


Malaysia faces a persistent and increasingly complex cyber threat environment driven by its economic growth, digital expansion, and strategic positioning in Southeast Asia. The country’s mature financial infrastructure, expanding digital government initiatives, and globally integrated semiconductor and electronics manufacturing sectors broaden its exposure to financially motivated cybercrime, underground marketplace activity, and state-aligned intelligence operations. Dark web monitoring indicates continued ransomware listings, credential resale, and access brokerage referencing Malaysian entities, alongside exploitation of publicly disclosed vulnerabilities affecting internet-facing services. Recent activity reflects sustained ransomware pressure, credential compromise, and espionage-linked intrusion attempts targeting high-value industries.
Malaysia’s geopolitical relevance further elevates its risk profile. As an ASEAN diplomatic actor and South China Sea stakeholder positioned between major U.S.-China supply chains, the country attracts sustained strategic interest. Open-source reporting and regional threat assessments indicate continued interest from China-linked espionage clusters focused on political intelligence collection, supply-chain surveillance, and technology acquisition, particularly within semiconductor and electronics sectors. Russian-aligned actors appear more opportunistic, primarily leveraging global vulnerability exploitation and credential-driven intrusion activity rather than Malaysia specific campaigns.
Threat motivations observed in recent months reflect a dual dynamic: strategic espionage objectives alongside revenue-driven extortion operations. Intelligence collection targeting defence procurement, maritime policy positioning, economic negotiations, and foreign investment activity intersects with ransomware campaigns seeking rapid financial return. Malaysia’s semiconductor and advanced electronics ecosystem remains a particularly attractive target within this context.
Regional threat reporting identifies China-linked nation-state actors such as APT41 and Mustang Panda as persistent espionage risks across Southeast Asia, with activity aligned to government, telecommunications, and advanced manufacturing sectors. Their operations typically support long-term intelligence collection and supply-chain surveillance objectives. In parallel, North Korea-linked Lazarus Group and financially motivated cybercriminal groups such as FIN7 present additional risk through credential compromise, financial targeting, and collaboration within ransomware ecosystems, placing economically significant Malaysian sectors within potential scope.
Operationally, actors rely heavily on social engineering, exploitation of internet-facing services, and third-party supply chain compromise to establish access. Ransomware affiliates leverage credential marketplaces and access brokers, while episodic hacktivist and DDoS activity emerges in response to geopolitical developments. Collectively, these factors position Malaysia as a strategically significant and consistently targeted cyber environment within the Asia Pacific region.
Malaysia continues to experience sustained advanced persistent threat (APT) activity, primarily attributed to state-linked actors operating within the Asia Pacific region. Observed campaigns indicate a concentration of activity originating from China-linked clusters, followed by North Korean and Russian-aligned operators.
China-attributed activity appears focused on strategic sectors, including government, telecommunications, technology, and manufacturing, reflecting long-term intelligence collection objectives aligned with regional geopolitical and economic interests.
North Korean-linked actors demonstrate financially motivated intrusion patterns, often overlapping with espionage objectives. Observed tactics include credential harvesting, malware deployment, and targeting of financial institutions.
Russian-attributed activity remains opportunistic and infrastructure-based rather than Malaysia specific, typically leveraging broader scanning, exploitation of exposed services, and credential reuse campaigns.
A proportion of campaigns remain unattributed, reflecting the increasing operational security of advanced threat actors and the use of shared tooling, proxy infrastructure, and false-flag techniques.
Overall, APT activity targeting Malaysia reflects a blend of strategic intelligence collection and financially motivated operations, consistent with broader regional threat dynamics.
Mustang Panda
A recent espionage campaign impacting Southeast Asia, including Malaysia, was attributed to the China-aligned threat group Mustang Panda. The operation involved the deployment of updated variants of the COOLCLIENT backdoor, delivered through DLL sideloading techniques to evade detection. The malware enabled persistent access, credential harvesting, and command-and-control communication with attacker-controlled infrastructure. Targeting reportedly focused on government and telecommunications entities, consistent with long-term strategic intelligence collection objectives attributed to China-linked clusters operating in the region.
APT41
APT41 is known for its espionage and financially motivated operations across the Asia Pacific, including activity impacting Southeast Asia. The group is identified for its dual-purpose operations, combining state-aligned intelligence collection with cybercrime campaigns such as ransomware deployment and software supply-chain compromise. APT41 frequently exploits publicly disclosed vulnerabilities in internet-facing applications to gain initial access, followed by credential harvesting, lateral movement, and data exfiltration. While not exclusively Malaysia-focused, its regional targeting patterns suggest potential risk to the Malaysian government, telecommunications, technology, and manufacturing sectors.
Lazarus Group
Lazarus Group is a North Korea-linked actor known for financially motivated intrusions targeting banks, cryptocurrency platforms, and defense-related entities across Asia Pacific. The group typically uses spear-phishing, custom malware loaders, and credential harvesting to establish persistence before conducting data theft or fund diversion. While not exclusively focused on Malaysia, its regional targeting patterns place the Malaysian financial and digital asset sectors within potential scope.
FIN7
FIN7 is a financially motivated intrusion group known for targeting payment systems and corporate networks to enable data theft and ransomware deployment. The group commonly gains initial access via phishing campaigns and weaponized documents, followed by the use of legitimate administrative tools (e.g., PowerShell, RDP) for lateral movement and privilege escalation. Although not Malaysia specific, FIN7’s historic focus on financial, retail, and hospitality sectors presents an opportunistic risk to Malaysian enterprises operating within similar payment-processing and supply-chain environments.
Malaysia continues to experience steady ransomware exposure over the past three months, with activity largely driven by a small number of active ransomware groups. January 2026 recorded the highest volume of victim listings during the monitoring period, followed by moderate activity in December 2025 and a slight decline in February 2026.
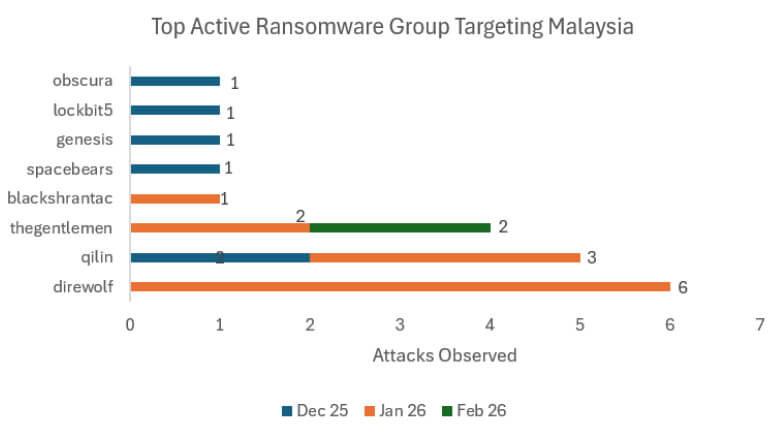
The most active groups impacting Malaysian entities during this period include Qilin and Direwolf, both of which accounted for multiple victim disclosures. Additional groups such as LockBit, SpaceBears, Genesis, Obscura, and BlackShamrock were observed listing isolated Malaysian victims, indicating opportunistic targeting rather than sustained, sector-specific campaigns.
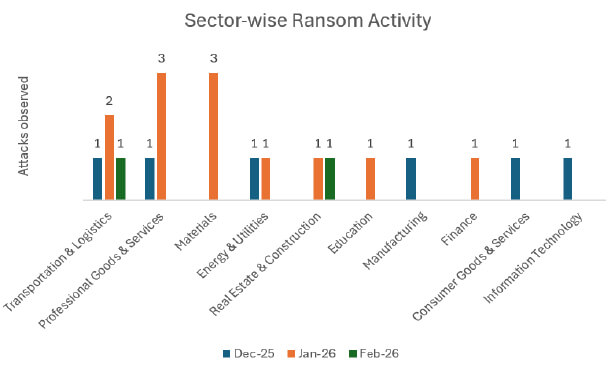
Sector analysis suggests that professional services, materials, transportation & logistics, and finance were among the most affected industries during the reporting window. The distribution of victims across multiple industries, reinforces that ransomware actors are leveraging broad exploitation and access-broker models rather than highly tailored Malaysia specific operations.
Overall, ransomware activity targeting Malaysia during the past three months reflects opportunistic, financially motivated intrusion patterns consistent with broader regional trends, with no single group demonstrating prolonged dominance.
Qilin
Qilin operates as a Ransomware-as-a-Service (RaaS) collective, where core operators maintain the encryption payload, leak infrastructure, and negotiation portals while affiliates conduct intrusions. The group has demonstrated opportunistic targeting across Asia Pacific, including Malaysia, with activity affecting professional services, manufacturing, and logistics entities.
Qilin commonly leverages access brokers and previously compromised credentials rather than highly tailored intrusion campaigns.
Observed tradecraft includes:
DragonForce
DragonForce is a RaaS operation known for aggressive leak-site publication and multi-stage extortion tactics. The group has shown regional interest in Southeast Asia and has been observed listing Malaysian victims in recent months.
DragonForce campaigns often demonstrate structured affiliate-led operations, relying on compromised RDP access and vulnerable edge devices.
Observed tradecraft includes:
LockBit
LockBit remains one of the most globally active ransomware collectives despite international law enforcement disruption efforts. Although its operational tempo fluctuated following takedown actions, affiliates continue to operate using residual infrastructure and rebranded variants.
In Malaysia, LockBit activity appears opportunistic rather than strategically focused.
Observed tradecraft includes:
Malaysia continues to face sustained cybercriminal interest driven primarily by financially motivated threat actors operating across the Asia Pacific region. While not among the highest global targets, Malaysia’s expanding digital economy, strong financial sector, and growing manufacturing footprint make it an attractive opportunistic target within broader regional campaigns.
Dark web monitoring over the recent three-month period indicates consistent mentions of Malaysian entities across underground forums and Telegram-based cybercrime channels. Discussions largely revolve around credential sales, ransomware victim listings, and financial data exposure, suggesting that Malaysia is primarily targeted through scalable intrusion models rather than highly tailored campaigns.
Analysis of targeted industries observed in underground chatter shows that Professional Goods & Services and Finance receive the highest concentration of mentions, followed by Government & Civic entities and Information Technology services. The prominence of professional services firms suggests interest in data-rich organizations that may also serve as supply chain entry points. Financial sector mentions are largely associated with credential harvesting, carding activity, and account takeover risks.
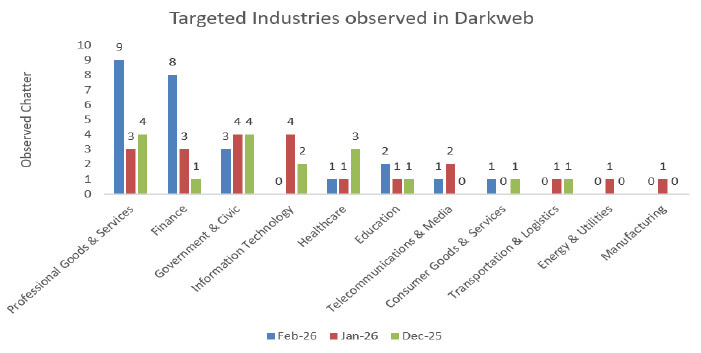
Healthcare and education sectors appear moderately represented in underground discussions, while telecommunications, logistics, energy, and manufacturing receive comparatively fewer mentions. However, lower chatter volume does not necessarily equate to lower risk; these sectors may be targeted opportunistically via exposed infrastructure rather than through direct market advertising.
Chatter topic analysis indicates that data breaches, credit card fraud, ransomware, and data leak sales dominate discussions referencing Malaysia. Credit card-related activity remains particularly prominent, reflecting continued monetization of financial data through underground marketplaces. Ransomware-related mentions show steady activity across the monitoring period, aligning with regional RaaS trends.
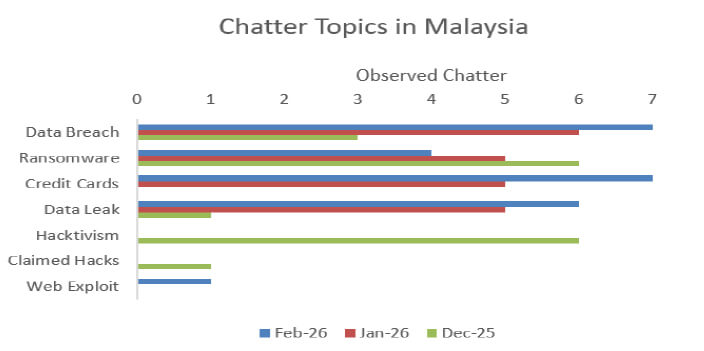
Hacktivism-related chatter appears event-driven rather than persistent. Observed spikes correspond to geopolitical developments within the region, suggesting that Malaysia may face short-term DDoS or defacement risks during periods of heightened political sensitivity rather than sustained ideological targeting.
Overall, Malaysia’s cyber threat environment is characterized by financially motivated intrusion attempts, active underground credential markets, and opportunistic ransomware activity. The data indicates that identity compromise and financial data monetization remain the primary drivers of adversarial interest in Malaysian entities.
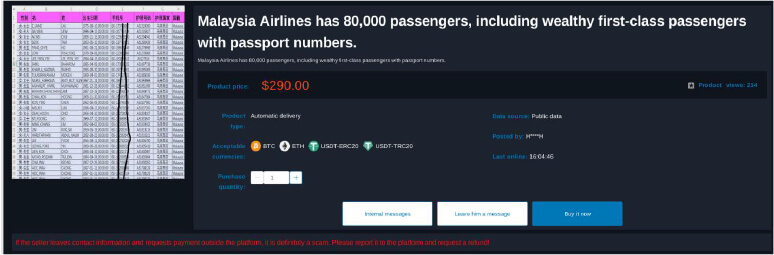
On January 29, 2026, a user was observed advertising the sale of an alleged dataset attributed to Malaysia Airlines. The listing claimed to contain information on approximately 80,000 passengers, including personally identifiable details such as names, passport numbers, contact information, and travel-related records, with particular emphasis on high-net-worth and first-class passengers.
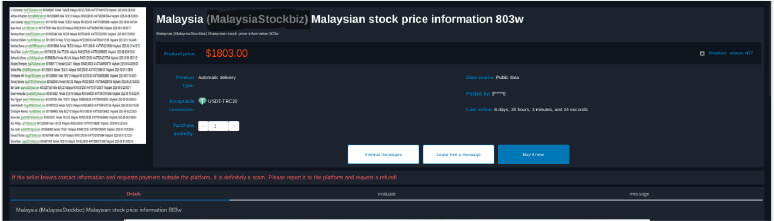
On November 25, 2025, a user was observed advertising the sale of an alleged dataset associated with MalaysiaStockBiz. The listing claimed to contain approximately 803,000 records of Malaysian stock-related information, including investor details such as names, email addresses, contact numbers, and associated financial or trading data, indicating potential exposure of sensitive financial and personally identifiable information.
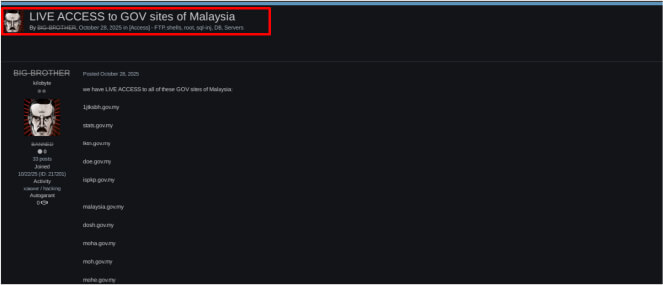
On 28 October 2025, a threat actor operating under the alias “BIG-BROTHER” was observed on an underground forum claiming to possess live access to multiple Malaysian government websites. The post alleged unauthorized access capabilities, including FTP access, web shells, SQL injection exploitation, database access, and server control, indicating a potentially severe compromise of government infrastructure associated with the government of Malaysia. The actor also listed several *.gov.my domains as affected targets, suggesting a broad attack surface and possible systemic vulnerabilities across multiple agencies.
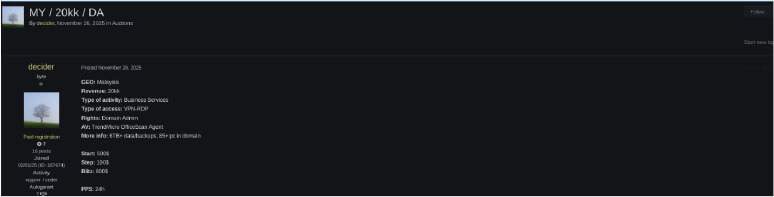
On 26 November 2025, a threat actor was observed on an underground forum advertising the sale of alleged corporate network access in Malaysia. The listing claimed VPN and RDP access to a business services environment, including domain administrator privileges, endpoint protection details, and access to approximately 85 systems with over 6TB of data and backups. The actor also indicated revenue-related information and auction pricing, suggesting the access could be leveraged for further exploitation, including ransomware deployment or data exfiltration.
On 6 December 2025, another forum user was identified seeking to purchase valid corporate accounts associated with Microsoft Office 365 environments. The buyer specified requirements for active, first-hand corporate credentials across multiple regions, including Malaysia, indicating potential intent for business email compromise (BEC), phishing campaigns, or unauthorized access to enterprise systems.
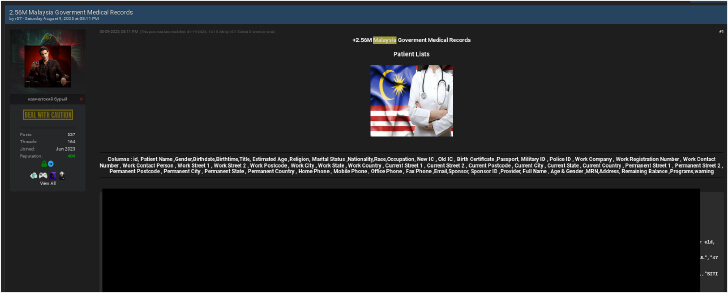
On 9 August 2025, a threat actor advertised a dataset allegedly containing over 2.56 million Malaysian government medical records. The dataset was claimed to include highly sensitive personal and healthcare information such as patient names, identification numbers, medical history, contact details, and financial or treatment-related data, indicating a significant risk of identity theft, fraud, and privacy violations linked to entities under the government of Malaysia.
In Malaysia, phishing is the primary driver of digital fraud, consistently representing over two-thirds of all reported fraud incidents.
Hacktivism in Malaysia is increasingly professionalized and politically motivated, often targeting government infrastructure to signal ideological messages. In 2024 and 2025, these groups moved beyond simple web defacements to orchestrated data leaks and threats of infrastructure disruption. There is an emerging trend of “hacktivist-to-ransomware” evolution, where groups threaten to switch from ideological disruption to financial extortion.
Past Incidents:
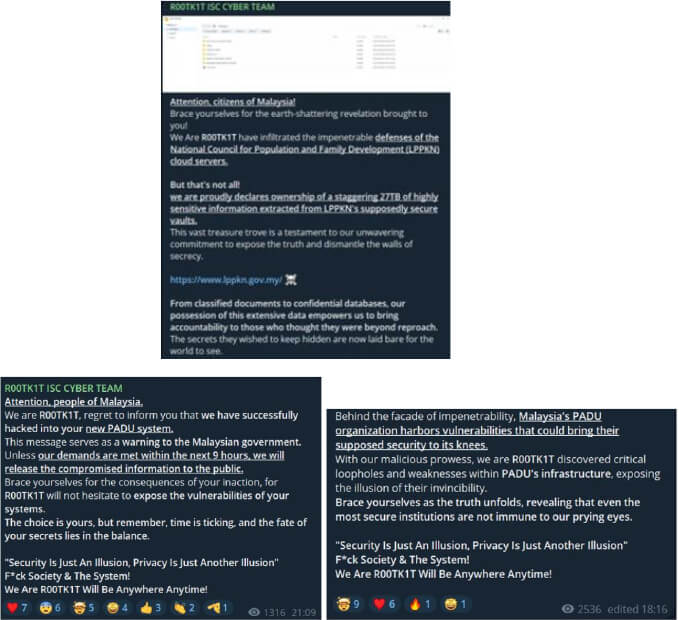
R00tK1T ISC Campaign (Jan–Feb 2024): The prolific hacktivist group R00tK1T targeted Malaysia’s digital infrastructure, including government agencies and national databases. The month-long campaign resulted in unauthorized access and multiple high-profile data breaches.
INDOHAXSEC Alert (2025): In early 2025, Cybersecurity Malaysia issued a specific alert regarding increased activity from INDOHAXSEC, targeting both public and private sector organizations.

Social engineering remains the most prevalent entry point for cybercrime in Malaysia, accounting for over 70%–77% of all fraud cases. In 2025–2026, the primary shift is toward AI-driven deception. Attackers now use Large Language Models (LLMs) to craft perfect, localized “Manglish” (Malaysian English) or Malay lures that bypass traditional “broken English” red flags. QR Code Phishing (“Quishing”) has also emerged as a critical threat, where malicious stickers are placed over legitimate codes in public spaces to harvest banking credentials.
Past Incidents:
Malaysia faces a “high frequency” DDoS risk, with over 120,849 recorded attacks in a single tracking period. While the average attack duration is relatively short (~37 minutes), the intensity has scaled dramatically. Threat actors now employ multi-vector attacks and “carpet bombing” (spreading traffic across wide IP subnets) to evade standard mitigation tools.
Past Incidents:
Critical Infrastructure Disruption (March 2025): The digital systems of Malaysia Airports Holdings Bhd (KLIA) faced a massive attack—linked to a $10 million ransom demand—that caused days of operational disruption.
High-Volume Bandwidth Attack (2025–2026): Recent reports recorded a peak DDoS bandwidth of 353.7 Gbps targeting Malaysian entities, demonstrating the significant capacity of regional threat actors.
E-Commerce “Survival” Event (2025): A Kuala Lumpur fashion startup lost RM180,000 in revenue after a targeted attack (combination of ransomware and service disruption) froze their payment systems for 4 days.
Considering Malaysia’s projected technology, business, and geopolitical landscape in 2026, the major upcoming events listed below may attract increased cyber threat activity, such as phishing campaigns, ransomware attacks, and hacktivism.
Potential Cybersecurity Focal Events – Malaysia 2026
1. High-Level Government and Critical Infrastructure Events
2. Major Technology and Business Expositions
3. Specialized Cybersecurity Conferences
These events may be subject to targeted phishing campaigns, credential harvesting, or reconnaissance activity against security professionals and participating organisations.
4. Financial and FinTech-Related Events
These events may be particularly attractive for phishing, business email compromise (BEC), and financial fraud campaigns targeting financial institutions, fintech firms, and investors.
Managing Malaysia’s external threat landscape requires consistent visibility into how the country is discussed, targeted, and exploited across the broader cyber ecosystem. This includes monitoring ransomware leak sites, underground marketplaces, exploit forums, and open-source reporting that references Malaysian organizations, sectors, or infrastructure. Given Malaysia’s economic and geopolitical relevance, external threat monitoring must account for both financially motivated actors and state-aligned espionage groups.
Organizations should maintain active tracking of ransomware disclosures, credential resale activity, and access broker listings tied to Malaysian entities. Equally important is monitoring exploit chatter related to widely used enterprise platforms, VPN appliances, and internet-facing services, as these are frequently leveraged in opportunistic intrusion campaigns. Early awareness of vulnerability exploitation trends allows defensive teams to prioritize patching and reduce exposure windows.
Threat intelligence efforts should also consider the regional activity of actors such as APT41, Mustang Panda, FIN7, and Lazarus Group, whose operational patterns intersect with Malaysia’s strategic and financial sectors. Correlating this external intelligence with internal security telemetry strengthens detection and response readiness.
Ultimately, effective ETLM is not only about monitoring threats but about turning external insight into actionable risk reduction. Integrating external intelligence with vulnerability management, incident response planning, and executive reporting will remain essential as Malaysia continues to face both strategic espionage interest and persistent ransomware activity.
Strengthen Critical Infrastructure Security
Ransomware and Financial Cybercrime Mitigation
Sector-Specific Protections
Social Engineering, Hacktivist, and DDoS Preparedness
Emerging Threat Monitoring