


South Korea faces a sustained and highly sophisticated cyber threat environment shaped by its advanced digital economy, strategic industrial base, and geopolitical positioning in East Asia. As one of the world’s leading semiconductor producers and a global technology powerhouse, the country presents high-value targets across government, defense, manufacturing, and financial sectors. Its deeply integrated supply chains, mature financial infrastructure, and expanding digital government services increase exposure to both financially motivated cybercrime and state-directed intelligence operations. National reporting consistently highlights growing frequency and complexity of ransomware campaigns, credential theft operations, and espionage-driven intrusions.
South Korea’s strategic importance further intensifies this threat profile. The country occupies a critical position between major global powers, maintains advanced defense capabilities, and serves as a central node in semiconductor and electronics supply chains. Its geopolitical environment, particularly tensions on the Korean Peninsula and broader regional security dynamics, ensure sustained intelligence interest. Espionage campaigns frequently align with objectives such as political intelligence collection, supply-chain surveillance, technology acquisition in semiconductor and electronics manufacturing, and monitoring of regional security and maritime policy developments.
South Korea’s cyber threat environment is heavily influenced by North Korea-linked nation-state actors, including Lazarus Group, Kimsuky, and APT37 (Reaper). Lazarus Group combines financial theft and strategic cyber operations, frequently targeting banks and cryptocurrency platforms. Kimsuky focuses on political intelligence collection through spear-phishing and credential harvesting. APT37, also known as Reaper, has historically conducted targeted espionage campaigns against South Korean government bodies, defense organizations, media outlets, and policy institutions, often leveraging zero-day exploits and tailored malware to support intelligence collection objectives. Together, these groups represent a sustained and strategically aligned threat to South Korea’s government, defense, and financial sectors.
Threat motivations observed in recent activity reflect a dual dynamic: State-aligned actors pursue long-term intelligence collection targeting defense procurement, military readiness, economic negotiations, and foreign investment strategy. Simultaneously, financially motivated groups exploit South Korea’s large corporate ecosystem and digital payment infrastructure through ransomware, data theft, and monetization of stolen credentials. Technology transfer efforts, particularly those focused on advanced chip manufacturing and electronics design, remain a persistent strategic concern.
Operationally, social engineering remains a primary intrusion vector, including spear-phishing campaigns targeting government officials, defense contractors, and technology firms. Supply-chain compromise presents elevated risk due to the country’s concentration of semiconductor fabrication and advanced manufacturing facilities. Additional threats include distributed denial-of-service activity, ideologically motivated disruption campaigns, and opportunistic exploitation of publicly exposed services. Collectively, these dynamics position South Korea as one of the most strategically targeted cyber environments in the Asia-Pacific region.
The attribution distribution highlights the sustained dominance of North Korea-linked actors targeting South Korea. Activity associated with Lazarus Group, Kimsuky, and APT37 (Reaper) reflects a combination of strategic intelligence collection and financially motivated operations. These actors demonstrate a consistent focus on government entities, defense contractors, cryptocurrency platforms, media organizations, and critical infrastructure, aligning with Pyongyang’s military, economic, and sanctions-evasion objectives.
Beyond North Korea-linked activity, South Korea remains exposed to opportunistic exploitation by China-aligned and financially motivated cybercriminal groups operating across the broader Asia-Pacific region. However, the concentration and persistence of DPRK-linked campaigns underscore that the primary strategic cyber threat to South Korea remains state-directed and geopolitically driven rather than purely criminal in nature.
Overall, the observed activity suggests a threat environment characterized by long-term intelligence positioning, targeted financial theft operations, and episodic disruptive campaigns aligned with regional security developments.
Lazarus Group
Lazarus Group is a North Korea–linked threat actor consistently associated with espionage and financially motivated cyber operations targeting the South Korean government, defense, cryptocurrency, and financial institutions. Campaigns have involved spear-phishing, weaponized document lures referencing inter-Korean relations, and the deployment of custom malware frameworks to establish persistence and conduct data exfiltration. In addition to intelligence collection, Lazarus has been linked to digital asset theft and supply-chain compromise activity, aligning with Pyongyang’s strategic objective of sanctions evasion and technology acquisition.
A sub-cluster of Lazarus, commonly tracked as Andariel, has demonstrated a more focused emphasis on intrusions against South Korean defense contractors and military-related infrastructure. This subgroup has been observed exploiting publicly disclosed vulnerabilities and leveraging tailored malware to support strategic military intelligence collection, reinforcing the persistent threat to South Korea’s defense ecosystem.
Kimsuky
Kimsuky is a DPRK-aligned espionage group primarily focused on political intelligence collection against South Korean government agencies, policy think tanks, academics, and media organizations. The group heavily leverages social engineering, credential phishing portals, and malicious attachments to harvest login data and monitor diplomatic and defense-related discourse. Kimsuky’s operations frequently aim to obtain insight into South Korea’s foreign policy positions, inter-Korean negotiations, and alliance coordination.
APT37 (Reaper)
APT37, also known as Reaper, is a North Korea-linked espionage actor that has conducted targeted intrusions against South Korean government agencies, defense contractors, media organizations, and policy institutions. The group has demonstrated the use of spear-phishing campaigns, zero-day exploits, and custom malware to gain initial access, followed by credential harvesting and data exfiltration. APT37’s operations are primarily intelligence-driven, focusing on political, military, and strategic information collection, reinforcing the sustained threat to South Korea’s national security and defense ecosystem.
APT41
APT41 is a China-linked group known for dual-use operations combining espionage with financially motivated campaigns. South Korea’s semiconductor, electronics manufacturing, and gaming industries fall within sectors historically targeted by APT41 across Asia. The group frequently exploits unpatched internet-facing applications to gain initial access, followed by credential harvesting, privilege escalation, and intellectual property exfiltration. Its targeting patterns align with broader supply-chain surveillance and technology transfer objectives.
Mustang Panda
Mustang Panda is a China-aligned espionage actor observed targeting government and policy-related entities across East Asia. Operations have leveraged DLL sideloading techniques and custom backdoors to maintain persistent access while evading detection. In the South Korean context, targeting interest typically aligns with political intelligence collection, maritime policy monitoring, and regional security analysis, consistent with Beijing’s strategic priorities in Northeast Asia.
South Korea experienced moderate but consistent ransomware exposure over the past three months, with activity distributed across multiple sectors rather than being concentrated in a single industry. January 2026 recorded the highest overall victim listings during the monitoring period, followed by steady activity in December 2025 and a slight decline in February 2026. The pattern suggests sustained but not escalatory targeting.
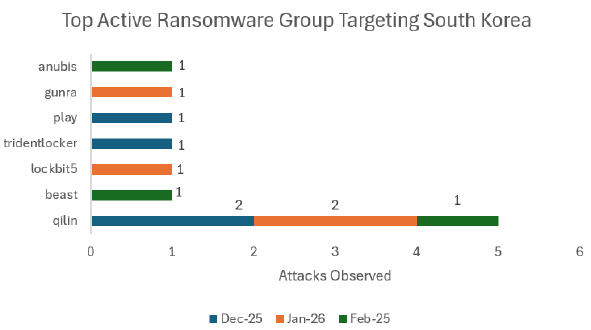
The most active ransomware group impacting South Korean entities during this period was Qilin, which accounted for multiple victim disclosures across all three months. Qilin’s repeated presence indicates continued operational focus and successful intrusion capability within the region. Other groups observed listing South Korean victims include LockBit 5.0, Play, Trigona/TridentLocker, Gunra, Beast, and Anubis, though these were largely limited to isolated incidents.
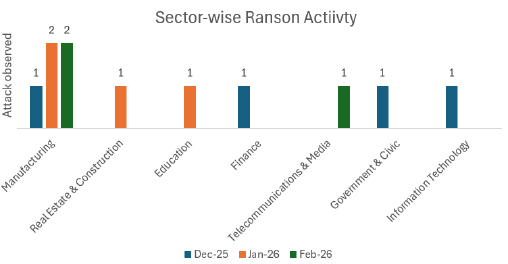
Sector-wise analysis indicates that Manufacturing experienced the highest concentration of ransomware activity, with multiple listings observed across January and February. Additional affected sectors include Finance, Government & Civic, Information Technology, Education, Telecommunications & Media, and Real Estate & Construction, though these industries recorded isolated incidents rather than sustained waves of attacks.
Manufacturing’s prominence reflects South Korea’s position as a major industrial and semiconductor hub, making it attractive for disruption and data theft. Incidents affecting government, finance, and IT sectors indicate targeting of data-rich and operationally critical environments that can generate stronger ransom leverage.
Overall, ransomware activity targeting South Korea appears financially motivated and opportunistic, consistent with broader regional RaaS trends. Although Qilin shows comparatively higher activity, no single group maintains sustained dominance, and the threat landscape remains fragmented across multiple operators.
Qilin
Qilin operates as a Ransomware-as-a-Service (RaaS) collective, where core operators maintain the encryption payload, leak infrastructure, and negotiation portals while affiliates conduct intrusions. The group has demonstrated opportunistic targeting across Asia-Pacific, including South Korea, with activity affecting professional services, manufacturing, and logistics entities.
Qilin commonly leverages access brokers and previously compromised credentials rather than highly tailored intrusion campaigns.
Observed tradecraft includes:
Play
Play remains an active ransomware operator globally, known for targeting enterprise environments and leveraging double-extortion tactics. The group has maintained operational continuity despite increased international scrutiny and defensive improvements across targeted regions.
In South Korea, Play activity appears opportunistic rather than strategically concentrated.
Observed tradecraft includes:
LockBit
LockBit remains one of the most globally active ransomware collectives despite sustained international law enforcement disruption efforts. Although major takedown actions have impacted parts of its infrastructure, affiliates continue operating through residual systems and evolving variants.
In South Korea, LockBit activity appears opportunistic rather than strategically focused.
Observed tradecraft includes:
South Korea continues to face consistent and multifaceted cybercriminal attention, driven by its advanced digital infrastructure, strong financial ecosystem, and globally connected industries. The threat landscape reflects a combination of financially motivated cybercrime and data-centric intrusions, with periodic spikes linked to large-scale breach events. This positions South Korea as a high-value target within the Asia-Pacific region, particularly for actors seeking scalable monetization opportunities.
Dark web monitoring over the observed three-month period indicates sustained references to South Korean entities, with a notable surge in activity during December. This spike is primarily driven by data breach disclosures and bulk data circulation, which continue to influence underground discussions into subsequent months. While activity decreases in January and February, the persistence of mentions suggests ongoing exploitation and resale of compromised data.
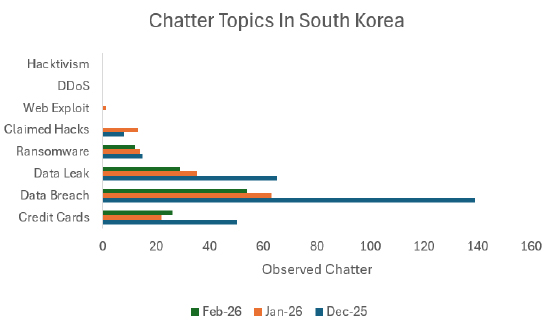
Data breach-related chatter significantly exceeds other categories, making it the dominant threat vector. Data leak discussions also remain prominent, indicating active trading of sensitive corporate and personal information across underground marketplaces. This trend highlights the continued importance of data exfiltration as a primary objective for threat actors targeting South Korean organizations.
Financially motivated activity remains a key driver, with credit card fraud and credential-based attacks consistently observed across the monitoring period. The steady presence of carding-related chatter suggests well-established monetization channels, where stolen financial data is rapidly operationalized. These activities are typically linked to credential stuffing, account takeover, and payment fraud schemes.
Ransomware-related discussions show moderate but persistent activity, aligning with broader Ransomware-as-a-Service (RaaS) operations targeting enterprises globally. While not the dominant threat, ransomware poses a continued risk of data exfiltration and double extortion, particularly for organizations managing large volumes of sensitive data. In contrast, hacktivism and DDoS-related chatter remain limited, indicating that such activity is more event-driven and influenced by geopolitical developments rather than sustained targeting.
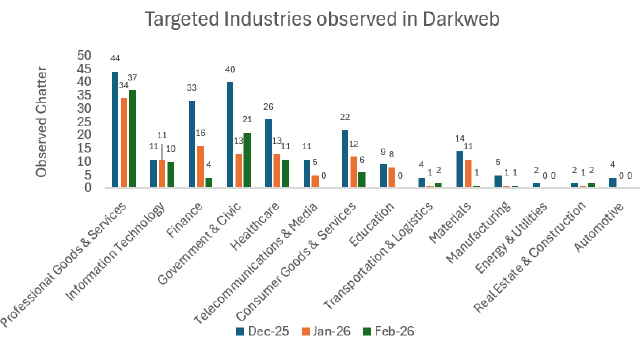
Industry targeting trends indicate that Professional Goods & Services and Government & Civic sectors receive the highest attention, followed by Healthcare, Finance, and Consumer Goods & Services. The focus on professional services suggests potential supply chain intrusion opportunities, while government-related chatter reflects interest in public sector data and infrastructure. Financial institutions remain attractive targets due to their direct monetization potential, particularly in relation to fraud and credential compromise.
Overall, South Korea’s cyber threat landscape is characterized by high-volume data breaches, active underground data markets, and sustained financial exploitation activities. The data indicates that information theft and monetization, particularly through breached datasets and financial credentials, remain the primary drivers of adversarial interest. While ransomware and hacktivism are present, they play a secondary role, reinforcing the need for strong data protection, identity security, and continuous monitoring of underground ecosystems.
Note: The authenticity of the breaches below remains unverified at the time of reporting, as the claims originate solely from the threat actors.
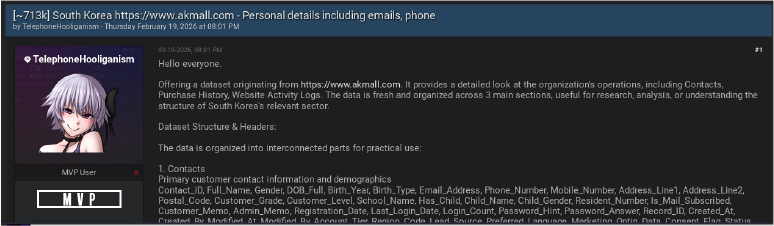
On February 19, 2026, a user named TelephoneHooliganism was observed advertising the sale of a dataset containing approximately 713,000 records attributed to the South Korean e-commerce site. The listing claims to offer comprehensive information organized into three main sections: primary customer contacts and demographics, purchase history, and website activity logs. The exfiltrated data reportedly includes highly sensitive personally identifiable information (PII) such as full names, gender, dates of birth, resident numbers, email addresses, phone numbers, and physical addresses.
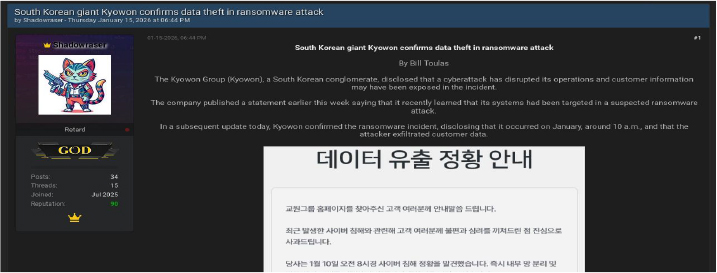
On January 15, 2026, a user named Shadowraser shared a report confirming that the Kyowon Group, a major South Korean conglomerate, fell victim to a ransomware attack. The incident, which occurred on January 10, resulted in operational disruptions and the confirmed exfiltration of sensitive customer data. The company issued a formal apology and began internal network isolation to mitigate further damage.
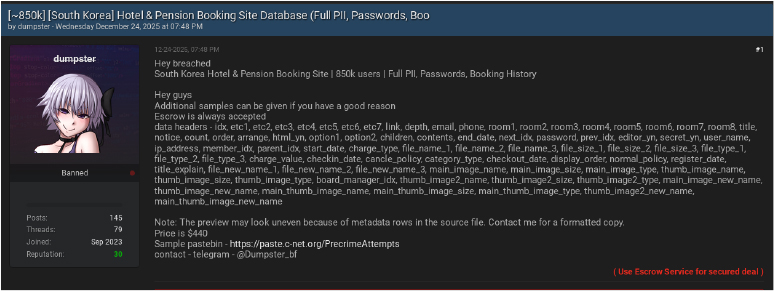
On December 24, 2025, the user dumpster also posted an advertisement for a database belonging to a South Korean hotel and pension booking site. The dataset is said to encompass 850,000 users and includes PII, passwords, and detailed booking histories. Offered for $440, the data headers suggest the leak contains technical metadata, check-in dates, and internal member indices, alongside user contact information.
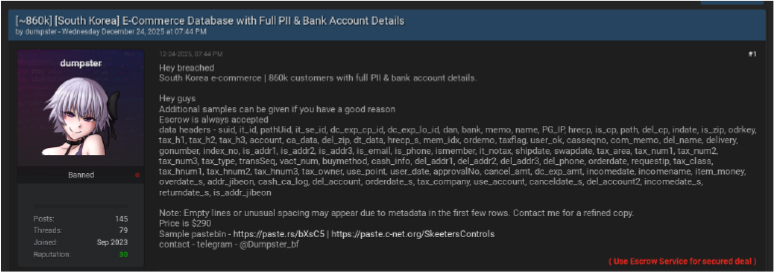
On December 24, 2025, a user known as dumpster advertised a dataset allegedly containing information on 860,000 customers from a South Korean e-commerce platform. The listing, priced at $290, claims to include full PII and sensitive financial data, specifically bank account details. The threat actor provided data headers indicating fields for bank names, account numbers, payment gateway IP addresses, and detailed delivery information.
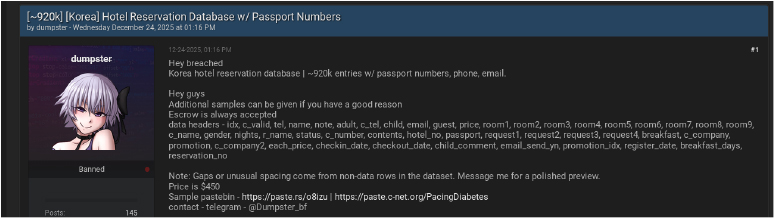
On December 24, 2025, the user dumpster listed a third dataset containing approximately 920,000 entries from a Korean hotel reservation system. This specific listing, priced at $450, highlights the inclusion of passport numbers alongside names, email addresses, and phone numbers. The advertisement details that the data contains granular reservation information, including room numbers, stay duration (nights), company names, and specific guest requests.
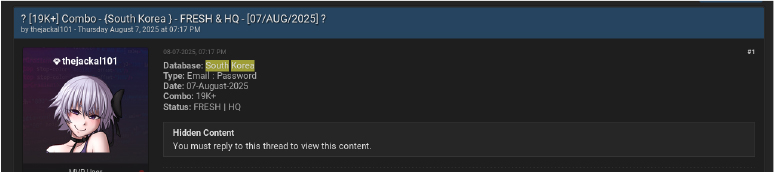
On August 7, 2025, a user named thejackal101 posted a dataset containing over 19,000 email and password combinations attributed to South Korean targets. The actor characterized the data as “FRESH & HQ” (high quality), offering it to the forum community under the condition of a thread reply to unlock the hidden content.
On April 6, 2025, a user known as el_capitan advertised a “Private Good Combolist” allegedly containing 50,000 entries related to South Korea. The listing, promoted alongside various spamming and cracking tools, requires users to interact with the thread or join a specific Telegram channel to gain access to the credentials.
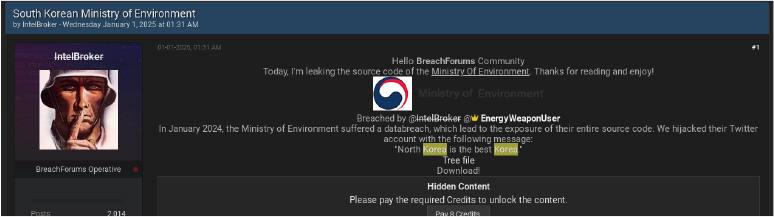
On January 1, 2025, the threat actor IntelBroker claimed to have leaked the entire source code of the South Korean Ministry of Environment. The post alleges that the breach originally occurred in January 2024 and involved the hijacking of the Ministry’s official Twitter account to post political messages. The leaked data was made available to forum members via a credit-based unlock system.
South Korea remains a primary target for sophisticated financial phishing, with attackers increasingly shifting toward high-value individual targets.
Hacktivism targeting South Korea is largely geopolitically driven and event-responsive, often linked to regional or international political developments. While many incidents involve DDoS campaigns and website defacements, some groups publicly threaten broader infrastructure disruption to amplify political messaging. Activity typically spikes during periods of diplomatic tension rather than reflecting sustained long-term campaigns.
Anonymous Campaigns (2023–2024): Various factions operating under the Anonymous banner claimed responsibility for DDoS attacks and website defacements targeting South Korean government portals and public institutions. These operations were largely symbolic and politically motivated.
Pro-Russian DDoS Threat Campaign (2024–2025): Following public discussions regarding potential South Korean military support to Ukraine, pro-Russian hacktivist actors circulated lists of South Korean government, municipal, and public service websites as targets for DDoS attacks. The campaign referenced entities including the City of Seoul, Korea Customs Service, the National Assembly, and multiple regional government offices. The activity appeared focused on temporary service disruption and political signalling rather than sustained network compromise.

South Korea is at the forefront of the “Deepfake Era” in cybercrime, with attackers exploiting the country’s highly digitized society.
Deepfake Corporate Fraud: Attacks using AI-generated voices and videos for virtual meetings have become a primary concern for 2026, targeting “trust-based communication methods” to authorize fraudulent transfers.
Massive Data Breaches: A major breach at the Kyowon Group in early 2026 potentially affected 9.6 million accounts, providing attackers with a massive repository of personal data to fuel future targeted social engineering.
Authority Impersonation: Experts warn that leaked personal data is increasingly being reused in AI-combined attacks where scammers impersonate government or financial officials with near-perfect accuracy.
DDoS attacks in South Korea have more than doubled as attackers shift from simple volume to highly sophisticated, multi-vector methods.
High-Profile Tech and Business Events
Sporting and Cultural Events
Managing South Korea’s external threat landscape requires consistent visibility into how the country and its strategic sectors are discussed, targeted, or exposed across ransomware leak sites, underground marketplaces, credential forums, and open-source reporting. Given South Korea’s geopolitical sensitivity, advanced semiconductor industry, and globally connected financial ecosystem, external monitoring must balance both state-sponsored espionage risks and financially motivated cybercrime activity. Emerging risks such as AI-driven phishing and deepfake-enabled social engineering further increase exposure, particularly against senior officials, financial executives, and technology leaders.
This means closely tracking ransomware disclosures, cryptocurrency exchange targeting, credential resale posts, and access broker listings that reference Korean government bodies, defense contractors, semiconductor manufacturers, and major enterprises. The rise of “quadruple extortion” ransomware – involving data encryption, public leaks, DDoS pressure, and customer blackmail -adds additional operational and reputational risk. Monitoring exploit discussions involving commonly used VPN platforms, cloud services, enterprise applications, and edge devices is equally important, especially as cloud-native adoption accelerates and misconfigured environments or weak authentication controls become attractive entry points.
It is also important to maintain awareness of activity linked to actors such as Lazarus Group, Kimsuky, Reaper, APT41, and Mustang Panda, whose operations frequently intersect with South Korea’s political, defense, financial, and technology sectors. A structured and continuous approach to monitoring these developments strengthens situational awareness and supports more informed, proactive risk management decisions.
Ultimately, effective ETLM in South Korea is not just about monitoring threats, but about turning external visibility into tangible risk reduction. Intelligence gathered from the external landscape should directly inform vulnerability prioritization, cloud security hardening, and incident response planning. As espionage pressures, AI-enabled deception, and ransomware evolution persist, integrating external insight into strategic and operational decision-making remains critical to maintaining national and sectoral resilience.
Strengthen Critical Infrastructure Security
Ransomware and Financial Cybercrime Mitigation
Sector-Specific Protections
Social Engineering, Hacktivist, and DDoS Preparedness
Emerging Threat Monitoring