portfolio of pharmaceutical products serving both business and consumer markets worldwide. Screenshots from a ransomware leak site show Glenmark’s compromise of approximately 1.8 TB of sensitive data, including financial records, invoices, account statements, transaction details, operational spreadsheets, vendor and procurement info, employee records with payroll and HR data, customer contacts, confidential documents, incidents, and business analytics.
Data Categories
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
Based on recent assessments by CYFIRMA, INC Ransomware represents a significant threat within the evolving landscape of ransomware attacks. Its use of strong encryption methods and double extortion tactics highlights the increasing sophistication of cybercriminal operations. Organizations are advised to enhance their cybersecurity measures by implementing robust defenses against phishing attacks, maintaining updated security protocols, and monitoring for unusual network activity to mitigate risks associated with this and other ransomware variants. Continuous vigilance is essential to protect against the threats posed by emerging ransomware groups like INC Ransomware.
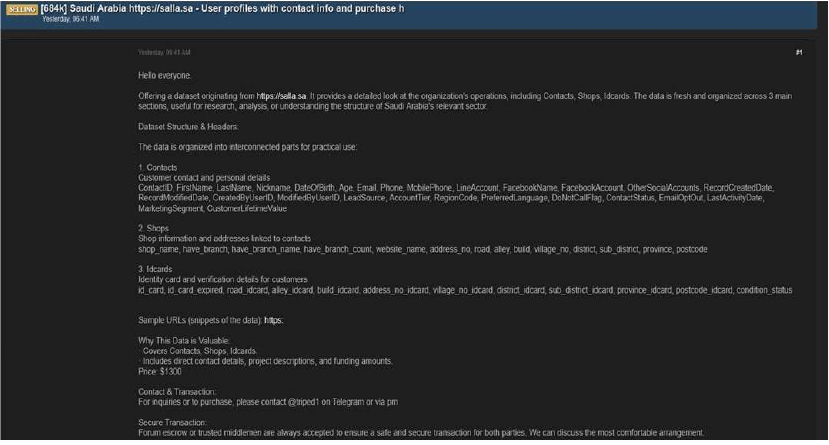
Salla Data Advertised on a Leak Site
Summary:
The CYFIRMA research team identified a post on a dark web forum by a threat actor using the alias “Grubder”, who claims to possess and offer for sale a substantial dataset allegedly obtained from salla[.]sa, a Saudi Arabia–based e-commerce platform that enables individuals and businesses to create, manage, and operate online stores through a SaaS model. The post indicates that the dataset is well-structured and may contain detailed information related to business operations, customer interactions, and identity-associated records.
According to the threat actor, the exposed dataset is organized into multiple interconnected segments and is being marketed as fresh, well-structured, and suitable for analysis or commercial use. The actor claims the data is divided into three primary categories:
1. Contacts (Customer Information)
This section allegedly contains detailed personal and account-related information, including:
2. Shops (Business Information)
3. ID Cards (Identity Verification Data)
Additional Claims by the Threat Actor
Sale Details
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
Source: Underground Forums
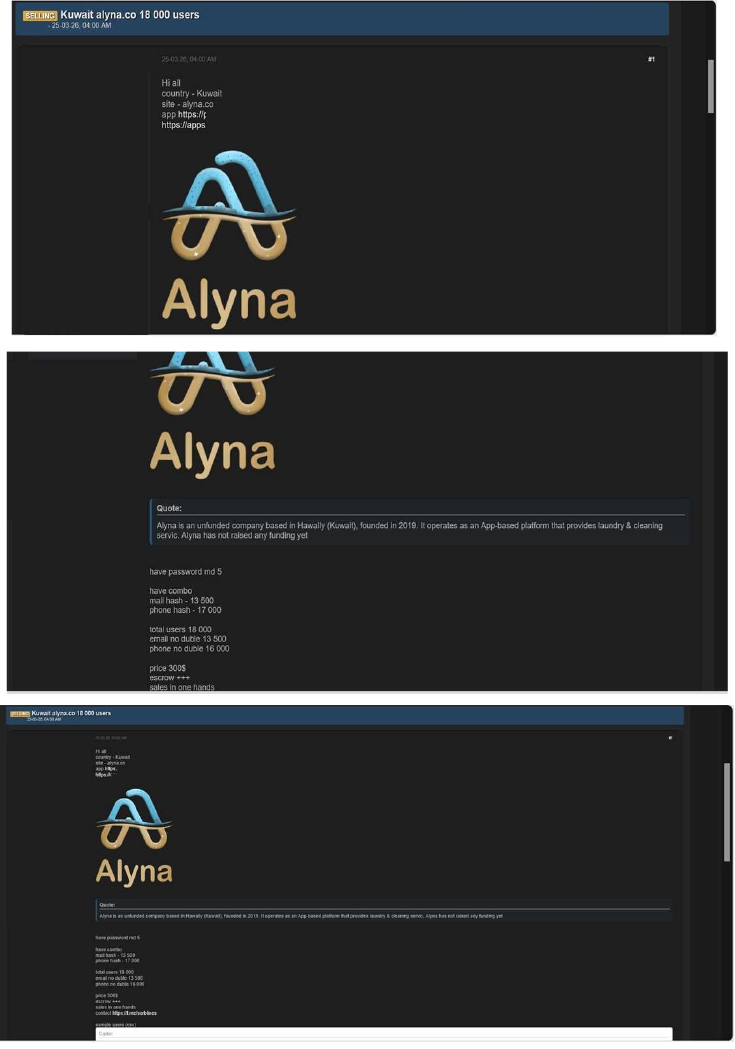
Alyna Data Advertised on a Leak Site
Summary:
The CYFIRMA research team identified a post on a dark web forum by a threat actor using the alias “Sorb”, claiming to be in possession of a dataset allegedly associated with Alyna[.]co, a Kuwait-based app offering laundry and cleaning services. The actor advertises the dataset as containing user information and is offering it for sale at a relatively low price, suggesting possible unauthorized access or aggregation of user data.
The threat actor recently posted on a cybercrime forum, claiming to possess a database containing approximately 18,000 user records and offering it for sale for
$300 USD. The post indicates that the data is structured and includes both raw and hashed credential-related information.
Allegedly Compromised Data Details
According to the threat actor, the dataset includes:
Sale and Distribution Details
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
Source: Underground Forums
Relevancy & Insights:
Financially motivated cybercriminals are continuously looking for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to gain access and steal valuable data. Subsequently, the stolen data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor known as “Grubder” is assessed to be a highly active and capable group primarily engaged in data-leak operations. Multiple credible sources have associated this actor with a series of security incidents involving unauthorized access to systems and the sale or dissemination of stolen data on dark web marketplaces. These activities underscore the persistent and rapidly evolving cyber-threat landscape driven by underground criminal ecosystems and highlight the urgent need for organizations to reinforce their cybersecurity posture through continuous monitoring, improved threat-intelligence capabilities, and proactive defensive measures to protect sensitive information and critical infrastructure.
Recommendations: Enhance the cybersecurity posture by:
The CYFIRMA research team observed that Arcterminal[.]xyz, a cryptocurrency and quest-tracking platform, has allegedly been compromised, exposing a database containing 66,769 unique user emails. The data is reportedly being advertised for sale for $1,500 by an unknown party on a cybercrime forum.
The allegedly compromised data includes:
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
Source: Underground Forums
Relevancy & Insights:
Financially motivated cybercriminals are continuously looking for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to gain access and steal valuable data. Subsequently, the stolen data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor known as “Grubder” is assessed to be a highly active and capable group primarily engaged in data-leak operations. Multiple credible sources have associated this actor with a series of security incidents involving unauthorized access to systems and the sale or dissemination of stolen data on dark web marketplaces. These activities underscore the persistent and rapidly evolving cyber-threat landscape driven by underground criminal ecosystems and highlight the urgent need for organizations to reinforce their cybersecurity posture through continuous monitoring, improved threat-intelligence capabilities, and proactive defensive measures to protect sensitive information and critical infrastructure.
Recommendations: Enhance the cybersecurity posture by:
The CYFIRMA research team observed that Arcterminal[.]xyz, a cryptocurrency and quest-tracking platform, has allegedly been compromised, exposing a database containing 66,769 unique user emails. The data is reportedly being advertised for sale for $1,500 by an unknown party on a cybercrime forum.
The allegedly compromised data includes:
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.

Source: Underground Forums
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
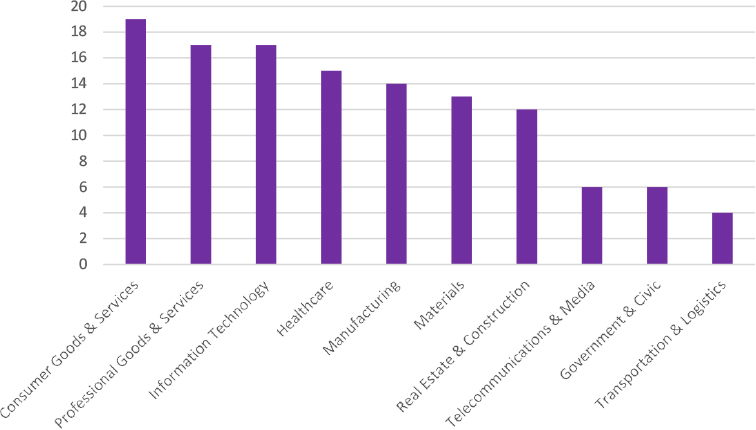
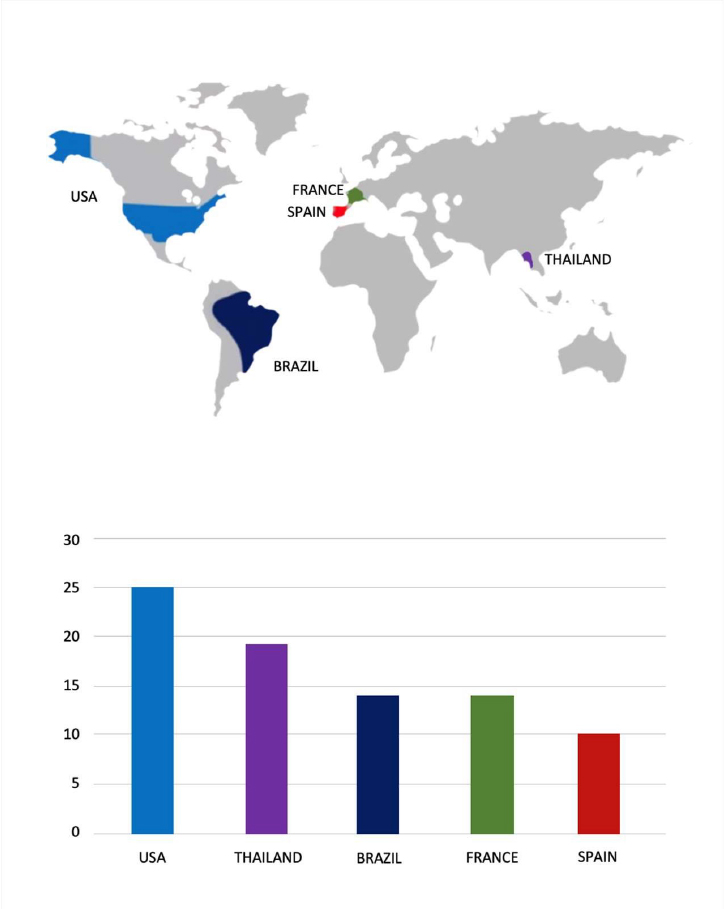
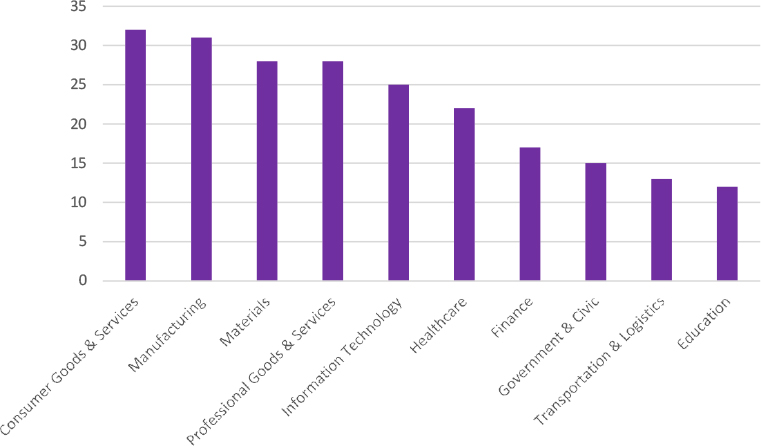
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
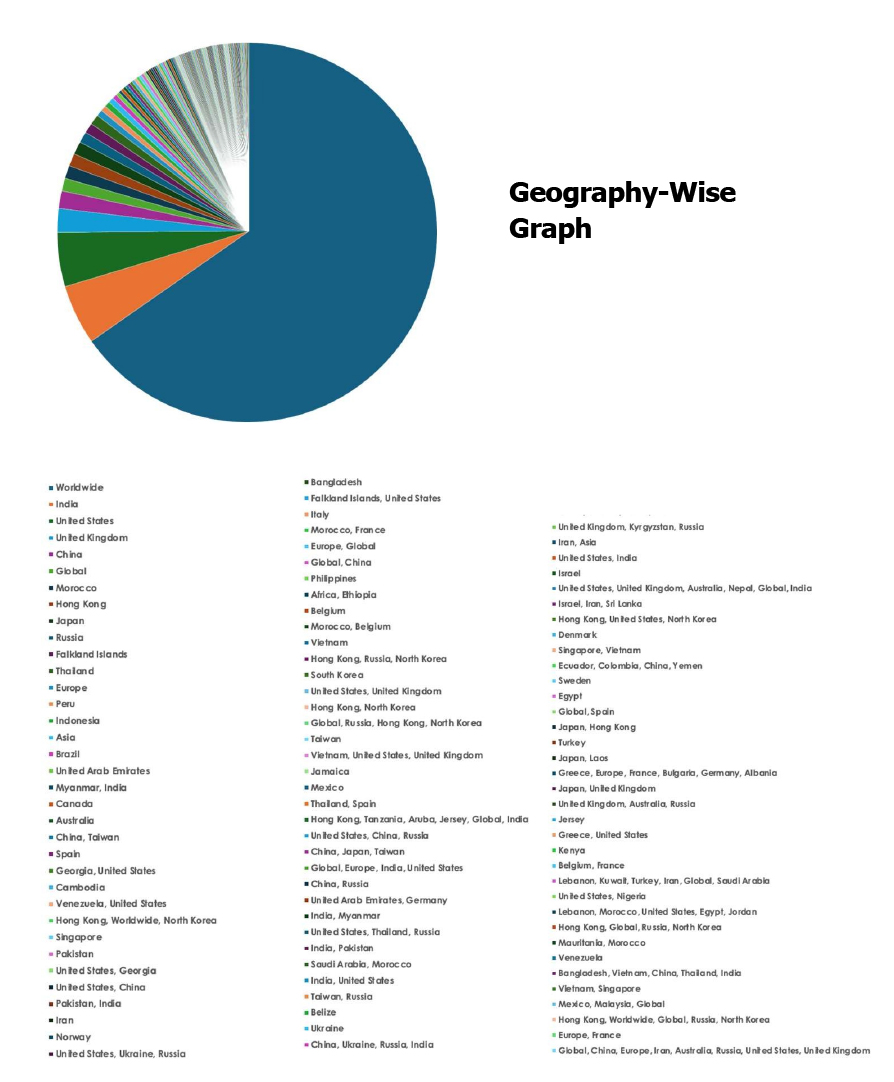
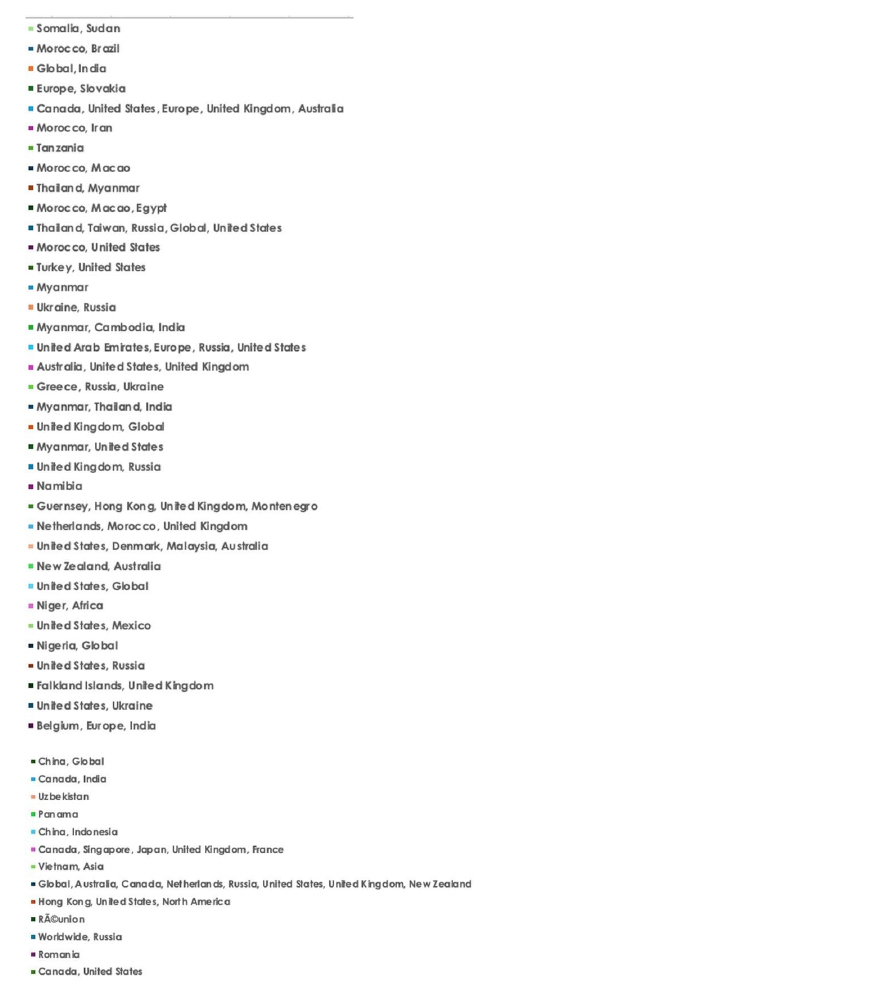
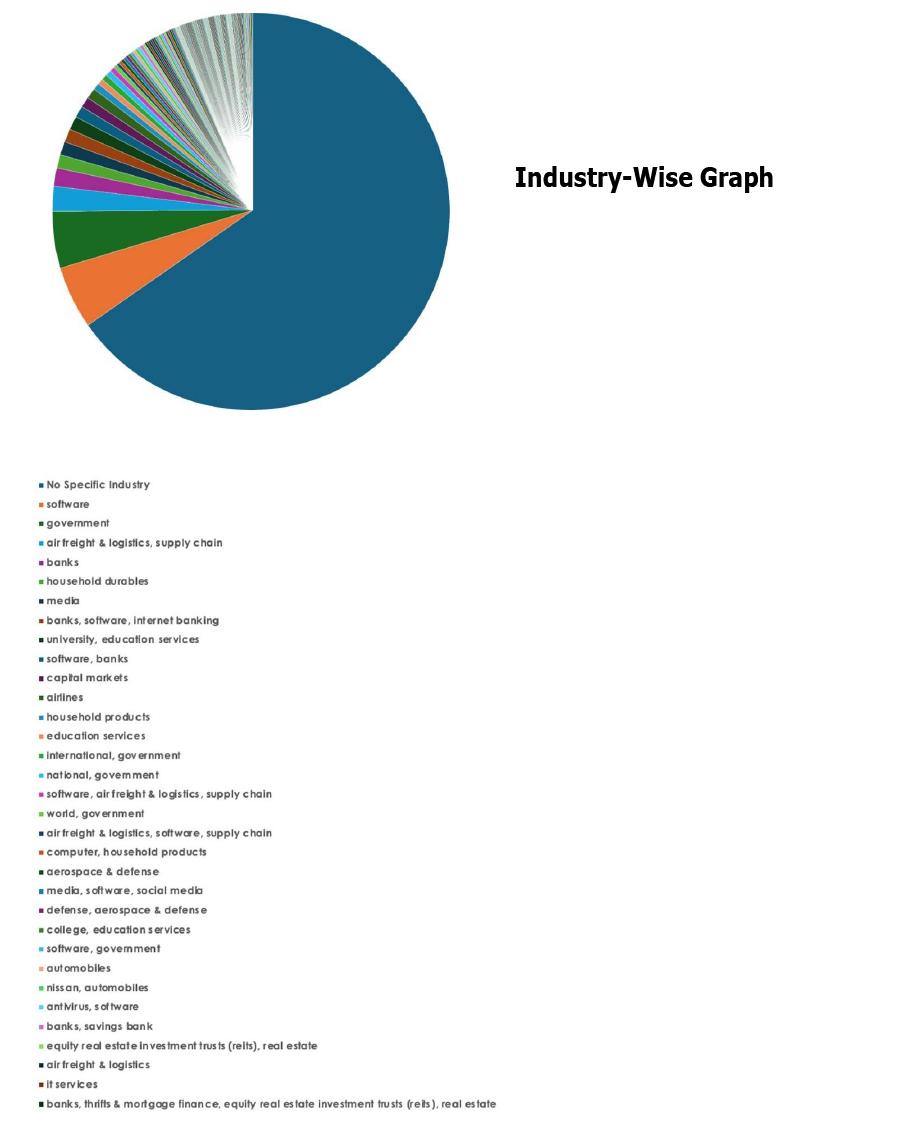
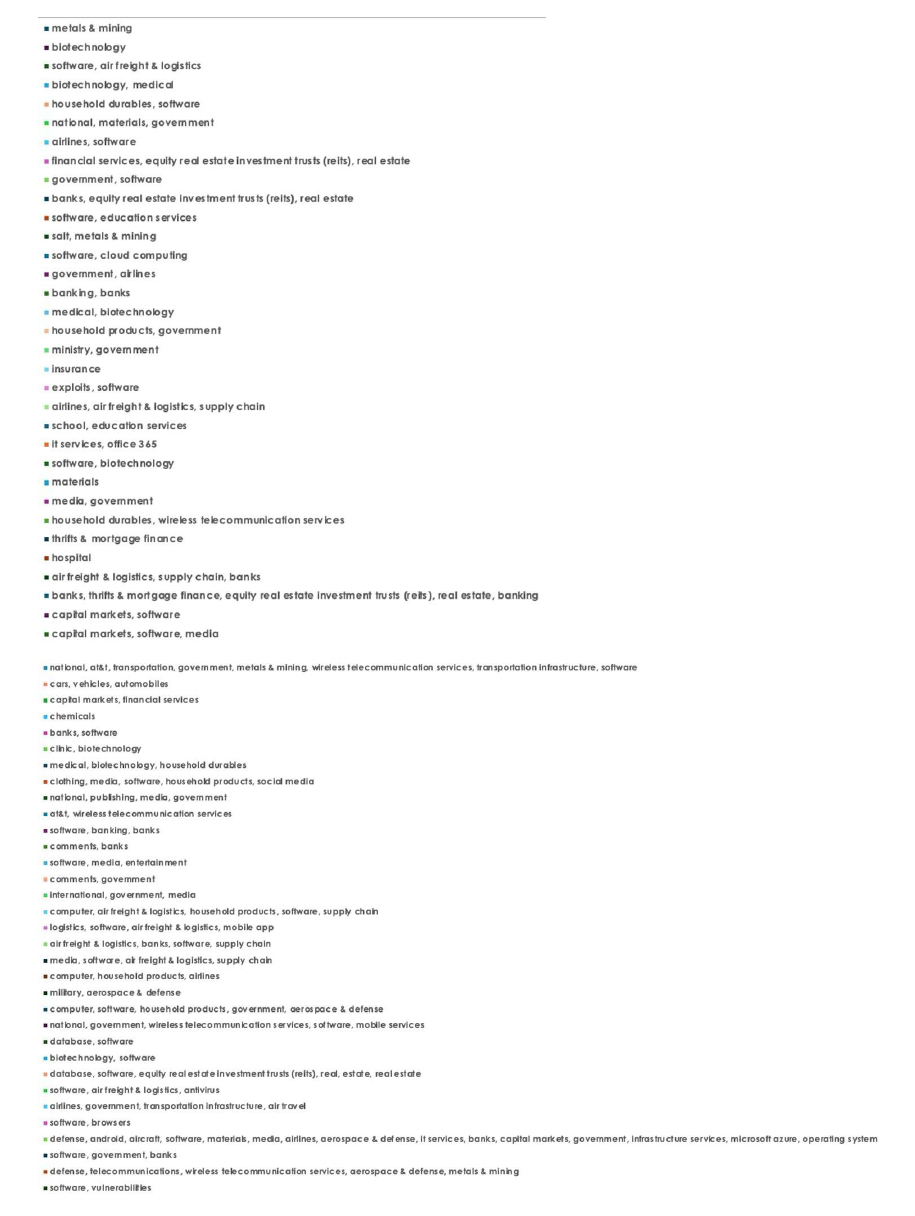
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.