


China’s cyber threat landscape during 2025–2026 is shaped by sustained inbound targeting from multiple foreign state-sponsored actors, persistent ransomware pressure across high-value sectors, and an expanding foreign intelligence collection mandate against Chinese national assets. Ransomware activity remains competitive and fragmented, with groups such as LockBit, World Leaks, and TheGentlemen leading activity against high-value sectors including telecommunications, energy, IT, and manufacturing, while legacy vulnerabilities continue to drive exploitation at scale. At the same time, China faces inbound threats targeting sensitive national assets, including alleged compromises of time synchronization infrastructure and large-scale dark-web data leak claims affecting public programs and research institutions. Overall, the environment is characterized by systemic infrastructure risk, zero-day operationalization speed, supply chain leverage, and increasing convergence between cyber espionage, strategic disruption capability, and criminal monetization.
Fragmented but Persistent Ransomware Pressure: China faces sustained ransomware activity led by LockBit, World Leaks, and TheGentlemen, with no single actor dominating. Telecommunications, energy, IT, and manufacturing remain the most consistently targeted sectors, reflecting their operational centrality and systemic impact potential.
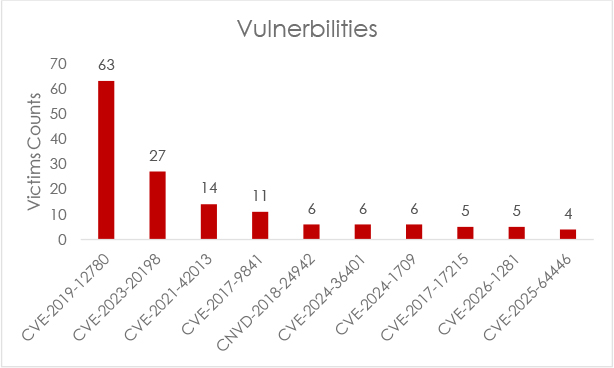
Legacy Vulnerabilities Still Driving Exploitation: Older CVEs (2014–2019) continue to generate significant detection volume, demonstrating persistent patching gaps across exposed infrastructure. Simultaneously, rapid weaponization of newly disclosed 2024–2025 vulnerabilities indicate attackers are balancing opportunistic exploitation with zero-day capability.
Supply Chain and Managed Service Provider Risk: Targeting patterns indicate deliberate positioning within SaaS providers, MSPs, and third-party technology ecosystems to achieve downstream access into multiple victim environments simultaneously.
Inbound Targeting of Chinese National Infrastructure: Alleged compromises affecting national time synchronization infrastructure and other strategic systems highlight systemic, cascading risk potential where disruption could impact finance, telecommunications, energy, and defense sectors.
Dark-Web Data Exposure and Criminal Activity: Multiple large-scale breach claims involving public service databases, financial institutions, and research organizations indicate ongoing data monetization activity, though several claims remain unverified.
Emerging Threat Acceleration Factors: AI-assisted offensive tooling, semiconductor and advanced technology targeting, and regulatory reporting centralization collectively reshape the threat landscape, increasing both attack precision and the strategic value of incident intelligence.
Ransomware continues to be the most disruptive threat to Chinese organizations, with attacks driven by both dominant and emerging groups.
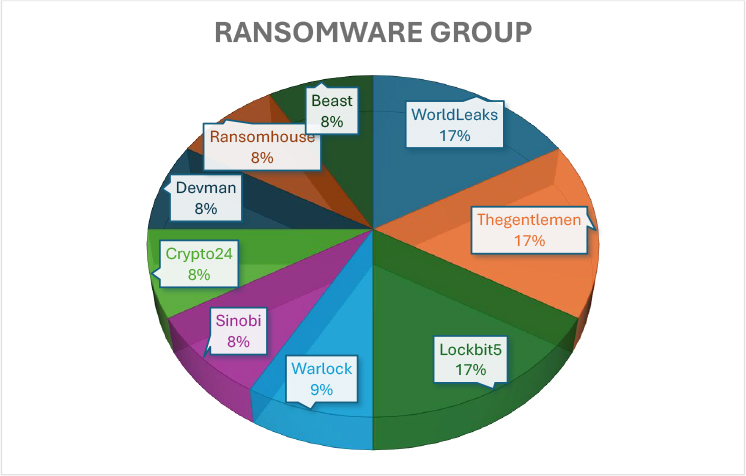
LockBit, World Leaks, and TheGentlemen emerge as the leading groups, each accounting for the largest share of observed activity. Their comparable percentages indicate a competitive landscape where multiple high-capability operators are active simultaneously rather than a single group dominating the environment.
A secondary tier includes Warlock, followed closely by Sinobi, Crypto24, Devman, RansomHouse, and Beast. These actors contribute smaller but still notable portions of activity, suggesting either more selective targeting or lower operational volume compared to the leading cluster.
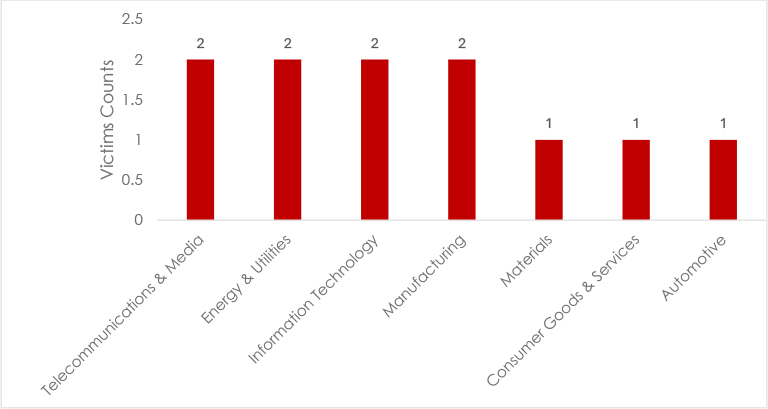
Telecommunications and Media, Energy and Utilities, Information Technology, and Manufacturing appear at the highest observed level, each showing comparable incident frequency. This suggests sustained threat actor interest in sectors that either manage core infrastructure, enable digital services, or support large-scale operational ecosystems. These industries typically present high-impact targets due to their network centrality and operational sensitivity.
Materials, Consumer Goods and Services, and Automotive show lower but consistent activity. While incident counts are comparatively smaller, these sectors remain relevant due to supply chain integration, industrial systems exposure, and reliance on connected operational technologies.
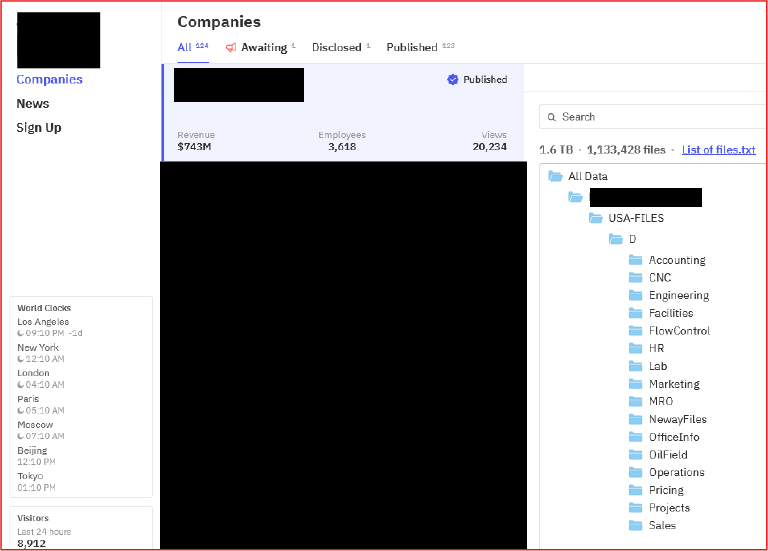
On Feb 15, 2026, the ransomware group LockBit5 reportedly released various stolen materials, including identification documents, and other confidential files of an information technology service provider based in China.
On Feb 15, 2026, the ransomware group LockBit5 reportedly exposed data associated with a water production and supply provider based in China.
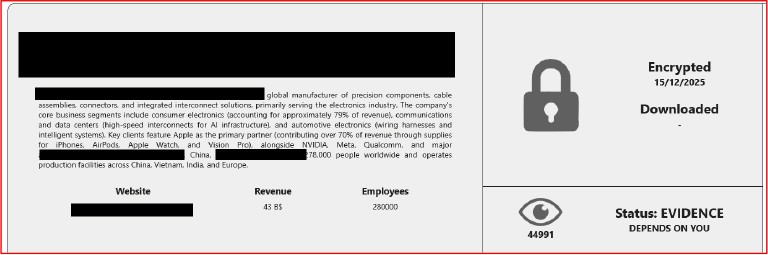
On Dec 12, 2025, the ransomware group Ransomhouse posted an alleged exposure of data of a major manufacturer based in China.
Based on their 90-day average detection rates, CVE-2019-12780 leads the list, followed by CVE-2017-17215, CVE-2014-8361, CVE-2018-10562, and CVE-2016-10372. The data shows that older vulnerabilities from 2014–2019 continue to generate significant activity, demonstrating the long tail of unpatched systems still exposed to exploitation. At the same time, the presence of newer 2024–2025 CVEs indicates that attackers are actively incorporating recently disclosed vulnerabilities into their campaigns.
| CVE ID | CVSS | Products Affected | Threat Actors | Exploit Available |
| CVE-2019-12780 | 9.8 | Belkin Wemo Smart Plug | LockBit, RansomHouse | No |
| CVE-2017-17215 | 9.1 | NETGEAR Routers (R6400, R7000, R8000) | World Leaks, TheGentlemen, Devman | Link |
| CVE-2014-8361 | 9.3 | Realtek SDK, IoT Devices, Network Equipment | Warlock, Sinobi, Beast | Link |
| CVE-2018-10562 | 8.9 | Dasan GPON Home Routers | LockBit, RansomHouse, Crypto24 | Link |
| CVE-2016-10372 | 9.8 | Eir D1000 modem | Unknown / Not attributed | No |
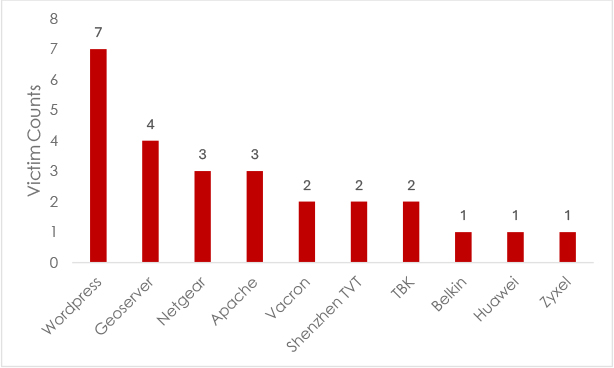
WordPress stands out as the most frequently exploited platform, indicating continued attacker focus on vulnerable plugins, outdated installations, and exposed administrative interfaces. Its prevalence reflects both its global footprint and its common exposure to the public internet.
GeoServer follows as the second most targeted technology, suggesting exploitation of unpatched vulnerabilities or misconfigured geospatial services. Netgear and Apache Software Foundation show similar levels of activity, typically linked to exposed web servers, misconfigurations, or outdated firmware in edge networking devices.
A secondary tier includes Vacron, Shenzhen TVT, and TBK, indicating targeting of surveillance and video management systems. Lower but consistent exposure is observed across infrastructure products from Belkin, Huawei, and Zyxel, typically through internet-facing management interfaces or outdated firmware.
Chinese organizations and critical infrastructure remain targets for criminal monetization and intelligence collection on underground forums. Our monitoring identified sustained activity involving data exfiltration claims, ransomware negotiations, and infrastructure reconnaissance targeting Chinese government, finance, technology, and critical infrastructure sectors. Cyclical peaks in ransomware and breach claims suggest coordinated campaign activity and operational disruption events. Analysis reveals patterns of data sales, criminal discussions on exploitation techniques, and strategic intelligence collection efforts against Chinese entities.
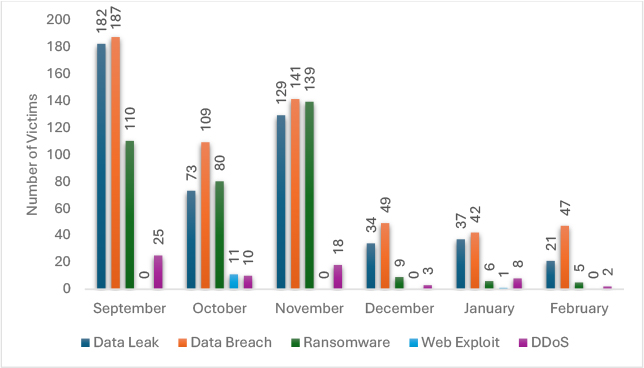
Data breaches and data leaks dominate throughout the timeline. September records the highest levels, with breaches at 187 and leaks at 182, followed by a gradual decline into December and January. While both categories drop substantially after November, breach activity remains comparatively stable in January and February, indicating continued compromise of sensitive data even as large-scale leak disclosures decrease.
Ransomware activity peaks in November at 139 incidents, following strong activity in September and October. However, a dramatic reduction is observed from December onward, with single-digit figures recorded in January and February. This suggests either operational disruption within ransomware ecosystems, reduced public disclosures, or a shift toward quieter data-exfiltration-driven campaigns rather than encryption-heavy operations.
Claimed hacks show moderate activity in October and November, disappear entirely in December and January, and reappear in February. This pattern may indicate fluctuating hacktivist or reputation-driven claim behaviour rather than consistent operational campaigns.
DDoS incidents follow a declining trajectory overall, with the highest concentration in September and smaller spikes in November and January. Hacktivism mirrors a similar pattern, with limited but noticeable activity in the early months before dropping sharply. Web exploitation appears sporadic, with a brief spike in October and isolated activity in January, suggesting opportunistic rather than sustained exploitation campaigns.
A sustained cyberespionage campaign targeting China’s National Time Service Centre ran from early 2022 through 2025, identified in October 2025. The facility is responsible for broadcasting China’s standard time signal to telecommunications networks, financial markets, transportation infrastructure, and defense systems.
Target Industries: Telecommunications, financial markets, transportation, defense systems, and power grid operations.
Target Technologies: Time synchronization infrastructure, telecommunications switching systems, financial trading platforms, power grid relays, internet routing protocols, and staff mobile devices.
Initial Access: Supply chain compromise through overseas telecommunications provider, exploiting a trusted third-party network connection to bypass perimeter defenses.
Key TTPs: Deployment of 42 specialized cyber-attack tools, persistence maintenance, network configuration data extraction, staff mobile device access, and long-term access maintenance.
Motivations: Intelligence collection on critical infrastructure dependencies, pre-positioning for potential disruption of financial systems and military communications, assessment of infrastructure vulnerabilities, and cascading failure potential.
Strategic Impact: Compromise of national time infrastructure affects all dependent systems, financial platforms, telecommunications switching, power grid relays, and encrypted communications. A corrupted time source induces cascading failures without generating external attack alerts, creating systemic risk across multiple critical sectors simultaneously.
APT33 is an Iranian state-sponsored threat actor operating under the control of the Islamic Revolutionary Guard Corps (IRGC). Active since at least 2013, the group has conducted sustained espionage and reconnaissance operations targeting critical infrastructure sectors globally, with particular focus on energy, aerospace, and petrochemical industries. The group is known for rapid vulnerability exploitation, aggressive reconnaissance activities, and targeting of organizations supporting Iran’s strategic competitors. In recent years, APT33 has expanded its operational scope to target Asian critical infrastructure, including Chinese energy sector assets, representing a strategic shift in geographic priorities toward direct competition with Chinese energy production and geopolitical influence.
Target Industries: Energy sector, government agencies, chemical and petrochemical plants, telecommunications, and aerospace.
Primary Technologies Targeted: Industrial control systems (SCADA), VPN appliances, email systems, web servers, and network infrastructure.
Initial Access Vectors: Spear-phishing with weaponized documents, exploitation of public-facing web applications, targeting of VPN infrastructure.
Key TTPs: Reconnaissance and surveillance of critical infrastructure; deployment of custom malware (DROPSHIP, TURNEDUP) for persistence; lateral movement targeting sensitive systems; dwell times averaging 6+ months for intelligence collection.
Motivations: Strategic intelligence collection on the Chinese energy infrastructure and production capacity; assessment of Iranian strategic competition with Chinese energy sector; technological espionage on energy-related research; competitive intelligence supporting Iranian industrial development.
Examples: Targeting of Chinese petroleum refineries and pipeline infrastructure; operations against natural gas distribution systems; surveillance of energy ministry communications and policy development; reconnaissance of advanced energy research programs.
Geographic Focus: Emerging targeting of Chinese energy infrastructure represents expansion of APT33 operations beyond traditional Middle Eastern focus, indicating increased interest in Asian strategic assets and direct competition with Chinese energy sector dominance.
APT34 is an Iranian state-sponsored cyber espionage group operating under the Ministry of Intelligence and Security (MOIS), active since at least 2014. The group specializes in targeted intrusions against government and private sector organizations in the Middle East, Europe, and increasingly Asia. APT34 is characterized by sophisticated social engineering, patient long-term access maintenance, and intelligence collection focused on sensitive government communications and strategic technology development. The group’s expansion into targeting the Chinese government and technology sectors reflects Iran’s strategic competition with China over regional influence, technology partnerships, and alignment with international powers. Recent operations demonstrate increasing technical sophistication and coordinated intelligence collection supporting the Iranian government decision-making.
Target Industries: Government, oil and gas, telecommunications, technology companies, and financial services.
Primary Technologies Targeted: Government email systems, oil and gas operational technology, web servers, and identity management systems.
Initial Access Vectors: Spear-phishing campaigns with sophisticated social engineering, exploitation of web application vulnerabilities, targeting of email servers, and supply chain compromise targeting government service providers.
Key TTPs: Persistent access through webshell installation; credential theft enabling lateral movement; intelligence collection on communications and decision-making; malware deployment (BONDUPDATER or TONEDEAF) for sustained access; document exfiltration targeting policy and strategic planning materials.
Motivations: Strategic intelligence collection on Chinese government decision-making; assessment of Chinese technology and energy sector capabilities; political and economic competitive intelligence; understanding of Chinese foreign policy priorities; technology acquisition supporting Iranian development goals.
Examples: Operations against Chinese government ministry networks; targeting of technology companies engaged in AI and semiconductor research; surveillance of energy sector planning and policy; reconnaissance of Chinese technology partnerships with third countries.
Geographic Focus: Operations targeting China represent an emerging intelligence priority for MOIS, reflecting the broader Iranian strategy to understand Chinese strategic intentions, technology capabilities, and competitive positioning in Asian markets.
Kimsuky is a North Korean state-sponsored cyber espionage group operating under the Reconnaissance General Bureau, active since at least 2012. The group specializes in sophisticated social engineering, credential theft, and intelligence collection targeting government, defense, technology, and research sectors globally. Kimsuky is known for patient, long-term access maintenance, and high-quality intelligence analysis of compromised systems. The group has expanded its targeting to the Chinese technology and defense sectors as part of broader North Korean intelligence collection operations.
Target Industries: Government agencies, technology companies, defense research, semiconductor manufacturing, AI research institutions, and cryptocurrency exchanges.
Primary Technologies Targeted: Email systems, enterprise networks, VPN infrastructure, cloud collaboration platforms, and identity management systems.
Initial Access Vectors: Sophisticated spear-phishing with tailored social engineering, exploitation of email vulnerabilities, targeting of researchers and government officials with fake job offers, and collaboration invitations.
Key TTPs: Credential harvesting through phishing; lateral movement using compromised credentials; long-term access maintenance; intelligence collection on communications and research activities; document exfiltration; use of legitimate cloud services for C2 obfuscation.
Motivations: Intelligence collection on Chinese technology development, including AI and semiconductor research; assessment of Chinese defense capabilities and research priorities; understanding of Chinese government technology strategies; acquisition of intellectual property supporting North Korean technology development.
Examples: Operations against Chinese AI research institutes; targeting of semiconductor research organizations; surveillance of defense ministry communications; intelligence collection on Chinese-foreign technology partnerships.
APT29 is a Russian state-sponsored cyber espionage group operating under the Foreign Intelligence Service (SVR). Active since at least 2008, the group conducts sophisticated, patient intelligence collection operations targeting government, technology, and research sectors globally. APT29 is known for advanced tradecraft, zero-day exploitation, and long-term persistence without detection. The group has targeted the Chinese government, technology, and research institutions as part of broader Russian intelligence collection operations.
Target Industries: Government agencies, technology companies, research institutions, defense contractors, diplomatic missions.
Primary Technologies Targeted: Government email systems, enterprise networks, cloud collaboration platforms, VPN infrastructure, and research computing systems.
Initial Access Vectors: Zero-day exploitation, spear-phishing with sophisticated social engineering, supply chain compromise, targeting of internet-facing services.
Key TTPs: Sophisticated malware development; lateral movement across government networks; long-term persistent access; credential harvesting; counter-forensics and anti-detection measures; use of legitimate services for C2.
Motivations: Strategic intelligence collection on Chinese government operations and decision-making; assessment of Chinese technology and defense capabilities; competitive intelligence on technology research; understanding of Chinese foreign policy priorities.
Examples: Operations targeting Chinese government ministries; surveillance of defense-related research; intelligence collection on technology development; operations against diplomatic communications infrastructure.
APT28 is a Russian military intelligence group operating under the GRU, active since at least 2007. The group conducts aggressive cyber espionage and cyber warfare operations targeting government, defense, technology, and infrastructure sectors. APT28 is characterized by rapid vulnerability exploitation, aggressive reconnaissance, and coordinated campaigns supporting Russian strategic objectives. The group has targeted the Chinese military and technology sectors.
Target Industries: Government agencies, military research, defense contractors, technology companies, telecommunications.
Primary Technologies Targeted: Military communication systems, government networks, defense research infrastructure, and technology development systems.
Initial Access Vectors: Spear-phishing with malicious attachments, exploitation of public-facing applications, targeting of military and defense research networks.
Key TTPs: Aggressive reconnaissance of target networks; rapid malware deployment; credential theft; lateral movement across military networks; document and research exfiltration; coordinated multi-stage attacks.
Motivations: Intelligence collection on Chinese military modernization and capabilities; assessment of Chinese defense doctrine; understanding of military technology development; competitive intelligence supporting Russian military planning.
Examples: Operations against Chinese military research institutions; targeting of defense contractors developing military systems; intelligence collection on military modernization programs.
Lazarus Group is a North Korean state-sponsored threat actor operating under the Reconnaissance General Bureau, active since at least 2009. The group is uniquely characterized by a dual operational mandate combining strategic cyber espionage with large-scale financially motivated cybercrime. Lazarus targets financial institutions, cryptocurrency exchanges, defence organizations, and technology companies globally. The group’s operations directly support North Korean state objectives, including sanctions evasion, intelligence collection, and revenue generation for state activities, making it one of the most versatile and consequential state-linked threat actors worldwide.
Target Industries: Financial institutions, cryptocurrency exchanges, defence contractors, aerospace organizations, technology companies, government agencies.
Primary Technologies Targeted: Banking systems, cryptocurrency platforms, SWIFT financial infrastructure, enterprise networks, supply-chain software, internet-facing services.
Initial Access Vectors: Spear-phishing with weaponized documents or malicious links; exploitation of internet-facing services; software supply-chain compromise; manipulation of software update mechanisms.
Key TTPs: Credential harvesting through phishing; lateral movement using legitimate administrative tools; persistence via backdoor implants; supply-chain compromise; cryptocurrency theft; targeting of high-value financial and strategic data repositories.
Motivations: Sanctions evasion through cryptocurrency theft and financial fraud; acquisition of military and strategic intelligence; collection of defence-related technology and intellectual property; generation of revenue to fund state activities.
Examples: Theft operations against cryptocurrency exchanges; intrusions into global financial institutions via SWIFT network manipulation; campaigns targeting defence contractors and aerospace organizations; high-profile destructive attacks against strategic targets.
Turla is a highly sophisticated Russian state-sponsored cyber espionage group widely attributed to the Federal Security Service (FSB), active for over a decade. The group specializes in long-term covert access to high-value networks, focusing on strategic intelligence collection related to foreign policy, defence planning, and geopolitical developments. Turla is consistently regarded as one of the most technically advanced espionage actors globally, distinguished by its use of covert communication channels, anti-detection techniques, and complex custom malware frameworks to maintain a persistent, undetected presence within targeted environments.
Target Industries: Government agencies, diplomatic institutions, defence organizations, research entities, international policy organizations, strategic technology research institutions.
Primary Technologies Targeted: Email and communications systems, enterprise networks, diplomatic infrastructure, satellite communications, VPN, and proxy infrastructure.
Initial Access Vectors: Spear-phishing emails with malicious attachments; exploitation of software vulnerabilities; use of compromised credentials; targeting of internet-facing services.
Key TTPs: Credential harvesting; lateral movement and network reconnaissance; long-term covert access maintenance; encrypted command-and-control infrastructure; system log manipulation; leveraging compromised satellite communications and proxy networks to obscure operational origin.
Motivations: Strategic intelligence collection on foreign policy and diplomatic activities; surveillance of defence planning and military strategy; monitoring of geopolitical research and international negotiations; acquisition of sensitive government and institutional communications.
Examples: Long-term infiltration of government and diplomatic networks across multiple regions; campaigns targeting geopolitical research organizations and international policy institutions; surveillance operations against defence ministries and research laboratories; covert monitoring of foreign policy communications over extended periods.
Sidewinder is an India-linked cyber espionage group suspected of operating under Indian state-sponsored direction (medium-high confidence attribution). Active since at least 2012, the group conducts political and military espionage supporting Indian national defense and foreign policy objectives. While the group’s primary mandate covers intelligence collection on Pakistani military and government operations, confirmed secondary targeting of China focuses on military modernization, defense technology development, and government strategic planning—reflecting India’s regional geopolitical competition with China. The group is characterized by sophisticated document-based exploits, multi-layer payload obfuscation, and geographic IP filtering on command-and-control infrastructure.
Target Industries: Government agencies and ministries, military and defense organizations, maritime and naval institutions, nuclear energy organizations, aviation, telecommunications, financial institutions, legal firms, and economic policy organizations.
Target Technologies: Microsoft Office document vulnerabilities (RTF and DOCX exploit chains), government email systems, Android mobile platforms, VPN infrastructure, maritime port management systems, and nuclear facility administrative networks.
Initial Access: Spear-phishing delivering DOCX or RTF files exploiting Microsoft Office RCE vulnerabilities disguised as government advisories and military briefings, Android malware distributed via legitimate-appearing APKs, government website cloning for credential phishing.
Key TTPs: Organization-branded decoy documents themed around government and military issues, DLL sideloading for defense evasion, multi-layer payload obfuscation with unique per-file encryption keys, anti-bot geographic IP filtering restricting payload delivery to targeted regions, living-off-the-land techniques, cloud platform abuse for C2, KernelCallBackTable injection, Pakistan Standard Time zone checks embedded in malware to confirm target geographic context.
Motivations: Primary mandate covers intelligence collection on Pakistani military and government operations; secondary targeting of China reflects intelligence collection on military modernization, defense technology development, and government strategic planning supporting Indian regional geopolitical competition with China.
Various hacktivist and state-adjacent groups with unclear attribution targeting Chinese government and surveillance infrastructure
Smaller, less formally attributed operations from Hong Kong-based and Tibetan independence-linked groups conduct sporadic targeting of Chinese government networks and surveillance infrastructure. Attribution remains challenging due to deliberate false-flag operations and operational security practices, but the suspected involvement of foreign intelligence services supporting Hong Kong and Tibetan activism cannot be excluded.
Target Industries: Government agencies, public security infrastructure, surveillance systems.
Primary Technologies Targeted: Government networks, surveillance systems, public security databases.
Initial Access Vectors: Exploitation of exposed government systems, supply chain compromise of surveillance vendors, and watering hole attacks.
Key TTPs: Website defacement, data exfiltration, denial of service attacks, and infrastructure disruption.
Motivations: Activism supporting Hong Kong autonomy; Tibetan independence advocacy; opposition to Chinese government surveillance; political messaging and awareness raising.
Geographic Focus: Hong Kong and Tibetan autonomous regions represent primary operational focus, with secondary targeting of central government surveillance and control infrastructure.
APT-C-01 is an unattributed cyber espionage group with a targeting profile consistent with Southeast Asian or Taiwan-linked intelligence tasking. The group conducts long-duration strategic intelligence collection against the Chinese government, military, and maritime organizations with confirmed sustained operations since at least 2007. Active resurgence in December 2024 indicates ongoing state-level resource backing. The group is characterized by sophisticated website cloning for phishing infrastructure, automatic malicious payload delivery mechanisms, and extensive use of cloud platforms for command-and-control and data exfiltration.
Target Industries: Government agencies and ministries, military and defense organizations, maritime and naval institutions, scientific research institutions, and academic organizations.
Target Technologies: Government email systems and web portals, phishing-cloned official government websites, and endpoint environments receiving legitimate-appearing downloads.
Initial Access: Phishing operations using cloned official government and institutional websites, victims directed to convincing replicas that trigger automatic download of malicious payloads. December 2024 campaign delivered Sliver RAT via this mechanism. Earlier campaigns used legacy Poison Ivy RAT shellcode variants and ZxShell via spear-phishing and watering hole attacks.
Key TTPs: Official website mimicry for phishing infrastructure, automatic payload download triggered on page visit, cloud storage abuse for C2 and exfiltration, multi-layer infrastructure for anti-attribution, long operational persistence with confirmed multi-year dwell times.
Motivations: Long-duration strategic intelligence collection against the Chinese government, military, and maritime organizations, political and military intelligence acquisition, government policy data, and military documents theft.
APT-C-00 is a Vietnamese state-sponsored cyber espionage group assessed with high confidence as operating on behalf of the Vietnamese state intelligence services. Operating hours and infrastructure consistently align with Vietnamese business hours and Vietnamese-language tooling. The group conducts strategic intelligence collection explicitly aligned with Vietnam’s national security and economic development interests, with China confirmed as the primary target geography. Vietnam’s sustained geopolitical competition with China over South China Sea territorial rights, trade interests, and technology access creates a direct and ongoing intelligence collection mandate. The group’s January 2025 targeting of Chinese cybersecurity researchers using GitHub as an infection vector reflects the intent to compromise network defenders and undermine China’s defensive cyber capability.
Target Industries: Cybersecurity research and technology companies, government agencies and ministries, large technology enterprises, organizations participating in China’s “Xinchuang” domestic IT self-sufficiency ecosystem, aviation and maritime sectors, manufacturing, and financial services.
Target Technologies: GitHub development infrastructure poisoned Visual Studio project files and malicious repositories targeting security professionals, Chinese red team tools including Cobalt Strike plugins, Windows DLL loading mechanisms via DLL hollowing (xpsservices.dll), Microsoft 365 cloud environments, Notion cloud note-taking platform for C2, China’s Xinchuang domestic hardware and software platforms.
Initial Access: GitHub supply chain poisoning, distributing backdoored security tools, Cobalt Strike plugins, and malicious Visual Studio project files targeting Chinese security professionals. Social engineering impersonation of security professionals from Chinese FinTech companies. Spear-phishing with malicious Office documents. Watering hole attacks against websites frequented by Chinese government and enterprise personnel.
Key TTPs: DLL hollowing overwriting memory within legitimate xpsservices.dll system library for silent payload execution under trusted process name, Notion cloud platform as C2 channel embedding instructions within Notion pages, registry persistence and scheduled task creation, supply chain poisoning via trusted developer platforms targeting security research community, Xinchuang domestic IT ecosystem targeting for supply chain attack capability, active credential harvesting against Microsoft 365 environments.
Motivations: Strategic intelligence collection supporting Vietnam’s national security and economic development interests, South China Sea competition and territorial intelligence, trade interest protection, technology access acquisition, direct targeting of China’s defensive cyber capability through security researcher compromise, and development of supply chain attack capability against China’s nationally strategic technology infrastructure.
Malware and Tools: Denis backdoor, Ratsnif network trojan, Backdoor.MacOS.OCEANLOTUS (macOS variant), Cobalt Strike (backdoored plugin variant), custom Notion-C2 implant, DLL hollowing loaders, JavaScript-based backdoors, macro-enabled Office document droppers, browser credential harvesters.
SinisterEye is an unattributed cyber espionage group with confirmed Chinese-speaking operators and analytically contested attribution. Targeting is overwhelmingly concentrated on entities within China itself foreign diplomatic organizations, foreign companies, and foreign nationals operating inside Chinese territory. The group’s confirmed ISP-level or backbone-level interception capability over ChinaNet (AS4134) raises two competing hypotheses: either a Chinese domestic intelligence operation surveilling foreign entities operating in China, or a foreign state actor with extraordinarily sophisticated China network infrastructure penetration. Neither attribution is publicly confirmed, and this analytical uncertainty should be explicitly noted in any assessment.
Target Industries: Foreign diplomatic organizations and embassies operating in China, foreign companies with China-based offices (defense, technology, trade sectors), international academic community, foreign nationals in China, defense aviation sector, government bodies with China-based operational presence.
Target Technologies: Windows operating system update mechanisms, specifically Windows software update traffic intercepted and manipulated via adversary-in-the-middle to deliver WinDealer, Android mobile devices via SpyDealer, C2 infrastructure utilizing a randomized pool of approximately 48,000 IP addresses drawn from legitimate Chinese domestic IP space and rotating constantly.
Initial Access: Adversary-in-the-middle attacks confirmed capability to intercept network traffic at ISP-level or backbone-level within AS4134 (ChinaNet). Legitimate software update requests from victim machines are intercepted in transit, with server responses replaced by a malicious payload before reaching the victim. Requires no user action, no phishing, no clicked link, no endpoint vulnerability exploitation, one of the most passive and difficult-to-detect initial access mechanisms globally. Confirmed also via malicious mobile applications distributing SpyDealer for Android.
Key TTPs: Man-on-the-side (MOTS) attack methodology, passive traffic interception with selective payload injection for specific targets only, all other traffic passing unmodified. WinDealer’s 48,000-IP randomized C2 pool selecting IPs from legitimate Chinese ISP address blocks, making C2 traffic visually and statistically indistinguishable from ordinary domestic traffic. Active Directory reconnaissance post-compromise. Credential harvesting and sensitive document exfiltration. SpyDealer Android malware for mobile device surveillance of targeted individuals.
Motivations: Surveillance and intelligence collection targeting foreign entities operating within China’s foreign diplomatic missions, international companies with China-based offices, academics, and foreign nationals resident in China. Exclusive focus on foreign entities inside Chinese borders, combined with ISP-level interception capability consistent with counterintelligence mandate: monitoring what foreign governments and organizations conduct inside China’s territory.
Malware and Tools: WinDealer (Windows backdoor primary implant), SpyDealer (Android surveillance malware), custom passive MOTS injection framework operating at network infrastructure level.
Attribution Confidence: High confidence for targeting and TTPs; Low confidence for national attribution. Analytical uncertainty explicitly noted could represent either Chinese domestic intelligence operation or foreign state actor with sophisticated China network infrastructure penetration.
NetDragon Botnet
NetDragon is a purpose-built botnet malware first identified in October 2024, specifically engineered to compromise Feiniu fnOS network-attached storage devices, a platform predominantly deployed by Chinese home users and small-to-medium businesses. By late January 2026, command-and-control panel telemetry confirmed over 1,143 bots simultaneously online with total infections approaching 1,500 devices, all exclusively Feiniu hardware. Geographic distribution confirms China as the primary impact zone, with secondary victims in the United States, Singapore, and Australia. Attribution is to unknown criminal actors rather than state-sponsored groups, but its confirmed impact on Chinese domestic infrastructure classifies it as a direct threat impacting China.
Intelligence Toolset
A suite of 42 specialized cyber-attack tools was deployed against China’s National Time Service Center in an alleged multi-year sustained operation. The scale of the toolset, 42 distinct specialized components, indicates a well-resourced, professionally organized operation with specific, pre-planned collection objectives rather than opportunistic exploitation.
National time infrastructure compromise represents a systemic, cascading risk. Financial markets, telecommunications switching, power grid control systems, and military communications all depend on a trusted, accurate time reference. A compromised time service can induce failures across these dependent systems without those systems generating alerts attributable to external attack, making this one of the highest-leverage, lowest-visibility infrastructure attack categories that exists.
Asian Winter Games Infrastructure Targeting
The attack techniques used against the Asian Winter Games infrastructure included arbitrary file read vulnerability exploitation, SQL injection attacks, HTTP X-Forwarded-For spoofing, mass port scanning, and targeted application vulnerability exploitation, a toolkit consistent with the broad offensive techniques used by advanced persistent threat actors across all nation-state categories. Cloud-based hosting infrastructure from providers, including Digital Ocean, was used to obfuscate attack origins, with servers in Europe and Asia leveraged as intermediate nodes.
Targeted Infrastructure: Event management systems, arrival and departure management, payment infrastructure, and, per Chinese authorities’ broader claims, provincial energy, transportation, water resources, and communications infrastructure.
AI-Accelerated Offensive Operations Against Chinese Systems
The rapid integration of generative AI tools into offensive cyber operations represents a structural acceleration of the threat that China faces from foreign actors. The use of AI for tailored phishing content generation in fluent Mandarin, accelerated vulnerability research against Chinese infrastructure, synthetic impersonation of Chinese officials and institutions, and malware development represents a capability expansion that previously required significantly greater human resources. As China’s adversaries adopt these tools, the pace, quality, and targeting precision of operations against Chinese systems will increase in proportion. This capability gap is of particular concern for smaller government agencies, regional infrastructure operators, and educational institutions, where domestic cybersecurity maturity remains uneven compared to centrally managed national systems.
Semiconductor and Technology Program Targeting
As China accelerates investment in indigenous semiconductor manufacturing, AI development, quantum computing, and aerospace technology in response to Western export controls, these programs become increasingly high-value intelligence collection targets for foreign actors seeking to assess China’s technological advancement pace and acquire research that reduces their own development timelines. The technology decoupling driven by semiconductor export restrictions simultaneously increases the strategic value of China’s domestic programs and increases the intelligence collection pressure they face, a compounding vulnerability where China’s most strategically important technology investments are simultaneously its most heavily targeted. Research institutions, state-owned enterprises in strategic technology sectors, and any organization involved in dual-use technology development should assess themselves as primary foreign intelligence targets.
Critical Infrastructure Regulatory Compliance as an Attack Intelligence Opportunity
China’s Cyberspace Administration’s new National Cybersecurity Incident Reporting Management Measures, effective November 1, 2025, require all network operators in China, including foreign entities operating domestically, to report cybersecurity incidents within four hours when they meet defined thresholds, with mandatory disclosure of ransomware details, including ransom amount, payment method, and deadline. While this framework serves as a genuine domestic security resilience measure, the centralization of real-time incident data also creates a comprehensive picture of active foreign operations against Chinese network information of significant strategic intelligence value. Foreign actors aware of this reporting framework may adapt their operations to remain below mandatory disclosure thresholds, increasing the stealth requirements for sustained collection operations against Chinese targets.
Contractor Ecosystem Operational Security Risk
China’s private sector contractor ecosystem operating as an intermediary layer between state intelligence agencies and offensive cyber operations represents an active targeting surface for foreign intelligence services seeking intelligence on Chinese cyber operations, personnel, and active campaigns without needing to directly penetrate state infrastructure. Adversaries have demonstrated a willingness to target contractor organizations directly as an alternative pathway into Chinese operational intelligence, exploiting the fact that private firms typically operate with weaker internal security postures than state intelligence agencies themselves.
The scale of exposure through this vector was made visible by prior contractor data exposure events, which revealed specific targeting lists, operational methods, internal communications, and evidence of ongoing campaigns. Each private contractor operating within China’s cyber ecosystem represents a potential breach point, a node where internal data, operational details, and personnel information can be accessed by foreign actors who target the contractors themselves rather than attempting to penetrate Chinese state intelligence infrastructure directly. As this contractor model expands in scale and scope, the structural exposure it creates for China’s operational security expands proportionally, making contractor ecosystem security an increasing priority for national cyber defense planning.
Supply Chain Compromise as Inbound Attack Vector
Supply chain compromise represents a primary and escalating inbound threat vector targeting Chinese government, defense, and technology organizations. Foreign advanced persistent threat actors increasingly leverage upstream software developers, hardware manufacturers, and managed service providers as indirect pathways into hardened Chinese government networks, exploiting the inherent trust extended to vendor software and hardware to bypass perimeter defenses.
1. Chinese Software Development Firms as Intelligence Targets:
2. Managed Service Provider and Cloud Infrastructure Compromise:
3. Hardware Supply Chain Infiltration:
4. Open-Source Software and Third-Party Library Compromise:
China is the largest country in East Asia and one of the central geopolitical actors shaping the security environment of the Asia-Pacific region. The region is becoming the epicenter of geopolitical competition for the remainder of the 21st century, with China’s rise to superpower status fundamentally reshaping the regional and global balance of power. China’s economic expansion, technological ambitions, and rapidly modernizing military capabilities have elevated the country to a position where it increasingly challenges the established international order and the influence of the United States and its allies.
At the same time, China faces a complex security environment characterized by numerous territorial disputes, strategic rivalries, and internal economic pressures. China’s domestic economic slowdown, demographic pressures, and ongoing efforts by Western countries to diversify supply chains away from China introduce additional uncertainty into Beijing’s strategic calculations, which may incentivize China to adopt a more assertive posture abroad while simultaneously tightening political and informational control domestically.
China also faces ongoing strategic competition with the United States, which has manifested in trade disputes, semiconductor supply chains, military posturing in the Indo-Pacific, and competition over emerging technologies. The United States has strengthened security partnerships with regional allies, including Japan, South Korea, Australia, and the Philippines, while promoting multilateral initiatives, such as the QUAD and AUKUS, which China perceives as attempts to counterbalance its influence.
Relations between China and several neighbours remain strained, including long-standing border tensions with India, historical disputes with Japan, and complex relations with Russia that have evolved into a strategic partnership. China’s growing alignment with Russia, particularly since the outbreak of the war in Ukraine, signals the emergence of a more coordinated Eurasian geopolitical bloc that could challenge Western influence in both Europe and Asia.
As geopolitical competition intensifies, China’s strategic relationships and territorial disputes create persistent intelligence collection incentives for foreign state actors, with cyber operations representing the primary tool through which adversaries monitor Chinese policy decisions, military modernization, and economic development.
The Philippines: Intense confrontations at Scarborough and Sabina shoals in 2024 and 2025 indicate Beijing has no intention of easing pressure in the area. China is also asserting pressure on the Philippines around the Spratly Islands, particularly at Second Thomas Shoal, islands on which the Philippines are determined to maintain a military presence. China has demonstrated willingness to use force against Philippine resupply vessels operating within the country’s exclusive economic zone, further escalation risks triggering the U.S.-Philippines Mutual Defense Treaty.
Taiwan: Taiwan remains the most sensitive geopolitical flashpoint in East Asia. The Chinese government considers the island a breakaway province and has repeatedly stated that reunification is inevitable, reserving the right to use force if necessary. Beijing has significantly increased military pressure through large-scale naval and air exercises, frequent incursions into Taiwan’s Air Defense Identification Zone, and operations designed to test Taipei’s response capabilities. Taiwan continues to strengthen its defense posture with increased military spending and closer security cooperation with the United States. Washington maintains strategic ambiguity, but has expanded arms transfers, military training and political support, and any attempt by China to impose a blockade, conduct coercive operations, or launch a military assault would likely trigger a severe regional crisis and draw in the United States and its allies. Any escalation would almost certainly be preceded and accompanied by large-scale cyber operations targeting government institutions, military systems, and critical infrastructure across the region.
Japan: Tensions between China and Japan have intensified around the disputed Senkaku/Diaoyu Islands in the East China Sea, where both countries claim sovereignty and regularly deploy coast guard and naval vessels. Chinese coast guard ships have increasingly entered waters around the islands and pursued Japanese fishing vessels, prompting repeated protests from Tokyo. The Taiwan contingency is viewed in Tokyo as a direct security threat because of geographic proximity and the potential to disrupt critical sea lanes, threaten Japanese territory and U.S. bases in Japan, and draw Tokyo into conflict through its alliance obligations. In response, Japan has strengthened patrols, expanded coast guard capabilities, and accelerated defense reforms. The recent diplomatic spat was triggered when new Japanese Prime Minister Sanae Takaichi declared that a “Taiwan contingency is a Japan contingency” and that Tokyo would “not rule out any option, including direct military involvement,” breaking from Japan’s strategic ambiguity. As tensions continue to rise, the risk of incidents at sea or in the air is increasing, with cyber operations and information campaigns likely playing significant roles in the early stages of any crisis.
Businesses and organizations operating in China or connected to Chinese supply chains therefore, face an increasingly complex risk environment involving cyber espionage, regulatory pressure, geopolitical tensions, and potential disruptions linked to broader regional conflicts.
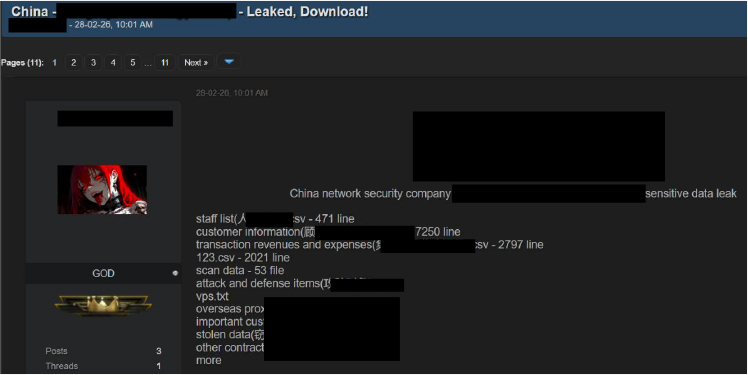
On Feb 26, 2026, a post identified on an underground forum claims a data leak involving a network security company in China. The threat actor alleges that multiple internal files have been exposed and shared, including staff lists, customer information records, transaction revenue and expense data, scan results, attack and defense-related materials, VPS details, overseas proxy IP lists, important customer lists, and contractual documents. The post indicates that the leaked content is distributed in various formats such as CSV, RAR, XLSX, and ZIP archives, suggesting potential exposure of internal operational and business-related data. At the time of analysis, the authenticity and scope of the claimed data leak could not be independently verified.
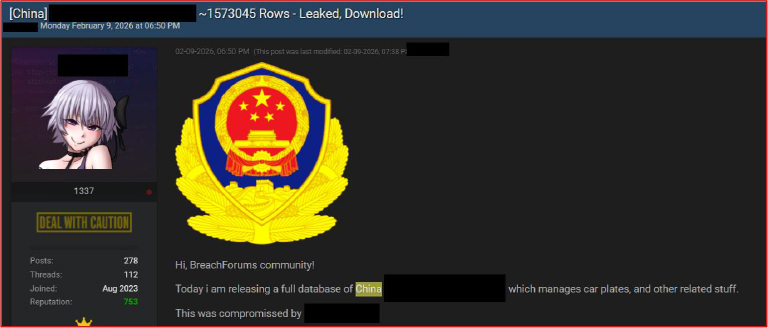
On Feb 9, 2026, a post identified on an underground forum advertises the leak of a database allegedly associated with a vehicle registration management system in China. The threat actor claims the dataset contains approximately 1,573,045 records and has been made available for download. Based on the description provided in the post, the compromised database is purportedly linked to a system responsible for managing vehicle license plates and related administrative information. At the time of analysis, the authenticity of the leaked dataset and the extent of the compromise could not be independently verified.
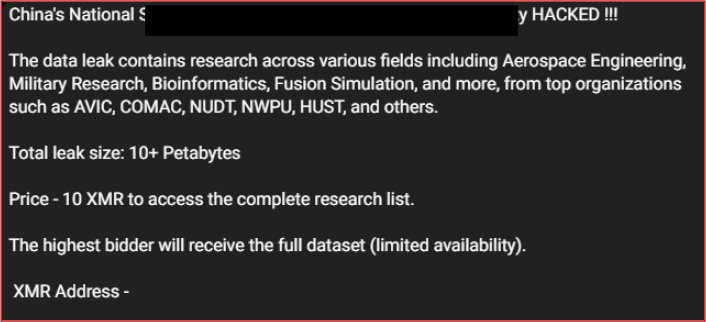
On Feb 6, 2026, a post on an underground Telegram channel claims that the National Supercomputing Center (NSCC) research facility in China has been compromised. The threat actor alleges that the breach resulted in the leakage of over 10 petabytes of research data spanning multiple advanced research domains, including aerospace engineering, military research, bioinformatics, and fusion simulation. The post further claims that the leaked data involves research associated with several prominent Chinese institutions and organizations, including Aviation Industry Corporation of China (AVIC), Commercial Aircraft Corporation of China (COMAC), National University of Defense Technology (NUDT), Northwestern Polytechnical University (NWPU), and Huazhong University of Science and Technology (HUST). The actor is reportedly offering access to the complete research dataset for 10 XMR (Monero), with the claim that the highest bidder will receive the full dataset due to limited availability. At the time of analysis, the authenticity of the breach and the scale of the alleged data leak could not be independently verified.
On Feb,6, 2026, a large dataset containing over 120,000 entries related to China Bank was processed and analyzed in an underground telegram channel. The data appears in a structured log or indexed format, indicating automated extraction or text processing. This dataset can be used for tasks such as data analysis, information retrieval, or monitoring financial-related records.

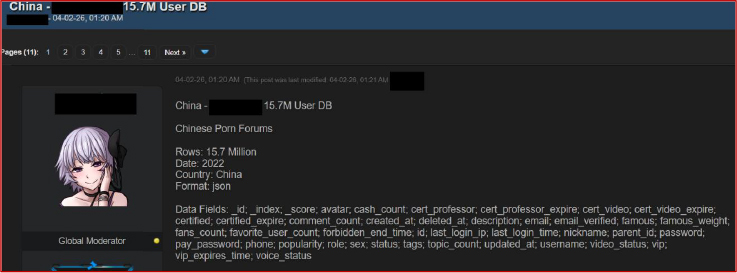
On Feb 4, 2026, a post on an underground forum advertises the sale of a database allegedly associated with Chinese porn forums in China. According to the listing, the dataset reportedly contains approximately 15.7 million user records dating back to 2022, with the data provided in JSON format. The post indicates that the database includes multiple user-related fields such as usernames, email addresses, passwords, nicknames, login IP information, account status, and other profile-related attributes. At the time of analysis, the authenticity and origin of the dataset could not be independently verified.
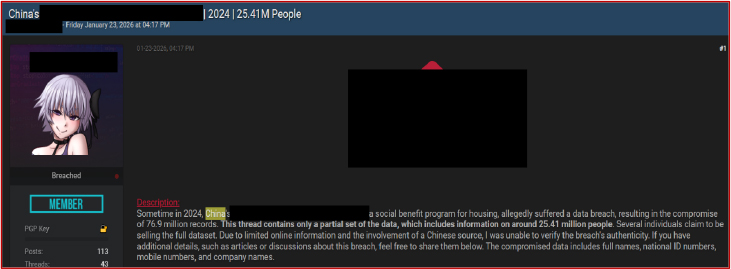
On Jan 21, 2026, a post identified on an underground forum claims a data breach associated with a social benefit housing program in China. According to the threat actor, the incident allegedly occurred in 2024, resulting in the compromise of approximately 7.69 million records. The forum thread reportedly contains only a partial dataset, while the full database is claimed to include information related to around 25.41 million individuals. The exposed dataset is said to contain personally identifiable information (PII) such as full names, national ID numbers, and mobile phone numbers. At the time of analysis, the authenticity of the breach and the actor’s claims could not be independently verified.
The implementation of China’s revised Cybersecurity Law represents a sustained, year-long elevated risk period rather than a discrete event. The amendments significantly expand state surveillance obligations and impose stricter controls over cross-border data flows creating two parallel risk dimensions simultaneously. Domestically, organizations failing to meet the new compliance thresholds become vulnerable to regulatory penalty and potential extortion by actors aware of their non-compliance status. For foreign firms operating within China, the tightened data localization and cross-border transfer restrictions introduce a compounding exposure, both regulatory risk from Chinese authorities and heightened espionage interest from state-aligned actors seeking to exploit the transition period before compliance architectures are fully operational. We assess this as a continuous background risk elevation throughout 2026 rather than a point-in-time event.
The Two Sessions — NPC & CPPCC (March 2026) China’s most strategically significant annual political gatherings the National People’s Congress and the Chinese People’s Political Consultative Conference, represent the highest-priority intelligence collection window in China’s domestic political calendar. Historically, these sessions are confirmed targets for foreign intelligence operations seeking advance visibility into economic policy decisions, regulatory direction, and strategic planning deliberations. In 2026, the Two Sessions carry elevated significance beyond prior years due to the formal agenda items expected to address AI governance alignment with national data laws, a policy area of direct interest to foreign technology intelligence operations. Communications infrastructure serving Beijing’s government district, delegation networks, and associated policy advisory bodies should all be treated as operating under active foreign surveillance pressure during this period.
International Conferences on Cybersecurity & AI (March 4–5, 2026 — Beijing/Macau) A concentrated gathering of cybersecurity leadership and AI practitioners focusing on blockchain-integrated security architectures, threat modeling methodologies, and AI applications in sensitive domains. Events of this nature attract both the intellectual property and the personnel connections that state-aligned espionage actors actively seek, making attendee devices, conference networks, and organizer infrastructure elevated-risk targets for credential harvesting and targeted intrusion operations during and immediately surrounding the event window.
China Beijing Attractions Expo (March 19–21, 2026): This gathering of over 600 tourism and digital entertainment companies represents a concentration of intellectual-property-rich organizations in a relatively lower-security conference environment. Digital entertainment platforms, content distribution technology, and tourism management systems are all confirmed areas of state-aligned IP theft interest, and the convergence of these many organizations in a single event creates an efficient targeting environment for actors seeking to compromise multiple entities through a single well-positioned operation.
Wenzhou International Hardware and Lock Exhibition (May 29, 2026): The focus of this exhibition on modern smart security technologies — including connected lock systems, access control infrastructure, and IoT-integrated physical security platforms creates a specific and underappreciated risk surface. IoT device vulnerabilities and physical security system architecture details represent high-value targets for actors seeking to identify exploitable weaknesses in the smart infrastructure being deployed across China’s commercial and residential sectors. Demonstration equipment, vendor technical documentation, and the connected infrastructure supporting the exhibition itself are all assessed as elevated-risk assets during this window.
Security China 2026 (November 3, 2026 — Beijing): As China’s largest public safety and intelligent security technologies exhibition, this event draws a concentration of organizations developing and deploying AI-driven surveillance, facial recognition, smart city monitoring, and physical security infrastructure. The dual-use nature of these technologies simultaneously civilian security tools and state surveillance instruments, makes this event a high-priority intelligence collection target for foreign state actors seeking visibility into China’s AI-driven security infrastructure development trajectory. Vendor technical presentations, system architecture demonstrations, and the procurement discussions occurring within this event represent significant intelligence value to foreign state actors monitoring China’s internal security technology advancement.
Industrial Cybersecurity Initiative Deadline (End of 2026) By the end of 2026, over 45,000 industrial companies across China are expected to have implemented enhanced ransomware protection frameworks under national industrial cybersecurity directives. The transition period leading up to this deadline represents a structurally elevated risk window organizations actively implementing new security architectures are simultaneously operating with partially migrated, incompletely tested environments that present increased attack surface compared to their steady-state posture. Ransomware operators and state-aligned actors targeting industrial control systems are both assessed as likely to increase operational tempo against industrial sector organizations during this compliance transition period, deliberately timing attacks to exploit the window before enhanced protections reach operational maturity.
New Vehicle Data Export Guidelines Compliance Audits (Q1/Q2 2026) The introduction of strict new compliance audit requirements for vehicle data exports creates an elevated espionage risk environment for automakers and connected-vehicle technology suppliers operating in China. The guidelines impose detailed data handling obligations covering connected vehicle telemetry, passenger behavioral data, and geographic mapping information collected by autonomous and semi-autonomous vehicles, all categories of data with confirmed strategic intelligence value to foreign actors. Organizations undergoing compliance audits, managing data localization infrastructure, and developing connected-vehicle platforms should assess themselves as active espionage targets during this period, as foreign state actors seek intelligence on both China’s connected-vehicle data holdings and the technical architecture being deployed to protect them.
Telecommunications and Energy Foreign state-aligned actors consistent with the long-dwell methodologies documented across the Iranian, North Korean, Vietnamese, and unattributed threat clusters in this report are assessed to be maintaining persistent footholds inside Chinese telecommunications and energy networks for intelligence collection and potential pre-positioning purposes. Simultaneously, foreign-invested firms operating within these sectors face elevated espionage risk from state-aligned actors seeking access to proprietary technologies, operational data, and strategic planning information. Organizations across both categories should operate under an assumption of active targeting and deploy continuous monitoring rather than perimeter-first defensive postures.
Cloud Service Providers China’s regulatory push toward decentralized, domestically hosted cloud infrastructure is creating an expanding attack surface within the cloud services sector. Smaller regional cloud providers now rapidly onboarding new enterprise clients under data localization mandates are operating with comparatively weaker security architectures than the major established platforms, while simultaneously taking on responsibility for increasingly sensitive organizational data. This combination of rapidly expanding client bases, immature security postures, and high-value data holdings makes smaller domestic cloud providers a priority target for both financially motivated actors and state-aligned espionage groups seeking to leverage a single provider compromise into simultaneous access across all of their clients.
Healthcare and Life Sciences: A series of international conferences on healthcare, biotechnology, and data analytics scheduled across Beijing, Shanghai, and Suzhou during April and June 2026 creates concentrated periods of elevated risk for China’s healthcare and life sciences sector. Research data theft targeting pharmaceutical development programs, genomic databases, clinical trial data, and biotechnology intellectual property represents a confirmed and high-priority collection mandate for multiple foreign state-aligned actors. The convergence of international researchers, domestic institutions, and commercially sensitive data in conference environments typically operating with a lower security posture than institutional networks create efficient targeting opportunities that state-aligned espionage actors are assessed as actively planning around.
China’s 2025–2026 cyber threat environment is defined by sustained ransomware pressure, rapid exploitation of both legacy and zero-day vulnerabilities, and highly mature state-linked operations capable of long-term persistence within critical infrastructure and supply chains. Foreign state-sponsored actors from Iran, Russia, North Korea, Vietnam, and India, alongside unattributed intelligence services, demonstrate sustained, patient targeting of the Chinese government, defense, and technology sectors, with dwell times and operational sophistication that elevate systemic risk well beyond isolated incidents. At the same time, large-scale data leak claims and targeted attacks on strategic national assets highlight continued inbound exposure. Overall, the landscape reflects a convergence of criminal, strategic, and geopolitical cyber activity, requiring resilience-focused defense, identity-centric security, and proactive threat hunting to mitigate long-dwell and high-impact compromise.
Strategic Recommendations
Operational Recommendations
Tactical Recommendations