

At CYFIRMA, we continuously monitor evolving cyber threats targeting enterprises and critical sectors. This report presents the discovery and in-depth analysis of a highly sophisticated, multi-stage post-exploitation framework observed targeting organizations in the Middle East and EMEA financial sectors. The threat actor leverages a legitimate, digitally signed Intel utility (IAStorHelp.exe) by abusing the .NET AppDomainManager mechanism, effectively turning a trusted binary into a stealthy execution container. This approach allows malicious code to be executed within a trusted environment. It bypasses conventional security controls without modifying the original signed binary. The level of sophistication, modular design, and operational discipline indicate capabilities consistent with advanced threat actors, demonstrating tradecraft comparable to mature offensive frameworks such as Cobalt Strike, Brute Ratel C4, and NightHawk, without sufficient evidence for direct attribution.
From a business and operational risk perspective, this threat introduces critical security gaps across multiple layers of enterprise defense. It bypasses traditional EDR and antivirus solutions through trusted binary abuse, JIT-based memory execution that avoids common API monitoring, and sandbox evasion using computational delays and constrained key derivation loops. Once command-and-control communication is established via Amazon CloudFront CDN infrastructure, attackers gain full remote access, exposing sensitive data including credentials, financial records, and intellectual property. The use of domain fronting renders standard network blocking ineffective, requiring advanced inspection mechanisms. Additionally, the malware employs anti-forensic techniques that erase memory artifacts, making post-incident investigation extremely difficult. Any affected system should therefore be treated as fully compromised, with a high likelihood of lateral movement and domain-level access by the adversary. This framework represents a shift toward trusted execution abuse and in-memory operations, significantly reducing the effectiveness of traditional signature-based defenses.
This report provides a comprehensive technical and threat intelligence analysis of an advanced post-exploitation framework that leverages trusted execution paths within the Windows .NET ecosystem to evade detection and establish persistent access in enterprise environments. The attack demonstrates the abuse of the AppDomainManager mechanism to hijack application initialization within a legitimate signed binary, enabling stealthy execution without altering the original executable. By combining configuration-based execution, layered obfuscation, cryptographic protection, JIT-based shellcode deployment, and reflective in-memory loading, the framework represents a significant evolution in attacker tradecraft. The analysis within this report outlines the full attack lifecycle from initial access and execution to evasion, payload delivery, and command-and-control communication while mapping observed behaviors to real-world threat trends and advanced adversarial techniques.
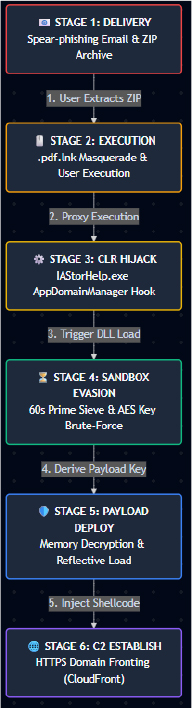
The attack progresses through six distinct stages, each engineered to bypass a specific layer of enterprise security controls. Stage 1 begins with spear-phishing delivery via a malicious ZIP archive containing all required components. In Stage 2, the user executes a disguised .pdf.lnk file, triggering trusted binary proxy execution of IAStorHelp.exe. Stage 3 leverages AppDomainManager hijacking via a malicious configuration file to force early execution of attacker-controlled code within the .NET CLR. Stage 4 implements dual-layer sandbox evasion through a 60-second computational prime sieve combined with a constrained AES key derivation loop. In Stage 5, the decrypted payload is reflectively loaded into memory, followed by JIT-based shellcode execution. Finally, Stage 6 establishes command-and-control communication using HTTPS domain fronting over CloudFront CDN infrastructure, enabling stealthy and resilient attacker control.
Icon Masquerading & Social Engineering
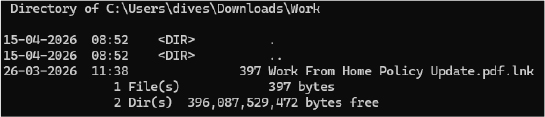
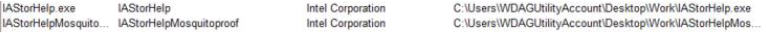
The infection chain begins with a spear-phishing email delivering a malicious ZIP archive containing six components: the signed Intel host binary (IAStorHelp.exe), a weaponized CLR configuration (IAStorHelp.exe.config), the malicious .NET DLL (IAStorHelpMosquitoproof.dll), an AES-encrypted payload blob (setting.yml), a LNK trigger (Work From Home Policy Update.pdf.lnk), and a benign decoy PDF. No automated dropper or exploit-based extraction was observed. The attack relies entirely on user-initiated ZIP extraction and manual LNK execution.
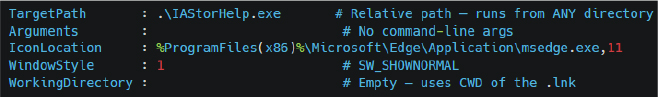
The LNK’s TargetPath uses relative path resolution (.\IAStorHelp.exe), with an empty WorkingDirectory, making the attack directory-agnostic. It executes from any extraction folder. The .NET CLR auto-discovers the co-located .config and DLL via standard assembly resolution, requiring no hardcoded paths, registry modifications, or environment variables. The entire kill chain is self-contained within the extraction directory.
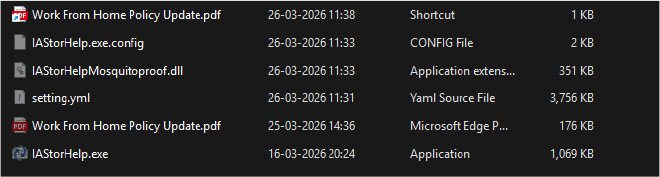
The LNK employs double-extension masquerading (.pdf.lnk) combined with dynamic icon resolution. Its IconLocation points to %ProgramFiles(x86)%\Microsoft\Edge\Application\msedge.exe,11, resolving to Edge’s PDF icon. Windows suppresses the .lnk extension by default, rendering the file visually identical to a legitimate PDF. Upon execution, the shortcut launches IAStorHelp.exe while simultaneously opening the decoy PDF to provide psychological distraction during background payload execution.
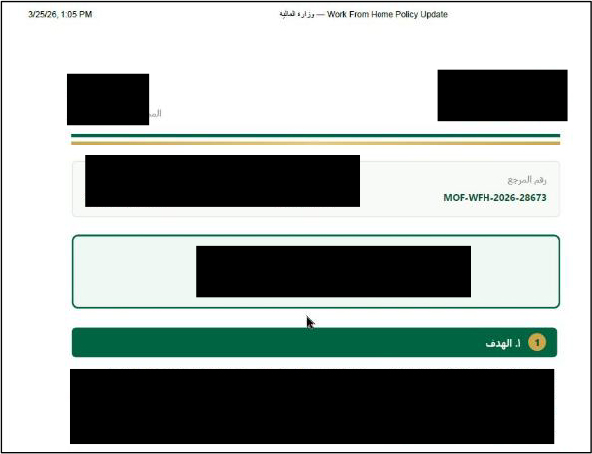
The decoy PDF is a professionally crafted Arabic-language document impersonating a Saudi government Ministry document. It bears official ministry branding. The document titled “Work From Home Policy Updates” cites Middle Eastern regional security conditions as justification for remote work, demonstrating contextually relevant social engineering. The production quality (correct Hijri calendar, authentic government formatting, proper Arabic typography) indicates native Arabic fluency and familiarity with Saudi institutional communications, consistent with a regionally-focused APT.
PE Analysis: Host Binary vs. Malicious DLL
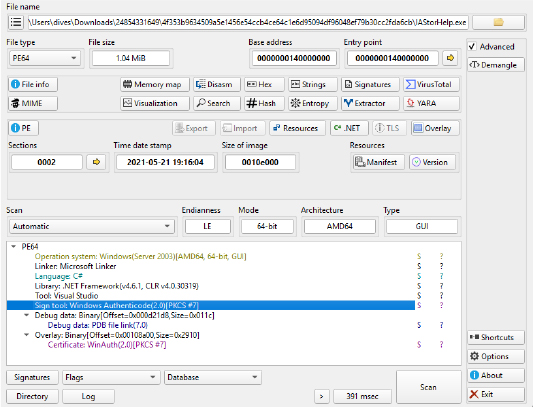
The following Detect It Easy (DIE) analysis screenshots compare the legitimate host binary with the malicious DLL. The contrast between the two is critical evidence for the investigation:
This screenshot proves the Intel utility is genuinely signed by Microsoft’s code-signing infrastructure, and security tools are explicitly configured to trust it, which is exactly what the attacker exploits.
DIE’s own heuristic engine flags this DLL as suspicious. It detects that the .NET constructor (the code that runs first when the DLL loads) has been deliberately obfuscated, a sign of malicious manipulation.
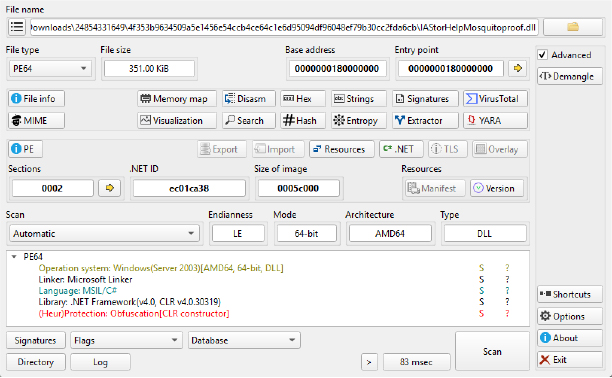
The legitimate IAStorHelp.exe is Authenticode-signed with a valid PKCS#7 certificate, while IAStorHelpMosquitoproof.dll is unsigned with an obfuscated CLR constructor. The attacker exploits the fact that the .NET CLR does NOT validate code-signing on assemblies loaded via AppDomainManager configuration, the signed host binary’s trust is inherited by the unsigned malicious DLL.
AppDomainManager Injection & Common Language Runtime (CLR) Hijacking
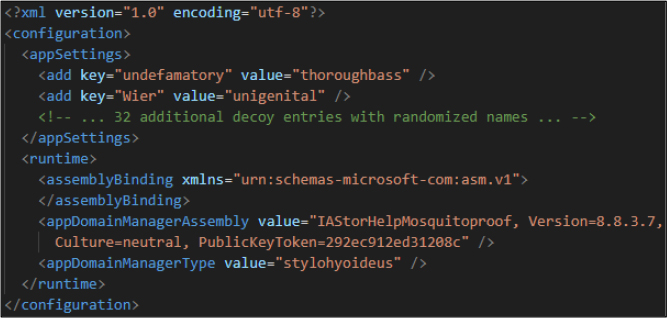
The attack leverages AppDomainManager hijacking through a malicious configuration file named IAStorHelp.exe.config, placed in the same Documents directory alongside the host binary IAStorHelp.exe. This co-location is critical because the .NET CLR automatically searches for a configuration file matching the pattern <executable_name>.config in the same directory as the executable during application startup, requiring no registry modifications, environment variable changes, or additional scripts to trigger the hijack. The config file was delivered inside the same ZIP archive as all other attack components, meaning it was already in position the moment the victim extracted the archive contents. By overriding the default .NET runtime behavior, this configuration forces the CLR to load and execute attacker-controlled code during the application’s initialization phase before any legitimate program logic is executed. Specifically, the config file contains a <runtime> block with two critical directives: an <appDomainManagerAssembly> tag pointing to IAStorHelpMosquitoproof.dll with a spoofed Version=8.8.3.7 and a fabricated PublicKeyToken=292ec912ed31208c, and an <appDomainManagerType> tag specifying stylohyoideus as the initialization class. Additionally, the file includes 32 fabricated <appSettings> entries using randomized dictionary-derived names such as “undefamatory” and “backstromite” to increase visual complexity and camouflage the malicious runtime directives during casual inspection. Every .NET application checks for a .config file at startup, and the attacker exploits this trusted mechanism by planting a poisoned config file that instructs the .NET runtime to load attacker code first, effectively hijacking the trusted Intel program before it even starts.
Entry Point Hook
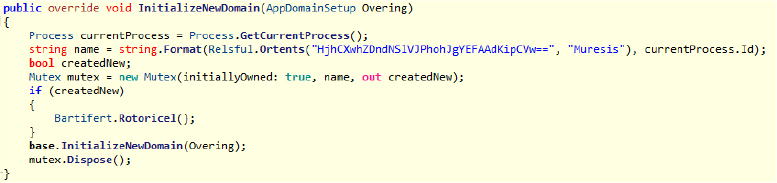
The execution flow is anchored in the stylohyoideus::InitializeNewDomain method, which overrides the default behavior of the AppDomainManager to establish an early execution foothold within the .NET runtime. This method is invoked automatically during the initialization of the application domain, allowing attacker-controlled code to run before the main application entry point. It implements a PID-scoped mutex mechanism to ensure single-instance execution, preventing redundant payload triggers within the same process. Upon successful initialization, it invokes the core orchestrator function, effectively launching the full multi-stage attack chain. This design ensures controlled, stealthy, and reliable execution, reinforcing persistence and minimizing detection during the early stages of compromise.
Evasion & Anti-Analysis Capabilities
String De-obfuscation Engine
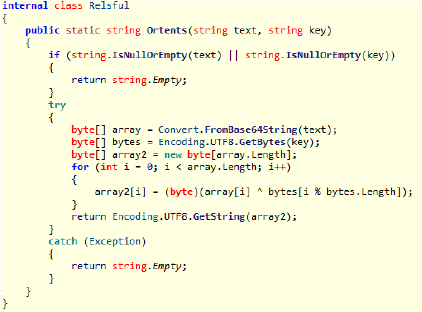
The method functions as a centralized string de-obfuscation engine, responsible for decoding all runtime strings within the malware assembly. It implements a layered approach where strings are first Base64-decoded, then processed using a repeating-key XOR cipher, and finally converted back into readable UTF-8 format. Instead of storing sensitive values such as file names (setting.yml) or command-and-control (C2) endpoints in plain text, the malware embeds them in an obfuscated form and only resolves them dynamically during execution. This ensures that static analysis tools and string extraction techniques are unable to reveal meaningful indicators. In simple terms, the malware keeps all important text “scrambled” and only decrypts it when required, using a lightweight XOR-based mechanism with a predefined key. By routing every string through this centralized function, the framework enforces consistent obfuscation across the entire codebase, significantly increasing resistance to reverse engineering and signature-based detection.
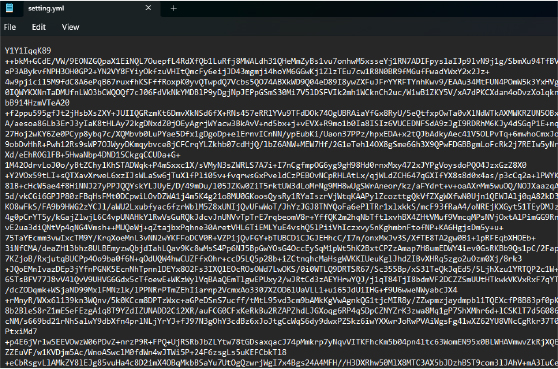
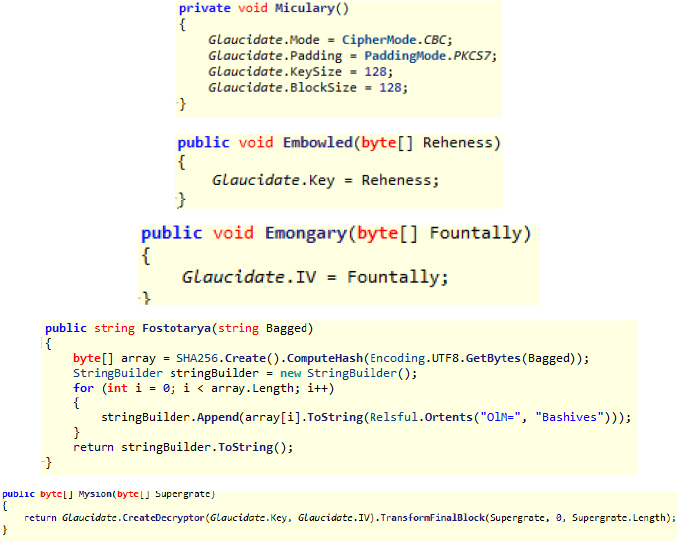
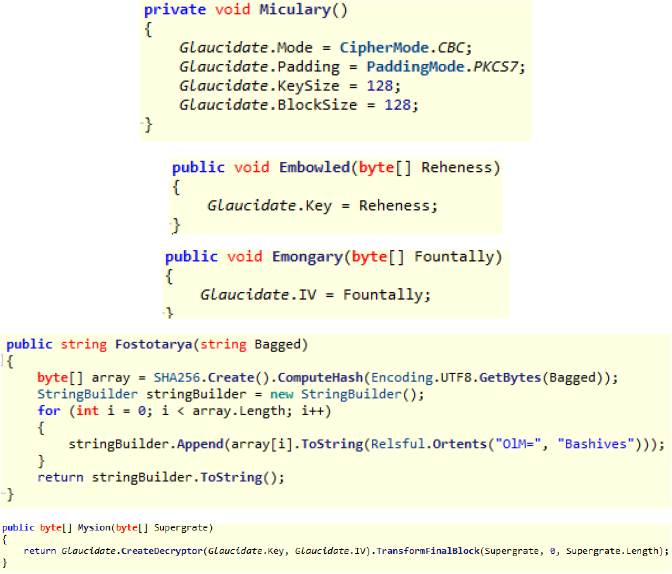
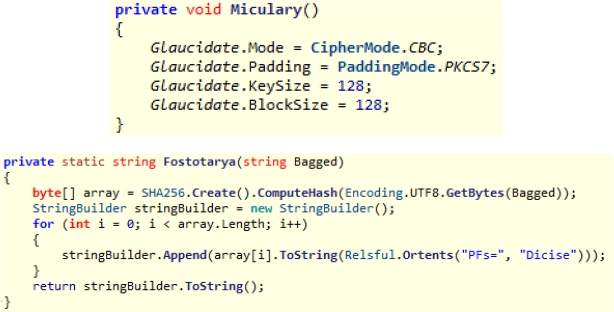
The Beartibly class implements a robust AES-128-CBC cryptographic routine to secure and conceal the core payload from both static and dynamic analysis. It utilizes CBC mode (CipherMode.CBC), PKCS7 padding (PaddingMode.PKCS7), and a 128-bit key and block size, ensuring reliable encryption while maintaining operational stealth. The payload blob (setting.yml, 3.67 MB) is Base64-encoded and AES-128-CBC encrypted, preventing direct inspection or extraction without proper decryption logic. The encryption parameters include a discovered initialization vector (IV) of 41bd37361bea411c, set through the Emongary() method, which assigns the value to RijndaelManaged.IV, and a derived encryption key of 769e88a66014f9d0, set through the Embowled() method, which assigns the value to RijndaelManaged.Key. The key is generated through a SHA-256-based key derivation mechanism using SHA256Managed.ComputeHash() on sequential integer strings, implemented in the Fostotarya() method which delegates to Imbios::Fostotarya for the hash computation and hex string conversion. The actual decryption is performed by the Mysion() method, which creates a decryptor via RijndaelManaged.CreateDecryptor() and processes the encrypted data through a CryptoStream wrapping a MemoryStream in CryptoStreamMode.Read mode. This layered approach not only protects the payload but also introduces computational overhead through the key derivation loop, contributing to effective sandbox evasion. By tightly integrating encryption within the execution workflow, the framework ensures that the malicious payload remains inaccessible until runtime, significantly reducing the likelihood of early detection.
Dual-Phase Sandbox Exhaustion
The malware employs a dual-phase sandbox evasion strategy designed to delay execution and defeat automated analysis environments. This mechanism combines computational workload with cryptographic operations to ensure that malicious behavior is not triggered within the limited execution window of most sandbox systems. By introducing controlled delays and resource-intensive tasks, the framework appears benign during initial inspection while preserving its full malicious capability for real-world execution. This approach significantly reduces detection rates in automated environments and enhances the overall stealth of the attack.
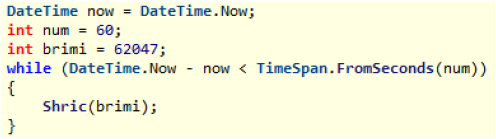
Phase 1: 60-Second Timing Gate
The malware invokes Bartifert.Shric(0x6F684C) inside a DateTime.Now loop bounded by TimeSpan.FromSeconds(60). Shric() executes a prime sieve computing all primes up to 7,300,172 (0x6F684C). This avoids Thread.Sleep() or Task.Delay(), which sandboxes can trivially detect and fast-forward. The prime computation is CPU-intensive, produces no suspicious API calls, and appears as legitimate mathematical processing to behavioral monitors, consuming the full 60 seconds of sandbox analysis budget before any malicious activity begins.
AES-128-CBC Cryptosystem
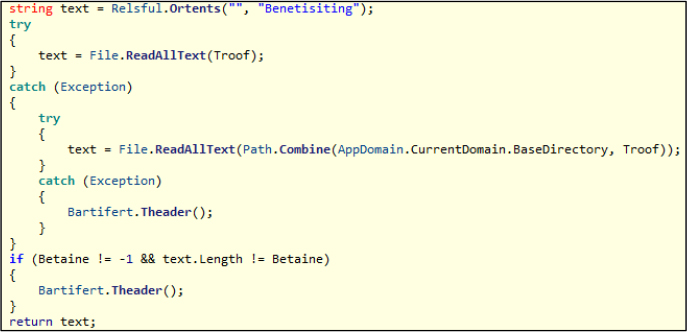
The Beartibly class configures System.Security.Cryptography.RijndaelManaged with CipherMode.CBC, PaddingMode.PKCS7, KeySize=128, and BlockSize=128 in its constructor Miculary(). The encrypted payload (setting.yml, 3.67 MB) is Base64-decoded and decrypted using the following method chain: Embowled() sets RijndaelManaged.Key via Encoding.UTF8.GetBytes(), Emongary() sets RijndaelManaged.IV via independent SHA-256 truncation of a separate XOR-encrypted seed, and Mysion() performs decryption through RijndaelManaged.CreateDecryptor() piped into a CryptoStream(MemoryStream, ICryptoTransform, CryptoStreamMode.Read). Discovered IV: 41bd37361bea411c. Discovered key: 769e88a66014f9d0.
Phase 2: Constrained AES Key Derivation Loop
This is not a traditional AES brute-force (2^128 keyspace). The malware iterates a constrained seed space of sequential integers 0 to 892,007 (0xD9C67). Each iteration: Fostotarya(i.ToString()) passes the seed to SHA256Managed.ComputeHash(Encoding.UTF8.GetBytes(input)), converts via BitConverter.ToString(), and truncates to 16 characters to form a 128-bit AES key candidate. The candidate is set via Embowled() on RijndaelManaged.Key, the IV is set via Emongary() on RijndaelManaged.IV, and Mysion() performs trial decryption through CreateDecryptor() into CryptoStream. The decrypted prefix is validated against the magic string “Occidentalism” (resolved at runtime via Ortents() with XOR key “Ichryptis”) using Enumerable.SequenceEqual(). Correct key resolves at iteration 41,410. Combined with Phase 1, the total delay exceeds 60 seconds, exhausting typical sandbox analysis time windows (3-5 minutes) before payload execution.
DLL Injection Storm
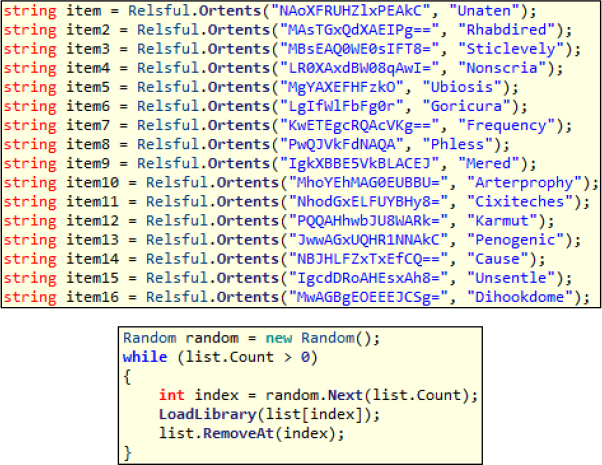
The function implements a DLL injection storm technique by loading 16 XOR-obfuscated DLL paths, which predominantly resolve to legitimate Windows system libraries. These paths are dynamically de-obfuscated using the Graphoth.Relsful::Ortents function and executed via kernel32::LoadLibrary in a randomized order. The paths are shuffled using System.Random, creating a burst of seemingly legitimate module loads that generate significant noise within security monitoring systems. This behavior floods detection mechanisms with benign-looking DLL load events, making it difficult to distinguish malicious activity from normal system operations. Additionally, this technique preloads dependencies required by the shellcode while obscuring the true execution path, effectively hiding malicious intent within routine Windows API activity.
.NET DLL Architecture Deep Dive
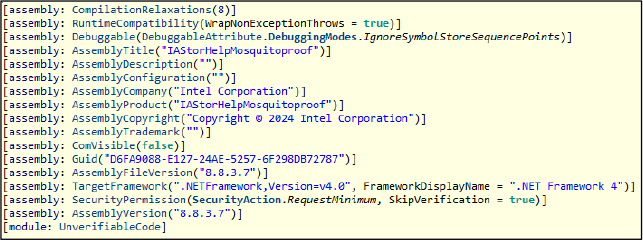
Assembly Metadata
The malware’s assembly metadata is deliberately crafted to appear legitimate, including spoofed attributes such as company name, versioning, and identifiers that mimic trusted software. It leverages standard .NET framework metadata structures while embedding malicious logic within the assembly, enabling it to blend seamlessly with legitimate applications and evade basic inspection techniques.
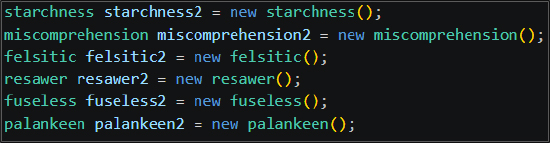
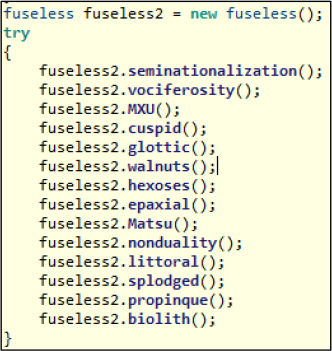
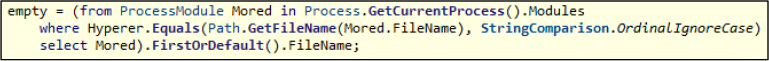
Static Analysis Dilution
The malware incorporates 36 junk classes with 100+ meaningless methods that exist solely to dilute static analysis and complicate reverse engineering efforts. These are organized into 14 structured try/catch chains, where each method performs trivial operations or returns random primitive values, creating the illusion of a large and complex application. In addition, the framework includes internal validation mechanisms, such as verifying the success of the DLL injection storm via process module enumeration and ensuring the integrity of the encrypted payload through size-guarded file reads. Together, these techniques not only obscure malicious logic but also reinforce execution reliability while misleading analysis tools.
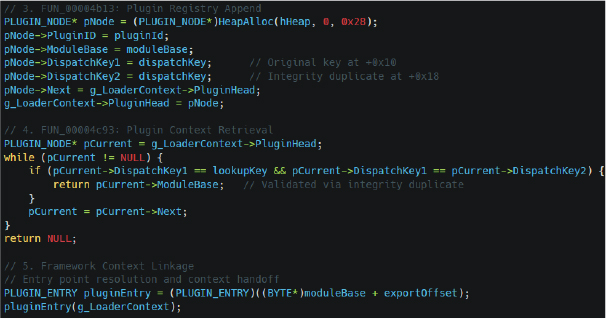
Operational Class Map (Attack Chain)
The framework follows a modular design where each class performs a specific role in the attack chain. The AppDomainManager hook initiates execution, followed by a central orchestrator that manages evasion and payload delivery. Dedicated modules handle encryption, shellcode execution, and DLL loading for evasion, while supporting components ensure data integrity, process validation, and runtime string decoding. This structured separation of responsibilities enables stealthy, controlled, and resilient execution across all stages of the attack.
| Class | Role | Key Methods |
| stylohyoideus | AppDomainManager hook | InitializeNewDomain -> PID-scoped Mutex -> Bartifert.Rotoricel |
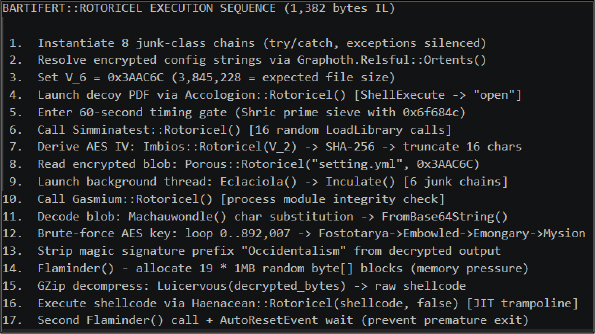
| Bartifert | Main orchestrator | Rotoricel (1,382 bytes IL), Shric, Eclaciola, Inculate, Flaminder, Luicervous |
| Beartibly | AES-128-CBC engine | Miculary (init), Embowled (set key), Emongary (set IV), Fostotarya (SHA-256), Mysion (decrypt) |
| Haenacean | Shellcode executor | Rotoricel (ThreadPool), Smutuallop, Semation (JIT trampoline), Readhing, Sundol |
| Simminatest | DLL injection storm | Electorided (16 random LoadLibrary), Rotoricel |
| Accologion | Decoy PDF launcher | Cytopsing (ShellExecute), Unspedii (path resolver), Rotoricel |
| Gasmium | Process module verifier | Adveness (LINQ ProcessModule search) |
| Imbios | SHA-256 key hasher | Fostotarya (SHA-256 -> hex string) |
The Just-In-Time (JIT) Trampoline Shellcode Execution
The malware employs a highly advanced JIT trampoline execution technique to run shellcode without relying on traditional memory allocation APIs such as VirtualAlloc or WriteProcessMemory, which are commonly monitored by security solutions. Instead, it leverages the .NET runtime by dynamically creating an assembly and forcing the JIT compiler to generate executable memory as part of normal application behavior. Once the JIT-compiled function is created, the malware overwrites the generated memory region with shellcode and executes it via a function pointer, effectively hiding malicious activity within legitimate runtime operations.
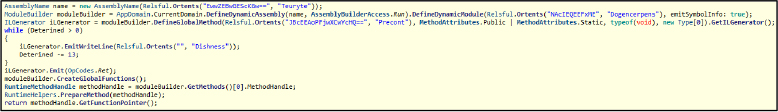
The Memory Execution Flow – JIT Trampoline Technique follows a structured sequence: the framework queues execution through a background thread, generates a dynamic assembly, defines and compiles a method to obtain a valid executable memory pointer, and then replaces the compiled instructions with shellcode. This memory is subsequently invoked through a delegate, enabling seamless execution within the managed runtime. By embedding shellcode into JIT-generated regions, the technique achieves stealthy in-memory execution, bypasses API-based monitoring, and creates a significant blind spot for endpoint detection and response (EDR) mechanisms.
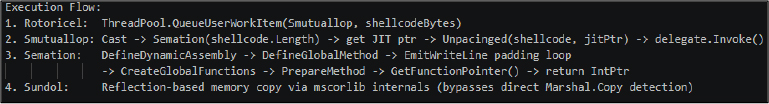
Why this matters: The shellcode is NOT executed via typical VirtualAlloc + WriteProcessMemory. Instead, the framework uses .NET’s Dynamic Assembly infrastructure to obtain a JIT-compiled function pointer, then overwrites that JIT’d memory region with shellcode bytes. This completely bypasses all traditional API monitoring.
Complete 17-Phase Execution Pipeline
Shellcode & Reflective Loader Analysis
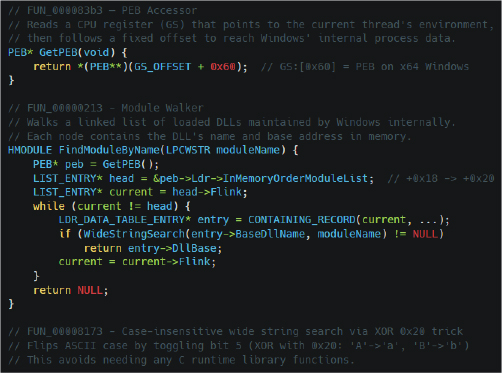
PEB-Based Zero-API Module Bootstrap
The malware utilizes a PEB-based zero-API bootstrap technique to locate critical system modules such as kernel32.dll and ntdll.dll without invoking any standard Windows API calls. By directly accessing the Process Environment Block (PEB) via the GS:[0x60] register on x64 systems, it traverses the internal loader structures (InMemoryOrderModuleList) to identify loaded modules and resolve their base addresses. This approach eliminates reliance on monitored functions like GetModuleHandle or LoadLibrary, thereby leaving minimal forensic traces. By performing module discovery and resolution entirely through memory structures, the malware achieves stealthy initialization, reduces detectable artifacts, and effectively bypasses API-hook-based security mechanisms.
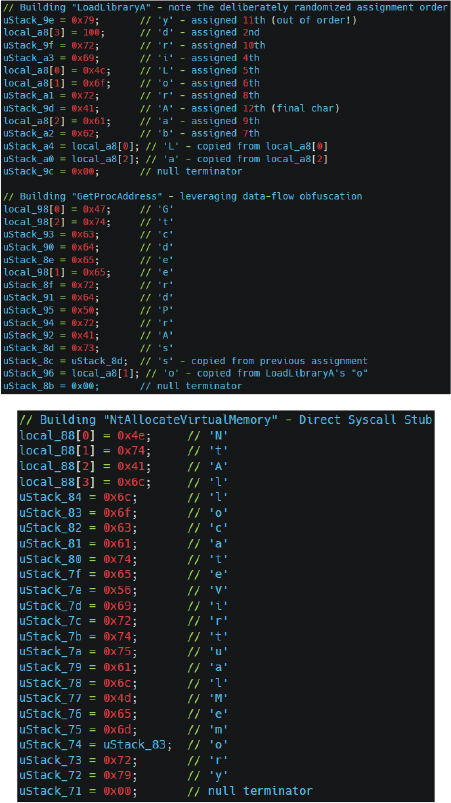
27-Entry Dynamic API Resolution Table
The malware constructs a 27-entry dynamic API resolution table at runtime, eliminating the need for static imports and reducing detectable artifacts. Instead of relying on standard functions like GetProcAddress, it builds API names using stack-based string construction techniques, often assembling characters in a non-linear or obfuscated order. These dynamically generated strings are then resolved manually to obtain function pointers for critical operations such as memory management, thread control, and section mapping. By resolving APIs in this manner often leveraging already located module bases via PEB traversal. The framework avoids traditional import tables and API hooks, enabling stealthy execution and evasion of security monitoring mechanisms.
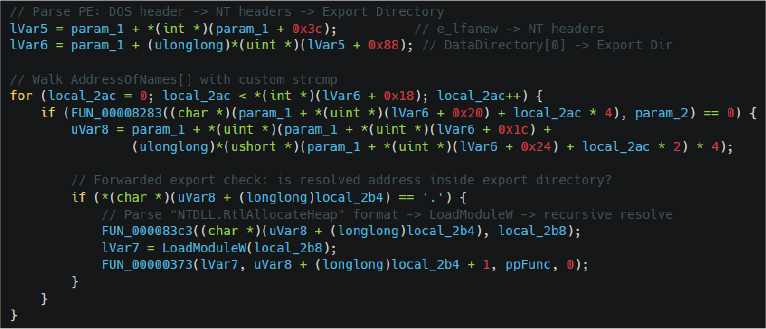
Custom Portable Executable (PE) Export Walker
The malware implements a custom PE export walker to resolve API functions directly from loaded modules without relying on standard Windows APIs such as GetProcAddress. After obtaining the base address of target modules via PEB traversal, it manually parses the PE structure, navigating through the DOS header to the NT headers and locating the Export Directory. It then iterates through the AddressOfNames, AddressOfFunctions, and AddressOfNameOrdinals tables to match function names and resolve their corresponding addresses. This manual resolution process enables the malware to dynamically retrieve required APIs while avoiding the use of monitored system calls, thereby enhancing stealth and bypassing API-hook-based detection mechanisms.
Reflective DLL Loader with Per-Section Protections
The malware implements a reflective DLL loader that manually maps PE modules into memory without using monitored APIs like LoadLibrary, enabling stealthy, fileless execution. In simple terms, it reconstructs the DLL in-memory step-by-step rather than relying on standard Windows loading mechanisms. It leverages low-level system calls to create and map memory regions, ensuring minimal visibility to security tools. A key feature is the application of per-section memory protections, where each PE section is assigned the most restrictive permissions: execute for code, read-only for constants, and read/write for data, closely mimicking the behavior of the legitimate Windows loader. This precise handling ensures that injected modules appear normal during memory inspection, allowing the malware to blend seamlessly with legitimate processes while effectively evading detection.
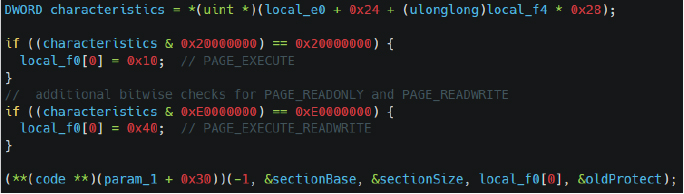
Two-Phase Secure Memory Teardown (Anti-Forensics)
The malware implements a two-phase anti-forensic memory teardown to completely eliminate traces of its payload after execution. In simple terms, it first locks down the memory so nothing can read it, and then removes it entirely, much like shredding a document before discarding it. In the first step, it invokes NtProtectVirtualMemory to change the memory region to PAGE_NOACCESS, preventing any further access by threads, debuggers, or forensic tools. In the second step, it calls NtFreeVirtualMemory with MEM_RELEASE to fully deallocate the memory pages, ensuring that no remnants of the payload remain. This deliberate two-stage process effectively blocks live memory analysis and makes post-incident forensic recovery extremely difficult, reinforcing the malware’s stealth and anti-analysis capabilities.
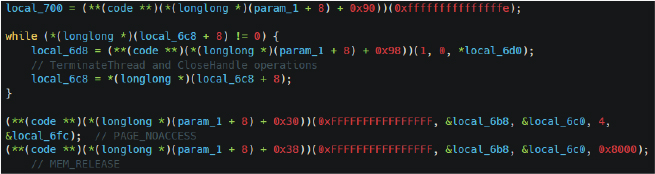
Plugin Architecture & Resilience
The framework is designed as a modular, plugin-based platform rather than a single standalone tool, enabling it to dynamically load and execute additional capabilities such as keylogging, screen capture, or data exfiltration at runtime. In simple terms, it operates like a system that can extend itself with “plugins,” similar to how browsers load extensions on demand. Each plugin is managed through a linked-list data structure, allowing the framework to efficiently track active modules, associated threads, and execution states. This structured approach not only ensures organized coordination between components but also enhances reliability, as the framework includes mechanisms to recover its internal state in case of crashes or failures, maintaining continuity of operations without requiring reinitialization.
5-Function Plugin Lifecycle Management
The framework uses a five-function lifecycle model to manage plugins from execution to cleanup, including thread tracking, registry insertion, context lookup, and recovery. Plugins are registered with associated metadata and tracked via linked structures, while worker threads are appended and removed as they execute and terminate. The design includes integrity checks through duplicated keys within plugin nodes and relies on standard heap allocations to blend with legitimate memory. This structured approach ensures efficient management, stealth, and resilience across plugin operations.
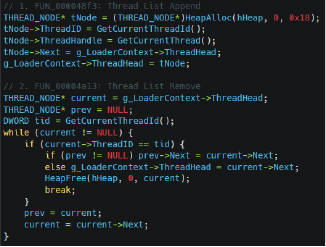
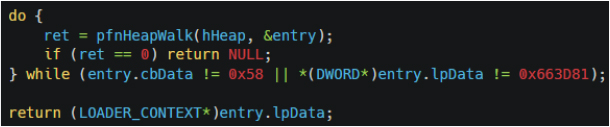
Heap-Walking Context Recovery
The framework includes a heap-walking recovery mechanism that acts as a safety net when its internal execution context is lost due to crashes or thread failures. It systematically scans all process heap allocations, searching for a structure of a specific size and a unique identifier (magic value) to re-establish control. By leveraging standard heap traversal techniques, it can locate and restore its core context dynamically, ensuring continuity of operations without reinitialization. This approach enhances resilience, fault tolerance, and stealth, as recovery is performed entirely in-memory using legitimate system behavior.
Dynamic analysis of the sample reveals active network communication and execution behavior consistent with a post-exploitation command-and-control (C2) framework operating under the guise of a trusted process. Upon execution, the binary establishes outbound connections over TCP, indicating successful beaconing to a remote infrastructure likely used for tasking and data exfiltration. Observed network behavior indicates periodic beaconing over HTTPS, with consistent with POST-based communication patterns. The traffic is encapsulated within standard TLS sessions, making payload inspection difficult without SSL/TLS interception. No abnormal certificate anomalies were observed, reinforcing the effectiveness of CDN fronting in blending malicious traffic with legitimate cloud service communications.
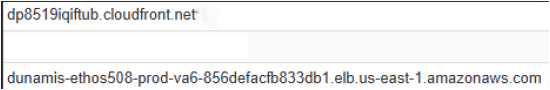
Active command-and-control (C2) Communication via CloudFront
Dynamic analysis confirms active C2 communication leveraging CDN-backed infrastructure to enhance stealth and operational resilience. The malware establishes outbound connections to domains hosted on Amazon CloudFront and AWS Elastic Load Balancing (ELB), effectively blending malicious traffic within legitimate cloud service communications. Specifically, dp8519iqiftub[.]cloudfront[.]net functions as a CDN-based redirector, while dunamis-ethos508-prod-va6-856defacfb833db1[.]elb[.]us-east-1[.]amazonaws[.]com represents the backend C2 infrastructure. This indicates a multi-layered architecture in which initial traffic is routed through the CloudFront distribution before being forwarded to the actual command server behind the ELB, thereby abstracting the true origin of attacker-controlled infrastructure. Such an approach enables attackers to evade traditional network defenses, as traffic appears to originate from trusted cloud services, rendering IP- or domain-based blocking less effective. Additionally, this architecture supports rapid backend rotation without disrupting active sessions, significantly enhancing operational security (OPSEC) and resilience.
Process Execution and Module Presence
The execution context shows the malware operating under IAStorHelp.exe, a legitimate Intel-signed binary, along with associated modules loaded within the process environment. This reinforces the use of trusted binary proxy execution, allowing the malware to blend into legitimate system activity and evade detection by security solutions that rely on process reputation.
The analyzed framework aligns closely with a growing cluster of advanced campaigns and commercial offensive tooling, indicating a clear convergence between advanced threat actor tradecraft and red-team-grade capabilities. Notable overlaps with campaigns such as GhostWriter / UNC1151, ScarCruft (APT37), and MuddyWater (MERCURY) highlight the increasing adoption of techniques like AppDomainManager hijacking, .exe.config-based CLR abuse, and CDN-backed command-and-control using platforms such as CloudFront. At the same time, architectural similarities with tools like Brute Ratel C4, NightHawk, and Cobalt Strike, including reflective loading, JIT-based execution, direct syscall usage, and structured plugin frameworks, suggest either inspiration from or intentional mimicry of mature offensive ecosystems. This blending of publicly known techniques with custom in-memory execution mechanisms reflects a strategic evolution where attackers prioritize stealth, modularity, and forensic resistance.
From a broader threat landscape perspective (2024–2026), this activity is consistent with rising APT trends targeting government, financial services, and critical infrastructure sectors across the Middle East and EMEA regions. The resurgence of socially engineered “Work From Home” themed lures, combined with a sharp increase in trusted binary abuse and AppDomainManager-based execution, underscores a shift toward low-noise initial access and trusted execution paths. Additionally, the widespread use of CDN fronting (e.g., CloudFront, Azure CDN) as a primary C2 transport layer demonstrates a deliberate move to blend malicious traffic within legitimate cloud ecosystems, rendering traditional detection approaches ineffective. Overall, the framework operates at the upper boundary of APT sophistication, significantly exceeding commodity malware capabilities and closely approaching, if not matching, the tradecraft observed in top-tier nation-state operations.
This analysis has comprehensively dissected a multi-stage, APT-grade post-exploitation framework that demonstrates exceptional operational security discipline across every stage of the attack chain. The intrusion begins with highly targeted social engineering, leveraging a Saudi government Ministry-themed decoy combined with pixel-perfect masquerading using a legitimate PDF icon. Initial access is achieved through AppDomainManager hijacking within a trusted Intel-signed binary, reinforced by process-level mutex controls to prevent duplication. The framework incorporates robust anti-sandbox mechanisms, including time-based execution delays and computational gating, ensuring malicious activity only triggers outside controlled environments. To evade static detection, it employs extensive code dilution and obfuscation, including numerous junk classes, layered try/catch chains, and centralized string de-obfuscation, effectively concealing operational logic from analysis tools.
At runtime, the framework transitions into a highly structured execution pipeline, dynamically resolving APIs through custom mechanisms that bypass traditional monitoring and orchestrating execution through multiple staged components such as DLL loading, memory manipulation, and verification routines. Shellcode execution is achieved via advanced JIT-based trampolining, enabling in-memory execution without reliance on conventional APIs, while reflective loading ensures memory protections closely mimic legitimate system behavior. The command-and-control infrastructure leverages CloudFront-based domain fronting, providing resilience and stealth in network communication. Additionally, the framework exhibits strong fault tolerance through heap-based context recovery mechanisms, allowing it to maintain operational continuity even in unstable conditions. Overall, the combination of stealth, modularity, and resilience reflects a highly sophisticated threat capability that challenges conventional detection mechanisms and necessitates a shift toward behavior-driven security monitoring, memory forensics, and encrypted traffic inspection.
rule CYFIRMA_APT_AppDomainManager_Mosquitoproof {
meta:
description = “Detects the malicious .NET loader and AppDomainManager injection artifacts”
author = “CYFIRMA Research”
date = “2026-04-11”
severity = “Critical”
strings:
$config_appdomain = “<appDomainManagerAssembly” nocase ascii wide
$config_type = “appDomainManagerType” nocase ascii wide
$hijack_class = “stylohyoideus” ascii wide
$class_graphoth = “Graphoth.Relsful” ascii wide
$class_beartibly = “Beartibly” ascii wide
$class_bartifert = “Bartifert” ascii wide
$class_haenacean = “Haenacean” ascii wide
$class_simminatest = “Simminatest” ascii wide
$class_gasmium = “Gasmium” ascii wide
$magic_val = “Occidentalism” ascii wide
$pinvoke = “Electorided” ascii wide
$guid = “D6FA9088-E127-24AE-5257-6F298DB72787” ascii wide
condition:
uint16(0) == 0x5A4D and (
(2 of ($config_*)) or
$hijack_class or
(3 of ($class_*)) or
$magic_val or
$guid or
($pinvoke and 1 of ($class_*))
)
}
rule CYFIRMA_APT_ReflectiveLoader_StageLaunch {
meta:
description = “Detects reflective stager shellcode with stage/launch convention and API table magic”
author = “CYFIRMA Research”
date = “2026-04-11”
severity = “Critical”
strings:
$magic_ctx = { 81 3D 66 00 }
$nt_alloc = “NtAllocateVirtualMemory” ascii
$nt_section = “NtCreateSection” ascii
$nt_mapview = “NtMapViewOfSection” ascii
$nt_protect = “NtProtectVirtualMemory” ascii
$export_stage = “stage” ascii
$export_launch = “launch” ascii
$dispatch_hdr = { 82 A1 50 00 A1 56 00 }
condition:
(2 of ($nt_*)) or
($magic_ctx and 1 of ($export_*)) or
($dispatch_hdr) or
(all of ($export_*) and 1 of ($nt_*))
}
Strategic Recommendations:
Tactical Recommendations:
Operational Recommendations:
MITRE ATT&CK MAPPING
| Tactic | Technique | ID | Evidence |
| Initial Access | Phishing: Spear phishing Attachment | T1566.001 | LNK file masquerading as WFH policy PDF |
| Execution | User Execution: Malicious File | T1204.002 | User double-clicks .pdf.lnk shortcut |
| Execution | Native API | T1106 | Direct NTDLL syscall stubs |
| Execution | Shared Modules | T1129 | 16 DLLs via randomized LoadLibrary |
| Persistence | Hijack Execution Flow: AppDomainManager | T1574.014 | .config overrides CLR initialization |
| Defense Evasion | Masquerading: Match Legitimate Resource Name or Location | T1036.005 | LNK uses Edge PDF icon; DLL spoofs Intel |
| Defense Evasion | System Binary Proxy Execution | T1218 | Signed IAStorHelp.exe as execution proxy |
| Defense Evasion | Obfuscated Files or Information: Software Packing | T1027.002 | AES-encrypted + GZip-compressed payload |
| Defense Evasion | Obfuscated Files or Information: Embedded Payloads | T1027.009 | 27 API names via scrambled stack strings |
| Defense Evasion | Obfuscated Files or Information | T1027 | XOR de-obfuscation; 36 junk classes |
| Defense Evasion | Deobfuscate/Decode Files or Information | T1140 | Runtime AES key derivation loop combined with XOR-based string de-obfuscation |
| Defense Evasion | Reflective Code Loading | T1620 | Custom reflective DLL loader |
| Defense Evasion | Indicator Removal | T1070 | PE headers wiped; buffers zeroed |
| Defense Evasion | Impair Defenses: Disable or Modify Tools | T1562.001 | Bypasses EDR hooks via direct NTDLL |
| Defense Evasion, Discovery | Virtualization/Sandbox Evasion: System Checks | T1497.001 | 60-second prime sieve timing gate |
| Defense Evasion | Execution Guardrails | T1480 | File size validation (0x3AAC6C) |
| Defense Evasion, Priv. Esc. | Process Injection: Thread Execution Hijacking | T1055.003 | JIT trampoline via DefineDynamicAssembly |
| Discovery | System Information Discovery | T1082 | Registry processor/locale interrogation |
| Discovery | Process Discovery | T1057 | Thread enumeration; Process.Modules scan |
| Privilege Escalation, Def. Ev. | Process Injection: Dynamic-link Library Injection | T1055.001 | Reflective DLL injection |
| Command & Control | Application Layer Protocol: Web Protocols | T1071.001 | HTTPS/TLS C2 over CloudFront |
| Command & Control | Proxy: Domain Fronting | T1090.004 | C2 via cloudfront.net CDN |
| No | IOCs | Type | Remarks |
| 1 | f2266b45d60f5443c5c9304b5f0246348ad82ca4f63c7554c46642311e3f8b83 | SHA-256 | Block |
| 2 | 4f353b9634509a5e1456e54ccb4ce64c1e6d95094df96048ef79b30cc2fda6cb | SHA-256 | Block |
| 3 | 5d784d3ca02ab0015b028f34aa54bc8c50db39f9671dc787bc2a84f0987043b2 | SHA-256 | Block |
| 4 | 8ba1b0392a8fbfb455c43c4e1408352d0e5fc281148810143a5b64938fb0982f | SHA-256 | Monitor |
| 5 | dp8519iqiftub[.]cloudfront[.]net | Domain | Monitor |
| 6 | dunamis-ethos508-prod-va6-856defacfb833db1[.]elb[.]us-east-1[.]amazonaws[.]com | Domain | Monitor |