


Ransomware activity in April 2026 reflects a rapidly maturing, highly adaptive, and increasingly industrialized cybercriminal ecosystem, with 801 publicly disclosed incidents recorded globally, reinforcing the continued expansion of ransomware-as-a-service (RaaS) operations and the sustained escalation observed throughout 2025 and early 2026.
The threat landscape remains heavily concentrated against high-value economies and operationally critical sectors, with the United States recording 1,563 victims, while industries such as Professional Goods & Services, Manufacturing, Healthcare, Consumer Goods & Services, and Information Technology experienced the highest levels of targeting due to their operational dependency and sensitive data exposure.
At the same time, ransomware actors are advancing tradecraft through rapid vulnerability exploitation, credential-based intrusions, botnet-assisted delivery, virtualization-backed evasion, low-noise execution methods, and cross-platform targeting of Windows, Linux, ESXi, and virtualized infrastructure, enabling faster, stealthier, and more scalable attacks. The ecosystem is also undergoing a significant economic and operational shift toward data-centric, multi-layered extortion models, where data theft, reputational pressure, and business disruption increasingly outweigh encryption alone, reflecting ransomware’s transformation into a resilient and globally distributed cybercrime economy.
Overall, April 2026 demonstrates that ransomware is no longer simply a disruptive malware threat but a persistent, modular, and highly scalable operational ecosystem requiring organizations to prioritize proactive threat intelligence, rapid vulnerability management, identity security, third-party risk oversight, and mature incident response readiness to reduce both operational and financial impact.
Welcome to the April 2026 Ransomware Threat Report. This report delivers a detailed analysis of the ransomware landscape, highlighting the emergence of new ransomware groups, evolving attack techniques, and notable shifts in targeted industries. By examining key trends, tactics, and significant incidents, this report aims to support organizations and security teams in understanding the current threat environment. As ransomware campaigns continue to grow in complexity, this report serves as a vital resource for anticipating future threats and strengthening proactive cybersecurity strategies.
Throughout April 2026, there was notable activity from several ransomware groups.
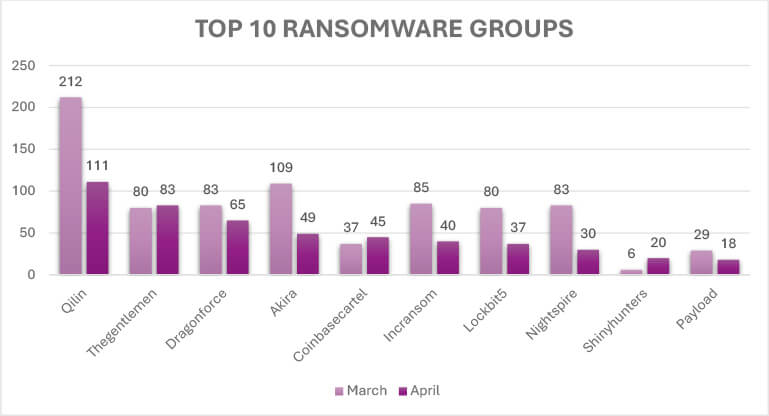
The March–April 2026 data reflects a mixed but still highly active ransomware landscape, characterized by declining activity among several dominant groups alongside continued expansion by a smaller number of actors. Qilin remained the most active operator despite a substantial decline from 212 to 111 incidents, while Dragonforce (83 → 65), Akira (109 → 49), Incransom (85 → 40), LockBit5 (80 → 37), and Nightspire (83 → 30) recorded notable decreases, suggesting reduced operational tempo, disruption, or shifts in campaign strategy. In contrast, TheGentlemen slightly increased its activity from 80 to 83 incidents, Coinbasecartel expanded from 37 to 45 incidents, and Shinyhunters rose sharply from 6 to 20 incidents, indicating continued operational growth and increased campaign execution among select actors. Payload experienced a moderate decline from 29 to 18 incidents but maintained operational visibility. Overall, April 2026 represented a redistribution of ransomware activity rather than a broad contraction, with declining activity among some previously dominant groups offset by the persistence and expansion of other ransomware operators across the evolving ransomware-as-a-service ecosystem.
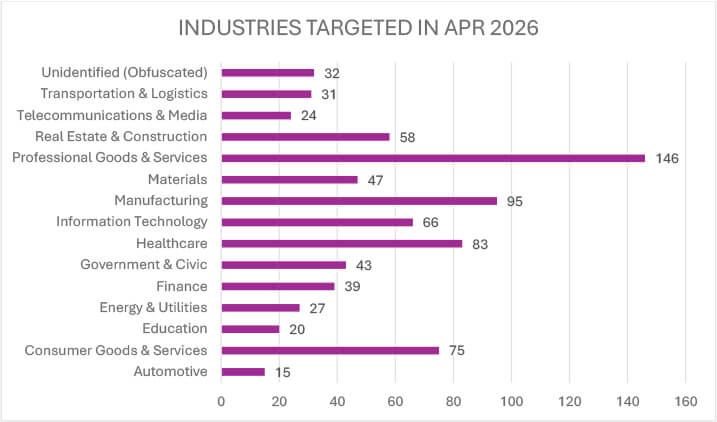
In April 2026, ransomware activity remained heavily concentrated in sectors combining operational dependency with high-value data exposure, with Professional Goods & Services (146 incidents) emerging as the most targeted sector, reflecting a continued focus on organizations handling sensitive client and business-critical data. Manufacturing (95), Healthcare (83), Consumer Goods & Services (75), and Information Technology (66) also recorded substantial activity, highlighting sustained pressure on production-driven, service-oriented, and digitally dependent industries where operational disruption can have immediate financial and strategic impact. Significant targeting was further observed in Real Estate & Construction (58), Materials (47), and Government & Civic (43), indicating continued exposure across infrastructure and public-facing sectors. Mid-level activity included Finance (39), Transportation & Logistics (31), Energy & Utilities (27), and Telecommunications & Media (24), while comparatively lower volumes were recorded in Education (20) and Automotive (15). Additionally, 32 incidents remained unidentified or obfuscated, reinforcing the persistent challenge of attribution within the ransomware ecosystem. Overall, the sectoral distribution demonstrates a continued emphasis on industries where operational disruption, supply-chain impact, and data compromise can be most effectively monetized by ransomware operators.
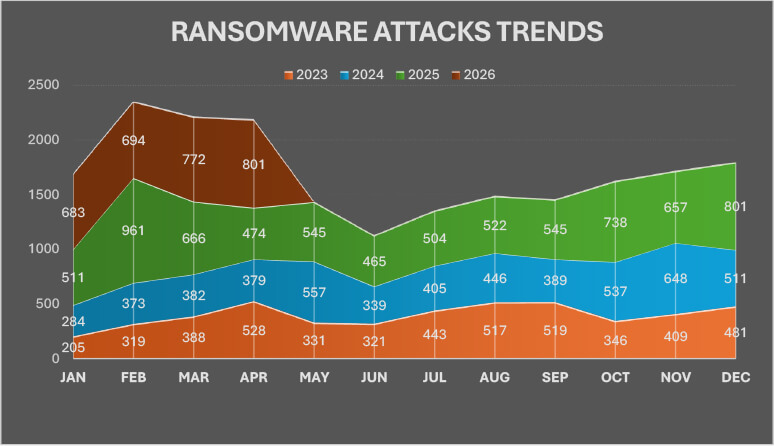
Ransomware activity demonstrates a clear year-on-year escalation, with April 2026 reaching 801 incidents, the highest monthly total recorded across the 2023–2026 dataset, surpassing both April 2025 (474) and April 2024 (379), indicating sustained structural growth rather than short-term fluctuation. Throughout 2025, activity remained consistently elevated, with multiple months exceeding 500 incidents and major spikes observed in February (961), October (738), November (657), and December (801), reflecting a sharp acceleration in ransomware operations and affiliate-driven campaigns. This momentum continued into 2026, where January (683), February (694), March (772), and April (801) all significantly exceeded equivalent periods in 2023 and 2024, reinforcing the persistence of elevated threat activity. Although February 2025 remains the single largest outlier spike, the broader trend highlights continued operational scaling, expansion of ransomware-as-a-service (RaaS) ecosystems, and increasingly mature campaign execution capabilities across the ransomware landscape.
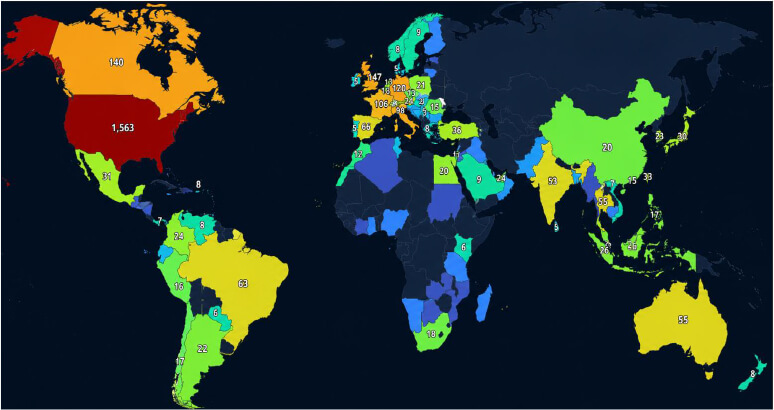
Ransomware activity in April 2026 remained heavily concentrated in the United States, which recorded 1,563 victims, maintaining a dominant lead over all other countries and reinforcing its position as the primary global target. A second tier of heavily targeted regions included the United Kingdom (147), Canada (140), Germany (120), France (106), and Italy (98), highlighting sustained adversary focus on mature, high-value economies with extensive digital infrastructure and high extortion potential. Beyond this, notable activity was observed in Spain (66), Brazil (63), Australia (55), Thailand (55), India (53), and Turkey (36), indicating continued expansion across both developed and emerging markets. Mid-level activity was distributed across countries such as Switzerland (34), Taiwan (33), Mexico (31), Japan (30), Singapore (26), Malaysia (25), UAE (24), Colombia (24), Austria (24), South Korea (23), Argentina (22), and Poland (21), reflecting consistent targeting of globally connected economies and regional commercial hubs. Additional activity remained broadly dispersed across Europe, Asia, Africa, and Latin America, while 115 incidents were classified as unidentified or obfuscated, reinforcing the persistent attribution challenges within the ransomware ecosystem. Overall, the geographic distribution demonstrates both a strong concentration against North American and Western European targets and a broad global operational reach consistent with the continued expansion of ransomware-as-a-service (RaaS) activity.
Irreversible Encryption Failures Amplifying Destructive Impact:
The VECT 2.0 ransomware, attributed to a threat actor group (VECT operators), reflects a notable shift in ransomware behavior where operational flaws unintentionally drive destructive outcomes. Unlike traditional ransomware that preserves data integrity for monetization, VECT 2.0’s flawed nonce management causes irreversible corruption of large files, effectively turning it into a pseudo-wiper. This indicates an evolution toward high-speed, chunk-based encryption routines aimed at scalability across environments (Windows, Linux, ESXi), but with inadequate cryptographic implementation. Additionally, its affiliate-based distribution via BreachForums and alignment with threat group TeamPCP demonstrates convergence with supply-chain compromise strategies, expanding initial access vectors beyond conventional intrusion methods. The net effect is a transition from controlled encryption-for-ransom models to large-scale, potentially uncontrollable data destruction with ransomware-like delivery.
ETLM Assessment
If this trajectory continues, ransomware operations may increasingly blur into intentional hybrid wiper models, where data destruction is either a fallback or strategic objective. Threat actors could refine such mechanisms to selectively corrupt critical data (e.g., backups, hypervisors, databases) while maintaining partial decrypt ability to preserve extortion leverage. Integration with supply-chain compromises suggests future campaigns may weaponize trusted software ecosystems for mass ransomware deployment at scale. Additionally, actors may deliberately introduce “controlled irrecoverability” features that destroy key segments of data while still demanding a ransom to increase pressure and reduce reliance on decryption infrastructure. This also opens the possibility of ransomware being used as a disruption tool in geopolitical or sabotage-driven operations, rather than purely financially motivated attacks.
Advanced Cryptographic Experimentation in Multi-Platform Ransomware Campaigns
The Kyber ransomware operation, attributed to a threat actor (affiliate within the Kyber ransomware group), demonstrates a clear progression toward cryptographic diversification and cross-environment targeting. Unlike earlier ransomware relying solely on classical encryption (e.g., RSA), this campaign introduces post-quantum cryptography (Kyber1024), albeit selectively and inconsistently, indicating exploratory adoption rather than full operational reliance. The dual deployment across Windows and VMware ESXi environments highlights a mature, coordinated attack model aimed at simultaneous infrastructure-wide impact, including hypervisors and virtualized workloads. Additionally, the combination of Rust-based development, partial encryption strategies, and aggressive recovery inhibition (e.g., backup deletion, service termination) reflects an evolution toward resilient, high-efficiency ransomware frameworks that prioritize speed, stealth, and maximum disruption while experimenting with next-generation cryptographic primitives.
ETLM Assessment
This trajectory suggests ransomware actors may continue integrating post-quantum algorithms into hybrid encryption models, not for immediate necessity but to future-proof operations against cryptographic advancements. Expect more modular ransomware architectures where encryption methods can be swapped dynamically (RSA, ECC, Kyber, etc.) depending on target profile or operational goals. Cross-platform targeting will likely expand further into cloud-native, containerized, and hybrid virtualization environments, enabling full-spectrum infrastructure compromise. Additionally, actors may refine selective encryption and adaptive impact strategies, balancing encryption speed with targeted destruction of critical assets (e.g., hypervisors, backups) to maximize leverage. Over time, “post-quantum ransomware” could evolve from experimental marketing claims into standardized operational capability, especially as threat actors seek differentiation and psychological leverage in extortion campaigns.
Operational Scaling Through Botnet-Enabled Delivery and Post-Exploitation Integration
The Gentlemen ransomware, operated by a threat actor group (Gentlemen RaaS affiliates), illustrates a clear advancement toward industrialized ransomware operations through integration with botnet infrastructure and mature post-exploitation tooling. The adoption of SystemBC proxy malware, a SOCKS5-based botnet with over 1,570 infected corporate hosts, marks a transition from isolated intrusions to botnet-assisted, covert payload delivery at scale. This is complemented by the use of Cobalt Strike, Mimikatz, and domain-wide propagation via GPO, indicating a tightly coordinated, human-operated attack workflow with enterprise-level targeting. Additionally, the hybrid encryption model (X25519 + XChaCha20) combined with partial file encryption demonstrates optimization for speed and large-scale deployment, while multi-platform support (Windows, Linux, NAS, BSD, ESXi) reinforces a shift toward full infrastructure compromise rather than endpoint-centric attacks.
ETLM Assessment
This evolution suggests ransomware operations will increasingly adopt botnet-backed delivery ecosystems to decouple initial access from payload execution, enabling scalable and persistent attack pipelines. Future campaigns may further integrate modular post-exploitation frameworks, allowing affiliates to dynamically deploy tooling (e.g., credential harvesters, lateral movement kits, stealth proxies) based on target environments. The convergence of RaaS models with botnets also opens the path for Ransomware-as-an-Infrastructure (RaaI), where access, delivery, and execution layers are fully commoditized. Additionally, expect enhanced use of low-noise partial encryption and adaptive targeting of critical assets (e.g., domain controllers, hypervisors) to maximize operational impact while evading detection. Over time, such ecosystems could evolve into continuous access platforms, where compromised networks are monetized repeatedly beyond single ransomware events.
Virtualization-Backed Evasion and Covert Execution in Ransomware Operations
The Payouts King ransomware, associated with a threat actor group (GOLD ENCOUNTER, with links to former BlackBasta affiliates), demonstrates a clear advancement toward virtualization-based evasion and covert execution strategies. Rather than depending solely on obfuscation within the host system, the operators deploy QEMU-based virtual machines to run malicious payloads in isolated environments that remain largely invisible to host-level security monitoring. This reflects a shift toward execution abstraction, where malicious operations are conducted outside the primary operating system’s visibility. The campaign also exhibits maturity through diverse initial access methods (including VPN exploitation, social engineering via Microsoft Teams, and vulnerability abuse) and extensive post-compromise activity, such as credential extraction (e.g., NTDS.dit), Active Directory reconnaissance, and controlled data exfiltration. Combined with intermittent encryption techniques (AES-CTR + RSA-4096) and deliberate disabling of security controls, this approach underscores a transition toward stealth-focused, infrastructure-aware ransomware operations designed for enterprise-scale impact.
ETLM Assessment
This trajectory indicates ransomware actors will increasingly adopt virtualization and container-based evasion techniques, enabling payload execution in layers invisible to traditional EDR/XDR solutions. Future operations may expand into nested virtualization, cloud workloads, and container orchestration platforms (e.g., Kubernetes) to maintain persistence and evade detection across hybrid infrastructures. The combination of covert VM backdoors and reverse SSH tunneling suggests a move toward persistent, low-noise access channels, allowing attackers to re-enter environments even after partial remediation. Additionally, threat actors may standardize “bring-your-own-environment” attack kits, where fully preconfigured malicious VMs are deployed dynamically, reducing dependency on victim infrastructure. This evolution could ultimately lead to ransomware campaigns functioning as stealth intrusion platforms first, encryption events second, with prolonged dwell time and multi-stage monetization strategies.
Accelerated Exploit-Driven Intrusion and Rapid Ransomware Deployment
The Medusa ransomware activity, executed by the threat actor group Storm-1175, demonstrates a decisive shift toward exploit-centric, high-velocity intrusion models. Unlike traditional ransomware operations that rely on phishing or commodity access brokers, Storm-1175 systematically weaponizes n-day and zero-day vulnerabilities, in some cases exploiting flaws even before public patch release. This reflects an evolution toward vulnerability-driven initial access pipelines, where speed of exploitation becomes a competitive advantage. The group’s ability to chain multiple exploits across diverse enterprise software (e.g., email servers, MFT platforms, remote management tools) and transition from access to ransomware deployment within 24 hours highlights operational compression, minimizing dwell time while maximizing impact. Additionally, pre-encryption activities such as credential theft, persistence establishment, and security control disablement indicate a highly automated and repeatable attack lifecycle, aligning ransomware operations with advanced intrusion tradecraft.
ETLM Assessment
This trajectory suggests ransomware actors will increasingly integrate real-time vulnerability intelligence and exploit acquisition ecosystems (including exploit brokers) to sustain rapid intrusion capabilities. Future campaigns are likely to feature automated exploit chaining frameworks, enabling attackers to pivot across multiple exposed services in a single operation. The continued emphasis on zero-day or near-zero-day exploitation may also drive ransomware closer to APT-like operational sophistication, blurring the line between financially motivated and state-aligned activity. Additionally, sectors with exposed perimeter infrastructure (e.g., healthcare, finance, critical infrastructure) will remain prime targets due to patching latency. Over time, ransomware operations may evolve into “exploit-first ransomware pipelines”, where encryption is just the final monetization stage following rapid, vulnerability-led compromise and data exfiltration.
Escalating Coercion Models Driving Data-Centric Ransomware Impact
The evolution toward multi-extortion ransomware, driven by numerous threat actor groups (expanding ransomware ecosystem with 120+ active groups), marks a fundamental shift from encryption-only attacks to data-centric coercion strategies. Initially, ransomware relied on encrypting files for ransom; however, as organizations improved backup and recovery, attackers adapted by introducing double extortion, exfiltrating sensitive data prior to encryption. This progression has further escalated into triple extortion, where attackers directly pressure victims’ customers or partners to amplify reputational and regulatory damage. This model reflects a transition from technical disruption to business-level extortion, where the value lies not just in system access but in the sensitivity and exploitability of stolen data. The increasing number of ransomware groups and the accessibility of AI-driven tooling further indicate democratization and scaling of ransomware capabilities, lowering the barrier for new entrants while intensifying competition and innovation.
ETLM Assessment
Ransomware operations are likely to continue evolving toward multi-layered extortion ecosystems, potentially extending beyond triple extortion into continuous extortion models, where stolen data is monetized repeatedly over time (e.g., resale, fraud, secondary attacks). Threat actors may increasingly prioritize data classification and selective exfiltration, targeting high-impact datasets (healthcare, financial, intellectual property) to maximize leverage. Additionally, the integration of AI-driven reconnaissance and automation could enable faster identification of valuable data and more personalized extortion tactics. As defenses improve, attackers may shift further toward pre-encryption monetization, where data theft alone becomes sufficient for extortion, reducing reliance on encryption altogether. This trajectory reinforces ransomware’s transformation into a data exploitation economy, where operational disruption is secondary to sustained coercion and monetization of sensitive information.
Mass Exploitation of Hosting Infrastructure Driving Opportunistic Ransomware Campaigns
The “Sorry” ransomware campaign, operated by an unattributed threat actor, highlights a shift toward large-scale, vulnerability-driven ransomware propagation targeting shared infrastructure platforms. By exploiting the critical cPanel/WHM authentication bypass (CVE-2026-41940) as a zero-day, attackers rapidly compromised tens of thousands of internet-facing servers (≈44,000 IPs), demonstrating a move from targeted intrusions to broad, automated exploitation of widely deployed administrative platforms. This campaign reflects an evolution where ransomware operators prioritize internet-exposed management layers (e.g., hosting panels) to achieve immediate, high-volume access. The use of a lightweight Linux-based encryptor (ChaCha20 + RSA-2048) and standardized ransom workflows further indicates automation and commoditization, enabling rapid deployment across compromised environments with minimal operational friction.
ETLM Assessment
This pattern suggests ransomware actors will increasingly focus on mass exploitation of critical edge and management-layer vulnerabilities (e.g., hosting panels, VPNs, remote access tools) to achieve rapid scale. Future campaigns are likely to incorporate automated scanning-to-exploitation pipelines, enabling near-instant weaponization of newly disclosed flaws. Additionally, attackers may expand toward multi-tenant environments (shared hosting, SaaS backends, cloud control planes) to maximize impact per compromise. The continued reliance on standardized encryption and ransom delivery mechanisms indicates a trajectory toward fully automated ransomware outbreaks, where human involvement is limited to initial exploit development and ransom negotiation. Over time, this could evolve into “ransomware worms” targeting exposed infrastructure, significantly increasing the speed and scale of global ransomware incidents.
Based on available public reports, approximately 31% of enterprises are compelled to halt their operations, either temporarily or permanently, in the aftermath of a ransomware onslaught. The ripple effects extend beyond operational disruptions, as detailed by additional metrics:
Impact Assessment
Ransomware remains a major threat to both organizations and individuals, locking critical data and demanding payment for its release. The consequences extend well beyond the ransom, often leading to costly recovery efforts, extended downtime, reputational harm, and potential regulatory fines. Such disruptions can destabilize operations and erode stakeholder trust. Addressing this growing risk demands a proactive cybersecurity posture and stronger collaboration between public and private sectors to build resilience against future attacks.
Victimology
Cybercriminals are increasingly targeting industries that manage vast amounts of sensitive data, ranging from personal and financial information to proprietary assets. Sectors such as manufacturing, real estate, healthcare, FMCG, e-commerce, finance, and technology remain high on the threat radar due to their complex and extensive digital infrastructures. Adversaries strategically exploit vulnerabilities in economically advanced regions, launching well-planned attacks designed to encrypt critical systems and extract significant ransom payments. These operations are calculated to yield maximum financial returns.
Ransomware entering 2026 is no longer a discrete cyber incident but an enduring, multi-stage business threat that blends elements of cybercrime, espionage tradecraft, and economic coercion. The continued separation of access, execution, and extortion, combined with browser-based trust abuse, engineered delivery artifacts, and long-lived access infrastructure, has significantly eroded the effectiveness of exploit-centric and signature-driven defenses. At the same time, the scale and complexity of affiliate-driven operations introduce inherent fragility, creating opportunities for disruption beyond traditional endpoint containment, particularly at the levels of access brokerage, backend infrastructure, and coordination workflows. For organizations, resilience in this environment will depend less on preventing individual intrusions and more on governance readiness, third-party risk management, user interaction telemetry, and executive decision preparedness. As ransomware groups continue to evolve toward stealth, optionality, and psychological leverage, proactive external threat landscape management and cross-functional response planning will be critical to reducing both operational impact and long-term business risk.