


This report provides a threat intelligence assessment of the cyber risk landscape affecting Hong Kong organizations between August 2025 and February 2026. The findings indicate a convergence of financially motivated ransomware operations, state-aligned espionage campaigns, and the increasing exploitation of internet-facing vulnerabilities. Ransomware groups such as RansomHouse, Cl0p, and Sinobi remained highly active, primarily targeting finance and manufacturing sectors through double-extortion tactics. At the same time, advanced threat actors, including Lotus Panda and PlushDaemon, conducted espionage-focused operations leveraging techniques such as DLL sideloading, modular backdoors, and cloud-based command-and-control infrastructure. The assessment also highlights persistent malware activity, underground data sales involving Hong Kong-related datasets, and emerging risks linked to AI weaponization, IoT exploitation, and mobile surveillance. Overall, the landscape reflects a combination of financially driven disruption and strategic intelligence gathering, requiring organizations to strengthen vulnerability management, detection capabilities, and proactive threat intelligence integration.
Ransomware Remains the Dominant Disruptive Threat
Ransomware activity continues to represent the most operationally and financially impactful risk to Hong Kong organizations. Groups such as RansomHouse, Clop, and Sinobi maintained consistent targeting momentum, with double-extortion tactics (encryption + data exfiltration) increasingly standard across campaigns.
Finance and Manufacturing Are the Most Targeted Sectors
The finance and manufacturing industries recorded the highest incident volumes. Finance remains attractive due to direct monetization opportunities and sensitive transactional data, while manufacturing is targeted due to operational downtime pressure and supply-chain leverage.
Sustained State-Aligned Espionage Activity
Hong Kong continues to face strategic targeting from advanced threat actors, including Lotus Panda and PlushDaemon. Observed tradecraft includes DLL sideloading, modular backdoor deployment, credential harvesting, and long-term persistence mechanisms consistent with intelligence collection objectives.
Cloud Platforms Increasingly Abused for Command-and-Control (C2)
Threat actors are leveraging legitimate services such as cloud storage, social media platforms, and enterprise mail systems to host or proxy C2 traffic. This tactic blends malicious communications with normal enterprise traffic, reducing detection visibility.
Exploitation of Internet-Facing Vulnerabilities as Primary Initial Access Vector
Unpatched VPN appliances, firewall platforms, web applications, and exposed administrative interfaces remain high-risk entry points. WordPress environments, misconfigured enterprise services, and outdated firmware across network devices were frequently observed as exposure points.
Remote Access Trojans (RATs) and Backdoors Enable Long-Term Access
Malware such as Shadow RAT, INET RAT, Sagerunex, and SlowStepper were observed in targeted environments. These tools facilitate reconnaissance, credential harvesting, lateral movement, and controlled data exfiltration.
Widespread Credential Theft and Infostealer Activity
Credential-harvesting malware continues to affect financial platforms, logistics firms, and SMEs. Compromised credentials increase downstream risks, including business email compromise (BEC), account takeover, and ransomware deployment.
Dark Web Data Sales Involving Hong Kong Entities
Multiple underground posts advertised alleged Hong Kong-related datasets, including resident records, telecom subscriber information, industrial databases, and financial-sector data compilations. If validated, such exposures could materially increase phishing, fraud, and identity theft risks.
IoT and Smart Infrastructure Present Expanding Attack Surface
Smart devices, building management systems, and retail IoT deployments frequently operate outside structured patch cycles, creating persistent soft targets for intrusion and lateral movement.
Zero-Click Mobile Exploit Risk Increasing for High-Value Individuals
Indicators suggest a rise in non-interactive mobile compromise techniques targeting executives, politically sensitive individuals, and high-value personnel, enabling covert surveillance and data extraction.
Emerging Risk from AI Weaponization
Underground discussions indicate increasing interest in weaponizing generative AI for phishing automation, malware generation, and prompt-injection exploitation. Rapid AI adoption without mature governance introduces additional enterprise risk exposure.
Regulatory Transition Period Creates Temporary Exposure Window
The lead-up to formal critical infrastructure enforcement may create compliance gaps that sophisticated threat actors could exploit, particularly in telecom, finance, energy, and transportation sectors.
Ransomware continues to be the most disruptive threat to Hong Kong organizations, with attacks driven by both dominant and emerging groups.
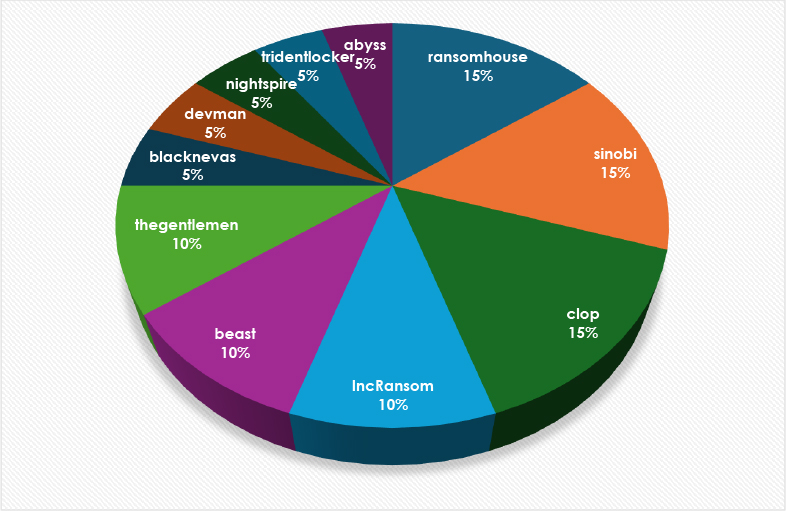
Figure 1: Ransomware Group Targeting Hong Kong
At the top tier, three groups, RansomHouse, Sinobi, and Cl0p, each represent approximately 15% of the total observed incidents. This indicates a strong operational presence and consistent campaign activity during the reporting period. Their share suggests mature operational capability, repeatable intrusion workflows, and reliable victim acquisition pipelines.
A second tier of activity is formed by IncRansom, Beast, and TheGentlemen, each contributing roughly 10% of observed cases. These actors appear active but less dominant, indicating either narrower targeting strategies or shorter campaign cycles compared to the leading groups.
The remaining portion of the landscape is composed of several lower-frequency actors, including BlackNevras, Devman, NightSpire, TridentLocker5, and Abyss, each accounting for approximately 5% of the activity. Their smaller distribution suggests opportunistic campaigns, emerging operational maturity, or limited infrastructure scale.
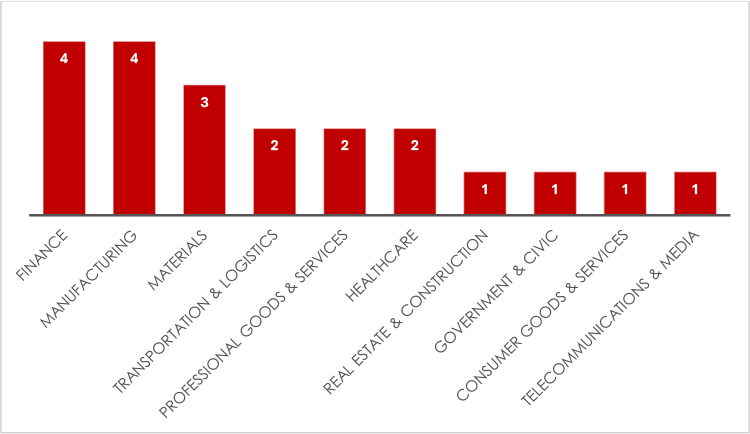
Figure 2: Industries Targeted
Finance and manufacturing appear as the most heavily targeted sectors, each recording the highest number of incidents. The strong presence of finance aligns with attacker motivations centred on direct monetary gain, access to transactional systems, and opportunities for fraud or extortion through sensitive financial data exposure. Manufacturing continues to attract ransomware operators due to its reliance on uninterrupted production processes and interconnected supply chains, where operational downtime can quickly generate pressure to meet ransom demands.
The materials sector follows with slightly lower but still notable activity. Organizations in this area often operate within complex procurement and distribution ecosystems, making them attractive targets for attackers seeking broader supply-chain leverage or indirect access to downstream partners.
Transportation and logistics, professional goods and services, and healthcare form a mid-level grouping with comparable incident counts. Transportation and logistics environments are commonly targeted because of their role in global movement networks and their dependence on real-time operational systems. Professional services organizations frequently act as data aggregators or third-party service providers, increasing their exposure to credential theft and lateral movement scenarios. Healthcare remains a consistent target due to the sensitivity of medical data and the operational urgency associated with patient services.
Lower levels of activity are observed across real estate and construction, government and civic sectors, consumer goods and services, and telecommunications and media. While incident volumes are smaller in these areas, their infrastructure importance and data exposure still present strategic value. Government-related environments may attract reconnaissance-driven activity, while telecommunications systems remain relevant due to their role in network connectivity and data transit.
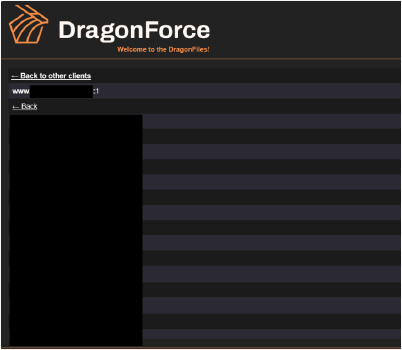
On Feb 6, 2026, the ransomware group named DragonForce reportedly released over 434GB of various stolen materials, including identification documents and other confidential files of a manufacturing company based in Hong Kong.
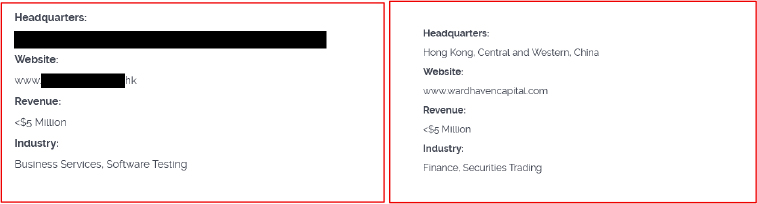
On Jan 30, 2026, the ransomware group Cl0p added a Hong Kong-based financial services provider and a Telecommunications and Media service provider to their data leak site, and allegedly exposed data associated with the organizations.
On Jan 8, 2026, the ransomware group Insomnia added a major Business Service provider based in Hong Kong to their data leak site. At the time of the report, no data had been exposed or observed in the data leak site.
On October 1, 2025, the ransomware group Sinobi exposed 250GB of financial and customer data associated with professional service providers based in Hong Kong.
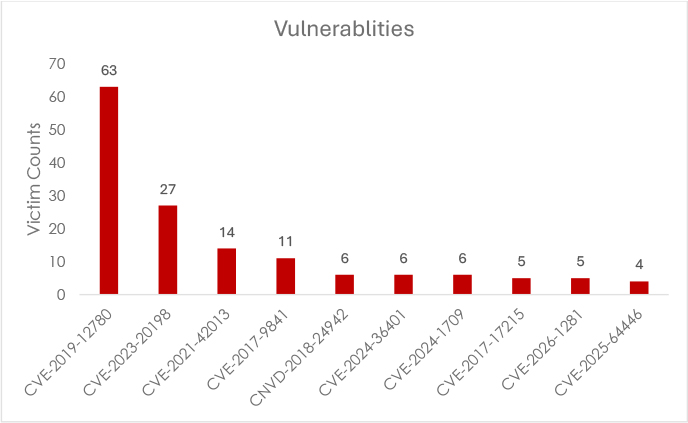
Based on their 90-day average detection rates, CVE-2019-12780 leads the list, followed by CVE-2023-20198, CVE-2021-42013, and CVE-2017-9841, highlighting both the persistence of legacy vulnerabilities and the continued exploitation of more recent disclosures. The presence of long-standing CVEs alongside 2023–2026 entries shows the evolving yet cyclical nature of cyber threats, where attackers repeatedly target known weaknesses that remain unpatched.
| CVE ID | CVSS | Products Affected | Threat Actors | Exploit Available | Exploitation Context |
| CVE-2019-12780 | 9.8 | Ivanti Pulse Connect Secure | Salt Typhoon, RansomHouse | NO | Initial access for telecom targeting |
| CVE-2023-20198 | 9.9 | Cisco IOS XE Software | Salt Typhoon, Clop, Beast | Link | Authentication bypass and persistence |
| CVE-2021-42013 | 10 | Apache Log4j 2 | Sinobi, TheGentlemen, BlackNevras | Link | RCE in Java applications |
| CVE-2024-21887 | 9.8 | Ivanti Connect Secure | Salt Typhoon, Clop, Lotus Panda | Link | Command injection for credential harvesting |
| CVE-2024-3400 | 10 | Palo Alto PAN-OS | Salt Typhoon, Beast, Abyss | Link | Unauthenticated RCE for firewall compromise |
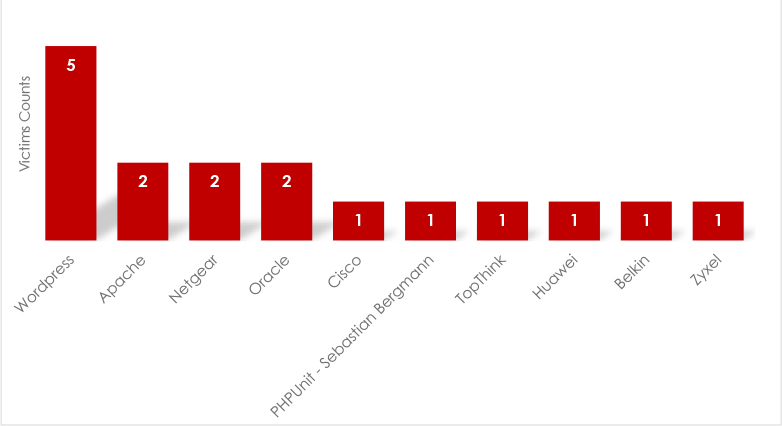
WordPress appears as the most frequently exploited platform, primarily due to vulnerable plugins, outdated installations, and exposed administrative interfaces. A second tier includes Apache Software Foundation, Netgear, and Oracle Corporation, where misconfigured web services, unpatched vulnerabilities, and exposed enterprise applications provide initial access opportunities.
Additional exposures were observed across infrastructure technologies from Cisco, Sebastian Bergmann (via vulnerable PHPUnit components), TP-Link, Huawei, Belkin, and Zyxel, typically through exposed management interfaces or outdated firmware.
Entities in Hong Kong continued to be disproportionately targeted by threat actors operating on underground forums and dark web marketplaces. Our monitoring identified numerous underground posts, data sales, and breached database advertisements specifically targeting organizations in Hong Kong across financial, government, telecom, and industrial sectors. The prevalence of Hong Kong-specific data sales, combined with active discussions among cybercriminals regarding exploitation techniques targeting local infrastructure, indicates sustained interest in the region as a high-priority target. The following analysis details the types of data being traded, threat actor activity patterns, and strategic implications for Hong Kong organizations.
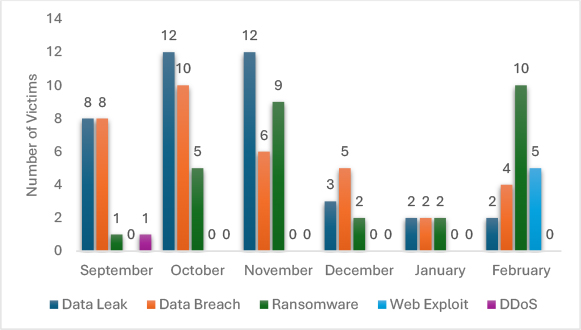
Data leak and data breach activity remain consistently dominant across multiple periods, indicating sustained attacker focus on data exfiltration for extortion and resale. The early periods show particularly high volumes, suggesting strong reliance on credential compromise, misconfigured storage exposure, and initial access through vulnerable internet-facing services.
Ransomware activity shows a gradual increase in later periods, reflecting a shift toward monetization-driven operations where attackers combine data theft with encryption-based extortion. This pattern aligns with the broader trend of double-extortion campaigns targeting operational environments.
Web exploitation activity remains relatively moderate but becomes more visible in the later stage, indicating increased use of vulnerable web applications and exposed services as initial access vectors. Distributed denial-of-service (DDoS) activity appears minimal overall, suggesting it is used selectively, likely as a secondary pressure technique rather than a primary attack method.
SALT TYPHOON (APT73) / OPERATOR PANDA / RedMike / Earth Estries / GhostEmperor
Salt Typhoon is among the most strategically consequential threat clusters tracked globally, conducting sustained telecommunications espionage operations since at least 2019 under a mandate aligned with China’s Ministry of State Security. The group represents a specialized intelligence collection capability focused on global telecommunications infrastructure, enabling Chinese intelligence services to identify, track, and monitor communications of foreign government officials, defense contractors, international organizations, and strategic competitors. Operations span more than 80 countries with at least 600 organizations formally notified of compromise. The group’s emphasis on telecommunications infrastructure reflects a deliberate strategic choice to position within the global communications backbone, providing access far exceeding direct targeting of individual organizations. Salt Typhoon’s operational maturity, zero-day exploitation capability, and rapid adaptation to patching demonstrate state-level resources and commitment to sustained telecom espionage.
Target Industries: Telecommunications, government ministries, transportation networks, lodging infrastructure, critical infrastructure operators, military-adjacent organizations
Target Technologies: Telecommunications switching systems, VPN appliances (Ivanti, Palo Alto), Cisco IOS XE routers, Cisco Smart Install, firewall systems, submarine cable infrastructure, telecommunications management platforms
Initial Access vectors: CVE-2024-21887 (Ivanti command injection), CVE-2024-3400 (Palo Alto RCE), CVE-2023-20198/20273 (Cisco IOS XE), CVE-2018-0171 (Cisco Smart Install), telecom service provider targeting, MSP supply chain compromise
Key TTPs: Credential harvesting from telecom management systems, living-off-the-land tools (PowerShell, WMI), lateral movement across infrastructure, long-term persistence, Cisco Smart Install backdoors, DLL sideloading via antivirus binaries, base64 encoding for log obfuscation, exfiltration of communications metadata
Motivations: Intelligence collection on global communications of foreign officials and defense personnel, geopolitical leverage through telecom infrastructure access, monitoring of diplomatic negotiations and military command systems, capability across government, transportation, defense networks, and transiting telecom infrastructure
Lotus Panda / Billbug / Lotus Blossom Chinese State-Linked
The group has been observed leveraging updated variants of the Sagerunex backdoor, which appears to be an evolved derivative of the previously known Billbug/Evora malware lineage.
A notable shift we have identified in this group’s operational profile is the migration of command-and-control infrastructure to legitimate cloud platforms, including Dropbox, Twitter/X, and Zimbra-based mail services, making C2 traffic significantly harder to detect through conventional network monitoring. The Zimbra variant specifically collects victim host information and exfiltrates it to an attacker-controlled mailbox, while simultaneously enabling lateral movement using the compromised account.
The group appears to be using legitimate security vendor executables for DLL sideloading, deploying credential-stealing modules capable of extracting passwords and cookies directly from Google Chrome’s credential store.
Target Industries: Government agencies, manufacturing, telecommunications, media, research institutions
Primary Technologies Targeted: Windows systems, cloud platforms (Dropbox, Twitter/X), Zimbra mail systems
Initial Access Vectors: Spear-phishing with malicious attachments, watering hole attacks, and exploitation of unpatched web applications
Key TTPs: DLL sideloading using legitimate vendor executables, Sagerunex modular backdoor deployment, cloud-based C2 through Dropbox/X/Zimbra, credential extraction from Chrome credential store, lateral movement using compromised mail accounts
Motivations: Intellectual property theft, government intelligence collection, strategic positioning within regional supply chains.
UNG0002 South Asian Origin Espionage Actor
UNG0002 has been conducting targeted operations against organizations in China, Hong Kong, and Pakistan. Our findings cover two distinct campaigns attributed to this group, with the primary campaign codenamed Operation AmberMist running from January to May 2025, with persistence and lateral movement phases overlapping with our reporting window.
Target Industries: Defense, electrotechnical engineering, energy, civil aviation, academia, medical institutions, cybersecurity, gaming, and software development.
Key TTPs: Shadow RAT delivered via DLL side-loading, with ClickFix-style PowerShell commands used for initial access. INET RAT and Blister DLL loaders have also been confirmed in our forensic analysis.
PlushDaemon
PlushDaemon, active since at least 2019. This group conducts sustained espionage operations targeting individuals and organizations across mainland China, Taiwan, Hong Kong, South Korea, the United States, and New Zealand.
Their signature implant, SlowStepper, is a modular backdoor with a toolkit exceeding 30 distinct components. Our investigation confirmed that the group deployed SlowStepper via a supply-chain attack, replacing a legitimate VPN application installer with a trojanized version, allowing implantation without raising user suspicion.
Target Industries: Financial services, telecommunications, energy, aviation
Key TTPs: SlowStepper modular backdoor (30+ command modules), OilRig infrastructure, spear-phishing, malware-as-a-service distribution
Motivations: Financial theft, intelligence gathering, geo-economic advantage in the Asia-Pacific region.
APT41 / Earth Baku / Brass Typhoon / Double Dragon — Chinese State-Aligned, Dual Mandate
APT41 is one of the most directly confirmed Chinese state-aligned threat groups targeting Hong Kong, with a documented history of operations against the city’s government entities, pro-democracy politicians, civil society activists, telecommunications providers, and technology companies. Their mandate is unique within the Chinese APT ecosystem; they simultaneously conduct state-directed espionage aligned with Beijing’s strategic economic development priorities and independently motivated financial cybercrime, including digital currency theft, financial system manipulation, and ransomware deployment, all by the same operators. In a confirmed Hong Kong-specific campaign designated Operation CuckooBees, APT41 deployed SpyLoader malware against government organizations in Hong Kong, maintaining persistence on victim networks for over a year in some confirmed cases before detection. Within the current reporting window, APT41’s most significant confirmed activity, the targeted spear-phishing campaign impersonating a US Congressman to infiltrate trade policy organizations, timed to coincide with active US–China negotiations, was geographically focused on the United States, but Hong Kong remains an active, confirmed target geography for both their espionage and cybercrime operations.
Target Industries: Healthcare, software, telecoms, financial services, gaming, semiconductor
Key TTPs: Supply-chain compromise, watering hole attacks, APT10 infrastructure reuse, data exfiltration for sale, and intelligence leverage
Motivations: Dual-use targeting government intelligence alongside financial cybercrime for personal profit, supply-chain access for persistent compromise
Evasive Panda / Daggerfly / Bronze Highland / StormBamboo — Chinese State-Aligned, Civil Society and Individual Targeting
Evasive Panda is one of the most directly and consistently confirmed Chinese state-aligned threat groups targeting Hong Kong specifically, not as an incidental geography but as a primary, deliberate target. Active since at least 2012. The group’s most sophisticated confirmed delivery mechanism is adversary-in-the-middle DNS poisoning, intercepting HTTP update requests from legitimate Chinese-language applications, including QQ, iQIYI, SohuVA, and IObit Smart Defrag, and silently substituting the legitimate update with an MgBot backdoor installer.
The CloudScout toolset, deployed alongside MgBot in confirmed intrusions, extends the group’s surveillance reach into cloud services by hijacking authenticated web browser sessions using stolen cookies. Confirmed CloudScout modules target Google Drive, Gmail, and Microsoft Outlook, with the broader toolkit assessed to cover at least 10 distinct cloud platforms.
Target Industries: Maritime, engineering, telecommunications, utilities, technology.
Key TTPs: Persistence mechanisms, exploitation of zero-days, living-off-the-land binary execution, long-term access maintenance.
Motivations: Maritime domain awareness, technology theft, expansion of Chinese maritime capabilities, and industrial espionage.
Tropic Trooper / Earth Centaur / KeyBoy / Pirate Panda — Chinese State-Aligned, Government and Infrastructure Targeting
Tropic Trooper is a long-running Chinese state-aligned espionage group active since 2011, with continuous operations spanning over 15 years through 2025-2026. Hong Kong, Taiwan, and the Philippines are confirmed as three primary target geographies, making Tropic Trooper one of the most persistently relevant threat actors for Hong Kong’s government and critical sector organizations due to its sustained, uninterrupted targeting across all three regions. The group is noted for proficiency in red team-style operational tradecraft, deliberately using open-source frameworks to develop new backdoor variants, deploying reverse proxy tools to bypass network security monitoring, and adapting their toolset rapidly when their implants are detected.
Targeted Industries: Government agencies and ministries, healthcare organizations, transportation operators, high-technology companies, telecommunications providers, human rights organizations, military and defense-adjacent organizations, and academic institutions.
Key TTPs: DLL sideloading and Phantom DLL hijacking, webshell deployment via Umbraco CMS, PowerShell-based tool execution, Active Directory enumeration and SMB lateral movement, Dropbox API-based C2 to blend with legitimate cloud traffic, multi-cloud exfiltration via Rclone, custom event log deletion for anti-forensics, SoftEther VPN for persistent encrypted access.
Malware and Tools: ChiserClient, SmileSvr, Lilith RAT, ShadowPad, Quasar RAT, Nerapack, Crowdoor, USBFerry, China Chopper webshell, Rclone, BitsAdmin.
Here is the APT37 section rewritten in the concise format:
APT37 / ScarCruft / Reaper — North Korea’s Reconnaissance General Bureau (RGB)
APT37 is a state-sponsored cyber espionage group attributed to North Korea’s intelligence apparatus, active since at least 2012. The group specializes in targeted intelligence collection against government, academic, media, and policy research organizations across the Asia-Pacific region. Between August 2025 and March 2026, APT37 expanded operations into Hong Kong, focusing on intelligence collection related to Korean Peninsula policy, regional security dynamics, and geopolitical surveillance. The group’s targeting reflects North Korea’s interest in monitoring international discussions of DPRK policy, sanctions enforcement, and China-North Korea relations. APT37 is characterized by sophisticated social engineering, cloud-based command-and-control infrastructure, and persistent surveillance capabilities designed for long-term intelligence collection.
Target Industries: Academic and policy research organizations, think tanks analyzing East Asian geopolitics, media and journalists covering North Korea, government agencies and diplomatic networks, cybersecurity researchers, and the threat intelligence community.
Target Technologies: Email systems, cloud storage services (Dropbox, Google Drive, OneDrive), Microsoft Graph API infrastructure, Hangul Word Processor (HWP) documents, compressed archives (RAR, ZIP), endpoint systems, USB-connected storage.
Initial Access: Targeted spear-phishing with security policy briefings and North Korea geopolitical updates as lures, malicious HWP documents, weaponized compressed archives containing LNK payloads, cloud-hosted payload links, conference invitation spoofing, and decoy threat-intelligence reports targeting security researchers.
Key TTPs: Abuse of trusted cloud platforms (Dropbox, Google Drive, OneDrive) for command-and-control communication, ROKRAT remote access trojan using cloud C2, BLUELIGHT cloud-based RAT leveraging Microsoft Graph API, FadeStealer malware enabling keylogging, screen capture, USB monitoring, data exfiltration, sophisticated social engineering for malware delivery and stealth maintenance, staged payload delivery through compressed archives, long-term surveillance and monitoring of target communications.
Motivations: Intelligence collection on regional policy discussions about North Korea and DPRK activities, monitoring of international sanctions enforcement mechanisms, surveillance of research communities analyzing DPRK behavior and capabilities, tracking of international diplomatic interactions involving China and North Korea relations, assessment of foreign government policy toward DPRK, and intelligence supporting North Korean geopolitical objectives.
Partners/Ecosystem: North Korea Reconnaissance General Bureau operational control, potential coordination with other RGB cyber operations, possible relationships with Chinese intelligence services for shared collection on Korean Peninsula dynamics, use of contractor relationships for technical capability development.
Shadow RAT
Shadow RAT was observed within targeted intrusion environments associated with the UNG0002 cluster. The malware was delivered primarily through DLL side-loading execution chains combined with staged loaders. Its functionality enabled persistent command execution, system reconnaissance, and controlled data exfiltration. The affected sectors included software development environments, engineering organizations, and research institutions where long-term access provided strategic intelligence value.
Target Technologies: Windows systems, software development tools and repositories, engineering workstations, research computing infrastructure.
Initial Access: DLL side-loading execution chains using legitimate vendor executables, staged loaders delivered through compromised development tools or ClickFix-style PowerShell commands, phishing with malicious archives targeting development teams.
TTPs: Persistent command execution, system reconnaissance and enumeration, credential harvesting from development environments, controlled data exfiltration of source code and technical documents, lateral movement across engineering networks, long-term access maintenance for strategic intelligence collection.
INET RAT
INET RAT was identified in follow-on intrusion stages where attackers expanded interactive control after initial compromise. This tooling supported lateral movement and credential harvesting across enterprise identity infrastructures. Activity patterns were most strongly correlated with technology providers and cybersecurity-related organizations.
Target Technologies: Windows enterprise networks, Active Directory and identity management systems, email infrastructure, VPN, and remote access systems.
Initial Access: Deployed as a secondary payload after Shadow RAT establishes initial foothold, escalation from compromised developer accounts with elevated privileges, and exploitation of trust relationships within enterprise environments.
TTPs: Interactive remote command execution, lateral movement across enterprise identity systems and domain networks, credential harvesting from identity infrastructure, email account compromise and mailbox access for data exfiltration and further lateral movement, privilege escalation to domain administrator accounts, multi-stage attack coordination with Shadow RAT for expanded control.
Infostealers
Credential-stealer malware activity remained widespread across financial and digital asset ecosystems. RedLine Stealer activity was strongly correlated with browser credential harvesting and cryptocurrency wallet targeting, particularly affecting fintech platforms and trading environments. AgentTesla campaigns were primarily associated with business email compromise workflows impacting finance and logistics operations, where attackers leveraged mailbox access to manipulate payment processes. FormBook infections were observed predominantly across small-to-medium enterprise environments in retail, trading, and manufacturing sectors, where keystroke logging and credential extraction enabled follow-on account compromise.
Target Technologies: Windows browsers (Chrome, Edge, Firefox), cryptocurrency wallet applications, email clients and web-based mail systems, point-of-sale systems, password managers
Initial Access: Spear-phishing with malicious attachments and macro-enabled documents, malvertising and compromised advertising networks, drive-by downloads from compromised websites, exploitation of unpatched browser vulnerabilities through exploit kits, trojanized software installers from unofficial sources
TTPs – RedLine Stealer: Browser credential harvesting from Chrome, Edge, and Firefox, cryptocurrency wallet targeting and fund theft, clipboard hijacking for transaction manipulation, system information harvesting for reconnaissance, browser history and autofill data exfiltration.
TTPs – AgentTesla: Keylogging on infected systems, email credential harvesting and SMTP configuration theft, Remote Desktop Protocol (RDP) credential extraction, form-grabbing and web injection for credential interception, screenshot capture for multi-factor authentication bypass.
TTPs – FormBook: Keystroke logging and form data capture, credential extraction from browsers and applications, web injection for malicious redirects, ransomware delivery and execution, DDoS botnet functionality.
Sagerunex Backdoor
New variants of the Sagerunex backdoor are actively used against Hong Kong targets. The evolution from traditional C2 infrastructure to cloud-based communication channels, specifically Dropbox, Twitter/X, and Zimbra mail, represents a deliberate operational security upgrade by the deploying threat actor, designed to blend malicious traffic with legitimate cloud service communication and evade standard network-level detection.
Target Technologies: Windows enterprise networks, government systems and workstations, manufacturing control systems and operational technology networks, telecommunications infrastructure management systems.
Initial Access: DLL sideloading using legitimate vendor executables (security software, system utilities), phishing with malicious Office documents containing macro payloaders, watering hole attacks targeting industry-specific websites, and exploitation of unpatched web applications in target networks.
TTPs: Persistent access mechanisms through multiple persistence points, privilege escalation to system and domain administrator accounts, lateral movement across enterprise networks and segmented systems, file and credential exfiltration to attacker-controlled infrastructure, modular command structure enabling rapid capability addition and tool deployment, cloud-based C2 through Dropbox/X/Zimbra for evasion, exploitation of legacy protocols for network-wide persistence.
SlowStepper Backdoor
SlowStepper is a highly modular, feature-rich backdoor deployed by PlushDaemon. With over 30 distinct operational components, the implant supports a broad range of surveillance and exfiltration capabilities. Initial deployment was confirmed via a trojanized VPN installer, a supply chain vector increasingly favoured by state-aligned actors for its ability to bypass perimeter defenses.
Target Technologies: Windows systems and servers, VPN infrastructure and appliances, enterprise gateway and network management devices, remote access systems, firewall management interfaces.
Initial Access: Trojanized VPN installers compromised at the manufacturer or distribution level (supply chain compromise), trojanized security appliance firmware updates, spear-phishing with credential stealers enabling secondary deployment, exploitation of VPN appliance vulnerabilities for direct installation.
TTPs: Remote command execution and shell access, file transfer and data exfiltration, keylogging and screen capture, system process manipulation and injection, proxy functionality for lateral movement and C2 traffic obfuscation, credential theft from memory and system stores, reconnaissance and system enumeration, anti-analysis and evasion mechanisms, persistence through multiple system restart cycles.
Agentic AI as an Offensive Weapon
There is a rapid increase in underground discussions around jailbreaking and weaponizing generative AI tools for offensive cyber operations. Specific use cases being explored by threat actors include AI-generated malware, hyper-personalized phishing lures, and adversarial attacks on AI training data. As Hong Kong enterprises rapidly adopt AI without mature governance frameworks, we assess the risk of data leakage through prompt injection and AI system compromise to be materially elevated heading into 2026.
IoT and Smart Infrastructure Exploitation
Our assessments have identified systemic vulnerabilities in IoT deployments across Hong Kong, particularly within digital signage, building management systems, and smart retail infrastructure. There is a significant increase in malware incidents targeting smart devices year-over-year, with trojans disguised as legitimate applications being the dominant delivery mechanism. These devices frequently operate outside formal patch management cycles, making them persistent soft targets.
Critical Infrastructure
With the Protection of Critical Infrastructure Cybersecurity Ordinance coming into force on January 1, 2026, we assess that the transition period before the formal designation of Critical Infrastructure Operators expected in mid-2026 represents a window of elevated risk. Threat actors aware of compliance gaps among energy, banking, healthcare, telecom, and transport sector operators may time attacks to exploit the enforcement lag, knowing that incident response and regulatory posture remain immature in many organizations.
Zero-Click Mobile Exploits for High-Value Surveillance
We identified a rising pattern of non-interactive device compromise targeting politically sensitive and high-value individuals. Evidence points to infiltration of smartphones without any user interaction, with payloads functioning as persistent backdoors granting remote access to device data, communications, and location. Given Hong Kong’s role as a political, civil society, and financial hub, we assess that executives, legal professionals, journalists, and civil society leaders in HK face elevated and growing mobile surveillance risk.
Supply Chain Compromise Escalation
Supply chain compromise through trojanized software, firmware updates, and hardware implants has emerged as a critical emerging threat vector with direct impact on Hong Kong organizations. Intelligence indicates increasing sophistication in supply-chain targeting, particularly affecting telecommunications providers, software vendors, and VPN/security appliance manufacturers serving the Asia-Pacific region.
Observed Compromise Vectors:
VPN/Security Appliance Installers: Trojanized Ivanti, Palo Alto, and Cisco VPN installers distributed to end-customers. SlowStepper deployment confirmed via compromised VPN installer supply chain by PlushDaemon. This vector bypasses traditional perimeter security and delivers backdoors directly to customer networks.
Software Update Mechanisms: Compromise of legitimate software update infrastructure enabling distribution of malware to the installed base. Particularly impactful for enterprise software and system management tools.
Hardware Backdoors: Increasing evidence of compromised network hardware (routers, switches, firewalls) with persistent backdoors at the manufacturing stage. These enable long-term access and surveillance capabilities invisible to traditional security monitoring.
Third-Party Software Libraries: Compromise of open-source package repositories and commercial library vendors enabling injection of malicious code into widely-used components. The scope can be massive, affecting hundreds of organizations simultaneously.
High-Risk Financial & Web3 Events
Hong Kong FinTech Week x StartmeupHK Festival (November 2–6, 2026): This event represents one of the highest-concentration cyber risk periods in Hong Kong’s 2026 calendar. As a major international convergence of fintech, Web3, and AI leadership, it presents a premium target environment for data theft operations, credential harvesting, spear-phishing campaigns against high-value attendees, and ransomware attacks against event organizers and participating institutions. State-aligned and financially motivated threat actors are both assessed as likely to increase operational tempo around this window.
Wiki Finance Expo Hong Kong (March 22 & July 23–24, 2026): With a specific focus on fintech, foreign exchange, and cryptocurrency, this expo creates a concentrated environment of high-value financial targets. We assess the elevated risk of cryptocurrency-related fraud, exchange platform breaches, and targeted social engineering operations against participants during both event dates.
Bloomberg Invest Hong Kong (June 10, 2026): A high-profile gathering of financial decision-makers and institutional investors makes this event a prime target for corporate espionage operations and credential harvesting campaigns. Attendee devices, event Wi-Fi infrastructure, and organizer communication channels should all be treated as elevated-risk surfaces during this period.
Emerging Technology & Infrastructure Events
Tech Fest Summit Hong Kong (May 21, 2026): This AI and robotics-focused summit attracts technology leadership and intellectual property-rich organizations, making it a target environment for IP theft operations and IoT-focused intrusion attempts against connected devices and demonstration infrastructure deployed at the venue.
Joint Conference & Exhibition 2026 Smart Cities (April 30, 2026): As a forum focused on smart city infrastructure and transportation systems, both sectors explicitly named under Hong Kong’s new Critical Infrastructure Ordinance, this event draws direct attention to organizations whose security posture is under active regulatory scrutiny. Ransomware operators and state-aligned actors targeting critical infrastructure are both assessed as opportunistic risks around this event window.
Mobility Tech Asia (March 10, 2026): Focused on electric mobility and charging infrastructure, this event introduces IoT and operational technology security risks into a conference environment. Connected charging infrastructure and EV platform demonstrations present exploitable attack surfaces for threat actors targeting industrial and transportation sector organizations.
Key Regulatory & Policy Milestones
Critical Infrastructure Cybersecurity Ordinance — Full Implementation (January 1, 2026): The formal enforcement of Hong Kong’s Protection of Critical Infrastructure Cybersecurity Ordinance across energy, IT, banking, transport, and healthcare sectors creates a window of elevated risk during the transition period. Organizations in the early stages of compliance implementation present a softer security posture, and threat actors aware of regulatory timelines may deliberately time operations to exploit the gap between legislative enforcement and operational security maturity across newly designated critical infrastructure operators.
Hong Kong Cybersecurity Outlook 2026 — Public Release (Q1 2026): The public release of the annual threat outlook document creates an intelligence windfall for adversaries, publicly documenting identified vulnerabilities, sector-specific weaknesses, and defensive gaps across Hong Kong’s digital landscape. We assess that increased reconnaissance activity against sectors and vulnerabilities highlighted in the published outlook should be anticipated in the weeks immediately following its release, as threat actors operationalize publicly disclosed findings against named target environments.
Geopolitical Context and Hong Kong’s Threat Environment
Hong Kong occupies a strategically important position on the southern coast of China as a major financial, logistics, and business hub linking mainland China with global markets. The territory’s threat landscape is shaped by its position within China’s national security framework, its historical role as an international commercial gateway, and its exposure to intensifying strategic rivalry between China and the United States.
The continued consolidation of Beijing’s control through national security legislation, the Law of the People’s Republic of China on Safeguarding National Security (2020), and the Safeguarding National Security Ordinance (March 2024) has reduced the distinction between Hong Kong’s legal and regulatory environment and mainland China in matters touching security, political activity, information control, and foreign influence. This has increased political and regulatory risk for organizations operating in Hong Kong, particularly international companies, media organizations, technology firms, and entities handling politically sensitive data.
Hong Kong remains one of Asia’s most important commercial centres, meaning Beijing has a strong interest in preserving its core functionality as a business hub even as it tightens political control. This creates a complex environment where the city remains open for commerce but increasingly restrictive in matters perceived to touch sovereignty, subversion, or state security.
Hong Kong is directly exposed to the broader deterioration in U.S.-China relations, including sanctions, export controls, restrictions on advanced technology, and disputes over autonomy. As a global financial node with exposure to both Western and Chinese capital, Hong Kong is especially vulnerable to disruptions from sanctions escalation, regulatory fragmentation, and crisis scenarios affecting cross-border payments, logistics, and digital infrastructure.
Hong Kong authorities reported a record 15,877 cybersecurity incidents in 2025, a 27 percent year-on-year increase, with AI-enabled attacks, phishing, and supply chain compromise highlighted as leading risks. As a dense, hyperconnected urban economy, Hong Kong presents an attractive target for cyber espionage, financially motivated crime, and disruptive operations. Compromise in Hong Kong can generate outsized downstream effects across regional supply chains and corporate networks.
Given Hong Kong’s political sensitivity and proximity to mainland Chinese state priorities, any regional crisis involving China, Taiwan, or the South China Sea could quickly generate cyber and informational spillover effects. Cyber operations offer a means of operating below the threshold of overt confrontation. In any major confrontation involving China and the United States or China and Taiwan, Hong Kong would almost certainly face heightened cyber risk, stronger political scrutiny, increased pressure on critical infrastructure, and possible attempts to control information flows.
Note: The authenticity of the breaches below remains unverified at the time of reporting, as the claims originate solely from the threat actors.
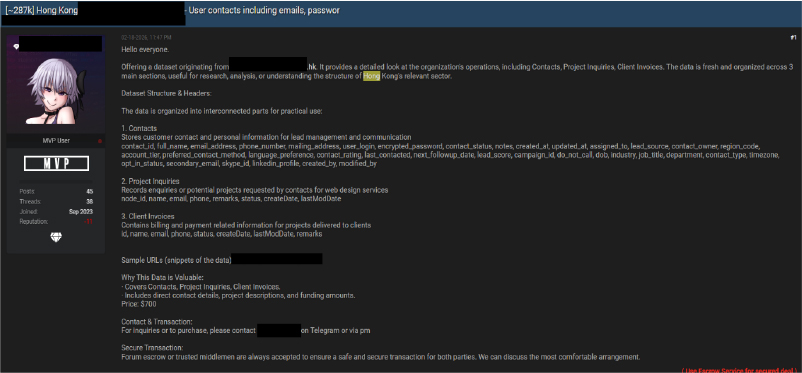
On Feb 18, 2026, a post advertises the sale of a Hong Kong–based dataset allegedly containing user contact information, including emails and passwords. The seller claims the data is structured into organized sections such as contacts, project inquiries, and client invoices, making it suitable for research or analysis purposes. The dataset is described as recent, well-structured, and priced at $700, with transactions conducted via private contact and escrow options offered for security.
On Feb 11, 2026, an underground forum post under the title “Hong Kong Stock Investment.” The post appears to promote or share stock-related information, potentially including stock codes and trading details. The user profile section highlights community engagement through displayed reputation points, likes, and total posts. The main content area suggests that stock data or investment insights are being discussed.
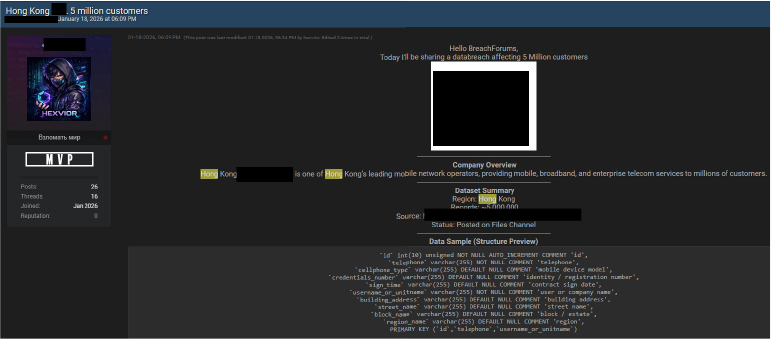
On Jan 18, 2026, a post in an underground forum advertised an alleged data breach involving a Hong Kong-based telecom provider, claiming exposure of approximately 5 million customer records. The seller states the data originates from a mobile communications subscriber database and includes fields such as ID numbers, phone numbers, usernames, email addresses, contract details, and address information. The breach is presented as recently posted and available via a file channel, with a sample database structure shown to demonstrate the scope of compromised information.
On Jan 12, 2026, a file linked to a Hong Kong Monetary government entity was being shared in an underground Telegram channel, allegedly linked to Hong Kong’s financial sector. The description references the official website of the Hong Kong Monetary Authority and claims a total of “300W” (likely 3 million) records. The content suggests a potential data compilation associated with Hong Kong’s financial domain, which, if legitimate, could pose significant risks, including financial fraud, phishing, identity theft, and targeted attacks against individuals or institutions connected to the Hong Kong financial ecosystem.
On Jan 6, 2026, a threat actor advertised the sale of a Hong Kong-based industrial product database. The post claims the dataset contains approximately 106,000 entries, including brand names, contact emails, phone numbers, system IPs, and detailed product-related metadata (e.g., product categories, descriptions, images, and timestamps). The seller describes the data as “fresh” and not publicly available, offering samples upon request and accepting escrow payments. If authentic, the dataset could expose sensitive business information and increase the risk of phishing, business email compromise (BEC), supply chain targeting, and corporate reconnaissance against affected Hong Kong industrial entities.
On Aug 25, 2025, a threat actor is advertising the sale of a Hong Kong residents’ database on a cybercrime forum. The post claims the dataset contains approximately 2.8 million records, including names, phone numbers, and HKID details. The seller states that duplicate entries have been removed based on phone numbers and offers escrow payment options. Sample data is reportedly available upon request, with contact directed via Telegram.
The Hong Kong threat landscape is defined by a dual risk dynamic: financially motivated ransomware groups driving operational disruption, and state-aligned actors conducting sustained espionage campaigns. The increasing abuse of legitimate cloud services, exploitation of exposed infrastructure, credential-centric attacks, and supply-chain compromise reflect a shift toward stealthier, more persistent intrusion models.
Finance, manufacturing, telecom, and critical infrastructure sectors remain structurally high-value targets. At the same time, dark web data trade, IoT exposure, and emerging AI-enabled attack methodologies are expanding the overall attack surface.
Organizations must assume continued targeting and prioritize resilience, detection maturity, and rapid response capability. Proactive intelligence operationalization, strong vulnerability governance, and continuous threat hunting will be critical to reducing dwell time and mitigating strategic and financial impact moving forward.
Enterprise Ransomware Resilience
With sustained activity from ransomware groups such as RansomHouse, Cl0p, and TheGentlemen, we recommend:
Supply Chain & Third-Party Risk Governance
Given supply-chain compromise patterns observed in campaigns linked to PlushDaemon, we recommend:
Cloud & AI Security Governance
With increasing abuse of cloud infrastructure and emerging AI-related threats:
Critical Infrastructure Readiness
In view of increasing regulatory and threat pressure:
IoC Operationalization
As IoCs are provided in this report, we recommend:
Exploitation Monitoring & Patch Validation
Given observed exploitation trends:
Detection for RAT & Backdoor Activity
Malware families observed include:
We recommend:
Cloud-Based C2 Detection
As certain actors leverage legitimate platforms for C2:
Credential Theft & Infostealer Defense
Given widespread infostealer activity:
Continuous Threat Hunting
We recommend monthly intelligence-led hunts focusing on:
We can provide structured hunt queries aligned to the TTPs identified in this report.
Dark Web & Data Leak Monitoring
Given the active underground sale of Hong Kong-related datasets:
Network Segmentation & IoT Hardening
Due to IoT and smart infrastructure risks:
Executive & Mobile Security Controls
In response to zero-click mobile exploit risks: