


CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple industries, geography, and technology – that could be relevant to your organization.
Type: Ransomware
Target Technologies: Windows Systems, Network Shares, Mapped Drives, Enterprise File Storage Systems, Backup Repositories, Remote Access Services (RDP)
Introduction:
CYFIRMA Research and Advisory Team has found BASANAI Ransomware while monitoring various underground forums as part of our Threat Discovery Process.
BASANAI Ransomware
BASANAI ransomware has been identified as a MedusaLocker-family file-encrypting malware variant that prevents access to victim data by encrypting files and appending a distinct extension associated with the BASANAI strain. Upon execution, the malware systematically encrypts files across the infected system and drops a ransom note, typically named “README.txt”, informing victims of the compromise. Analysis indicates that the ransomware leverages strong cryptographic algorithms (commonly AES combined with RSA, consistent with MedusaLocker variants) to ensure that files cannot be decrypted without attacker-controlled keys. The operators claim that not only local files but also network shares and potentially backups may be impacted, increasing operational disruption. In addition to encryption, the threat actors assert that sensitive data may have been exfiltrated, introducing a double extortion element where victims face both data loss and potential public exposure. Victims are instructed to contact the attackers via the provided communication channels to negotiate payment, typically in cryptocurrency. At present, no confirmed public decryption tool is available for this variant, and recovery without attacker cooperation remains unlikely.

Screenshot: File encrypted by the ransomware (Source: Surface Web)
The ransom note associated with BASANAI ransomware, usually delivered as “README.txt”, explicitly informs victims that their files have been encrypted using robust encryption mechanisms and are no longer accessible. The message states that only the attackers possess the unique private key required for decryption, and strongly discourages victims from attempting recovery through third-party tools or by modifying encrypted files, warning that such actions may result in irreversible data corruption. The note typically includes instructions for contacting the attackers via email addresses or TOR-based communication channels, along with a unique victim ID to facilitate negotiation. It further reinforces pressure by indicating that sensitive data may have been stolen during the attack, and threatens public release or sale of this data if the ransom is not paid. The language used follows standard MedusaLocker-style coercion tactics, combining technical intimidation (irreversible encryption claims) with psychological pressure (data leakage threats), while offering no verifiable assurance that payment will lead to successful data recovery.
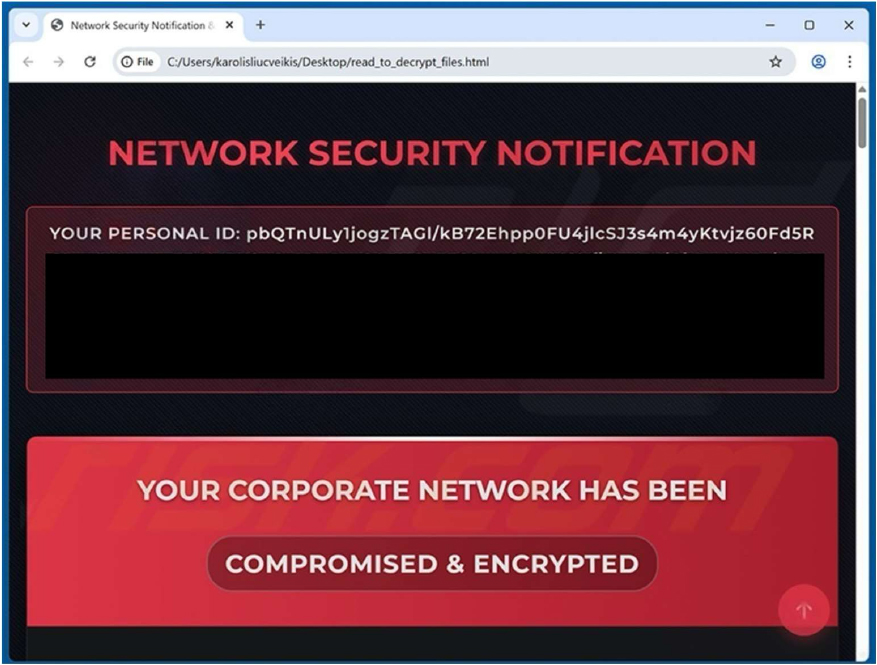
Screenshot: The appearance of the BASANAI’s Ransom Note (Source: Surface Web)
The following are the TTPs based on the MITRE Attack Framework
| Tactic | Technique ID | Technique Name |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1129 | Shared Modules |
| Persistence | T1112 | Modify Registry |
| Persistence | T1543 | Create or Modify System Process |
| Persistence | T1543.003 | Create or Modify System Process: Windows Service |
| Persistence | T1547 | Boot or Logon Autostart Execution |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1055 | Process Injection |
| Privilege Escalation | T1543 | Create or Modify System Process |
| Privilege Escalation | T1543.003 | Create or Modify System Process: Windows Service |
| Privilege Escalation | T1547 | Boot or Logon Autostart Execution |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1548 | Abuse Elevation Control Mechanism |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1027.002 | Obfuscated Files or Information: Software Packing |
| Defense Evasion | T1036 | Masquerading |
| Defense Evasion | T1055 | Process Injection |
| Defense Evasion | T1070 | Indicator Removal |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1112 | Modify Registry |
| Defense Evasion | T1202 | Indirect Command Execution |
| Defense Evasion | T1497 | Virtualization/Sandbox Evasion |
| Defense Evasion | T1548 | Abuse Elevation Control Mechanism |
| Defense Evasion | T1562 | Impair Defenses |
| Defense Evasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| Defense Evasion | T1564 | Hide Artifacts |
| Defense Evasion | T1564.003 | Hide Artifacts: Hidden Window |
| Credential Access | T1003 | OS Credential Dumping |
| Credential Access | T1539 | Steal Web Session Cookie |
| Credential Access | T1552 | Unsecured Credentials |
| Credential Access | T1552.001 | Unsecured Credentials: Credentials In Files |
| Credential Access | T1555 | Credentials from Password Stores |
| Credential Access | T1555.003 | Credentials from Password Stores: Credentials from Web Browsers |
| Discovery | T1012 | Query Registry |
| Discovery | T1057 | Process Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1497 | Virtualization/Sandbox Evasion |
| Collection | T1005 | Data from Local System |
| Collection | T1074 | Data Staged |
| Collection | T1114 | Email Collection |
| Command and Control | T1071 | Application Layer Protocol |
| Command and Control | T1095 | Non-Application Layer Protocol |
| Impact | T1485 | Data Destruction |
| Impact | T1486 | Data Encrypted for Impact |
| Impact | T1489 | Service Stop |
Relevancy and Insights:
ETLM Assessment:
CYFIRMA’s analytical assessment indicates that BASANAI ransomware is likely to continue operating as part of the MedusaLocker ecosystem, with future developments expected to focus on incremental operational improvements rather than novel innovation. Based on observed behavior, operators may enhance encryption efficiency, propagation across networked environments, and reliability of payload execution to maximize impact. There is a strong likelihood of continued and more structured use of double extortion tactics, particularly emphasizing data exfiltration to increase victim pressure and payment rates. Future campaigns may also refine initial access vectors, potentially leveraging exposed RDP services, phishing campaigns, or exploitation of unpatched vulnerabilities common entry points associated with this ransomware family. However, there is currently no evidence suggesting advancement into highly sophisticated or targeted attack methodologies, indicating that BASANAI will likely remain aligned with commodity ransomware operations, focusing on scalable, opportunistic attacks rather than highly specialized intrusions.
Sigma rule:
title: Files With System Process Name In Unsuspected Locations tags:
– attack.defense-evasion
– attack.t1036.005 logsource:
category: file_event product: windows
detection: selection:
TargetFilename|endswith:
– ‘\AtBroker.exe’
– ‘\audiodg.exe’
– ‘\backgroundTaskHost.exe’
– ‘\bcdedit.exe’
– ‘\bitsadmin.exe’
– ‘\cmdl32.exe’
– ‘\cmstp.exe’
– ‘\conhost.exe’
– ‘\csrss.exe’
– ‘\dasHost.exe’
– ‘\dfrgui.exe’
– ‘\dllhost.exe’
– ‘\dwm.exe’
– ‘\eventcreate.exe’
– ‘\eventvwr.exe’
– ‘\explorer.exe’
– ‘\extrac32.exe’
– ‘\fontdrvhost.exe’
– ‘\fsquirt.exe’ # was seen used by sidewinder APT – https://securelist.com/sidewinder-apt/114089/
– ‘\ipconfig.exe’
– ‘\iscsicli.exe’
– ‘\iscsicpl.exe’
– ‘\logman.exe’
– ‘\LogonUI.exe’
– ‘\LsaIso.exe’
– ‘\lsass.exe’
– ‘\lsm.exe’
– ‘\msiexec.exe’
– ‘\msinfo32.exe’
– ‘\mstsc.exe’
– ‘\nbtstat.exe’
– ‘\odbcconf.exe’
– ‘\powershell.exe’
– ‘\pwsh.exe’
– ‘\regini.exe’
– ‘\regsvr32.exe’
– ‘\rundll32.exe’
– ‘\RuntimeBroker.exe’
– ‘\schtasks.exe’
– ‘\SearchFilterHost.exe’
– ‘\SearchIndexer.exe’
– ‘\SearchProtocolHost.exe’
– ‘\SecurityHealthService.exe’
– ‘\SecurityHealthSystray.exe’
– ‘\services.exe’
– ‘\ShellAppRuntime.exe’
– ‘\sihost.exe’
– ‘\smartscreen.exe’
– ‘\smss.exe’
– ‘\spoolsv.exe’
– ‘\svchost.exe’
– ‘\SystemSettingsBroker.exe’
– ‘\taskhost.exe’
– ‘\taskhostw.exe’
– ‘\Taskmgr.exe’
– ‘\TiWorker.exe’
– ‘\vssadmin.exe’
– ‘\w32tm.exe’
– ‘\WerFault.exe’
– ‘\WerFaultSecure.exe’
– ‘\wermgr.exe’
– ‘\wevtutil.exe’
– ‘\wininit.exe’
– ‘\winlogon.exe’
– ‘\winrshost.exe’
– ‘\WinRTNetMUAHostServer.exe’
– ‘\wlanext.exe’
– ‘\wlrmdr.exe’
– ‘\WmiPrvSE.exe’
– ‘\wslhost.exe’
– ‘\WSReset.exe’
– ‘\WUDFHost.exe’
– ‘\WWAHost.exe’ filter_main_generic:
# Note: It is recommended to use a more robust filter instead of this generic one, to avoid false negatives.
TargetFilename|contains:
# – ‘\SystemRoot\System32\’
– ‘C:\$WINDOWS.~BT\’
– ‘C:\$WinREAgent\’
– ‘C:\Windows\SoftwareDistribution\’
– ‘C:\Windows\System32\’
– ‘C:\Windows\SysWOW64\’
– ‘C:\Windows\WinSxS\’
– ‘C:\Windows\uus\’ filter_main_tiworker:
Image|endswith:
– ‘\TiWorker.exe’
– ‘\wuaucltcore.exe’ TargetFilename|startswith: ‘C:\Windows\Temp\’
filter_main_svchost: Image|endswith:
– ‘C:\Windows\system32\svchost.exe’
– ‘C:\Windows\SysWOW64\svchost.exe’ TargetFilename|contains:
– ‘C:\Program Files\WindowsApps\’
– ‘C:\Program Files (x86)\WindowsApps\’
– ‘\AppData\Local\Microsoft\WindowsApps\’ filter_main_wuauclt:
Image:
– ‘C:\Windows\System32\wuauclt.exe’
– ‘C:\Windows\SysWOW64\wuauclt.exe’
– ‘C:\Windows\UUS\arm64\wuaucltcore.exe’ filter_main_explorer:
TargetFilename|endswith: ‘C:\Windows\explorer.exe’ filter_main_msiexec:
# This filter handles system processes who are updated/installed using misexec. Image|endswith:
– ‘C:\WINDOWS\system32\msiexec.exe’
– ‘C:\WINDOWS\SysWOW64\msiexec.exe’
# Add more processes if you find them or simply filter msiexec on its own. If the list grows big
TargetFilename|startswith:
– ‘C:\Program Files\PowerShell\7\pwsh.exe’
– ‘C:\Program Files\PowerShell\7-preview\pwsh.exe’
– ‘C:\Program Files\WindowsApps\Microsoft.PowerShellPreview\’ filter_main_healtray:
TargetFilename|contains: ‘C:\Windows\System32\SecurityHealth\’ TargetFilename|endswith: ‘\SecurityHealthSystray.exe’ Image|endswith: ‘\SecurityHealthSetup.exe’
condition: selection and not 1 of filter_main_* falsepositives:
– System processes copied outside their default folders for testing purposes
– Third party software naming their software with the same names as the processes mentioned here
level: medium (Source: Surface Web)
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
Type: Backdoor| Objectives: Persistence | Target Technology: Windows OS | Target Geography: Global
CYFIRMA collects data from various forums, based on which the trend is ascertained. We identified a few popular malwares that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week, the “RodexRMM” malware is in focus.
Overview of Operation RodexRMM Malware
The analysed sample, identified as RodexRMM, demonstrates a structured and stealth- oriented set of behaviours indicative of a controlled malicious operation. Its activity suggests a clear intention to establish persistence within the infected environment while operating in a manner that closely mimics legitimate system processes. By utilizing standard system paths and interacting with core components, the malware attempts to remain inconspicuous and avoid raising immediate suspicion. Additionally, it gathers key system information, likely to assess the environment and prepare for subsequent actions.
Furthermore, RodexRMM exhibits multiple defense evasion characteristics, including the use of obfuscation and strategic interaction with system configurations and registry settings. These actions may contribute to weakening security visibility or bypassing detection mechanisms. The observed behaviour also indicates an awareness of analysis environments, suggesting that the malware may actively attempt to evade sandboxing or monitoring tools, thereby prolonging its presence on the compromised system.
The communication patterns associated with RodexRMM reveal outbound connections to external services, potentially to obtain system-related information such as public IP data. This, combined with its capability to execute processes and manage system activities, suggests the presence of a command-and-control mechanism. Overall, the malware reflects a level of sophistication consistent with threats designed for persistence, reconnaissance, and remote control, posing a notable risk in both targeted and opportunistic attack scenarios.
Attack Method
The attack methodology associated with RodexRMM demonstrates a structured and methodical approach aimed at establishing persistence, escalating privileges, and maintaining sustained access within a compromised environment. Malware achieves persistence by creating or modifying system-level processes, ensuring that it continues to execute even after system restarts. In addition, similar process manipulation techniques are employed to facilitate privilege escalation, allowing the malware to operate with elevated permissions and gain broader control over system resources.
To minimize the likelihood of detection, RodexRMM incorporates multiple defense evasion mechanisms. These include the use of obfuscation and software packing techniques to conceal its internal structure and hinder analysis by security solutions. The malware also interacts with critical system registry configurations, potentially altering execution flows or bypassing monitoring controls. Furthermore, its behaviour indicates an awareness of analysis environments, suggesting that it may actively attempt to evade sandboxing and security inspection mechanisms.
The malware further engages in systematic reconnaissance to assess the characteristics of the infected system. It performs process enumeration, collects system-level information, and identifies the presence of security software. This information-gathering phase enables the malware to adapt its operations based on the environment, thereby improving its ability to remain undetected and execute subsequent actions effectively.
In terms of communication, RodexRMM utilizes standard web-based protocols to establish contact with external infrastructure. It connects to publicly available services to obtain information such as the system’s external IP address, which can assist in identifying and managing compromised hosts. By leveraging commonly used communication channels and legitimate services, the malware effectively obscures its network activity within normal traffic patterns, complicating detection and response efforts.
The following are the TTPs based on the MITRE Attack Framework for Enterprise
| Tactic | Technique ID | Technique Name |
| Persistence | T1543 | Create or Modify System Process |
| Defense Evasion | T1027.002 | Obfuscated Files or Information: Software Packing |
| Discovery | T1057 | Process Discovery |
| T1518.001 | Software Discovery: Security Software Discovery | |
| T1082 | System Information Discovery | |
| Command and control | T1071 | Application Layer Protocol |
INSIGHTS
ETLM ASSESSMENT
From an ETLM perspective, the progression of threats such as RodexRMM reflects a broader shift toward highly discreet and persistent attack models that align closely with legitimate business operations. This evolution is likely to complicate organizational visibility, making it increasingly challenging to differentiate between normal activities and malicious behaviour across enterprise environments. As a result, organizations may experience growing exposure to undetected, low-profile intrusions, while employees through routine system interactions may unknowingly contribute to the expansion of the attack surface. Collectively, these developments point toward a more complex and less transparent threat landscape, where understanding and managing risk will become progressively more challenging due to the subtle and integrated nature of emerging threats.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems. (Source: Surface Web)
YARA Rules
rule RodexRMM_String_IOCs
{
meta:
description = “Detects RodexRMM using string-based IOCs (hash artifacts and C2 indicator)”
author = “CYFIRMA” date = “2026-04-07
strings:
/* Malware Sample Hash artifacts as strings */
$hash_md5 = “1e6acadabf333d7caf8b66e234af3a31”
$hash_sha1 = “432860ca09217e8e48455a7471c107ab81aaf778”
$hash_sha256 =
“34a774a9f08253a41a215b9ec6022e9f3911f2ba15d5c453cf7ef329120c8c65”
condition:
any of ($hash_*)
}
Strategic Recommendations
These are high-level, long-term initiatives to strengthen organizational cybersecurity posture:
Management Recommendations
These focus on policies, procedures, and governance to ensure proper oversight and risk mitigation:
Tactical Recommendations
These are immediate, actionable steps to prevent, detect, and respond to malware at the operational level:
Key Intelligence Signals:
Chinese Threat Actor Silver Fox Expanding footprints in APAC
About the Threat Actor
Silver Fox aka Void Arachne – suspected Chinese threat actor, is assessed to have been active since at least 2019–2020, demonstrating continuous evolution in its tooling and targeting capabilities while maintaining an aggressive posture toward organizations. The group has expanded its operational footprint and digital presence across multiple countries in the APAC region.
TTPs based on MITRE ATT&CK Framewor
| Tactic | ID | Technique |
| Initial Access | T1189 | Drive-by Compromise |
| Initial Access | T1566 | Phishing |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
| Execution | T1106 | Native API |
| Execution | T1129 | Shared Modules |
| Execution | T1204 | User Execution |
| Execution | T1047 | Windows Management Instrumentation |
| Persistence | T1112 | Modify Registry |
| Persistence | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Privilege Escalation | T1055.001 | Process Injection: Dynamic-link Library Injection |
| Privilege Escalation | T1055 | Process Injection |
| Privilege Escalation | T1548 | Abuse Elevation Control Mechanism |
| Defense Evasion | T1562 | Impair Defenses |
| Defense Evasion | T1497 | Virtualization/Sandbox Evasion |
| Defense Evasion | T1202 | Indirect Command Execution |
| Defense Evasion | T1562.001 | Impair Defenses: Disable or Modify Tools |
| Defense Evasion | T1036 | Masquerading |
| Defense Evasion | T1055 | Process Injection |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1548 | Abuse Elevation Control Mechanism |
| Defense Evasion | T1112 | Modify Registry |
| Defense Evasion | T1055.001 | Process Injection: Dynamic-link Library Injection |
| Defense Evasion | T1553.002 | Subvert Trust Controls: Code Signing |
| Defense Evasion | T1620 | Reflective Code Loading |
| Defense Evasion | T1564 | Hide Artifacts |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1497 | Virtualization/Sandbox Evasion |
| Discovery | T1057 | Process Discovery |
| Discovery | T1518 | Software Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1497 | Virtualization/Sandbox Evasion |
| Lateral Movement | T1563.002 | Remote Service Session Hijacking: RDP Hijacking |
| Collection | T1185 | Browser Session Hijacking |
| Command and Control | T1071 | Application Layer Protocol |
| Command and Control | T1573 | Encrypted Channel |
| Command and Control | T1095 | Non-Application Layer Protocol |
Latest Developments Observed
The threat actor is suspected of targeting organizations across India, Japan, and Southeast Asia through a large-scale cyber campaign leveraging Remote Access Trojan (RAT) malware. The campaign involves the creation of fraudulent websites designed to mimic trusted software platforms such as Zoom, Telegram, and VPN services. The primary objective appears to be the exfiltration of sensitive information, along with establishing persistent access to monitor user activity over extended periods.
ETLM Insights
Void Arachne (aka Silver Fox) is a financially driven cybercriminal group focused on large-scale intrusion and extortion operations, where scalable access, persistent monitoring, and data exfiltration underpin its revenue generation model. The group’s campaigns demonstrate a strong dependence on deception-based access methods and mass distribution strategies, allowing it to compromise a wide range of targets across the APAC region while maintaining prolonged access within affected systems.
Operationally, the actor prioritizes persistence, stealth, and scalability to support continuous intelligence collection and monetization. Its increasing adoption of AI- driven capabilities signals a shift toward more adaptive and psychologically oriented operations, enhancing targeting accuracy, automation, and evasion. Looking ahead, Void Arachne is likely to further advance its AI-enabled tradecraft, broaden its operational footprint, and refine high-volume campaigns to achieve greater efficiency and lower detection rates.
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
YARA Rules
rule SilverFox_RAT_IP_Based_Detection
{
meta:
description = “Detects potential Silver Fox (Void Arachne) related Win32 executable communicating with known IP”
author = “CYFIRMA” date = “2026-04-07”
threat_actor = “Void Arachne / Silver Fox” type = “RAT / Win32 EXE”
strings:
$ip1 = “27.124.3.175” ascii
condition:
(uint16(0) == 0x5A4D) and
$ip1
}
Strategic Recommendations
Management Recommendations
Tactical Recommendations
North Korean threat actor compromises popular JavaScript library
A North Korean threat actor yesterday inserted a malicious dependency into two npm releases for axios, the most popular JavaScript library for making HTTP requests, according to researchers. The affected versions – axios 1.14.1 (typically over 100 million weekly downloads) and axios 0.30.4 (around 83 million weekly downloads) – were live for roughly two to three hours on March 31, 2026, before being removed by npm. The malicious change involved adding a hidden dependency ([email protected]) that acted as an obfuscated dropper. This dropper deployed the WAVESHAPER.V2 backdoor, a cross-platform remote access trojan capable of running on Windows, macOS, and Linux. The backdoor is designed to collect system information, enumerate directories, and execute additional payloads, potentially enabling credential theft and further compromise. Researchers attribute the attack to UNC1069 (also known as Sapphire Sleet or linked to groups like CryptoCore/MASAN), a financially motivated North Korean-nexus threat actor active since at least 2018.
ETLM Assessment:
UNC1069, a financially motivated North Korean-linked threat actor (also tracked as Sapphire Sleet, CryptoCore, and MASAN), has been active since at least 2018 and primarily focuses on generating revenue for the North Korean regime through cyber theft. The group typically targets the cryptocurrency and Web3 ecosystem—including centralized exchanges, cryptocurrency startups, software developers in fintech, high- technology companies, and venture capital firms—using sophisticated social engineering tactics such as spear-phishing, fake job offers, impersonation of investors or recruiters on platforms like Telegram and LinkedIn, deepfake-powered Zoom meetings, and AI-enhanced lures. Once initial access is gained, they deploy custom malware (including backdoors like WAVESHAPER and downloaders) to harvest credentials, browser data, session tokens, and cryptocurrency wallets, enabling large- scale financial theft and occasionally supply-chain compromises to broaden their reach. Their ultimate goal is to steal funds that help bypass international sanctions and support the regime’s priorities – as reported in this CYFIRMA paper.
Major Incident in FBI Networks
The Federal Bureau of Investigation has formally classified last month’s intrusion into the networks used to manage wiretaps and other sensitive surveillance operations as a “major incident,” underscoring the seriousness of the breach that has already triggered a criminal investigation and prompted efforts to strengthen the agency’s cybersecurity.
According to a Justice Department notification to Congress, the FBI opened an inquiry into anomalous activity on the compromised network on February 17. The affected system contains highly sensitive law enforcement data, including information from electronic surveillance, pen registers, trap-and-trace devices, and personally identifiable information on subjects of FBI investigations. On March 23, it was determined that the intrusion met the threshold of a “major incident” – a designation reserved for breaches likely to cause significant harm to national security or expose large amounts of sensitive personal data.
ETLM Assessment:
An earlier notification to lawmakers in March described the threat actor’s techniques as “sophisticated,” noting that the intruders exploited a commercial Internet Service Provider vendor’s infrastructure to bypass FBI network security controls. The notices did not identify the suspected perpetrator or specify the full scope of data that may have been accessed or exfiltrated. The breach is suspected by researchers to have been carried out by China-linked hackers (likely the Salt Typhoon group or another actor affiliated with China’s Ministry of State Security), who used sophisticated supply-chain techniques via a commercial ISP vendor to gain access. The primary goal appears to be espionage: identifying who the FBI is actively surveilling, mapping U.S. intelligence and law enforcement targets, exposing phone numbers and metadata of monitored individuals, and gaining counterintelligence advantages against American operations.
NightSpire Ransomware Impacts the GMP Group
Attack Type: Ransomware
Target Industry: Recruitment & Staffing (Human Resources)
Target Geography: Singapore
Ransomware: NightSpire Ransomware
Objective: Data Theft, Data Encryption, Financial Gains
Business Impact: Financial Loss, Data Loss, Reputational Damage
Summary:
CYFIRMA observed in an underground forum that a company from Singapore, The GMP Group (https[:]//www[.]gmprecruit[.]com/), was compromised by NightSpire Ransomware. The GMP Group has established itself as a pioneer in Singapore’s recruitment industry, dedicated to connecting Asia’s top talent with leading organizations. With a strong presence across Southeast Asia, the company offers specialized recruitment services across a wide range of industries, positioning itself as a one-stop solution for all recruitment needs. The compromised dataset includes financial documents, salary records, and candidates’ PII, along with resumes, CVs, and other sensitive and confidential information.

Source: Dark Web
Relevancy & Insights:
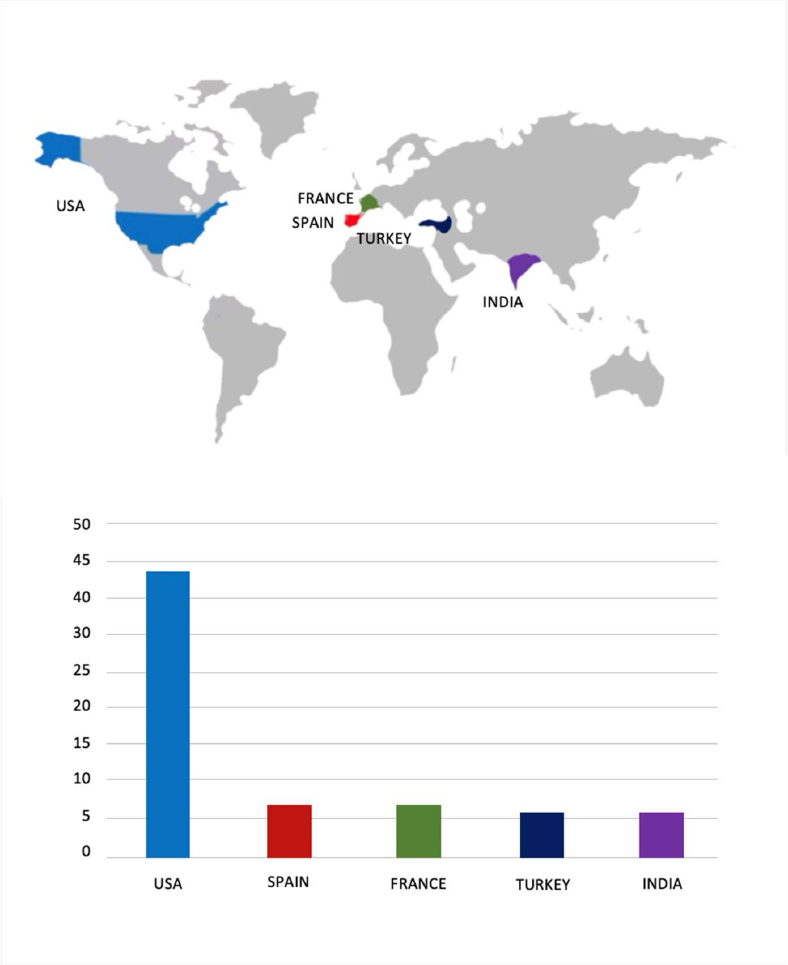
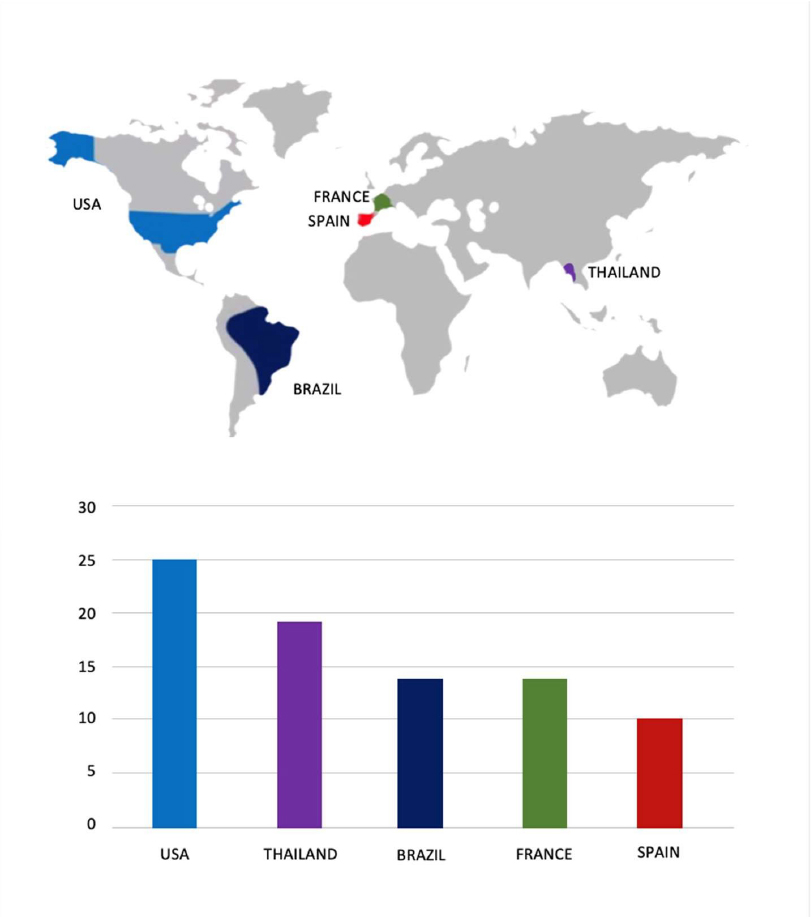
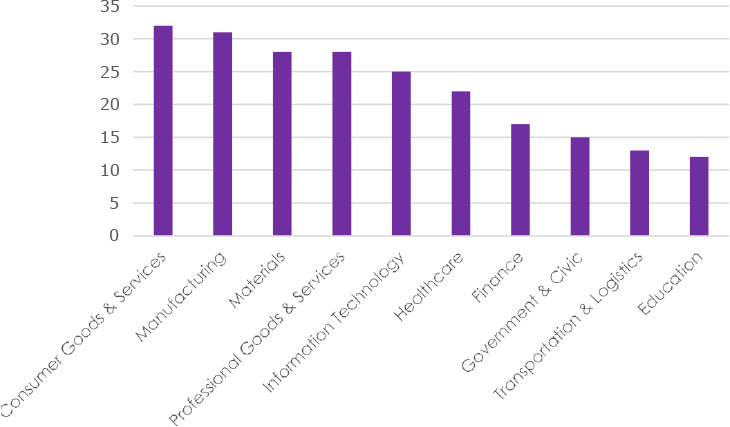
The Top 10 Industries most affected by the NightSpire Ransomware victims list from 1st Jan 2025 to 07th April 2026 are as follows: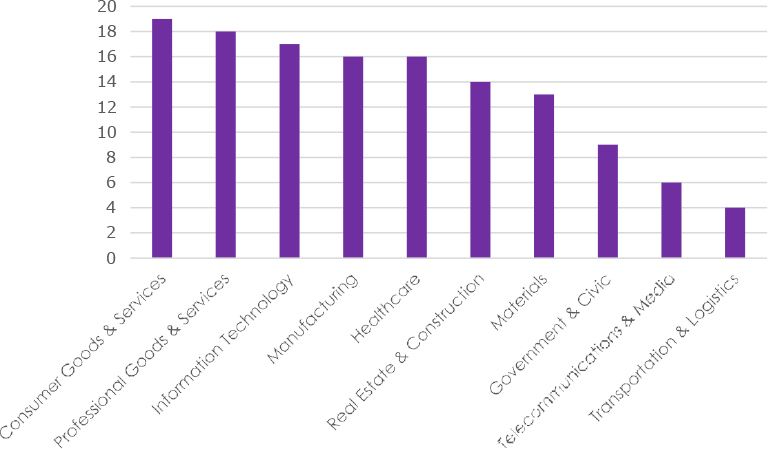
ETLM Assessment:
According to CYFIRMA’s assessment, NightSpire is a ransomware group that emerged in early 2025, marking itself as a formidable player in the rapidly evolving ransomware landscape. Despite its recent appearance, NightSpire has already gained attention for its aggressive tactics and well-structured operations
The Gentlemen Ransomware Impacts Equity Life
Summary: CYFIRMA observed in an underground forum that a company from Indonesia, Equity Life(https[:]//www[.]equity[.]co[.]id/), was compromised by the Gentlemen Ransomware. Equity Life Indonesia offers a range of life and health insurance solutions tailored for individual clients, corporate employee benefits, and retail insurance through various distribution channels. Their services include professional agency support, bancassurance partnerships, and customizable employee benefit programs to ensure the safety and well-being of employees. The data, which has been breached, has not yet appeared on the leak site, indicating that negotiations between the affected party and the ransomware group may be underway. The compromised data includes confidential and sensitive information belonging to the organization.
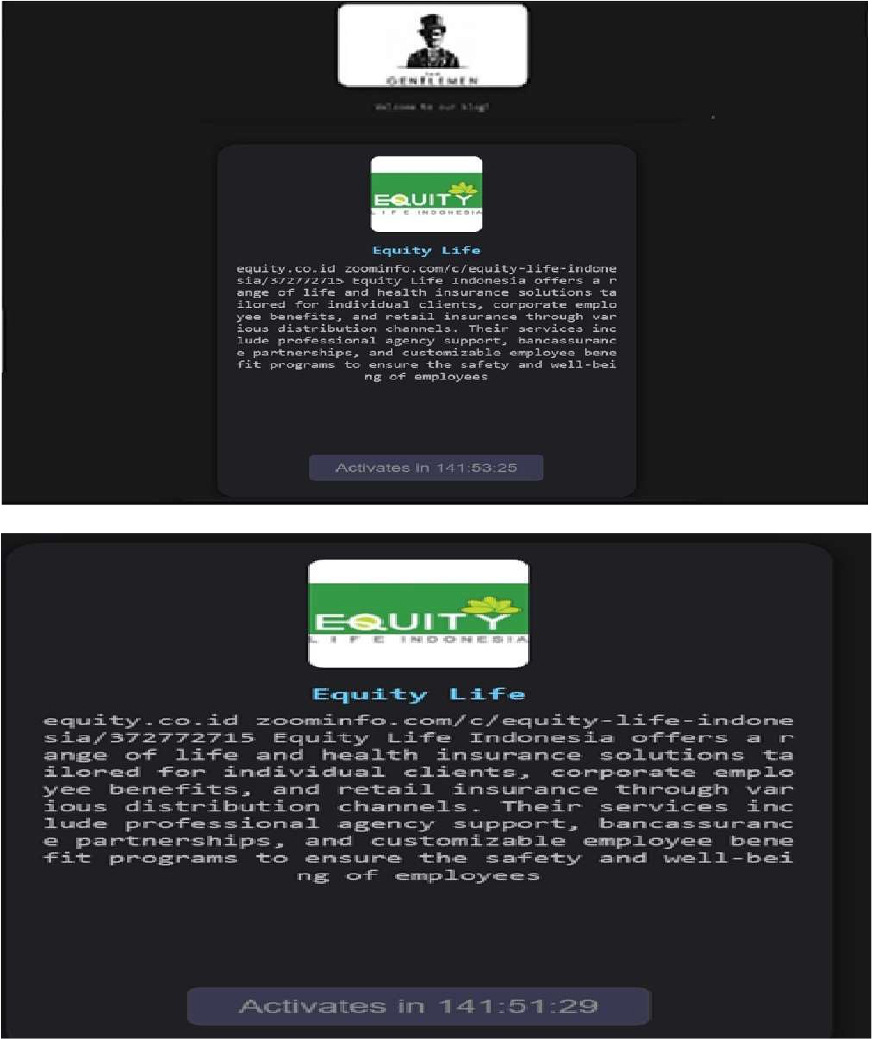
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, the Gentlemen Ransomware is a highly adaptive and globally active threat that leverages dual-extortion tactics, combining data theft with file encryption. The group employs advanced evasion and persistence techniques, supports cross-platform and scalable ransomware deployment, and conducts targeted attacks across multiple industries and geographic regions. This combination of capabilities makes it a significant risk to enterprise cybersecurity defenses, particularly for organizations with limited detection and incident-response maturity.
Vulnerability in Cisco Nexus Dashboard
Relevancy & Insights:
The vulnerability exists because authentication details are included in the encrypted backup files.
Impact:
A remote user with a valid backup file and encryption password from an affected device can decrypt the backup file and use the authentication details in the backup file to access internal-only APIs on the affected device.
Successful exploitation of the vulnerability may allow code execution as root.
Affected Products:
https[:]//sec[.]cloudapps[.]cisco[.]com/security/center/content/CiscoSecurityAdv isory/cisco-sa-nd-cbid-5YqkOSHu
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
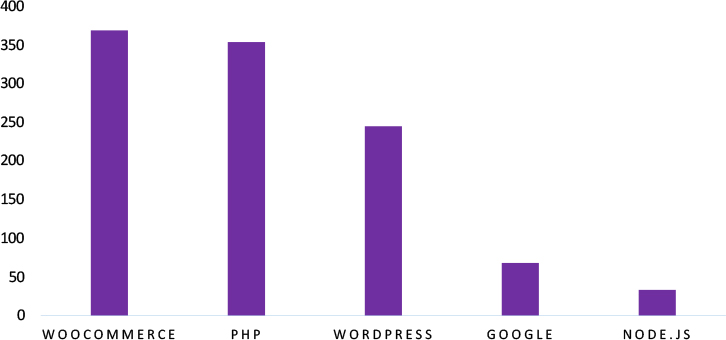
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies due to a range of vulnerabilities. The following are the top 5 most affected technologies.
ETLM Assessment
Vulnerability in the Cisco Nexus Dashboard introduces significant risks to enterprise environments that rely on centralized network and infrastructure management platforms. As the Nexus Dashboard is widely used for managing data center operations and network resources, exploitation of this vulnerability could expose sensitive credentials and enable unauthorized access across interconnected systems. Organizations leveraging such management platforms must ensure secure credential storage practices and implement strict access controls to mitigate potential risks. Addressing this vulnerability is essential to maintaining the confidentiality of sensitive data and protecting enterprise network infrastructure across industries and regions.
Everest Ransomware attacked and published the data of PT Brantas Abipraya
Summary:
Recently, we observed that Everest Ransomware attacked and published the data of PT Brantas Abipraya(https[:]//www[.]brantas-abipraya[.]co[.]id/) on its dark web website. PT Brantas Abipraya is an Indonesian state-owned enterprise (SOE) primarily engaged in the construction and infrastructure sector. The data leak includes detailed personal information of employees and their families, such as identity documents, photos, national ID numbers, addresses, phone numbers, and medical data, along with confidential HR records, competency and certification data, payroll and bank details, and sensitive information related to strategic project staff; it also exposes classified evaluations and psychological profiles of senior management and executives, internal HR and training materials, financial reports and budgets, insider personal files, and a large collection of corporate video and audio recordings of meetings and training sessions. The Total size of data compromised is approximately 236.58 GB.
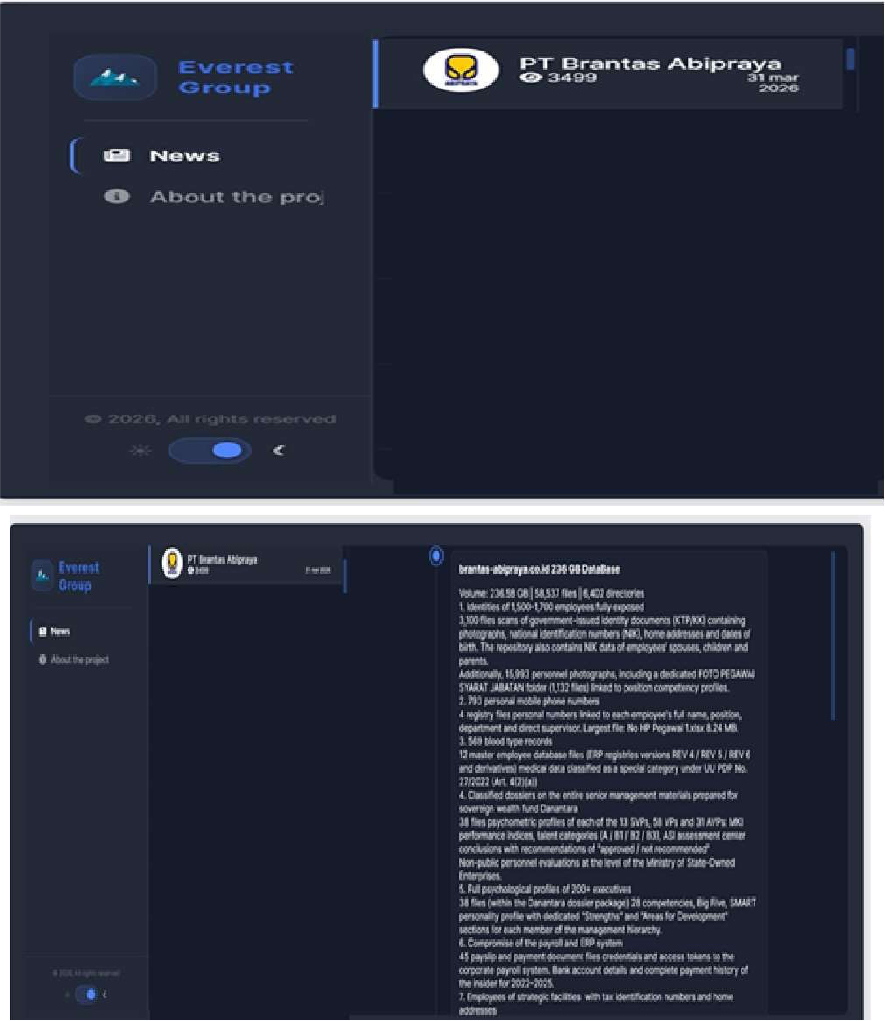
Source: Dark Web
Relevancy & Insights:
Everest is a “double extortion” ransomware gang: attackers first exfiltrate data, then encrypt systems, and finally threaten to leak or sell the stolen information unless a ransom is paid.
ETLM Assessment:
According to CYFIRMA’s assessment, Everest ransomware continues to pose a persistent and evolving cyber threat. The group is actively broadening its targeting across new sectors, expanding its role as an initial access broker, and increasingly relying on data-leak extortion as its core operational tactic. Organizations are advised to remain vigilant by strengthening access controls, closely monitoring for lateral movement and Cobalt Strike–related activity, and maintaining robust incident response and detection capabilities to mitigate the risks posed by Everest’s ongoing campaigns.
Mihnati Data Advertised on a Leak Site
Summary: The CYFIRMA research team identified a post on a dark web forum by a threat actor operating under the alias “Grubder”, who claims to possess and offer for sale a large dataset allegedly sourced from mihnati[.]com, a Saudi Arabia– based employment and recruitment platform that connects job seekers with employers.
According to the forum post, the dataset provides a comprehensive view of platform operations, including contacts, candidate profiles, and candidate experience records. The actor describes the dataset as fresh, well-structured, and organized, making it potentially valuable for research, profiling, or commercial exploitation.
Dataset Structure Overview
The threat actor claims the dataset is divided into three primary interconnected categories:
1. Contacts (Personal & Account Information)
This section allegedly contains detailed personal and contact-related data of users, including:
2. Candidate Profiles (Professional & Personal Data)
This segment reportedly includes extensive candidate profile information, such as:
3. Candidate Experience (Work History Data)
This section is said to include candidate work experience records with regional and international breakdowns:
Sale Details
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
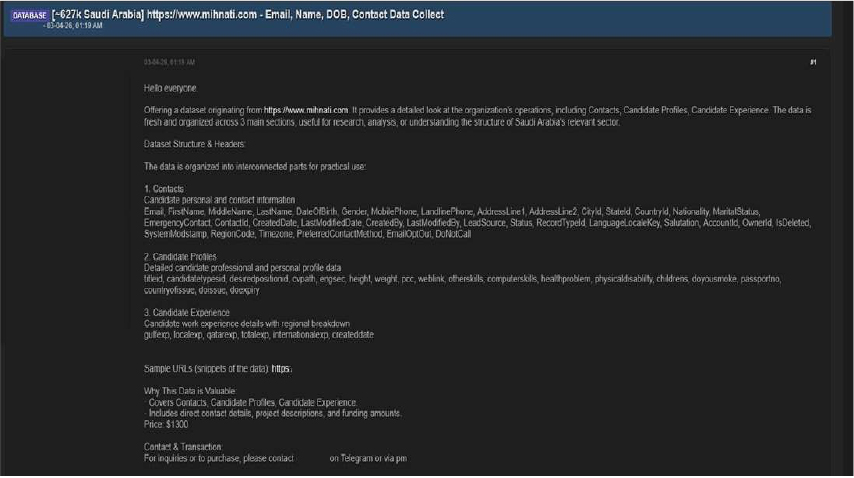
Source: Underground Forums
Trilateral Cooperation Secretariat Japan Data Advertised on a Leak Site
Summary:
The CYFIRMA research team identified a post on a dark web forum by a threat actor operating under the alias “gtavispeak”, who claims to possess and offer for sale a dataset allegedly sourced from jp.tcs-asia[.]org. The targeted entity appears to be associated with operations in Japan, and the dataset is described as containing sensitive administrative and operational data.
According to the forum post, the dataset provides a detailed overview of organizational activities, including contacts, support tickets, and content engagement records. The actor claims the data is fresh, well-structured, and organized into interconnected sections, making it potentially valuable for analysis, research, or exploitation.
Dataset Structure Overview
The threat actor states that the dataset is divided into three primary interconnected categories:
1. Contacts (Customer & Account Information)
This section allegedly includes primary customer and contact data collected from website interactions, such as:
2. Support Tickets (Customer Interaction Records)
This segment reportedly contains customer support ticket data capturing inquiries and responses, including:
3. Content Engagement (User Activity Data)
This section is said to track user interactions with platform content, including:
Additional Claims by the Threat Actor
Sale Details
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
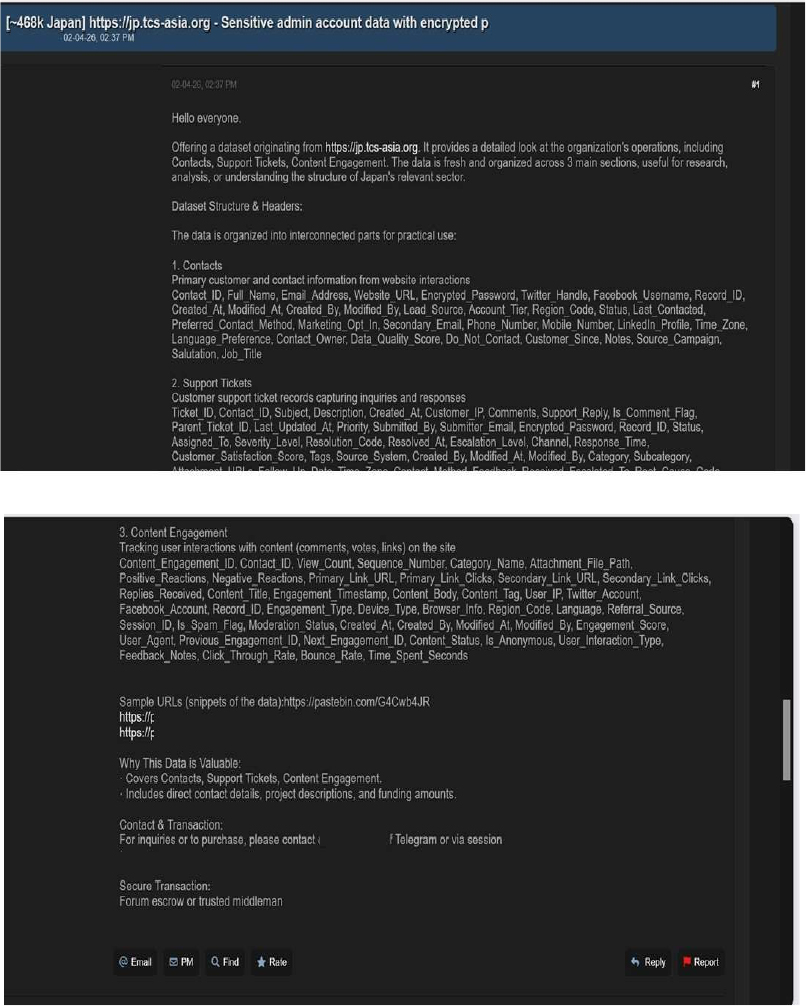
Source: Underground Forums
Relevancy & Insights:
Financially motivated cybercriminals are continuously looking for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to gain access and steal valuable data. Subsequently, the stolen data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor known as “Grubder” is assessed to be a highly active and capable group primarily engaged in data-leak operations. Multiple credible sources have associated this actor with a series of security incidents involving unauthorized access to systems and the sale or dissemination of stolen data on dark web marketplaces. These activities underscore the persistent and rapidly evolving cyber-threat landscape driven by underground criminal ecosystems and highlight the urgent need for organizations to reinforce their cybersecurity posture through continuous monitoring, improved threat-intelligence capabilities, and proactive defensive measures to protect sensitive information and critical infrastructure.
Recommendations: Enhance the cybersecurity posture by:
The CYFIRMA research team observed that Xtium, a managed service provider (formerly known as ATSG) focusing on AI-powered IT infrastructure, security, and cloud solutions, has allegedly been compromised in a massive extortion campaign. A threat actor claims to have breached the company’s network and maintained undetected access to their Veeam backup instances for approximately eight months. According to the forum post, after initial extortion negotiations with Xtium management stalled, the attacker breached the network a second time ten days later. The actor is now listing the stolen data for sale and actively soliciting Xtium’s clients directly, offering to delete their specific backups in exchange for payment.
According to the actor, the 485.8TB of allegedly compromised data includes:
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
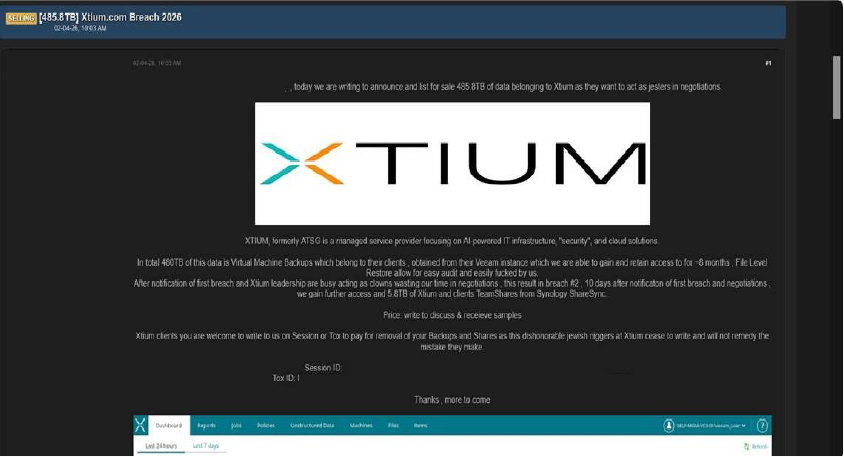
Source: Underground Forums
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
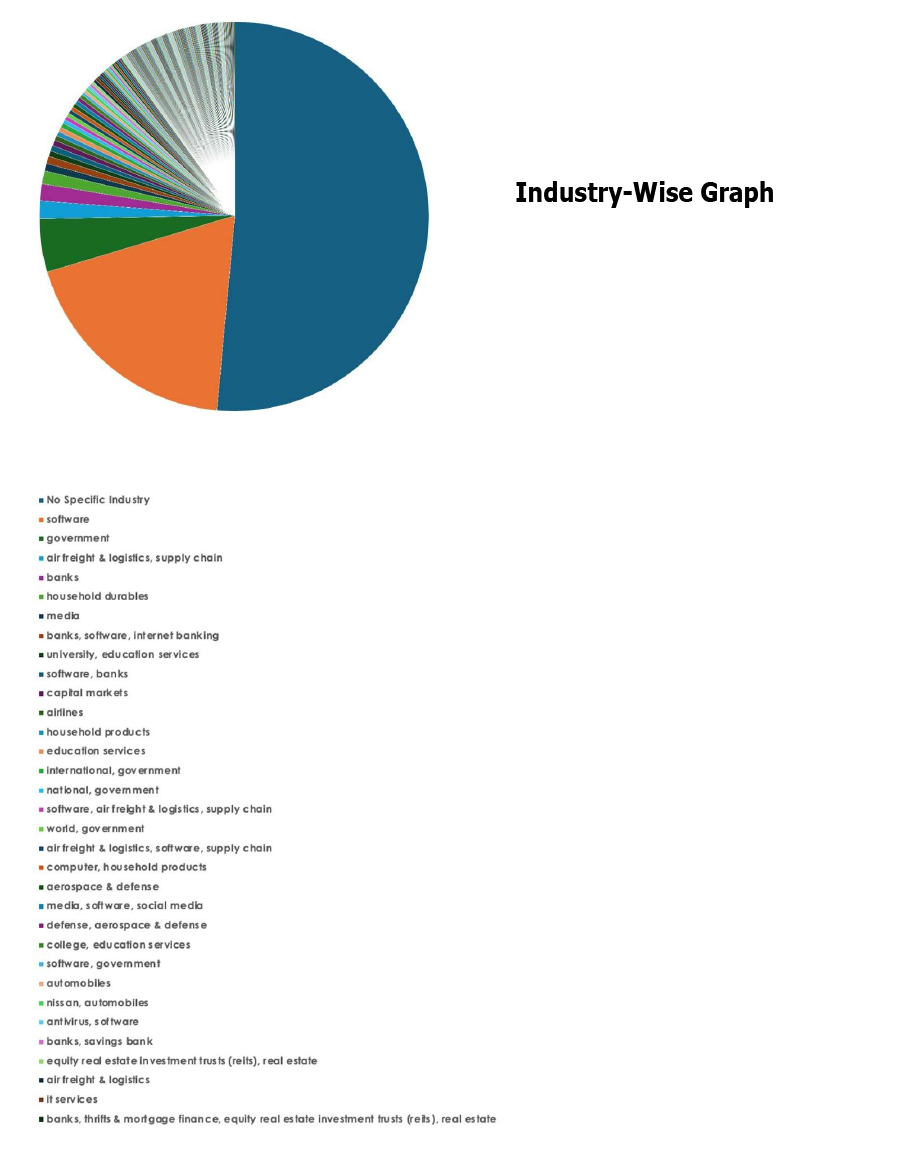
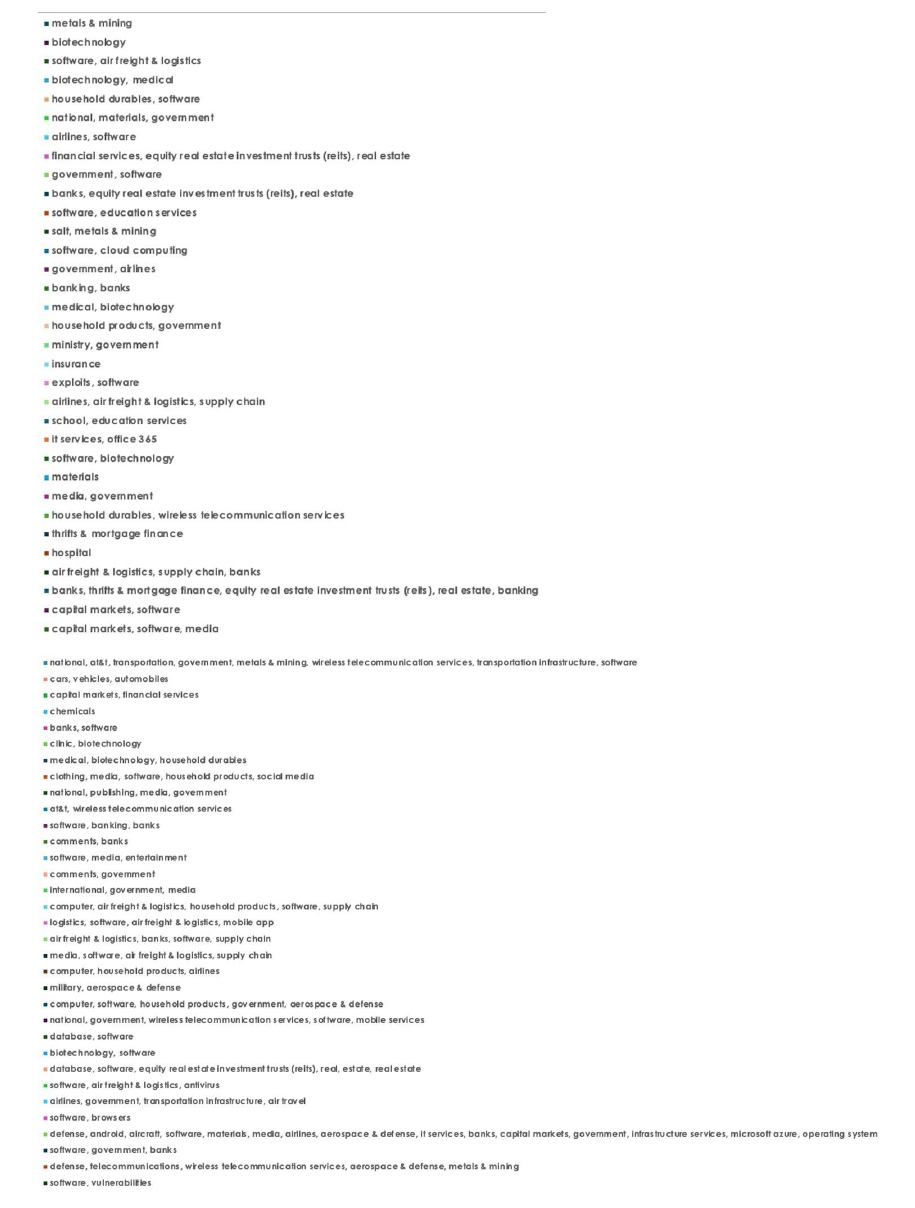
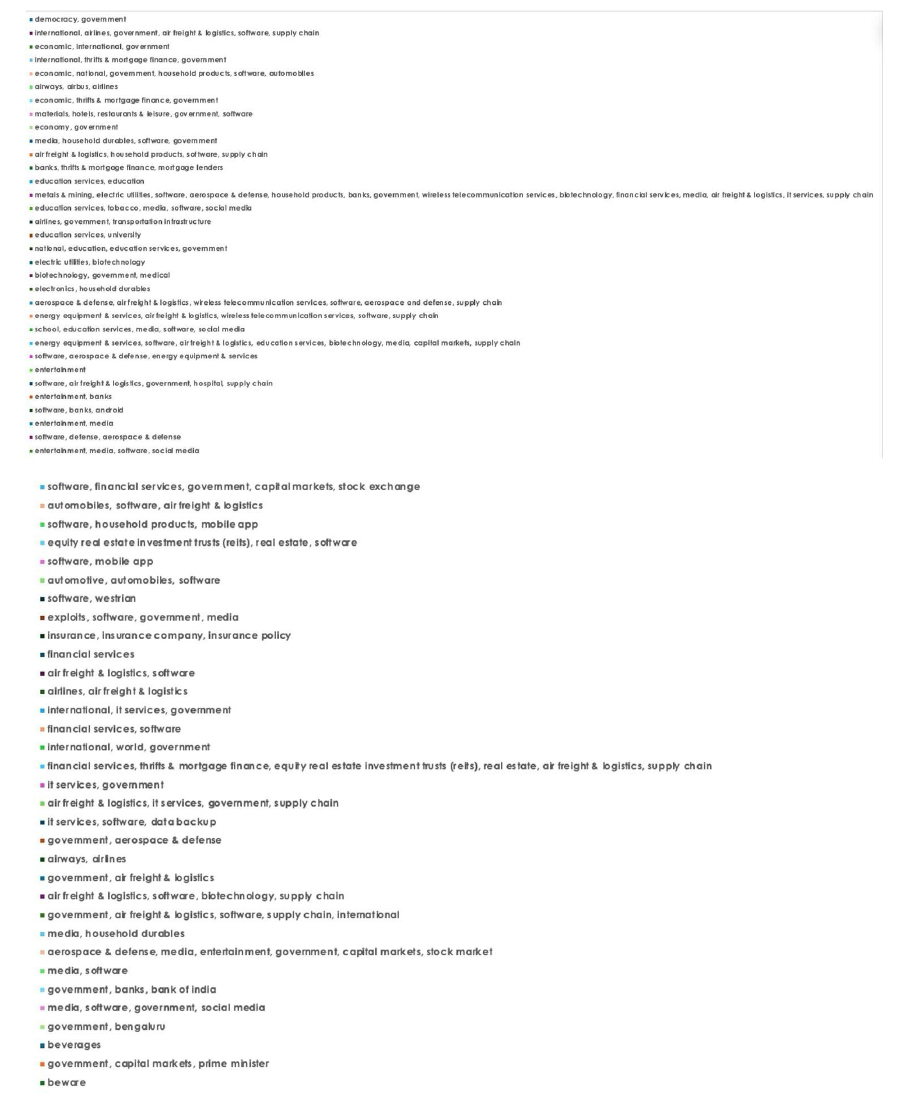
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
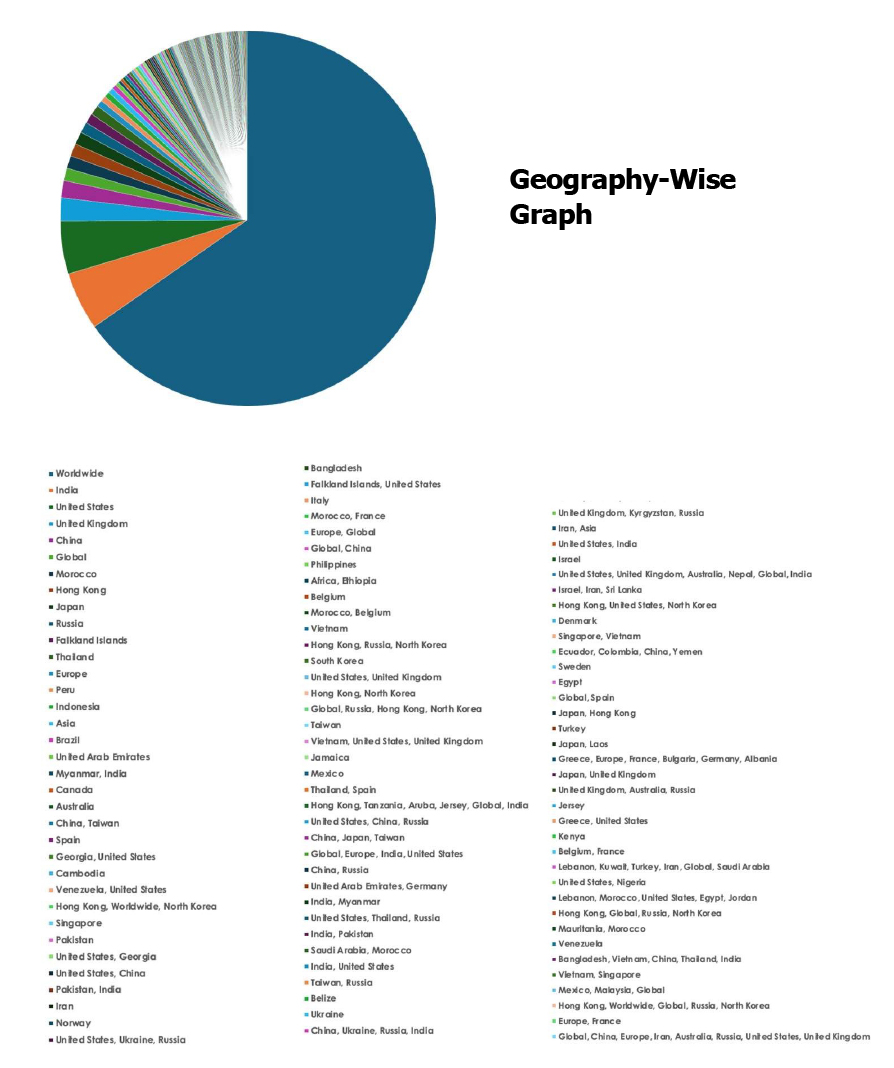
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.