


CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple industries, geography, and technology that could be relevant to your organization.
Type:
Ransomware
Target Technology:
Windows
Targeted Industries:
Consumer Goods & Services, Professional Goods & Services, Energy & Utilities, Education, Materials, Real Estate & Construction, Telecommunications & Media, Manufacturing
Targeted Countries:
Japan, Austria, Brazil, Botswana, Hong Kong, Spain, South Africa, Romania, New Zealand, Turkey, Thailand, Germany, USA
Introduction
CYFIRMA Research and Advisory Team has found KRYBIT ransomware while monitoring various underground forums as part of our Threat Discovery Process.
KRYBIT Ransomware
KRYBIT is a ransomware strain that encrypts files on a compromised system and appends the “.KRYBIT” extension to each affected file (e.g., “1.jpg” becomes “1.jpg.KRYBIT”). It also drops a ransom note named “RECOVER-README.txt.” The malware includes a data exfiltration component, with operators claiming to have extracted sensitive data before encryption. The activity involves multiple Tor-based onion domains running on Apache with PHP 8.0.30. Observed cases include at least 20 victims across sectors such as consumer services, business services, education, technology, and manufacturing, with incidents reported in Germany, Mexico, Turkiye, Japan, and Austria.
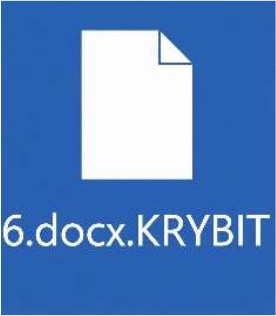
Screenshot: File encrypted by the ransomware (Source: Surface Web)
The ransom note states that the victim’s system or network has been encrypted and that files are only recoverable using the attackers’ decryption tools and cipher key. It claims exfiltration of sensitive data, including employee personal data, credentials, financial records, and technical design files, and threatens public disclosure if negotiations fail. The note warns against modifying encrypted files or using third-party recovery tools, asserting that such actions may render decryption impossible. Victims are instructed to download the Tor Browser and access a specified onion-based chat portal using a unique ID to initiate communication and recovery procedures.
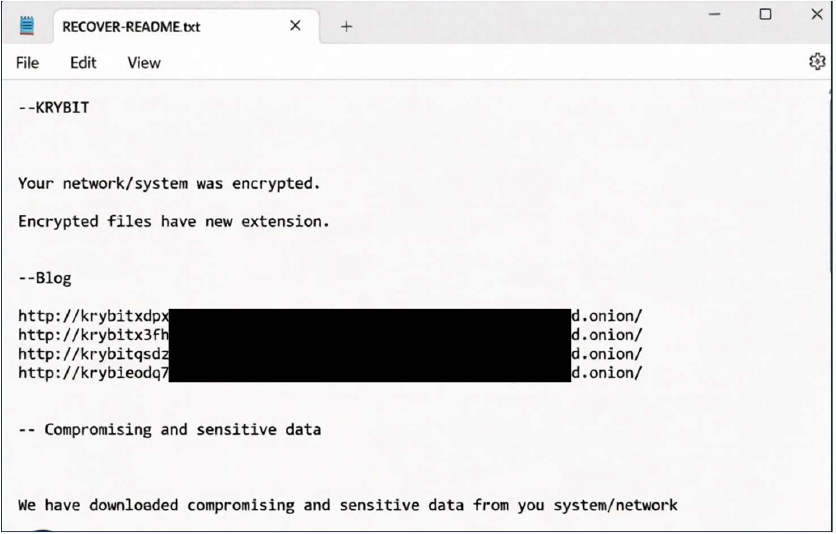
The appearance of the KRYBIT ransom note (“RECOVER-README.txt”) (Source: Surface Web)
The group maintains a data leak site accessible via Tor, supporting a double-extortion model that combines encryption with the threat of data publication. Operational metrics show recent discovery dates (first observed on 2026-04-03 and last on 2026-04-27), a short inactivity gap, and an average delay of 2.7 days between compromise and observed activity. No infostealer component has been identified in associated victim domains.
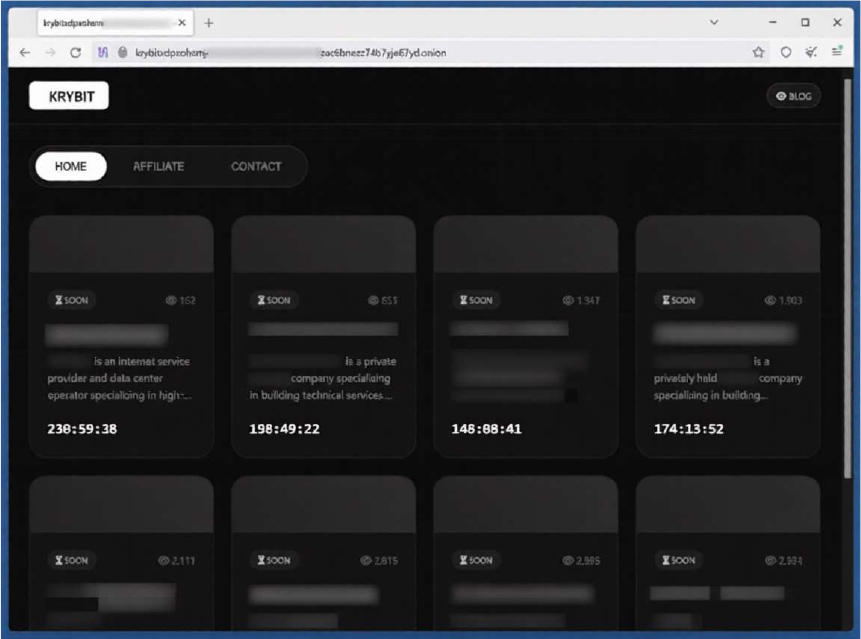
The appearance of the KRYBIT Data Leak Site (Source: Surface Web)
The following are the TTPs based on the MITRE Attack Framework
| Tactic | Technique ID | Technique Name |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1129 | Shared Modules |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1055 | Process Injection |
| Privilege Escalation | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1548 | Abuse Elevation Control Mechanism |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1027.005 | Obfuscated Files or Information: Indicator Removal from Tools |
| Defense Evasion | T1036 | Masquerading |
| Defense Evasion | T1055 | Process Injection |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1202 | Indirect Command Execution |
| Defense Evasion | T1222 | File and Directory Permissions Modification |
| Defense Evasion | T1548 | Abuse Elevation Control Mechanism |
| Defense Evasion | T1564.003 | Hide Artifacts: Hidden Window |
| Credential Access | T1003 | OS Credential Dumping |
| Credential Access | T1552.001 | Unsecured Credentials: Credentials In Files |
| Discovery | T1007 | System Service Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1135 | Network Share Discovery |
| Discovery | T1518 | Software Discovery |
| Collection | T1005 | Data from Local System |
| Collection | T1074 | Data Staged |
| Collection | T1114 | Email Collection |
| Command and Control | T1071 | Application Layer Protocol |
| Command and Control | T1090 | Proxy |
| Impact | T1486 | Data Encrypted for Impact |
| Impact | T1489 | Service Stop |
| Impact | T1490 | Inhibit System Recovery |
Relevancy and Insights:
ETLM Assessment:
CYFIRMA’s analysis indicates that KRYBIT operates as a structured double-extortion ransomware, combining file encryption with prior data exfiltration to maximize impact on victims. The ransomware employs techniques such as shadow copy deletion to inhibit recovery, process injection for execution, and abuse of legitimate system utilities to evade detection. It further demonstrates capabilities aligned with credential access, system and network discovery, and data staging, indicating a well-defined multi-stage attack lifecycle. The use of Tor-based infrastructure and embedded onion domains enables anonymized communication, negotiation, and potential data leak operations, reinforcing its operational maturity.
From a tactical perspective, KRYBIT shows strong alignment with common ransomware methodologies, including defense evasion through obfuscation, masquerading, and manipulation of system processes and registry keys. Its ability to terminate processes, interact with backup-related services, and modify system configurations highlights a focus on weakening system defenses prior to encryption. The inclusion of discovery and collection techniques suggests that attackers perform internal reconnaissance and identify high-value data before executing the encryption phase, further supporting its double-extortion approach.
Going forward, the ransomware is likely to evolve with more sophisticated evasion strategies, including enhanced obfuscation layers and deeper integration with legitimate administrative tools to bypass security controls. It may adopt increased automation in lateral movement and data exfiltration, allowing faster compromise of larger environments. Additionally, expansion to target a broader range of platforms and environments, along with continued reliance on anonymized infrastructure and leak sites, can be expected to strengthen its operational efficiency and extortion capabilities.
Sigma rule:
title: Shadow Copies Deletion Using Operating Systems Utilities description: Shadow Copies deletion using operating systems utilities tags:
– attack.defense-evasion
– attack.impact
– attack.t1070
– attack.t1490 logsource:
category: process_creation product: windows
detection: selection1_img:
– Image|endswith:
– ‘\powershell.exe’
– ‘\pwsh.exe’
– ‘\wmic.exe’
– ‘\vssadmin.exe’
– ‘\diskshadow.exe’
– OriginalFileName:
– ‘PowerShell.EXE’
– ‘pwsh.dll’
– ‘wmic.exe’
– ‘VSSADMIN.EXE’
– ‘diskshadow.exe’ selection1_cli:
CommandLine|contains|all:
– ‘shadow’ # will match “delete shadows” and “shadowcopy delete” and “shadowstorage”
– ‘delete’ selection2_img:
– Image|endswith: ‘\wbadmin.exe’
– OriginalFileName: ‘WBADMIN.EXE’ selection2_cli:
CommandLine|contains|all:
– ‘delete’
– ‘catalog’
– ‘quiet’ # will match -quiet or /quiet selection3_img:
– Image|endswith: ‘\vssadmin.exe’
– OriginalFileName: ‘VSSADMIN.EXE’ selection3_cli:
CommandLine|contains|all:
– ‘resize’
– ‘shadowstorage’ CommandLine|contains:
– ‘unbounded’
– ‘/MaxSize=’
condition: (all of selection1*) or (all of selection2*) or (all of selection3*) falsepositives:
– Legitimate Administrator deletes Shadow Copies using operating systems utilities for legitimate reason
– LANDesk LDClient Ivanti-PSModule (PS EncodedCommand) level: high
(Source: Surface Web)
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
Type: RMM-based Backdoor| Objectives: Administration | Target Technology: Windows OS | Target Geography: Global
CYFIRMA collects data from various forums based on which the trend is ascertained. We identified a few popular malwares that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week, “DattoRMM” is in focus.
Overview of Operation DattoRMM
DattoRMM is a legitimate remote monitoring and management (RMM) solution. While such tools are commonly utilized by organizations for administrative oversight and remote system management, they are increasingly being exploited by threat actors to facilitate unauthorized access and persistence. In this instance, several indicators suggest that the tool may not have been deployed through standard or authorized channels.
Behavioral analysis reveals that the program performs extensive system-level operations, including configuration changes, service creation, and persistence mechanisms. Although these actions are consistent with legitimate RMM functionality, they can also be indicative of misuse when observed outside a controlled administrative context. Furthermore, the program establishes communication with external infrastructure and exhibits signs of defense evasion, which heightens concerns regarding potential unauthorized activity.
In conclusion, while DattoRMM is not inherently malicious, its presence in this scenario reflects the risks associated with dual-use tools. Unauthorized or unmonitored deployment can enable adversaries to maintain access, conduct surveillance, and manipulate systems. Organizations are therefore advised to validate the legitimacy of such installations, enforce strict access controls, and continuously monitor anomalous behavior to mitigate potential security risks.
Attack Method
The attack is initiated through the execution of a suspicious Windows-based executable that activates multiple system-level processes while leveraging legitimate system utilities to operate inconspicuously. In its initial stage, the malware utilizes trusted components such as regsvr32.exe and Windows Management Instrumentation (WMI) to facilitate code execution in a manner that reduces the likelihood of detection. It subsequently unpacks and deploys additional components into system directories, establishing a foundation for continued malicious activity.
To establish persistence, the malware performs critical modifications within the system, including the creation of services and alterations to registry keys that enable automatic execution during system startup. It further adjusts firewall configurations using command-line utilities such as netsh.exe, allowing its own communications while potentially weakening existing security controls. These combined actions ensure that the malicious presence is maintained across system restarts and remains resilient against basic remediation efforts.
The attack also incorporates advanced defense evasion and privilege escalation techniques. By injecting malicious code into legitimate processes, the malware conceals its activity within normal system operations, thereby reducing the chances of detection by security solutions. In addition, it employs obfuscation and anti-analysis mechanisms, including delayed execution and sandbox awareness, to evade automated detection systems and hinder detailed examination.
Following successful establishment, the malware initiates communication with external command-and-control infrastructure through encrypted channels, often using standard application-layer protocols. This enables remote command execution and controlled data exchange. Concurrently, the malware conducts system reconnaissance and collects sensitive information, such as clipboard data and session-related artifacts, and may deploy additional payloads, reflecting a structured and adaptable approach aimed at sustaining long-term unauthorized access and control.
The following are the TTPs based on the MITRE Attack Framework for Enterprise
| Tactic | Technique ID | Technique Name |
| Execution (TA0002) | T1047 | Windows Management Instrumentation |
| T1053 | Scheduled Task/Job | |
| T1059 | Command and Scripting Interpreter | |
| T1106 | Native API | |
| T1129 | Shared Modules | |
| Persistence (TA0003) | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| T1112 | Modify Registry | |
| Privilege Escalation (TA0004) | T1055 | Process Injection |
| Defense Evasion (TA0005) | T1027.002 | Obfuscated Files or Information: Software Packing |
| T1070 | Indicator Removal | |
| T1140 | Deobfuscate/Decode Files or Information | |
| T1202 | Indirect Command Execution | |
| T1222 | File and Directory Permissions Modification | |
| T1497 | Virtualization/Sandbox Evasion | |
| T1553.003 | Subvert Trust Controls: SIP and Trust Provider Hijacking | |
| T1562 | Impair Defenses | |
| T1564 | Hide Artifacts | |
| Credential Access (TA0006) | T1539 | Steal Web Session Cookie |
| Discovery (TA0007) | T1010 | Application Window Discovery |
| T1012 | Query Registry | |
| T1057 | Process Discovery | |
| T1082 | System Information Discovery | |
| T1083 | File and Directory Discovery | |
| T1518 | Software Discovery | |
| T1115 | Clipboard Data | |
| Collection (TA0009) | T1125 | Video Capture |
| Command and Control (TA0011) | T1071 | Application Layer Protocol |
| T1573 | Encrypted Channel | |
| Impact (TA0040) | T1485 | Data Destruction |
| T1486 | Data Encrypted for Impact | |
| T1529 | System Shutdown/Reboot |
INSIGHTS
ETLM ASSESSMENT
From an ETLM perspective, the continued misuse of legitimate tools such as DattoRMM is expected to reshape how organizations approach internal security and operational trust in the future. At the executive level, there may be increasing concern around governance and visibility, as traditional indicators of compromise become less reliable when adversaries leverage approved software. From a tactical standpoint, operational teams could face growing difficulty in distinguishing between authorized administrative actions and covert misuse, leading to more complex monitoring and validation processes. At the leadership and management level, this evolution may influence how employee access, accountability, and oversight are structured, as the risk of undetected activity within trusted environments becomes more pronounced, potentially impacting both organizational resilience and workforce confidence.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems.
YARA Rules
rule DattoRMM_String_IOCs
{
meta:
description = “Detects DattoRMM-related sample using string-based IOCs (hash artifacts)”
author = “CYFIRMA” date = “2026-04-27”
strings:
/* Malware Sample Hash artifacts as strings */
$hash_md5 = “b9500f72e9ad39d9efc0b5152e2807e0”
$hash_sha1 = “caa8e68e2cf9e7d23b371074cacf65f1a3a342c5”
$hash_sha256 = “95f0297e9e3b9401cf2b803daae9e6e934779d5b7cebdcdf2d07f1884893096b”
condition:
any of ($hash_*)
}
Strategic Recommendations
These are high-level, long-term initiatives to strengthen organizational cybersecurity posture:
Management Recommendations
These focus on policies, procedures, and governance to ensure proper oversight and risk mitigation:
Tactical Recommendations
These are immediate, actionable steps to prevent, detect, and respond to malware at the operational level:
Key Intelligence Signals:
UNC6692: Emerging Social Engineering–Driven Threat Actor Profile
About the Threat Actor
UNC6692 is a newly identified threat cluster that has emerged for its use of advanced social engineering techniques via Microsoft Teams, alongside a custom malware ecosystem referred to as SNOW. Active since late December 2025, the group has conducted large-scale email flooding campaigns designed to overwhelm targets with excessive messages, creating confusion and urgency to enable follow-on malicious activities.
TTPs based on MITRE ATT&CK Framework
| Tactic | ID | Technique |
| Resource Development | T1608.002 | Stage Capabilities: Upload Tool |
| Resource Development | T1608.005 | Stage Capabilities: Link Target |
| Initial Access | T1566.002 | Phishing: Spear phishing Link |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
| Execution | T1053 | Scheduled Task/Job |
| Execution | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Execution | T1559 | Inter-Process Communication |
| Execution | T1204.001 | User Execution: Malicious Link |
| Execution | T1204.002 | User Execution: Malicious File |
| Execution | T1559.002 | Inter-Process Communication: Dynamic Data Exchange |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1059.003 | Command and Scripting Interpreter: Windows Command Shell |
| Execution | T1059.006 | Command and Scripting Interpreter: Python |
| Execution | T1059.007 | Command and Scripting Interpreter: JavaScript |
| Execution | T1059.010 | Command and Scripting Interpreter: AutoHotKey & AutoIT |
| Persistence | T1176.001 | Software Extensions: Browser Extensions |
| Persistence | T1053 | Scheduled Task/Job |
| Persistence | T1112 | Modify Registry |
| Persistence | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Persistence | T1543 | Create or Modify System Process |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Persistence | T1547.009 | Boot or Logon Autostart Execution: Shortcut Modification |
| Privilege Escalation | T1068 | Exploitation for Privilege Escalation |
| Privilege Escalation | T1053 | Scheduled Task/Job |
| Privilege Escalation | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Privilege Escalation | T1543 | Create or Modify System Process |
| Privilege Escalation | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1547.009 | Boot or Logon Autostart Execution: Shortcut Modification |
| Privilege Escalation | T1134 | Access Token Manipulation: Create Process with Token |
| Privilege Escalation | T1134.001 | Access Token Manipulation: Token Impersonation/Theft |
| Privilege Escalation | T1055 | Process Injection |
| Defense Evasion | T1134 | Access Token Manipulation: Create Process with Token |
| Defense Evasion | T1134.001 | Access Token Manipulation: Token Impersonation/Theft |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1112 | Modify Registry |
| Defense Evasion | T1202 | Indirect Command Execution |
| Defense Evasion | T1036.005 | Masquerading: Match Legitimate Resource Name or Location |
| Defense Evasion | T1622 | Debugger Evasion |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1027.010 | Obfuscated Files or Information: Command Obfuscation |
| Defense Evasion | T1027.015 | Obfuscated Files or Information: Compression |
| Defense Evasion | T1055 | Process Injection |
| Defense Evasion | T1140 | Deobfuscate/Decode Files or Information |
| Defense Evasion | T1564.001 | Hide Artifacts: Hidden Files and Directories |
| Defense Evasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| Credential Access | T1003.001 | OS Credential Dumping: LSASS Memory |
| Credential Access | T1003.002 | OS Credential Dumping: Security Account Manager |
| Credential Access | T1003.003 | OS Credential Dumping: NTDS |
| Credential Access | T1110.003 | Brute Force: Password Spraying |
| Credential Access | T1110.001 | Brute Force: Password Guessing |
| Credential Access | T1552.001 | Unsecured Credentials: Credentials In Files |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1007 | System Service Discovery |
| Discovery | T1018 | Remote System Discovery |
| Discovery | T1087.001 | Account Discovery: Local Account |
| Discovery | T1518 | Software Discovery |
| Discovery | T1046 | Network Service Discovery |
| Discovery | T1622 | Debugger Evasion |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1012 | Query Registry |
| Discovery | T1016 | System Network Configuration Discovery |
| Discovery | T1033 | System Owner/User Discovery |
| Lateral Movement | T1021.002 | Remote Services: SMB/Windows Admin Shares |
| Lateral Movement | T1021.001 | Remote Services: Remote Desktop Protocol |
| Collection | T1560 | Archive Collected Data |
| Collection | T1560.001 | Archive Collected Data: Archive via Utility |
| Collection | T1113 | Screen Capture |
| Collection | T1005 | Data from Local System |
| Collection | T1074 | Data Staged |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and Control | T1090 | Proxy |
| Command and Control | T1105 | Ingress Tool Transfer |
| Command and Control | T1572 | Protocol Tunneling |
| Exfiltration | T1020 | Automated Exfiltration |
| Exfiltration | T1567.002 | Exfiltration Over Web Service: Exfiltration to Cloud Storage |
| Exfiltration | T1567 | Exfiltration Over Web Service |
| Impact | T1489 | Service Stop |
Latest Developments Observed
The threat actor is suspected of impersonating IT helpdesk personnel and persuading victims to accept Microsoft Teams chat invitations originating from accounts outside their organization. The objective of these interactions is to gain unauthorized access, deploy custom malware, and exfiltrate sensitive information from targeted environments.
ETLM Insights
UNC6692 is a newly identified threat cluster characterized by social engineering- driven intrusion operations aimed at obtaining initial access through the manipulation of trust rather than direct technical exploitation. The group’s activities indicate a strong focus on credential theft and unauthorized access to enterprise environments, likely supporting follow-on objectives such as intelligence gathering and data exfiltration.
Operationally, the threat actor demonstrates a structured intrusion methodology that exploits trust relationships within enterprise communication and collaboration ecosystems. The threat actor leverages interaction-based access vectors embedded within routine business workflows, allowing malicious activity to blend into legitimate organizational communications while reducing dependence on exploiting technical vulnerabilities. This approach enables scalable access operations and increases the likelihood of persistence through identity-based compromise across interconnected enterprise environments.
Based on the observed behavioral patterns and tradecraft, the threat actor is expected to continue refining its trust-centric intrusion techniques and further exploit legitimate communication channels to sustain unauthorized access. This evolving operational model positions the group as a significant threat to organizations operating within distributed and cloud-connected digital ecosystems, where identity compromise can lead to broader operational, security, and data exposure risks.
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
YARA Rules
rule UNC6692_SNOW_Ecosystem_Consolidated
{
meta:
author = “CYFIRMA” threat_actor = “UNC6692”
description = “Consolidated detection for UNC6692 SNOW ecosystem based on SNOWBELT, SNOWGLAZE, and SNOWBASIN behavior”
confidence = “medium-high” strings:
// SNOWBELT (Browser extension backdoor behavior + control logic)
$b1 = “sendJsonDataToS3”
$b2 = “AES-GCM”
$b3 = “chrome.runtime.connectNative”
$b4 = “chrome.downloads.onChanged”
$b5 = “websocket_control”
$b6 = “payload”
$b7 = “screenshot”
$b8 = “delete_cache”
// SNOWGLAZE (WebSocket tunneling + SOCKS proxy behavior)
$g1 = “socks_connect”
$g2 = “socks_data”
$g3 = “conn_id”
$g4 = “agent_info”
$g5 = “register”
$g6 = “WebSocket”
$g7 = “ping”
$g8 = “disconnect”
// SNOWBASIN (Local HTTP backdoor endpoints)
$s1 = “/stream”
$s2 = “/buffer”
$s3 = “/flush”
$s4 = “/commit”
$s5 = “/capture”
$s6 = “/gc”
$s7 = “serve_forever”
$s8 = “cmd.exe”
$s9 = “powershell.exe” condition:
(
6 of ($b*) and 5 of ($g*) and 5 of ($s*)
)
}
Strategic Recommendations
Management Recommendations
Tactical Recommendations
Chinese hackers target Indian banks and the Mongolian government
Researchers have published a report on a newly discovered Chinese APT, which they’re tracking as “GopherWhisper”, that’s targeting Mongolian government entities. The threat actor uses malware written in Go and abuses Discord, Slack, Microsoft 365 Outlook, and file.io for command-and-control communication and data exfiltration. The researchers managed to extract thousands of C&C messages from these services, providing deep insight into the group’s operations. They noted: “We discovered the group in January 2025, when we found a previously undocumented backdoor, which we named LaxGopher, on the system of a governmental entity in Mongolia. Digging deeper, we managed to uncover several more malicious tools, mainly various backdoors, all deployed by the same group.”
Meanwhile, another research team has published a report on a new variant of the LOTUSLITE backdoor that’s being deployed in espionage-focused attacks against India’s banking sector. The researchers attribute the campaign to the Chinese APT “Mustang Panda” based on code overlaps and shared TTPs. The campaign reflects a shift in delivery tradecraft of Mustang Panda’s cluster delivering LOTUSLITE, which is moving from CHM-based delivery to JavaScript loaders to DLL sideloading across recent operations, while also pivoting geographically from U.S. government entities to India’s financial sector.
ETLM Assessment:
The Chinese hackers behind GopherWhisper are focused on espionage against Mongolian government entities. Their goal is to gain persistent access to government networks in order to steal sensitive political, diplomatic, and strategic information. As a close neighbor to China, Mongolia is of significant interest for monitoring internal policies, foreign relations, border issues, and any developments that could affect regional stability or China’s broader interests in the area. The malware and command- and-control techniques used are designed for long-term stealthy data collection rather than immediate disruption or financial gain.
In the second campaign, the Mustang Panda group is targeting India’s banking sector with a new variant of the LOTUSLITE backdoor as part of espionage operations. Here, the primary objective appears to be gathering economic intelligence, including insights into financial policies, banking operations, regulatory matters, and potentially high-value transactional or client data. This reflects a shift toward collecting information on India’s economic landscape and financial stability, alongside their ongoing interest in geopolitical intelligence. The campaign shows the group adapting their delivery methods while pivoting from previous government targets to the financial sector for strategic advantage.
Unauthorized users access Anthropic’s Mythos model
A small group of unauthorized users gained access to Anthropic’s Mythos AI model, which had been restricted to a limited set of vetted partners because of its capability to discover new software vulnerabilities. According to an anonymous source, several users in a private online forum obtained access to Mythos on the same day the company announced its plans for the model two weeks ago, and they have been using it regularly ever since. The users relied on a combination of tactics to breach the system. These included leveraging legitimate access held by an individual working at a third-party contractor for Anthropic, as well as employing common internet sleuthing tools frequently used by cybersecurity researchers. The group operates within a private Discord channel dedicated to hunting for information about unreleased AI models, including the use of bots to scan for details that companies have inadvertently posted on unsecured platforms such as GitHub.
ETLM Assessment:
It is unlikely that this unauthorized access to Anthropic’s Mythos AI model is tied to a nation-state actor. The incident appears to stem from relatively low-sophistication methods used by a small group of AI enthusiasts operating in a private Discord channel. They gained entry mainly through one member’s legitimate access as a contractor at a third-party vendor, combined with basic internet sleuthing—such as guessing the model’s deployment URL based on patterns from past Anthropic models and information leaked in an earlier breach at another AI startup. This is more characteristic of curious hobbyists or opportunistic researchers hunting for unreleased AI models than a coordinated state-backed operation.
That being said, North Korean hacking groups such as Lazarus have a well- documented history of compromising third-party contractors, stealing legitimate credentials, and blending into online communities to target high-value AI technologies, precisely because Mythos was deliberately delayed from public release and restricted to only a handful of vetted partners. The delay stemmed directly from Anthropic’s security concerns over the model’s unprecedented ability to autonomously discover new software vulnerabilities, capabilities that could be weaponized for offensive cyber operations, zero-day exploitation, or large-scale attacks—exactly the kind of strategic advantage Pyongyang’s cyber program actively seeks to offset its conventional military weaknesses and generate revenue through stolen intellectual property. By infiltrating via a contractor’s access and using low-profile sleuthing tools, the group could harvest this powerful offensive tool without triggering the alarms that a more overt nation-state breach would raise, turning what looked like hobbyist curiosity into a sophisticated intelligence haul.
Germany Accuses Russia of Cyberattack on Top Officials
Germany suspects Russia is behind a cyberattack that targeted senior government officials in Berlin through the Signal messaging app, according to the German government. Those affected by the phishing campaign have been notified, and the data leak from their compromised devices has been contained. However, authorities cannot rule out that additional individuals may also have been impacted. The official spoke on condition of anonymity in line with government protocol. Two cabinet members were among those targeted. Germany considers Russia the biggest threat to its national security and has accused Moscow of conducting hybrid warfare, including covert cyberattacks on critical infrastructure and disinformation operations aimed at deepening social divisions.
ETLM Assessment:
Russia is conducting an extensive hybrid warfare campaign against Germany, blending cyberattacks, sabotage, espionage, and disinformation to undermine national security, sow social divisions, and weaken support for Ukraine and NATO. Berlin has attributed multiple incidents to Russian military intelligence (GRU), including the 2024 cyberattack on German air traffic control by the APT28 (Fancy Bear) group, widespread router compromises, and disinformation operations such as the “Storm- 1516” campaign that spread deepfakes and false election-fraud narratives ahead of German elections. In 2025 alone, German authorities recorded over 300 suspected sabotage attempts, including drone incursions near airports and military sites, arson and vandalism against defense industry facilities, and interference with critical infrastructure like railways and undersea cables. These actions, often carried out through proxies, criminal networks, or cutouts for plausible deniability, aim to disrupt Germany’s role as a key NATO hub, erode public confidence in democratic institutions, and prepare the ground for potential larger-scale confrontation, prompting Germany to label Russia its greatest immediate threat to peace and security.
INC Ransomware Impacts Aluminium Products Company (ALUPCO)
Summary:
CYFIRMA observed in an underground forum that a company from Saudi Arabia, Aluminium Products Company (ALUPCO) (https[:]//alupco[.]com/), was compromised by INC Ransomware. ALUPCO is the Middle East’s largest aluminium extruder, established in 1975, offering a diverse range of high-quality extruded profiles and comprehensive building solutions. The company specializes in project management, architectural solutions, and modular buildings, catering to clients across various sectors. With a commitment to sustainability and performance, ALUPCO aims to enhance efficiency in the building journey from start to finish. Their extensive operations span multiple countries, serving a wide array of customers globally. The compromised dataset includes contact information, confidential documents, financial records, customer data, incident reports, and human resources (HR) information.
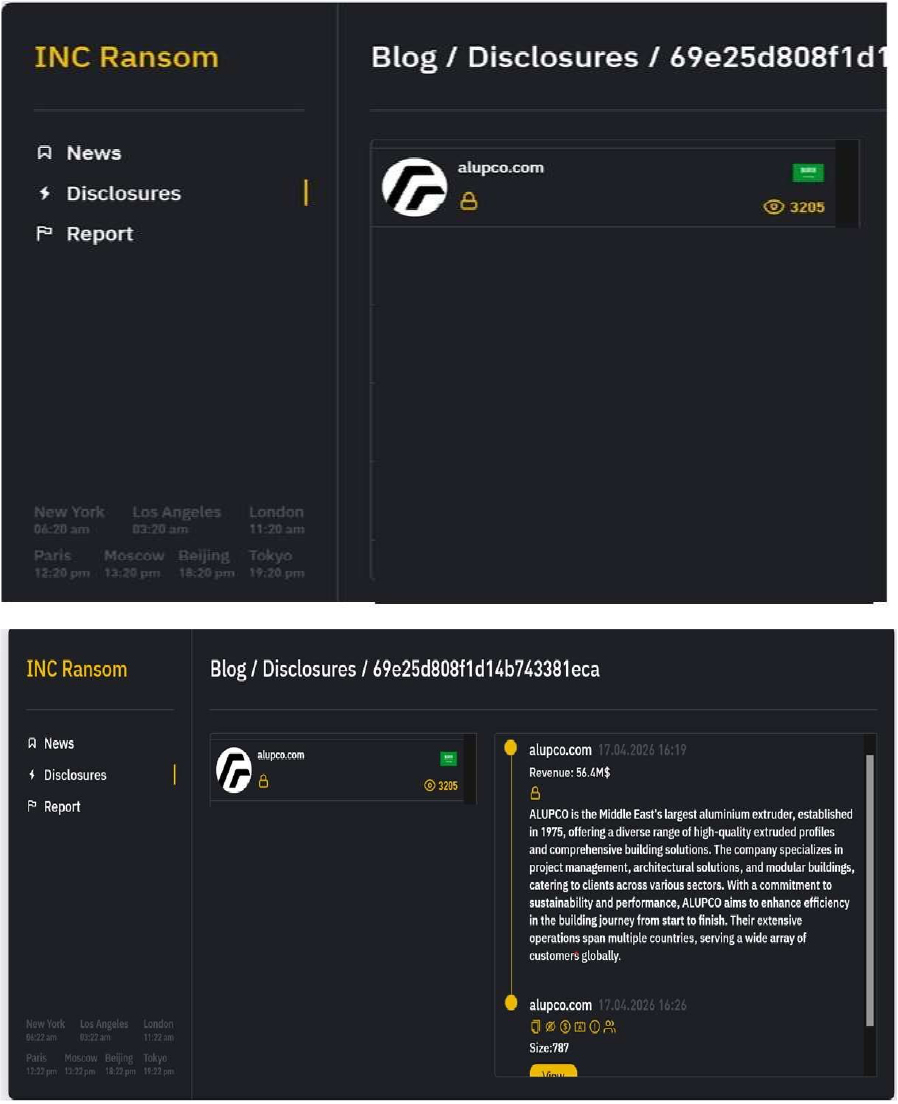
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
Based on recent assessments by CYFIRMA, INC Ransomware represents a significant threat within the evolving landscape of ransomware attacks. Its use of strong encryption methods and double extortion tactics highlights the increasing sophistication of cybercriminal operations. Organizations are advised to enhance their cybersecurity measures by implementing robust defenses against phishing attacks, maintaining updated security protocols, and monitoring for unusual network activity to mitigate risks associated with this and other ransomware variants. Continuous vigilance is essential to protect against the threats posed by emerging ransomware groups like INC Ransomware.
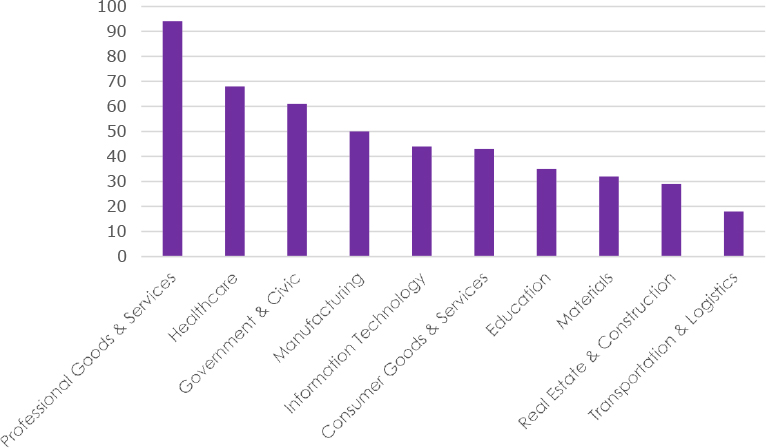
RansomExx Ransomware Impacts SOGO Auction
Summary:
CYFIRMA observed in an underground forum that a company from Japan, SOGO Auction(https[:]//sogocorporation[.]com/), was compromised by RansomExx Ransomware. SOGO Auction is a prominent Japan-based, specialized auctioneer with over 30 years of experience in trading used construction machinery and heavy equipment. Operating since the 1990s, they provide both on-site and online, high- volume auctions for items like excavators and bulldozers. It is operated by SOGO Corporation. The ransomware disclosure indicates that the compromised data includes a structured customer database (“customer_list”) containing extensive personal and contact information. This likely involves full names, addresses (multiple address fields), country, ZIP codes, and company details, along with phone numbers (telephone, fax, and mobile), email addresses, and IP-related data. Additionally, the dataset appears to store account-related fields, such as passwords, tokens, and language preferences, as well as timestamps (creation/update dates) and internal flags. The total size of the compromised data is approximately 951 MB.
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, Ransomexx ransomware represents a highly targeted and enterprise-focused threat that leverages human-operated intrusion techniques to maximize impact. The group conducts carefully planned attacks by gaining initial access through exposed services or compromised credentials, followed by privilege escalation, lateral movement, and selective deployment of ransomware across critical systems. Ransomexx demonstrates strong capabilities in defense evasion, including disabling security tools and backups prior to encryption, and supports cross-platform operations affecting both Windows and Linux environments. Its focus on high-value organizations, particularly within government and critical infrastructure sectors, combined with its strategic, low-noise operational approach, makes it a significant risk to enterprise cybersecurity, especially for organizations lacking robust monitoring, segmentation, and incident response capabilities.
Vulnerability in NanoMQ
Relevancy & Insights:
The vulnerability exists due to a boundary error in the uri_param_parse function.
Impact: A remote attacker can pass specially crafted data to the application, trigger a heap-based buffer overflow and execute arbitrary code on the target system.
Successful exploitation of this vulnerability may result in complete compromise of vulnerable system.
Affected Products:
https[:]//github[.]com/nanomq/nanomq/security/advisories/GHSA-6w96-9qw7- m599/#poc
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
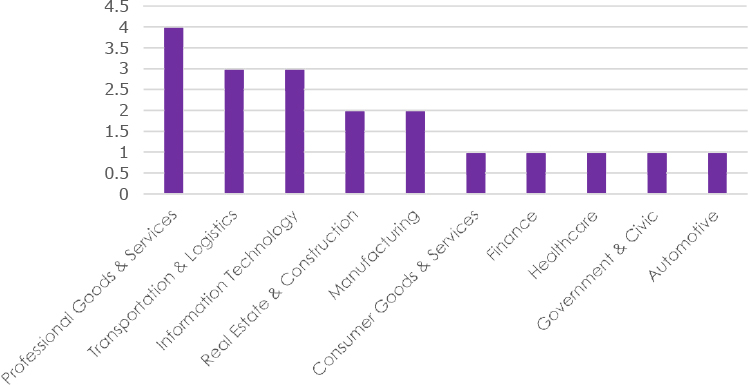
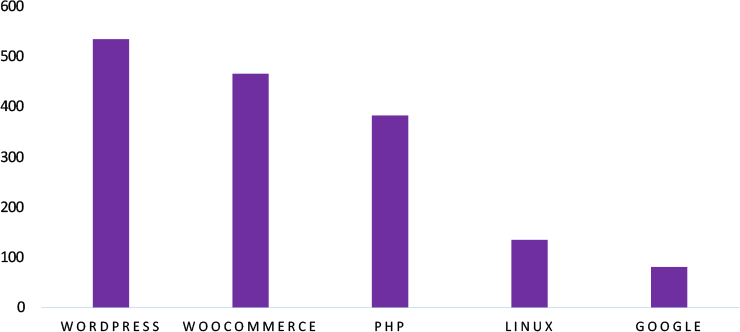
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies due to a range of vulnerabilities. The following are the top 5 most affected technologies.
ETLM Assessment
Vulnerability in NanoMQ introduces significant risks to IoT and messaging infrastructures that rely on MQTT-based communication. As NanoMQ is widely used in lightweight messaging systems for real-time data exchange, exploitation of this vulnerability could disrupt communication channels or allow unauthorized code execution in critical environments. Organizations leveraging IoT messaging platforms must ensure timely patching, secure configuration, and continuous monitoring to prevent potential compromise. Addressing this vulnerability is essential to maintaining the integrity, availability, and security of distributed messaging systems across enterprise and industrial environments.
The Gentlemen Ransomware attacked and published the data of the Cosmo Group Public
Summary:
Recently, we observed that The Gentlemen Ransomware attacked and published the data of Cosmo Group Public(https[:]//www[.]cosmogroup[.]co[.]th/) on its dark web website. Cosmo Group Public is a Thailand-based manufacturer with more than six decades of expertise in producing high-end packaging and precision components for the global luxury market. The company focuses on crafting premium gift boxes, retail displays, watch dials, cases, and related accessories, serving industries such as jewellery, watches, cosmetics, and fragrances. With a strong reputation for quality, innovation, and craftsmanship, Cosmo partners with leading international luxury brands and adheres to rigorous global standards, supported by multiple certifications in quality management and sustainability. The compromised data includes confidential and sensitive information belonging to the organization.
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, The Gentlemen Ransomware is a highly adaptive and globally active threat that leverages dual-extortion tactics, combining data theft with file encryption. The group employs advanced evasion and persistence techniques, supports cross-platform and scalable ransomware deployment, and conducts targeted attacks across multiple industries and geographic regions. This combination of capabilities makes it a significant risk to enterprise cybersecurity defenses, particularly for organizations with limited detection and incident-response maturity.
Abu Dhabi Department of Finance Super Admin Access Advertised on a Leak Site
Summary: The CYFIRMA research team identified a post on a dark web forum by a threat actor operating under the alias “Crimson,” who is advertising the sale of allegedly compromised super administrator access to the Abu Dhabi Department of Finance (UAE) portal (addof[.]gov[.]ae). The Abu Dhabi Department of Finance (ADDOF), which serves as the emirate’s central financial authority, is reportedly the target of this claimed network access sale. The actor alleges possession of high- level administrative privileges associated with the official domain and is offering this access on a cybercrime forum for a fixed price of $800 USD.
According to the forum listing, the alleged access for sale includes:
Super Administrator Access to the ADDOF network/systems
The authenticity of this Access sale remains unverified at the time of reporting, as the claim originates solely from the threat actor.
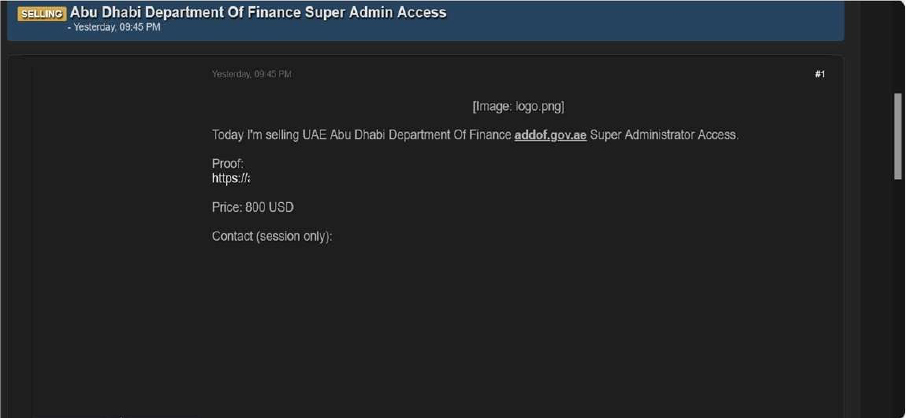
Source: Underground Forums
Taiwan military/Cybersecurity Data Advertised on a Leak Site
Summary: The CYFIRMA research team identified a post on a dark web forum by a threat actor using the alias “Yakohomot,” advertising the sale of an allegedly compromised dataset related to Taiwan’s military and cybersecurity information. The post suggests that the dataset contains sensitive materials associated with cybersecurity operations, strategic intelligence, and critical infrastructure. Based on the actor’s description, the data appears to involve multiple high-value domains, including references to TSMC infrastructure, economic reports, naval radar research and development, and military infrastructure projects such as the Wuling Base.
According to the threat actor, the leaked dataset includes:
The actor claims the total dataset size is approximately 1.8 GB, consisting primarily of text documents and reports. Sample files have been shared in the post as proof, indicating structured and potentially classified or sensitive content. The dataset is being offered for sale at a price of $16,000 USD, with a session-based contact identifier provided for further communication. This incident indicates a potential exposure of sensitive military and strategic intelligence data, which could pose significant national security and geopolitical risks if the claims are legitimate.
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
Source: Underground Forums
Relevancy & Insights:
Financially motivated cybercriminals are continuously looking for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to gain access and steal valuable data. Subsequently, the stolen data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor, “Yakohomot,” is assessed as an active and capable entity focused on data-leak operations, with credible sources linking them to multiple incidents involving unauthorized system access and the distribution or sale of stolen data on dark web platforms. These activities highlight the evolving cyber threat landscape driven by underground criminal networks and emphasize the need for organizations to strengthen cybersecurity through continuous monitoring, enhanced threat intelligence, and proactive defenses to safeguard sensitive data and critical systems.
Recommendations: Enhance the cybersecurity posture by:
The CYFIRMA research team identified a post on a dark web forum by a threat actor using the alias “GlitchX,” advertising the sale of an allegedly compromised database linked to a Qatar-based platform, mybookqatar[.]com. According to the post, the dataset contains information on approximately 280,000 users and is being offered in CSV format, suggesting structured and easily exploitable data. The actor has also shared sample records within the forum to demonstrate the authenticity of the leak.
Based on the details provided, the exposed dataset appears to include a wide range of personally identifiable information (PII) and account-related data, potentially impacting a significant number of users. The fields listed in the sample indicate the presence of:
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
Source: Underground Forums
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
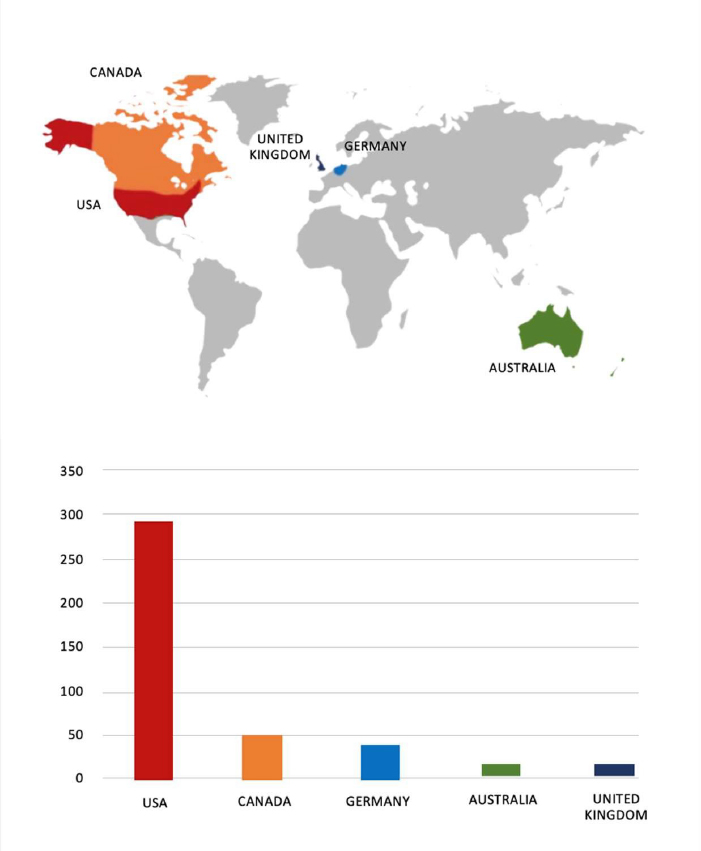
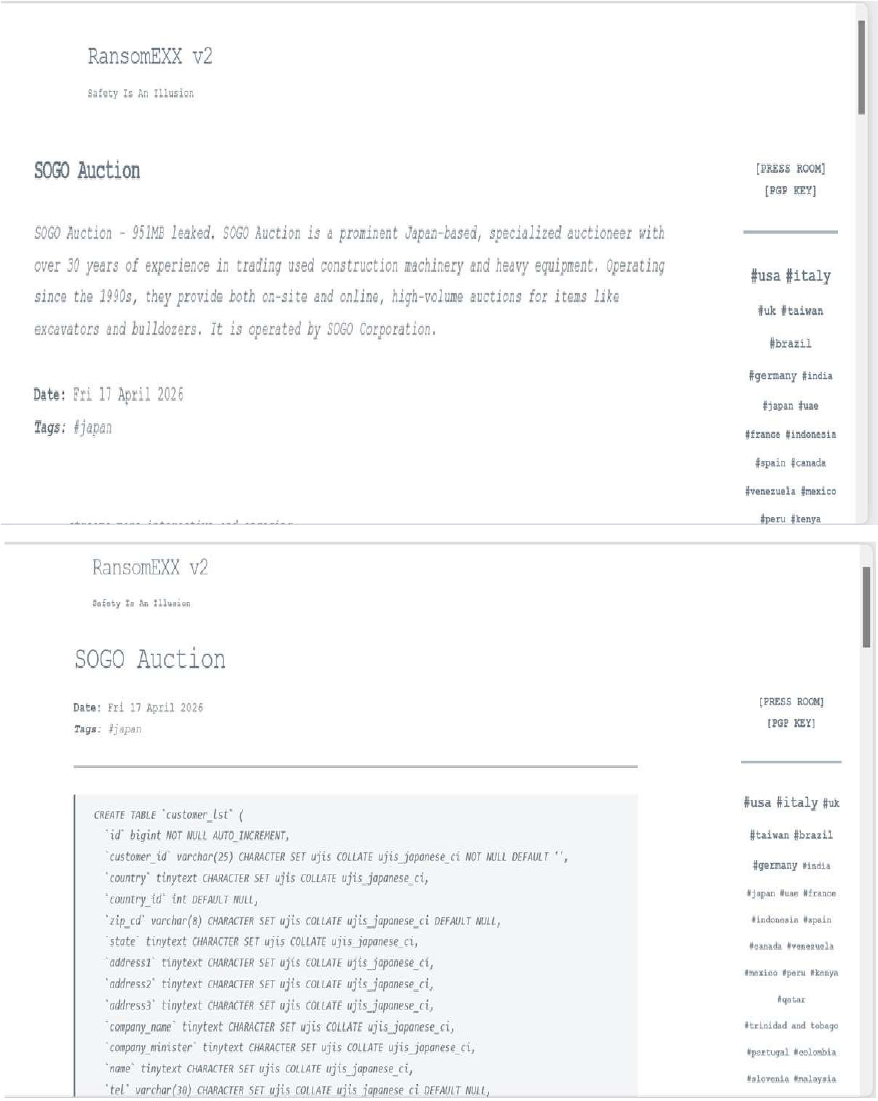
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
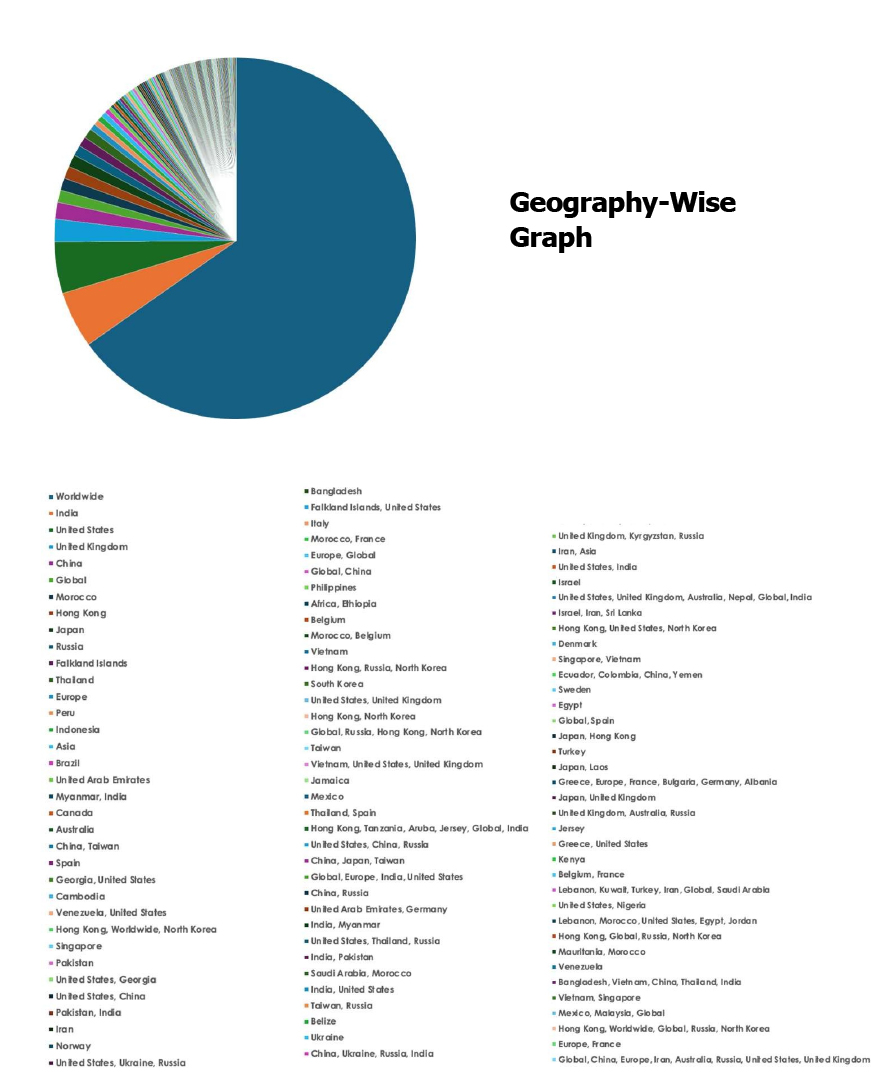
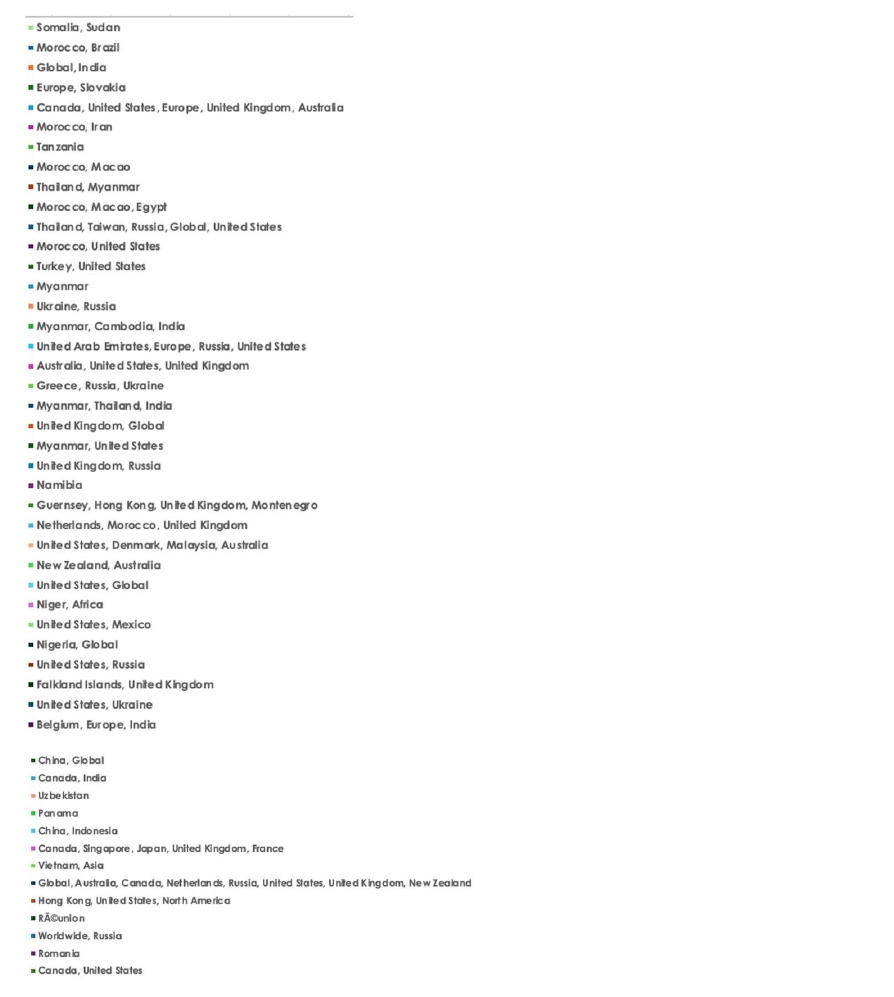
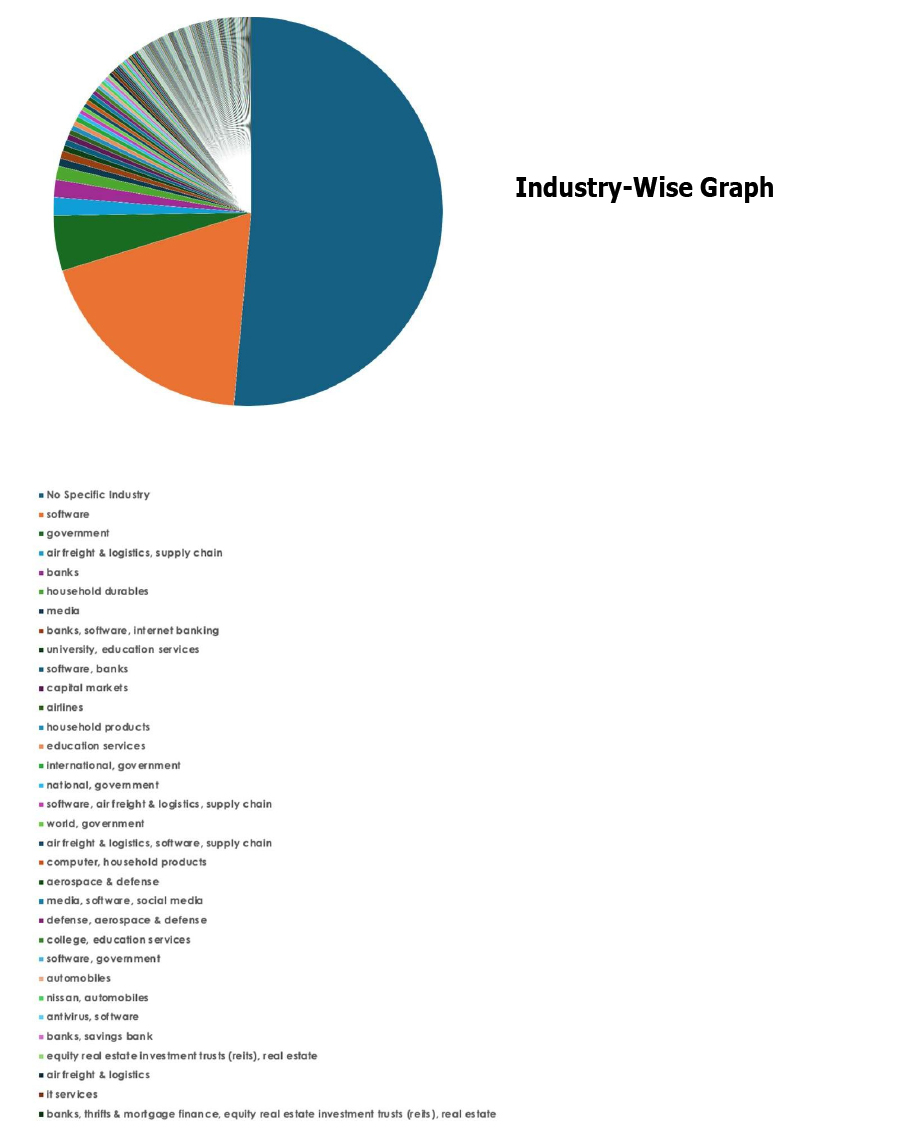
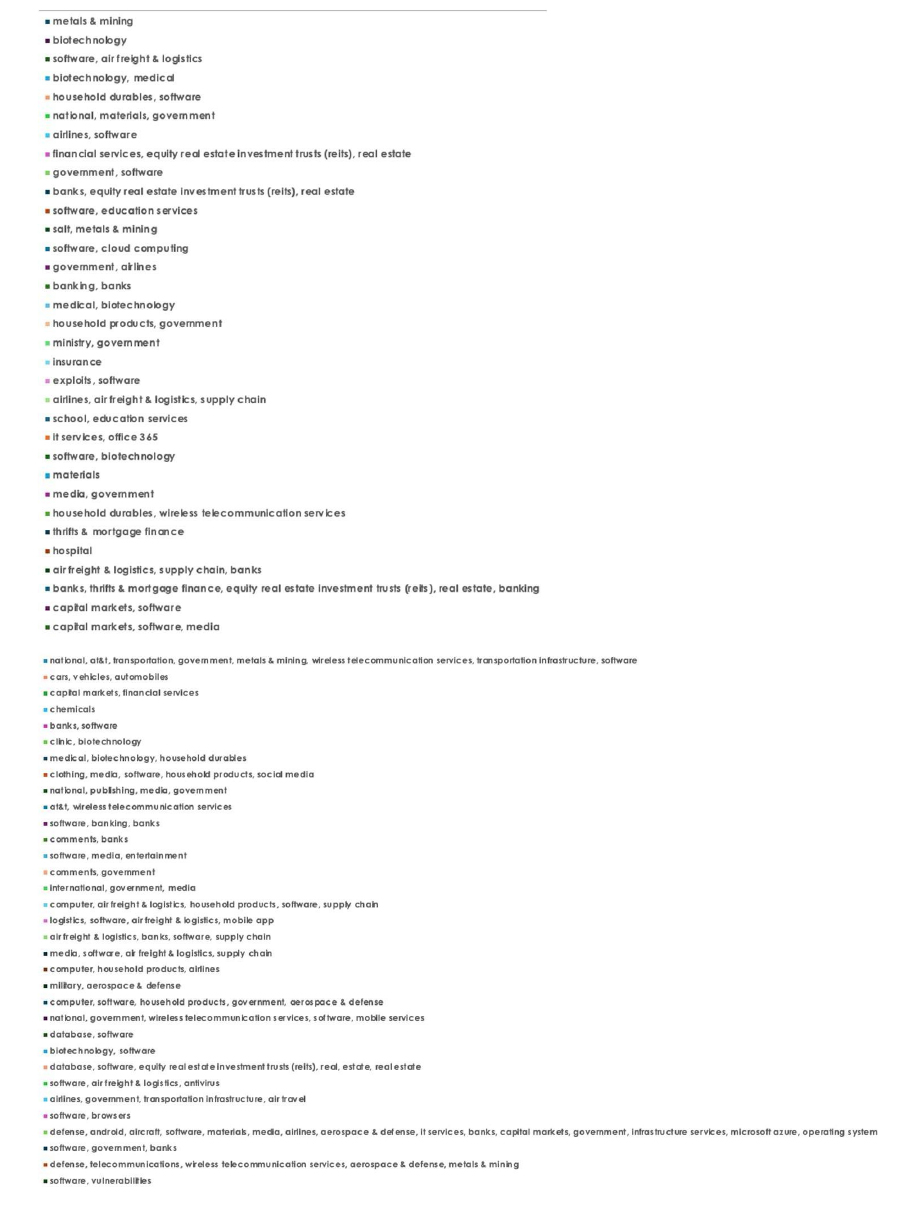
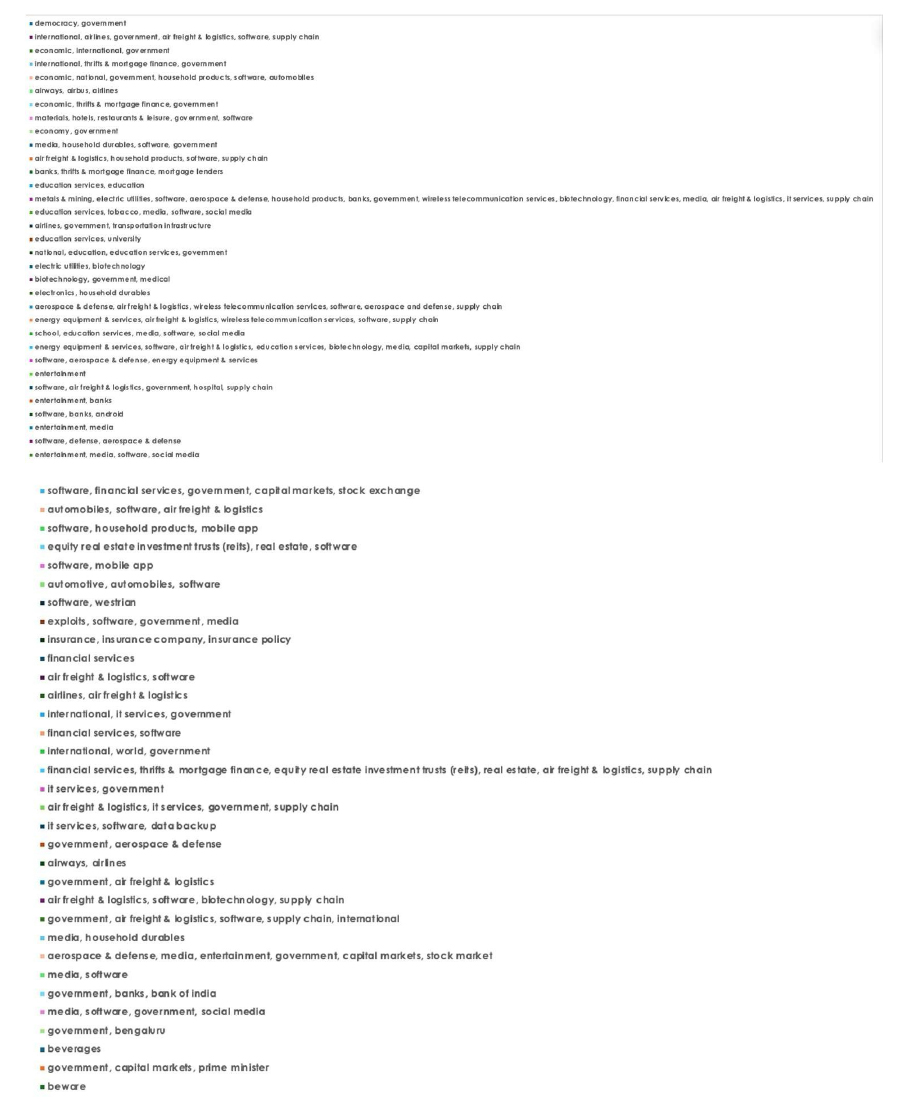
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.