


Taiwan’s threat landscape in 2026 remains one of the most dynamic and geopolitically charged in the Indo-Pacific region. As a global semiconductor powerhouse, a key node in international supply chains, and a focal point of strategic competition between major powers, Taiwan faces persistent cyber, information, military, and economic pressure. The threat environment is characterized by sustained activity from state-sponsored advanced persistent threat (APT) groups, primarily linked to the People’s Republic of China (PRC), alongside opportunistic cybercriminal actors and influence operations. These activities range from cyber espionage and intellectual property theft to disinformation campaigns and critical infrastructure reconnaissance. The convergence of geopolitical rivalry, technological competition, and regional military signalling has elevated Taiwan into a priority target set for both strategic intelligence collection and pre-positioning operations that could support future contingencies.
Official assessments report an average of approximately 2.63 million daily intrusion attempts against critical infrastructure in 2025, marking a 6 percent year-on-year increase and a more than 100 percent rise since 2023. Although the dominant threat originates from PRC-linked advanced persistent threat groups, Taiwan’s exposure is influenced by wider geopolitical dynamics.
Recent U.S.–Iran escalations involving cyber activity demonstrate how interconnected hybrid conflicts can indirectly affect regional security environments, including resource prioritization and defensive postures in the Indo-Pacific. Collectively, these factors position Taiwan at the forefront of strategic cyber competition and sustained state-sponsored pressure.

This cyber threat landscape report provides a comprehensive, current overview of the key drivers, actors, methods, and vulnerabilities shaping Taiwan’s security environment in 2025 and into early 2026. By synthesizing official intelligence insights and observed trends, it equips decision-makers, security teams, and stakeholders with actionable context to prioritize defenses, allocate resources, strengthen international partnerships, and enhance overall resilience against escalating state-directed cyber campaigns.
Taiwan’s security environment is profoundly shaped by escalating U.S.–China strategic rivalry.
The most prominent state-sponsored groups actively targeting Taiwan in recent assessments (particularly throughout 2025 and into early 2026) are predominantly linked to Chinese state interests. These actors focus on espionage, long-term access maintenance, intellectual property theft (especially in technology and semiconductors), and preparatory positioning against critical infrastructure, often as part of broader hybrid pressure tactics.
| APT Designation | Common Aliases | Key Sectors Targeted in Taiwan | Likely State Affiliation / Notes |
| APT41 | Winnti, Barium | Semiconductor firms, telecommunications, healthcare networks, software supply chains | Widely attributed to PRC Ministry of State Security (MSS)-linked actors |
| APT40 | Leviathan, TEMP.Periscope | Maritime industries, naval contractors, research institutions, government entities | Associated with Hainan-based MSS operations |
| APT27 | Emissary Panda, LuckyMouse | Central and local government agencies, aerospace, energy providers, defense suppliers | Linked to PRC state intelligence elements, historically tied to PLA/MSS activity |
| Volt Typhoon | Bronze Silhouette | Critical infrastructure, telecom providers, energy grids, transportation networks | Attributed by multiple governments to PRC state-sponsored operators, reportedly aligned with PLA Strategic Support elements |
| Flax Typhoon | Ethereal Panda | Government ministries, education sector, manufacturing, IT service providers | Assessed as PRC state-backed cyber espionage group |
| BlackTech | Circuit Panda, Canary Typhoon, Earth Hundun | Government agencies, communications and transmission networks, science parks, industrial and technology hubs | Assessed as Chinese state-sponsored, frequently linked to MSS-associated activity |
| Mustang Panda | Basin, Bronze President, Twill Typhoon | Government administration, energy infrastructure, diplomatic entities, administrative networks | Attributed to Chinese state intelligence, commonly associated with MSS |
| UNC3886 | (Tracked under multiple vendor designations) | Government entities, science parks, semiconductor and high-tech manufacturing sectors | Evaluated as PRC state-linked actor with emphasis on stealthy, long-term persistence |
| Lazarus Group | Hidden Cobra, APT38, Guardians of Peace | Financial institutions, cryptocurrency exchanges, tech/finance sectors (historical heists) | North Korean state-sponsored (Reconnaissance General Bureau/RGB-linked); primarily financial cybercrime with occasional espionage overlap |
| NoName057(16) | 05716nnm, Nnm05716 | Government sites, financial services (e.g., Taipei Stock Exchange, Mega Financial, Chang Hwa Bank), airports, tax/aviation agencies | Pro-Russian hacktivist collective; DDoS-focused, ideologically aligned with Russia. Historically Conducted 50+ attacks after President Lai’s Russia-Far East remarks; used DDoSia tool; disrupted by Operation Eastwood (July 2025) |
| Cyber Army of Russia | People’s Cyber Army, CARR (Reborn variant) | Government, financial, critical infrastructure (aligned with NoName057(16) targets) | Decentralized pro-Russian hacktivist group; initially Ukraine-focused, later collaborated on Taiwan DDoS campaigns; suspected loose GRU connections in broader operations |
| RipperSec | (Various Telegram operations) | Government and financial platforms (coordinated with NoName057(16) in Taiwan wave) | Pro-Muslim/pro-Russian hacktivist group (Malaysia-based); politically motivated DDoS campaigns against Taiwan attacks using tools such as MegaMedusa |
Reconnaissance and Network Mapping
A substantial portion of hostile cyber activity targeting Taiwan involves sustained scanning and probing of public-facing systems and critical infrastructure networks. These operations are designed to identify vulnerabilities, map network architecture, and maintain updated targeting intelligence to support future access operations.
Supply Chain Compromise
Adversaries increasingly leverage third-party vendors, managed service providers, and software update mechanisms to gain indirect access to primary targets. By exploiting trusted relationships within Taiwan’s semiconductor, manufacturing, and technology ecosystems, threat actors can infiltrate multiple downstream organizations simultaneously. Such operations enable stealthier intrusion pathways and amplify operational impact across interconnected networks.
Credential Theft and Spear-Phishing
Targeted phishing campaigns remain a primary intrusion vector, particularly against government officials, military personnel, and employees within critical infrastructure sectors. By compromising legitimate credentials, threat actors are able to bypass perimeter defenses and establish trusted access within sensitive environments.
Malware Deployment and Persistent Access
Following initial compromise, operators frequently deploy custom backdoors, remote access tools, and stealthy malware implants engineered for long-term persistence. Many of these payloads are designed to remain dormant, enabling covert access for extended periods and supporting both intelligence collection and contingency planning.
Data Exfiltration Operations
Cyber espionage campaigns focus on the theft of classified government information, defense planning materials, advanced industrial research, and sensitive personal data linked to key officials. Such intelligence can provide strategic, economic, or coercive advantage during periods of heightened tension.
Pre-Positioning Within Critical Infrastructure
A defining characteristic of observed activity is deliberate pre-positioning within essential sectors, including energy, telecommunications, and high-technology manufacturing. By embedding persistent access mechanisms, adversaries may retain the capability to disrupt or degrade services rapidly in the event of geopolitical escalation, reflecting a broader state-sponsored strategy centred on long-term operational readiness rather than immediate disruption.
Note: The authenticity of the breaches below remain unverified at the time of reporting, as the claims originate solely from the threat actors.
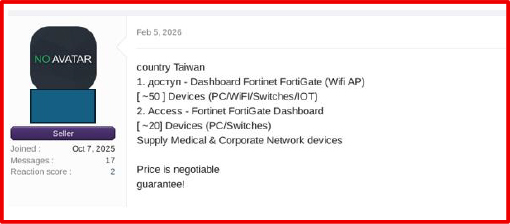
On February 5, 2026, a threat actor advertised on a cybercrime forum the sale of alleged Fortinet FortiGate dashboard access linked to organizations in Taiwan supporting medical and corporate network environments. The listing claims access to one environment managing approximately 50 devices (PCs, WiFi, switches, IoT) and another managing approximately 20 devices (PCs and switches). Pricing was described as negotiable, and the seller claimed a guarantee.
If authentic, unauthorized access to FortiGate management interfaces could enable network reconfiguration, traffic monitoring, credential harvesting, and potential lateral movement within the affected environments, posing significant operational and security risks.
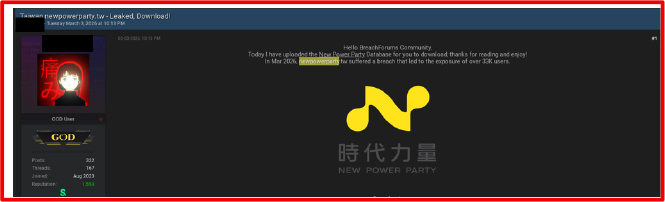
On March 3, 2026, a threat actor posted on a cybercrime forum claimed to have leaked the database of Taiwan’s New Power Party. The post alleges that the organization suffered a breach in March 2026 resulting in the exposure of more than 33,000 user records.
The threat actor stated that the database was uploaded and made available for download, with access restricted behind a forum credit-based paywall system. No technical details regarding the intrusion vector, data fields exposed, or proof-of-data samples were publicly disclosed in the visible portion of the post.
If authentic, the exposure of user data linked to a political organization could pose risks including phishing, identity theft, reputational damage, and potential targeting of registered members or supporters. Further validation would be required to confirm the legitimacy, scope, and impact of the alleged breach.
On February 8, 2026, a threat actor posted on a Russian-speaking cybercrime forum advertising the auction of Domain Admin access to a Taiwan-based manufacturing company, allegedly valued at approximately USD 20 million. According to the listing, the auction was initiated with a starting bid of USD 1,250, a bid increment of USD 250, and a “Blitz” (buyout) price of USD 3,000.

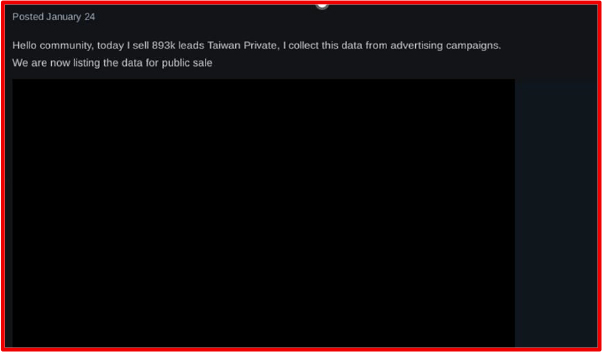
On January 24, 2026, a threat actor on a Russian-speaking cybercrime forum advertising the sale of 893,000 Taiwan-based private leads. The post was published in a section typically associated with spam, mailings, databases, responses, and mail dumps. In the listing, the actor claims the data was collected from advertising campaigns and is now being offered for public sale.
The exposed sample entries appear to include full names, Taiwanese phone numbers (+886), personal email addresses (Yahoo, Gmail, iCloud, Hotmail, etc.), and country identifiers (Taiwan). If authentic, the dataset could present significant risks including:
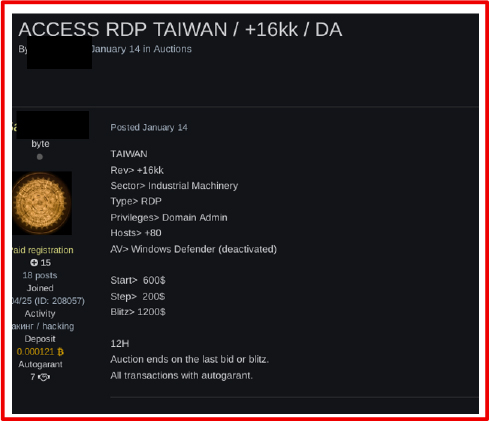
On January 14, 2026, a threat actor advertised on a Russian-speaking cybercrime forum the auction of RDP access with Domain Admin privileges to a Taiwan-based company in the Industrial Machinery sector, reportedly generating over USD 16 million in revenue. The listing claimed access to more than 80 hosts, with Windows Defender allegedly disabled.
The auction started at USD 600, with a USD 200 bid increment and a USD 1,200 buyout option, and was set to run for 12 hours via an escrow (autogarant) system. If legitimate, such high-level access could enable full network compromise, including ransomware deployment, data theft, and operational disruption.
On December 31, 2025, a threat actor posted on a Russian-speaking cybercrime forum advertising the sale of VPN and Local Administrator access to a Taiwan-based manufacturing company. The listing claims the targeted organization generates approximately USD 65 million in annual revenue and operates more than 40 domain-joined hosts, with access reportedly available across seven servers.
The auction was initiated with a starting price of USD 1,500, a bid increment of USD 250, and a buyout (“Blitz”) option of USD 2,500. The seller indicated that the transaction would be conducted via an escrow service. If authentic, VPN and Local Admin access to a domain-joined environment could enable lateral movement, privilege escalation, data exfiltration, and potential ransomware deployment, posing significant operational and financial risk to the organization.

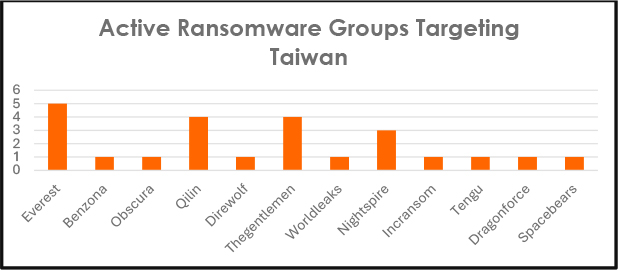
Ransomware activity targeting Taiwan shows a persistent but moderately fragmented threat landscape in recent periods (likely reflecting late 2025 to early 2026 data from leak sites and trackers). Everest leads with 5 confirmed incidents, indicating sustained focus and operational capability from this group against Taiwanese entities. A second tier of groups including Qilin (4), Direwolf (1), and TheGentlemen (4) demonstrate organized, repeated campaigns with notable volume.
Lower but consistent activity comes from Benzona (1), Obscura (1), Nightspire (1), Incransom (1), Tengu (1), Dragonforce (1), and Spacebears (1), alongside single or minimal hits from others like Gilin (possibly Qilin variant or typo) and Worldleaks. This distribution points to opportunistic targeting rather than exclusive dominance by one actor, with many groups leveraging affiliate models or rebranded tooling to hit regional victims.
The overall picture in Taiwan reflects broader global ransomware trends: heavy use of double-extortion (data theft + encryption), rapid attacker churn through rebranding, and focus on sectors offering quick leverage such as manufacturing, technology/IT services, logistics/transport, and SMBs where operational disruption or data exposure creates strong pressure for payment. While state-linked Chinese cyber operations (e.g., espionage/ransomware hybrids targeting critical infrastructure like energy and healthcare) have surged dramatically in 2025–2026 reports, the chart isolates criminal ransomware groups’ public claims/leaks against Taiwanese organizations.
The landscape remains dynamic and persistent, with Everest currently showing the strongest footprint in this dataset, but groups like Qilin (globally dominant in 2025–2026 with massive victim counts) and emerging players like Direwolf maintaining pressure through Asia-focused operations. Organizations in Taiwan should prioritize defenses against initial access vectors (phishing, exploited vulnerabilities, supply-chain compromises) and assume broad tooling reuse across these actors.
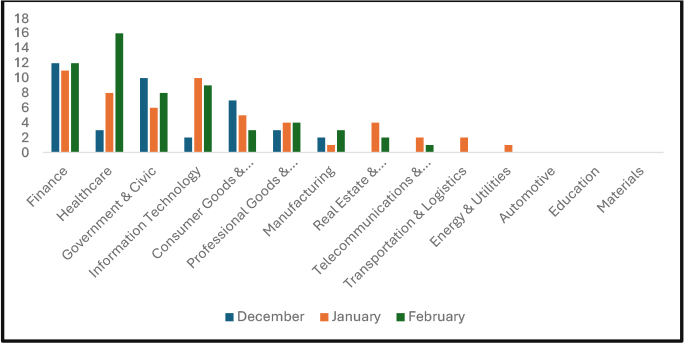
Cyber incidents in Taiwan during Dec 2025–Feb 2026 heavily targeted Finance (consistently high, ~12–14 incidents/month) and Healthcare (peaking at 16 in February, green bar tallest), reflecting criminal focus on high-value data for extortion or resale—aligning with ransomware trends like hospital data theft and finance breaches. Government & Civic and Information & Civic Technology follow strongly (both elevated in December blue bars, with Government dipping in January before rebounding), indicating persistent probing of public/administrative entities amid geopolitical tensions.
Consumer Goods & Technology and Professional Goods & Services show moderate but steady activity (February green spikes in some), while Manufacturing & Construction remains notable (consistent low-to-mid volume), matching global ransomware patterns where manufacturing often leads victim lists and Taiwan’s semiconductor/tech ecosystem draws both criminal and state actors. Lower-volume sectors include Real Estate, Telecommunications & Logistics, Energy & Utilities, Automotive, Education, and Materials with sporadic hits (e.g., January red in Energy/Transport), consistent with opportunistic criminal ops rather than the massive daily state-linked intrusions (2.63M+ attempts/day in 2025, surging into critical infrastructure like energy/hospitals per NSB reports).
Overall, the data highlights a criminal-driven landscape emphasizing data-rich sectors (finance, healthcare, tech) for monetization via breaches/leaks/ransomware, overlaid on relentless Chinese state-sponsored campaigns targeting energy, hospitals, telecom, and science parks for espionage/disruption. The February surge in healthcare incidents suggests increased data exfiltration or breach disclosures. Organizations should prioritize sector-specific defenses: encryption/resilient backups in finance/healthcare, vuln patching in manufacturing/tech, and monitoring for supply-chain/initial access in all areas.
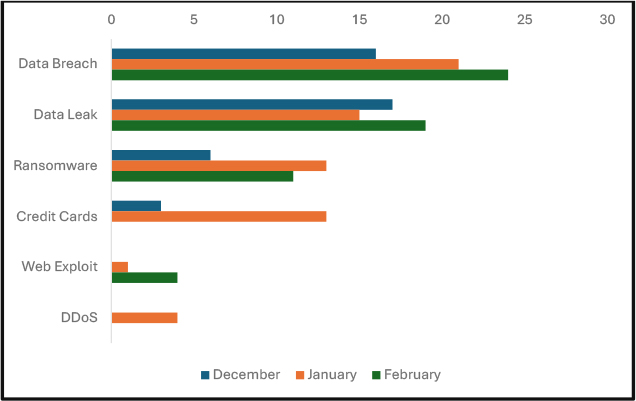
Data breaches and leaks overwhelmingly lead cyber incidents in Taiwan over Dec 2025–Feb 2026, peaking sharply in February—likely driven by successful exfiltration and dark-web publications from ransomware ops. Ransomware shows a clear January surge (highest volume), aligning with global holiday-season peaks and regional claims (e.g. Everest on ASUS in Dec, TheGentlemen and others in early 2026), before a modest February drop. Credit card theft spikes uniquely in January, probably from retail/logistics skimming or POS breaches post-holidays. Web exploits appear minimally (only February), and DDoS is isolated to January far below the massive ~2.63 million daily state-linked (Chinese) intrusion attempts reported across 2025 into 2026, which hit energy, hospitals, and infrastructure hardest.
This reflects a dual reality: high-volume criminal activity focused on data monetization/extortion (manufacturing, tech, SMBs, logistics) via double-extortion ransomware, plus relentless geopolitical probing. February’s data-event emphasis suggests increased leak-site activity or breach disclosures. Defenses should prioritize phishing resistance, vuln patching, segmented backups, and monitoring for initial access to break these chains early.
The listed vulnerabilities represent a mix of critical and high-severity flaws affecting widely deployed enterprise technologies, with several carrying a maximum CVSS score of 10.0. Many of these CVEs have been actively exploited, including APT34, APT44, NetTraveler, GhostSec, and Salth Typhoon, highlighting their operational value in targeted intrusion campaigns. Exploited products include remote access tools (ConnectWise ScreenConnect), network infrastructure (Cisco IOS XE, Citrix ADC), mobile device management platforms (Ivanti EPMM), collaboration software (Atlassian Confluence), and web servers (Apache HTTP Server). The presence of publicly available exploits increases the likelihood of both targeted and opportunistic attacks. Organizations using these products should prioritize patching, review exposure to the internet, and conduct threat hunting for indicators associated with the mentioned threat actors. Continuous monitoring and vulnerability management remain critical to mitigating risk from such actively exploited CVEs.
| Vulnerability | CVSS | Vendor | Product | Exploit Available? | Malware / Threat Actors / APTs Exploiting |
| CVE-2024-1709 | 10 | ConnectWise | ScreenConnect | Link | GhostSec |
| CVE-2024-36401 | 9.8 | GeoServer | GeoServer | Link | APT34, NetTraveler |
| CVE-2026-1281 | 9.8 | Ivanti | Endpoint Manager Mobile (EPMM) / MobileIron Core | Link | APT 44, Salth Typhoon |
| CVE-2023-20198 | 10 | Cisco | Cisco IOS XE | Link | APT 44, Salth Typhoon |
| CVE-2023-4966 | 7.5 | Citrix | Citrix ADC, Citrix Gateway | Link | Not publicly attributed |
| CVE-2021-42013 | 9.8 | Apache | Apache HTTP Server | Link | Not publicly attributed |
| CVE-2017-9841 | 9.8 | PHPUnit (Sebastian Bergmann) | PHPUnit | Link | Not publicly attributed |
| CVE-2023-22527 | 9.8 | Atlassian | Confluence | Link | APT34 |
Major national events in Taiwan present potential opportunities for cyber threat actors seeking visibility, disruption, espionage access, or influence operations. Large public gatherings, high media coverage, reliance on digital infrastructure, and international participation increase their attractiveness as targets.
Taiwan Lantern Festival 2026 (3–15 March 2026, Chiayi)
As one of Taiwan’s largest national celebrations, the Lantern Festival attracts millions of visitors and depends heavily on digital tourism platforms, large-scale LED displays, mobile applications, and live broadcasting infrastructure. The scale and symbolism of the event create exposure to website defacement campaigns targeting tourism portals, disruption attempts against live-streaming systems, and potential manipulation of digital signage. Public Wi-Fi networks and event-related mobile applications may also be leveraged for credential harvesting, malware distribution, or data interception. Additionally, the event’s national symbolism may attract disinformation activity intended to shape narratives or generate reputational impact.
Pingxi Sky Lantern Festival 2026 (3–6 March 2026, New Taipei City)
With significant global media attention and concentrated tourist activity, the Pingxi event presents risk primarily in the information domain. Social media manipulation, impersonation accounts, and phishing campaigns targeting travelers and hospitality services are plausible threat vectors. Tourism websites and ticketing platforms may face disruption or defacement attempts designed to cause operational inconvenience or reputational damage.
Tour de Taiwan 2026 (15–19 March 2026)
This international cycling event spans multiple cities and relies on digital timing systems, logistics platforms, and live sports broadcasting infrastructure. Potential cyber risks include interference with race management systems, data breaches involving athlete or sponsor information, and attempts to disrupt live transmissions. Given international participation, the event also presents an opportunity for credential harvesting or targeting of foreign entities.
Taipei Game Show 2026 (16 February 2026, Taipei Nangang Exhibition Center)
As one of Asia’s largest gaming conventions, this event draws global developers publishers, and technology vendors. The concentration of software demonstrations and third-party vendors increases exposure to malware distribution via compromised demos or infected removable media. Supply-chain intrusion attempts targeting gaming companies and credential harvesting campaigns directed at developers and exhibitors represent additional risks, particularly given the sector’s intellectual property value.
Taipei International Cycle Show 2026 (25 March 2026)
This major global trade exhibition for the bicycle industry brings together manufacturers, exporters, and international supply-chain partners. The event presents heightened risk of industrial espionage targeting proprietary manufacturing processes and product designs. Business email compromise (BEC) schemes, fraudulent invoicing, and supply-chain compromise attempts may also increase due to concentrated commercial engagement.
Taiwan National Day (Double Ten Day) – 10 October 2026
As a politically significant event featuring official speeches, military displays, and national symbolism, National Day represents a high-probability target for hacktivist campaigns and state-linked information operations. Risks include distributed denial-of-service (DDoS) attacks against government portals, website defacement, coordinated propaganda dissemination, and narrative manipulation across social media platforms.
Taiwan Pride Parade (Late October 2026)
As the largest LGBTQ+ pride event in East Asia, the parade attracts substantial international attention. The event may face ideological hacktivism, website disruption attempts targeting organizers, and coordinated online harassment or disinformation campaigns aimed at amplifying social division or reputational harm.
Taipei New Year’s Eve Celebration (31 December 2026)
The large-scale celebration near Taipei 101 relies heavily on broadcast systems, digital billboards, tourism platforms, and municipal services. Cyber risks include attempts to disrupt live broadcasting infrastructure, DDoS attacks against city services and tourism portals, and potential manipulation of digital displays. The global visibility of the event increases its attractiveness for both symbolic disruption and opportunistic cyber activity.
Collectively, these events represent periods of heightened cyber risk due to increased digital dependency, international exposure, and symbolic value. Proactive monitoring, temporary security reinforcement, and coordinated public–private response planning during these timeframes are recommended to mitigate potential disruption and reputational impact.
Taiwan’s cyber threat environment in 2025–early 2026 remains defined by sustained state-sponsored pressure alongside active criminal ransomware activity. PRC-linked APT groups continue to conduct large-scale espionage, infrastructure reconnaissance, and long-term access operations, while financially motivated actors exploit data-rich sectors for rapid monetization through double-extortion and data leaks.
Driven by geopolitical competition, semiconductor dominance, and evolving hybrid warfare tactics, Taiwan functions as a frontline digital battleground. The resulting risk landscape combines immediate operational and financial disruption with longer-term strategic and national security implications, requiring sustained vigilance and resilience.
Harden Initial Access Vectors
Deploy phishing-resistant MFA, strengthen email and web security controls, maintain rigorous patch management (especially for edge devices and VPNs), and implement robust EDR to reduce credential theft and exploitation risks.
Strengthen Sector-Specific Defenses
Finance and healthcare sectors should prioritize encrypted, segmented, and regularly tested backups to counter double-extortion. Semiconductor and technology firms must reinforce IP protection and supply-chain risk controls. Critical infrastructure operators should enhance OT/IT segmentation, continuous monitoring, and adopt zero-trust principles to limit persistent access.
Adopt Intelligence-Led and Proactive Monitoring
Integrate external threat intelligence to identify emerging vulnerabilities, leaked credentials, and underground access sales. Conduct regular credential hygiene reviews and monitor for reconnaissance activity targeting exposed services.
Build Operational Resilience
Maintain offline backups, test incident response and ransomware recovery plans, conduct regular tabletop exercises, and assume breach scenarios to improve detection and rapid containment. Strengthen information-sharing partnerships with regional allies to enhance early warning and coordinated defense.