


Singapore’s cyber threat landscape is increasingly shaped by the intersection of state-sponsored cyber espionage, financially motivated cybercrime, and organized ransomware operations, reflecting the country’s strategic importance as a regional financial, technological, and communications hub. Advanced persistent threat (APT) groups linked to nation states, including UNC3886, Mustang Panda, Volt Typhoon, APT41, and Lazarus Group, continue to conduct targeted campaigns against critical infrastructure, telecommunications networks, financial institutions, semiconductor manufacturers, and government-linked organizations. These actors employ sophisticated tactics, including exploitation of zero-day vulnerabilities, compromise of network edge devices, spear-phishing operations, credential harvesting, and stealthy persistence techniques, such as living-off-the-land activity and modular malware frameworks. Their objectives range from long-term intelligence collection and strategic network positioning to intellectual property theft and financial gains.
At the same time, Singapore faces a vibrant underground cybercriminal ecosystem reflected in sustained dark web activity, involving data breach listings, identity datasets, financial credential markets, and ransomware leak disclosures. Telecommunications, healthcare, IT services, and financial platforms appear frequently in underground discussions due to the large volumes of personal and transactional data they manage. Several listings advertising Singapore-linked databases containing identity details, financial account information, and healthcare records highlight the growing risk of identity theft, fraud, and social engineering campaigns targeting citizens and businesses. Ransomware groups, including prominent Ransomware-as-a-Service (RaaS) operators and smaller opportunistic actors, continue to target service-oriented sectors, such as professional services, information technology providers, and finance organizations, often leveraging double-extortion tactics involving both data encryption and public data exposure. Combined with ongoing exploitation of high-severity vulnerabilities in internet-facing enterprise systems, increasing use of social engineering techniques such as spear-phishing and credential harvesting observed in campaigns attributed to Mustang Panda, and growing risks associated with supply-chain compromise targeting technology vendors and managed service providers as seen in operations linked to APT41, these trends underscore a persistent and multi-dimensional threat environment affecting both national infrastructure and commercial enterprises.
Overview
Singapore’s cyber threat landscape is increasingly shaped by sophisticated state-sponsored advanced persistent threat (APT) actors seeking strategic intelligence, operational access, and economic advantage. These actors primarily originate from China and North Korea and conduct long-term cyber espionage campaigns targeting sectors that are critical to Singapore’s role as a regional technology, financial, and diplomatic hub. Telecommunications infrastructure, government institutions, financial systems, and high-technology industries such as semiconductors and electronics manufacturing remain particularly attractive targets due to the strategic intelligence and operational leverage they provide.
Recent threat intelligence indicates that multiple APT groups operate concurrently within the region, each employing distinct operational models and objectives. China-aligned actors such as UNC3886, Mustang Panda, Volt Typhoon, and APT41 focus primarily on strategic espionage, infrastructure access, and intellectual property acquisition, often leveraging zero-day vulnerabilities, spear-phishing campaigns, and living-off-the-land techniques to infiltrate and persist within high-value networks. In parallel, North Korea–linked actors such as Lazarus Group combine financially motivated cyber operations with intelligence collection, targeting financial institutions and digital asset platforms to generate revenue and circumvent international sanctions. Singapore’s position as a global connectivity hub, financial center, and diplomatic gateway to Southeast Asia further increases its exposure to cyber operations targeting regional coordination platforms, telecommunications networks, and multinational corporate environments. The presence of additional unnamed China-nexus actors targeting ASEAN-related networks highlights the broader strategic interest in monitoring regional political cooperation and policy development.
Collectively, these threat actors demonstrate advanced capabilities in covert access, persistence, and data exfiltration, often prioritizing long-term intelligence collection over immediate disruption. Their evolving tactics, including exploitation of infrastructure vulnerabilities, credential harvesting, stealthy backdoors, and encrypted command-and-control communications, underscore the need for continuous monitoring, proactive threat intelligence integration, and robust defensive measures across both public and private sector networks.
UNC3886 & its affiliates
UNC3886 is a China-nexus advanced persistent threat (APT) actor known for highly sophisticated cyber espionage activity targeting critical infrastructure, telecommunications, defense, and technology sectors globally. First identified by threat researchers in 2023, the group has been attributed with targeted campaigns involving the exploitation of zero-day vulnerabilities and deployment of custom tooling to gain covert access to high-value environments. Singapore’s authorities have publicly acknowledged UNC3886’s deliberate, targeted intrusions against national telecommunications infrastructure, underscoring its strategic interest in network and edge system access.
Recent Developments
Singapore’s Cyber Security Agency (CSA) and partner agencies conducted a coordinated response, Operation CYBER GUARDIAN, after detecting UNC3886 activity against all four major telcos in a deliberate espionage campaign. While the threat actor gained limited access to network segments and exfiltrated a small amount of technical (non-personal) data, there is no evidence of consumer data theft or service outages to date. Remediation efforts have focused on closing access points and enhancing monitoring to contain the intrusion.
Evolving Tactics
A distinguishing characteristic of UNC3886’s operations is its use of zero-day exploits in widely deployed infrastructure components, including perimeter firewalls, virtualization platforms, and network appliance firmware. The group has exploited vulnerabilities in Fortinet, VMware, Juniper, and similar technologies to gain initial access and bypass conventional defenses. Once inside, it employs living-off-the-land tactics, sophisticated credential harvesting, backdoor implantation, and anti-forensic techniques such as log manipulation and rootkit hiding to maintain a long-term presence with minimal detection footprint.
Malware Features and Functions
UNC3886 deploys specialized malware and customized backdoors designed to operate within network infrastructure and virtualization environments. The group has demonstrated the ability to implant persistent access mechanisms within compromised devices, including firmware-level modifications and stealthy backdoor modules capable of surviving system reboots. These tools enable remote command execution, credential harvesting, and covert data exfiltration through encrypted command-and-control channels, allowing the actor to maintain prolonged access to targeted telecommunications and network management systems while minimizing detection.
Conclusion
UNC3886 represents a high-capability, espionage-oriented threat actor with a demonstrated focus on critical infrastructure environments, particularly telecommunications and network virtualization platforms. Its advanced malware tooling, exploitation of zero-day vulnerabilities, and persistence mechanisms underscore its potential for stealthy, long-term access and intelligence collection. Singapore’s coordinated national response highlights both the severity of the threat and the importance of collaborative defense across government and private sectors. Continuous monitoring, patch management, and anomaly-based detection remain essential to mitigating this evolving actor’s operational advantages.
Overview
Mustang Panda is a China-aligned espionage actor known for long-term intelligence operations in Southeast Asia, with a primary focus on government agencies, policy think tanks, and organizations involved in regional diplomacy and security. In the Singapore context, the group’s activity likely targets political intelligence, ASEAN-related coordination, maritime security monitoring, and regional strategic planning. Its operations are characterized by careful selection of high-value targets, emphasizing stealth, persistence, and minimal detection while gathering sensitive information.
Recent Developments
Mustang Panda has maintained operational presence in Southeast Asia through sustained spear-phishing campaigns and intrusion attempts, particularly aimed at email accounts, administrative portals, and government networks. Singapore-based entities are considered high-value targets due to the city-state’s pivotal diplomatic, trade, and security roles. Observed campaigns include credential harvesting and targeted intrusion attempts leveraging regional geopolitical narratives, indicating strategic collection rather than opportunistic attacks. Security monitoring across Southeast Asia has also indicated spear-phishing campaigns targeting government-linked organizations, diplomatic missions, and policy research institutions associated with regional cooperation initiatives. Given Singapore’s central role in ASEAN diplomatic coordination and regional policy dialogue, such campaigns likely include attempts to compromise email systems and administrative portals belonging to Singapore-based entities involved in intergovernmental communication and strategic policy discussions.
Malware Features and Functions
The actor relies on custom malware frameworks designed for persistence and covert exfiltration. Techniques include DLL sideloading to bypass standard execution restrictions, tailored backdoors to maintain access, and encrypted communication channels for command-and-control activity. Mustang Panda’s tooling enables remote monitoring, data exfiltration, and lateral movement while minimizing forensic traces, allowing long-term intelligence gathering without immediate disruption to operational networks.
Evolving Tactics
Mustang Panda frequently combines social engineering with technical exploitation to achieve initial access. Spear-phishing emails remain the primary entry vector, often accompanied by highly contextualized content referencing diplomatic or regional security topics. Once inside, the group leverages living-off-the-land techniques, persistent backdoors, and stealthy privilege escalation methods. Campaigns demonstrate adaptability in circumventing endpoint detection and network monitoring, reflecting ongoing refinement of their TTPs (tactics, techniques, and procedures) to maintain long-term presence.
Conclusion
Mustang Panda represents a persistent, politically motivated threat to Singapore’s strategic institutions, particularly in government, policy, and regional security sectors. Its combination of targeted social engineering, custom malware deployment, and stealthy operational tradecraft underscores the importance of multi-layered defense strategies, including user awareness programs, advanced email security, anomaly-based network monitoring, and proactive threat intelligence integration to mitigate espionage risks.
Overview
Volt Typhoon is a China-linked cyber threat actor associated with strategic cyber operations targeting communications infrastructure and critical information systems. Active since at least 2021, the group has been linked to campaigns focused on gaining persistent access to telecommunications networks and related infrastructure across the Asia-Pacific region. Singapore’s role as a global connectivity hub and a key junction for undersea cable networks linking Asia to North America makes its telecommunications infrastructure a particularly attractive target for this actor. Unlike many traditional espionage-focused APT groups, Volt Typhoon operations are assessed to include pre-positioning activities designed to enable potential disruption or sabotage of communications infrastructure during geopolitical crises.
Recent Developments
Investigations into regional cyber activity revealed that infrastructure belonging to Singtel experienced intrusion activity associated with Volt Typhoon in 2024. The compromise reportedly involved the exploitation of vulnerabilities affecting enterprise networking platforms used for network orchestration. Following the intrusion, attackers deployed web-shell–based access mechanisms that enabled credential harvesting and lateral reconnaissance within targeted systems. Intelligence assessments indicate that access obtained during the operation may have been leveraged to support follow-on intrusions targeting organizations in other countries, suggesting Singapore’s telecommunications infrastructure was used as an operational stepping stone in broader campaigns.
Evolving Tactics
A defining characteristic of Volt Typhoon’s operational tradecraft is its extensive reliance on living-off-the-land techniques, which involve the use of legitimate system administration tools already present within compromised environments. By leveraging utilities such as command-line administration frameworks, network management utilities, and scripting environments, the actor can blend malicious activity into normal system operations and significantly reduce the likelihood of detection by conventional endpoint security tools. This approach, combined with the exploitation of vulnerabilities in network edge devices and software-defined networking infrastructure, enables the actor to maintain persistent access while avoiding the deployment of highly visible malware.
Conclusion
Volt Typhoon represents a strategic threat to Singapore’s communications infrastructure due to its focus on long-term network access and potential disruption capabilities. The group’s reliance on stealthy operational methods and legitimate system utilities underscores the need for enhanced behavioral monitoring, rigorous vulnerability management for network infrastructure platforms, and strengthened defensive visibility across telecommunications environments.
Overview
APT41 is a China-linked cyber threat group recognized for conducting dual-purpose campaigns that blend state-aligned espionage with financially motivated intrusions. Historically active across Asia, the group targets sectors rich in intellectual property, critical technology, and strategic operational data. In Singapore, APT41’s focus aligns with semiconductor manufacturing, electronics production, and regional corporate headquarters, reflecting interest in both commercial technology and supply-chain intelligence. Their operations underscore a persistent effort to combine economic and strategic objectives within a single threat framework.
Recent Developments
The group has leveraged multiple campaigns exploiting unpatched internet-facing applications in enterprise environments, often targeting regional technology hubs and multinational offices in Singapore. Observed activity includes compromise of corporate networks, lateral movement to high-value systems, and exfiltration of sensitive intellectual property. APT41’s targeting of subsidiaries, managed service providers, and supply-chain partners highlights the city-state’s exposure through interdependent business ecosystems, emphasizing risk to both operational continuity and proprietary technologies. Singapore’s position as a regional hub for semiconductor manufacturing, advanced electronics production, and multinational corporate headquarters increases exposure to APT41 operations focused on intellectual property acquisition and supply-chain intelligence. Intrusion activity in the region has demonstrated the group’s interest in corporate research environments, production management systems, and partner networks that support high-value technology development.
Malware Features and Functions
APT41 utilizes a diverse malware arsenal tailored to both espionage and financially motivated objectives. Tooling includes credential harvesters, remote access trojans (RATs), and privilege escalation modules capable of maintaining persistence in enterprise networks. Malware often features stealthy communication channels, encrypted exfiltration pipelines, and modular design to facilitate targeted attacks on specific applications or data repositories. Their toolkit supports both direct data theft and operational disruption when needed, allowing the group to achieve multiple objectives within the same intrusion.
Evolving Tactics
APT41 combines the exploitation of known vulnerabilities with sophisticated social engineering. The group frequently targets unpatched enterprise software, uses phishing campaigns to acquire credentials, and leverages lateral movement for access to sensitive systems. Tactics demonstrate adaptability, with tailored intrusion patterns depending on the industry, regional regulatory environment, and asset value. Their dual-purpose approach blurs lines between espionage and profit-driven intrusions, reflecting a hybrid operational model that is increasingly relevant to Singapore’s technology and manufacturing sectors.
Conclusion
APT41 poses a sustained and multifaceted threat to Singapore, particularly in semiconductor, electronics, and high-value corporate environments. The group’s combined espionage and financially motivated operations emphasize the need for robust vulnerability management, rigorous credential hygiene, proactive supply-chain security assessments, and continuous monitoring of network activity. Understanding APT41’s dual-purpose targeting framework is critical for mitigating both intellectual property theft and financial compromise risks.
Overview
Lazarus Group is a North Korea–linked threat actor recognized for combining strategic espionage with financially motivated cyber operations. The group’s campaigns historically target financial institutions, cryptocurrency platforms, and critical infrastructure, aiming to generate revenue while supporting state-aligned objectives such as sanctions evasion. In Singapore, Lazarus activity aligns with the city-state’s fintech ecosystem, digital asset exchanges, and international banking hubs, making these sectors particularly susceptible to credential compromise, transactional manipulation, and malware-facilitated theft.
Recent Developments
Lazarus has maintained persistent operations against financial entities in Southeast Asia, leveraging highly targeted campaigns against cryptocurrency exchanges and banking platforms. Observed activity includes compromise of remote access mechanisms, exploitation of application vulnerabilities, and multi-stage attacks designed to extract digital assets. While Singapore has not reported large-scale financial losses publicly, the actor’s presence signals ongoing reconnaissance and potential operational readiness to conduct theft or disruptive campaigns against high-value financial targets. Singapore’s growing fintech ecosystem and the presence of regional cryptocurrency exchanges also present attractive targets for Lazarus operations. Threat intelligence reporting indicates that the group has conducted reconnaissance and intrusion attempts against digital asset platforms and financial service providers operating in Southeast Asia, reflecting an ongoing effort to exploit financial infrastructure for revenue generation and sanctions evasion.
Malware Features and Functions
The group’s tooling includes custom backdoors, credential harvesters, and document-based malware designed for covert deployment. Attack vectors often leverage weaponized document lures embedded with macro-enabled scripts, enabling remote execution and persistent access. Malware frameworks such as VSingle and MATA have been historically linked to Lazarus, supporting lateral movement, data exfiltration, and encrypted command-and-control communications. Their malware capabilities are optimized to evade detection while maintaining operational flexibility for both espionage and revenue-generating activities.
Evolving Tactics
Lazarus blends traditional spear-phishing and document-based intrusion techniques with targeted exploitation of unpatched enterprise applications. Operational sophistication includes multi-layered obfuscation, living-off-the-land tactics, and rapid adaptation to emerging security controls. Campaigns often focus on financial workflows, digital asset management systems, and cross-border payment platforms, reflecting the dual-purpose objective of asset exfiltration and intelligence collection.
Conclusion
Lazarus Group represents a high-impact threat to Singapore’s financial and digital asset sectors, combining espionage with revenue-driven operations. The actor’s sophisticated malware toolkit, targeted intrusion methods, and focus on digital asset ecosystems emphasize the need for robust endpoint security, continuous monitoring of financial transactions, supply-chain risk assessment, and employee awareness programs. Proactive threat intelligence integration is essential to detect, mitigate, and respond to Lazarus operations before asset loss or operational disruption occurs.
Overview
Cyber threat intelligence reporting has also identified activity attributed to an additional China-nexus advanced persistent threat actor targeting regional organizations affiliated with ASEAN governmental cooperation frameworks. Although this actor has not been publicly named, security researchers have observed network traffic and intrusion indicators linking this group to compromise attempts involving government-related entities across Southeast Asia.
Regional Targeting Patterns
Observed activity indicates the actor has targeted organizations associated with government operations and regional diplomatic coordination in multiple ASEAN member states, including Singapore, Cambodia, and Laos. The targeting pattern suggests a strategic objective focused on regional political intelligence collection and monitoring of intergovernmental cooperation activities. Compromised systems within an ASEAN-affiliated organization were observed communicating with infrastructure linked to malicious command-and-control servers associated with this threat cluster, indicating that the actor had successfully established persistence within the network environment.
Operational Characteristics
Although publicly available information on this threat actor remains limited, the activity demonstrates characteristics consistent with state-aligned cyber espionage campaigns observed elsewhere in the region. These include selective targeting of politically significant institutions, use of external command-and-control infrastructure to manage compromised systems, and a focus on maintaining discreet, long-term access to sensitive networks rather than conducting disruptive attacks. Such activity highlights the broader strategic interest of state-aligned actors in monitoring regional diplomatic and policy developments.
Conclusion
The presence of an additional unnamed China-linked APT targeting ASEAN-related networks underscores the complexity of Singapore’s cyber threat landscape. As a central node in regional diplomacy and economic coordination, Singapore is likely to remain a focal point for cyber espionage operations aimed at gathering intelligence on political developments, security cooperation, and regional policy initiatives. Strengthening monitoring capabilities, improving cross-border information sharing, and integrating threat intelligence from regional partners will remain critical to detecting and mitigating such activity.
Dark web monitoring indicates a sustained, financially driven threat ecosystem targeting Singapore, characterized by high volumes of breached data circulation, identity-centric datasets, financial credential demand, and sector-specific compromise claims. Data breach and leak listings dominate overall chatter, accompanied by a marked rise in credit card–related activity and fluctuating ransomware disclosures, underscoring a monetization-focused underground economy. Sectoral discussions show concentration on Telecommunications & Media and Healthcare, alongside consistent targeting of IT, financial services, and professional service providers, industries aggregating large volumes of personal and transactional data. Notably, multiple high-impact listings involving citizen NRIC-linked datasets, healthcare records, financial trading platforms, e-commerce customer bases, and administrative system access suggest both opportunistic exploitation and deliberate acquisition of high-integrity identity data. Collectively, the observed activity reflects a mature threat marketplace prioritizing data resale, fraud enablement, account takeover, and long-term identity exploitation, reinforcing Singapore’s position as a high-value digital and financial target within the regional cybercriminal ecosystem.
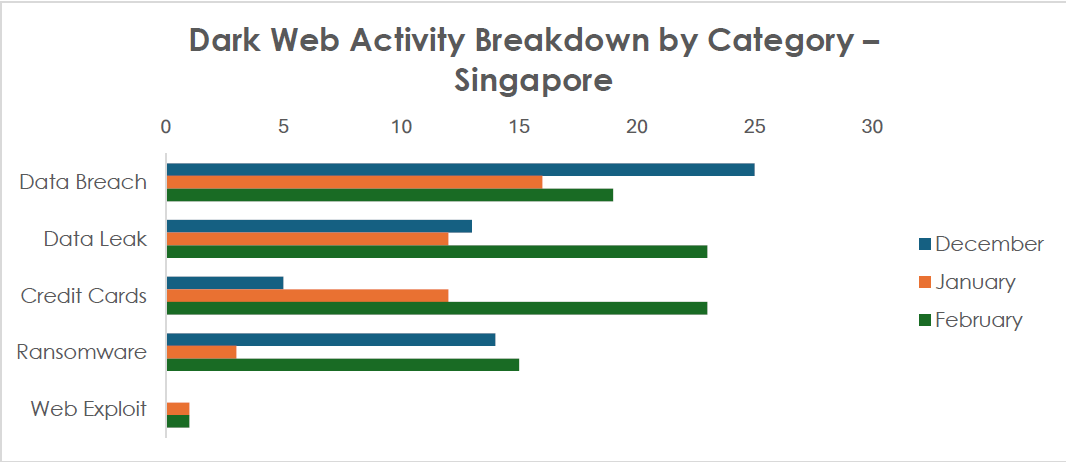
Dark web monitoring related to Singapore indicates sustained and diversified threat actor interest across multiple illicit categories. Data Breach listings accounted for the highest volume of chatter (25 in December / 16 in January / 19 in February; total 60), reflecting continued circulation and monetization of compromised databases. Data Leak posts followed closely (13, 12, 23; total 48), with a notable spike in February suggesting increased public release activity or delayed disclosure of previously compromised datasets. Credit card–related listings showed a sharp upward trend (5, 12, 23; total 40), signaling a growing focus on financial fraud and carding operations targeting Singapore-linked payment data. Ransomware-related mentions fluctuated (14, 3, 15; total 32), indicating episodic leak-site disclosures rather than a steady publication cadence. Web exploit discussions remained comparatively low (0, 1, 1; total 2), suggesting exploitation activity is occurring but not heavily advertised in open forums. Overall, the chatter profile reflects a financially motivated ecosystem centered on data monetization, payment fraud, and extortion, with increasing emphasis on directly exploitable financial datasets.
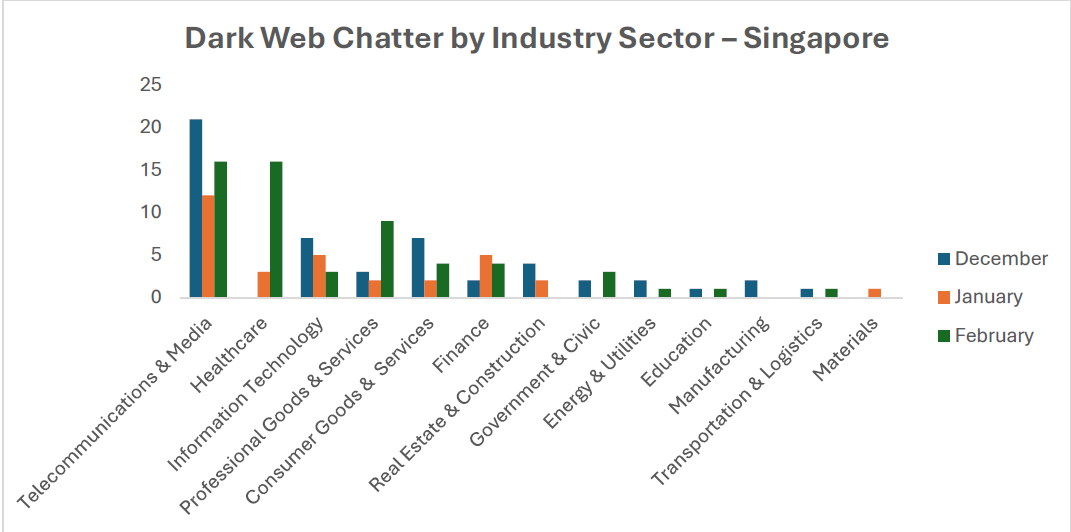
Dark web chatter associated with Singapore demonstrates clear sectoral concentration, with Telecommunications & Media (49 mentions) emerging as the most discussed industry, reflecting persistent interest in subscriber data, communication infrastructure access, and large-scale personal datasets. Healthcare (19) shows a significant February spike, indicating increased circulation or monetization of medical-related data, which carries high black-market value due to identity and insurance fraud potential. Information Technology (15) and Professional Goods & Services (14) remain consistently referenced, reinforcing the attractiveness of data-rich service providers and potential supply-chain pivot points. Financial sector mentions (11) indicate a steady targeting of interest aligned with fraud and account compromise objectives. Lower but notable activity across Consumer Goods, Government & Civic, Energy, and Logistics sectors suggests broad opportunistic scanning rather than isolated targeting. Overall, the distribution reflects a data-centric threat economy prioritizing sectors that aggregate large volumes of personal, financial, or infrastructure-linked information, with telecommunications and healthcare showing the strongest recent momentum in underground discussions.
Note: The authenticity of the breaches below remains unverified at the time of reporting, as the claims originate solely from the threat actors.
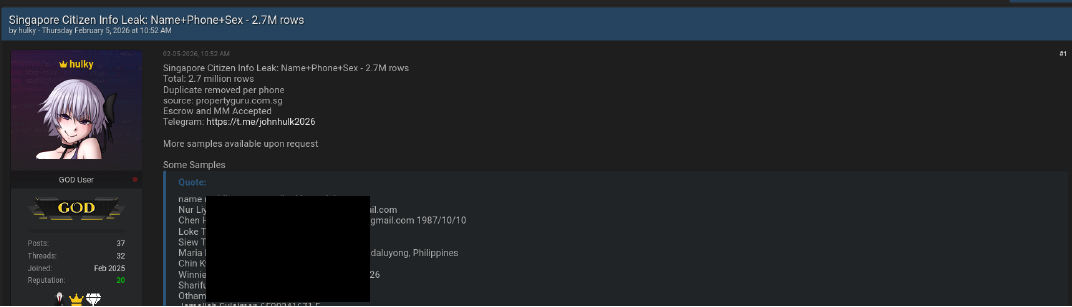
A dark web forum user operating under the handle “hulky” is advertising an alleged database titled “Singapore Citizen Info Leak – 2.7M rows,” claiming it contains names, mobile numbers, and gender details, with sample entries showing emails, dates of birth, and location data; the actor is offering escrow-supported transactions to enhance credibility and facilitate sale. If legitimate, this dataset would significantly heighten the threat environment in Singapore by enabling targeted smishing, phishing, SIM-swap fraud, and identity-driven social engineering, primarily impacting citizens, financial institutions, telecom operators, and government-linked digital services reliant on mobile-based authentication.
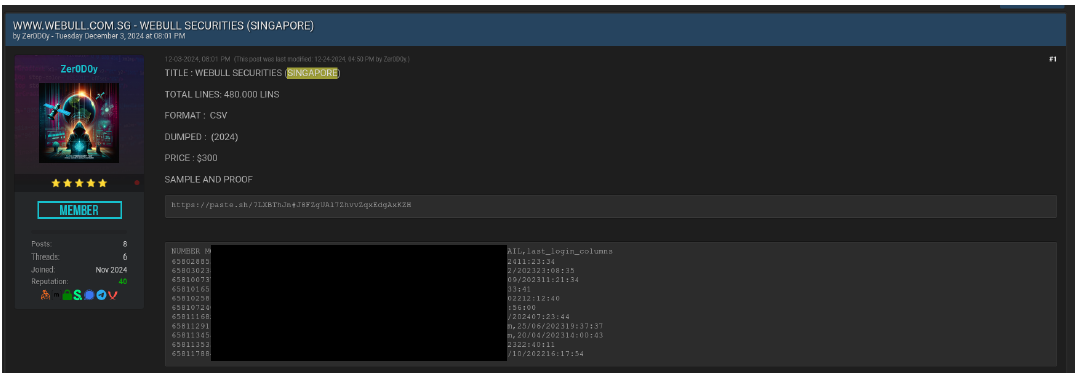
A dark web forum member operating under the alias “Zer0D0y” is advertising an alleged 480,000-line CSV dataset purportedly linked to Webull Securities (Singapore), with fields including mobile numbers, first and last names, gender, date of birth, email addresses, and last login timestamps; the actor claims the data was dumped in 2024 and is offering it for sale at USD 300, with a public sample provided to demonstrate authenticity. If legitimate, this exposure presents elevated risks of targeted financial phishing, account takeover attempts, credential stuffing, and identity fraud against retail investors, while also increasing the likelihood of impersonation scams leveraging trading activity pretexts; the primary impact would be on Webull clients, high-frequency traders, and associated financial service providers operating in Singapore.
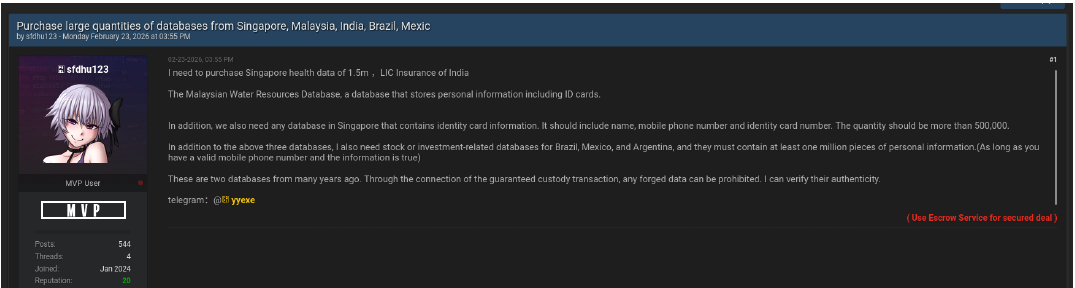
A dark web user operating under the handle “sfdhu123” is actively soliciting bulk acquisition of high-volume personal data sets, with specific emphasis on Singapore health data (1.5 million records) and any Singapore database containing national identity card numbers, names, and mobile numbers exceeding 500,000 records; the actor also references escrow-based “guaranteed custody” transactions and claims the ability to validate authenticity, indicating operational maturity and intent to procure verified, high-integrity data. The explicit targeting of identity card-linked datasets in Singapore signals elevated risk of identity theft, synthetic identity fraud, financial account takeover, and long-term impersonation schemes, particularly affecting healthcare institutions, government-linked databases, financial services, and citizens whose NRIC-linked credentials could be weaponized for high-confidence social engineering and regulatory bypass attempts.
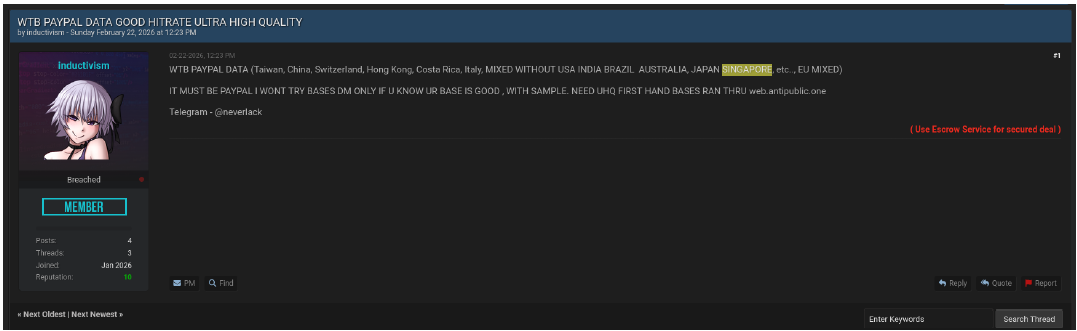
A dark web forum user operating under the alias “inductivism” is soliciting the purchase of “ultra-high quality” PayPal datasets across multiple jurisdictions, explicitly requesting verified, first-hand credential bases with samples and validation through breach-checking platforms; although the post excludes certain countries, the reference to mixed regional datasets and transactional verification mechanisms indicates ongoing demand for high-fidelity financial account credentials that may include spillover exposure affecting users in Singapore. This activity reflects sustained market appetite for credential stuffing and account takeover operations targeting PayPal accounts, posing indirect risk to Singapore-based individuals and businesses through reused credentials, cross-platform compromise, and downstream financial fraud.
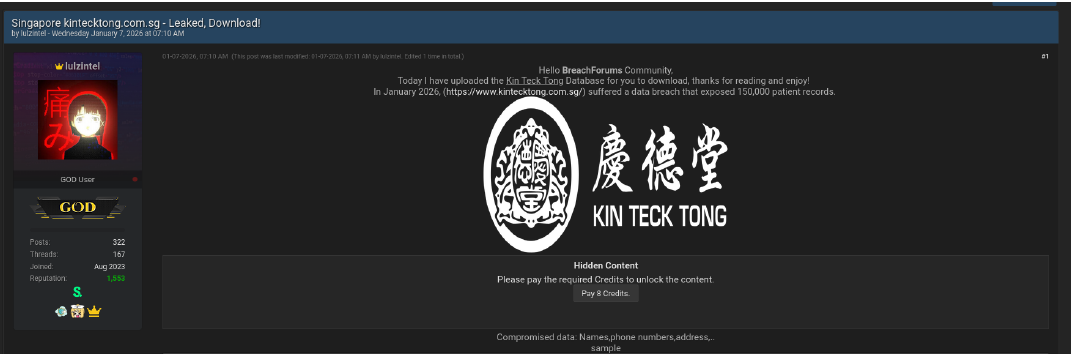
A dark web actor using the alias “lulzintel” has published an alleged database breach involving Kin Teck Tong, claiming exposure of approximately 150,000 patient records as of January 2026 and distributing the dataset via a gated forum download model. The posted SQL samples indicate highly sensitive structured data, including full names (English and Chinese), NRIC numbers, mobile numbers, dates of birth, residential addresses, invoice records, payment methods, partial medical history, allergy information, membership identifiers, and transaction metadata. If authentic, this constitutes a high-severity healthcare data breach within Singapore, significantly elevating risks of identity theft, medical fraud, insurance abuse, impersonation, and long-term social engineering, particularly impacting patients, elderly individuals, and those with chronic treatment histories whose combined identity and health data materially increase exploitation value.
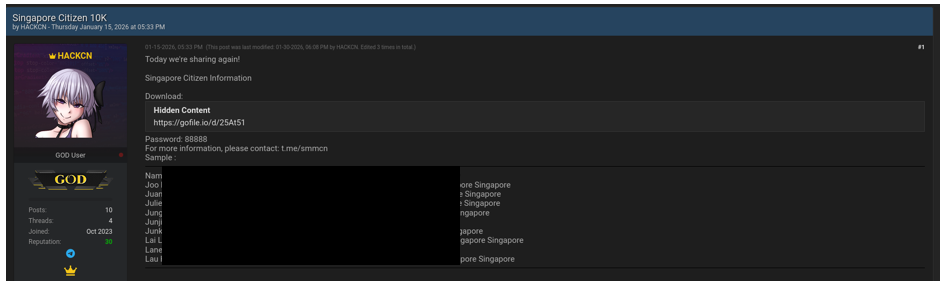
A dark web user operating under the alias “HACKCN” has publicly released a dataset titled “Singapore Citizen 10K,” providing a direct download link and password access, with sample records containing full names, gender, date of birth, email addresses, mobile numbers, NRIC numbers, nationality, and country of residence. Unlike sale-based listings, this appears to be an open distribution post, which increases the likelihood of rapid downstream propagation across multiple forums and threat actor ecosystems. This exposure materially heightens identity theft, impersonation, SIM-swap, and financial fraud risks within Singapore, particularly affecting individuals whose NRIC and mobile numbers can be weaponized for high-confidence social engineering against banks, telecom providers, and government digital services.
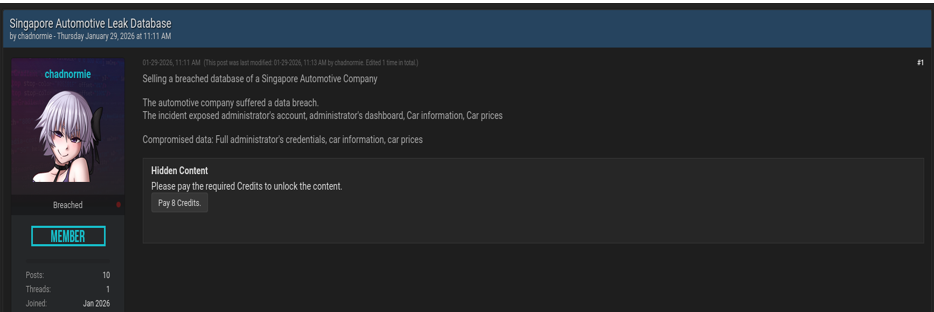
A dark web user under the alias “chadnormie” is advertising the sale of a breached database allegedly belonging to a Singapore-based automotive company, claiming exposure of full administrator credentials, access to the administrator dashboard, and associated vehicle information, including pricing data. The nature of the compromised assets suggests backend system compromise rather than a simple customer data leak, indicating potential privilege escalation and persistent access risks. If authentic, this incident could enable website defacement, price manipulation, fraudulent vehicle listings, business email compromise, and lateral movement into connected systems, posing operational and reputational risks to automotive dealerships and related service providers within Singapore, as well as downstream financial fraud risks affecting customers interacting with the platform.
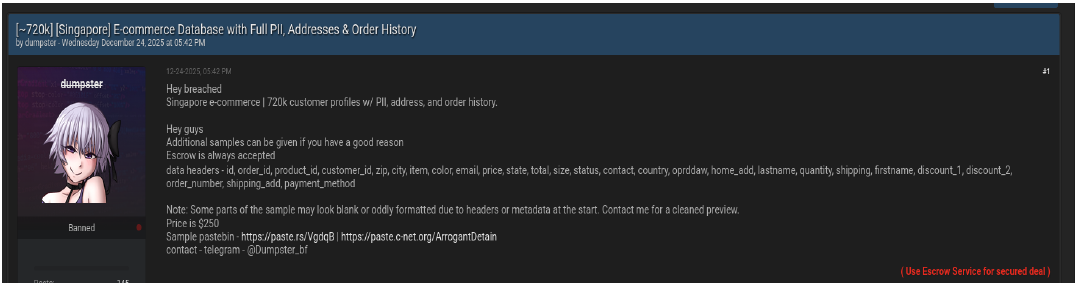
A dark web actor using the alias “dumpster” is advertising a purported 720,000-record Singapore e-commerce customer database, claiming exposure of full personally identifiable information (PII), residential and shipping addresses, contact numbers, email addresses, order history, product details, pricing, discounts, and payment method fields; the seller is offering escrow-backed transactions and additional samples to validate authenticity. The structured headers suggest direct database extraction rather than scraped data, indicating potential compromise of backend order management or CRM systems. If authentic, this breach significantly elevates risks within Singapore of targeted phishing, parcel delivery scams, refund fraud, account takeover, and business email compromise, particularly affecting frequent online shoppers, logistics providers, payment processors, and e-commerce platforms reliant on stored customer transaction histories.
The December 2025 – February 2026 assessment indicates a stable but persistent ransomware threat environment in Singapore, characterized by consistent monthly incident volumes and concentrated actor activity. While overall case numbers remained steady, the landscape was led by Qilin as the most active operator, with additional contributions from LockBit5, Everest, Safepay, and several lower-frequency groups, reflecting a mix of structured RaaS-driven campaigns and opportunistic intrusions. Targeting patterns demonstrate a clear preference for data-intensive and service-oriented sectors, particularly Professional Goods & Services and Information Technology, alongside continued pressure on Finance, Government-linked entities, and infrastructure-adjacent industries. Collectively, these indicators point to financially motivated actors maintaining sustained interest in Singapore’s high-value economic sectors, leveraging double-extortion models and sectoral interconnectedness to maximize impact and monetization potential.
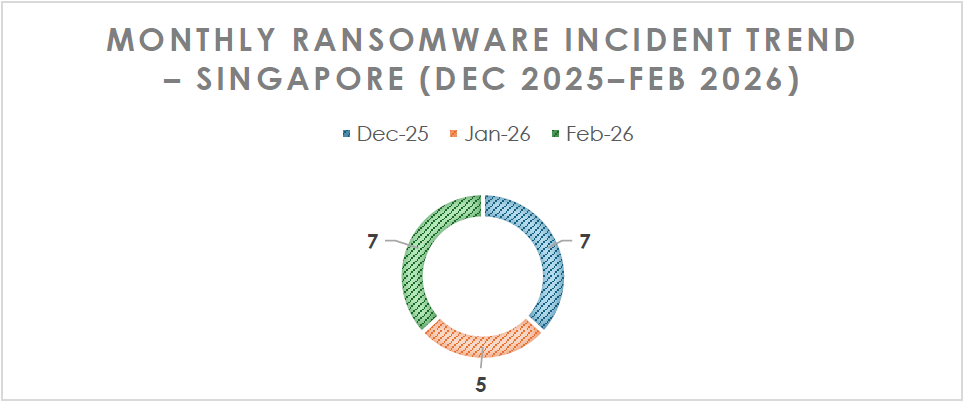
Between December 2025 and February 2026, ransomware activity targeting Singapore remained relatively consistent, with 7 incidents in December, a slight dip to 5 in January, and a rebound to 7 in February. The temporary reduction in January may reflect operational pauses, post-holiday disruption cycles, or delayed leak-site postings rather than a true decline in compromise activity. The February resurgence indicates sustained threat actor interest and stable operational tempo. Overall, the three-month pattern suggests a steady ransomware pressure environment rather than a spike-driven campaign, reinforcing the assessment that Singapore remains a consistently attractive target for financially motivated ransomware operators.
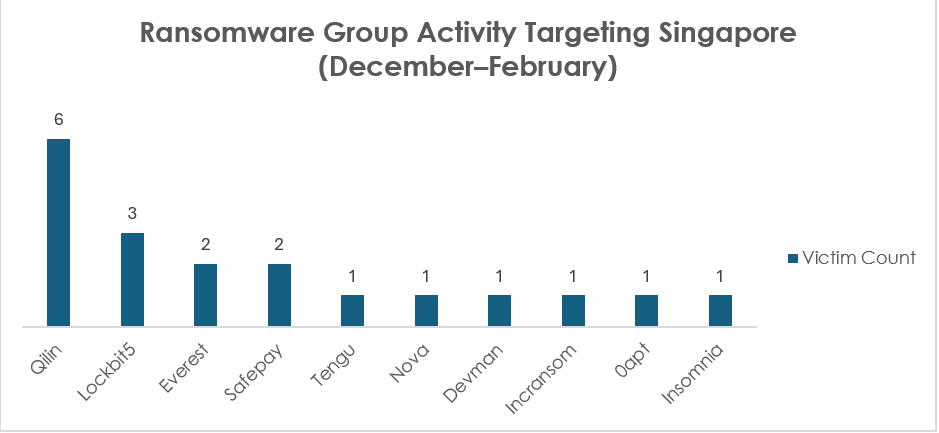
Between December and February, ransomware activity impacting Singapore reflects a moderately fragmented but Qilin-dominant threat landscape, with Qilin (6 incidents) emerging as the most active operator, accounting for the largest share of observed victim listings during the period. This is followed by LockBit5 (3), while Everest (2) and Safepay (2) show secondary but consistent presence. The remaining activity is distributed across single-incident Ransomware gangs: Tengu, Nova, Devman, Incransom, 0apt, and Insomnia, indicating opportunistic or low-frequency targeting rather than sustained campaigns. Overall, the data suggests a hybrid environment where one primary RaaS actor maintains repeated operational focus on Singapore-based entities, while multiple smaller or emerging groups test access footholds. The concentration of activity among a limited number of groups implies structured affiliate-driven targeting rather than random victim selection, and the presence of both established (LockBit lineage) and lesser-known actors signals continued attractiveness of Singapore-based organizations for data exfiltration and double-extortion operations.
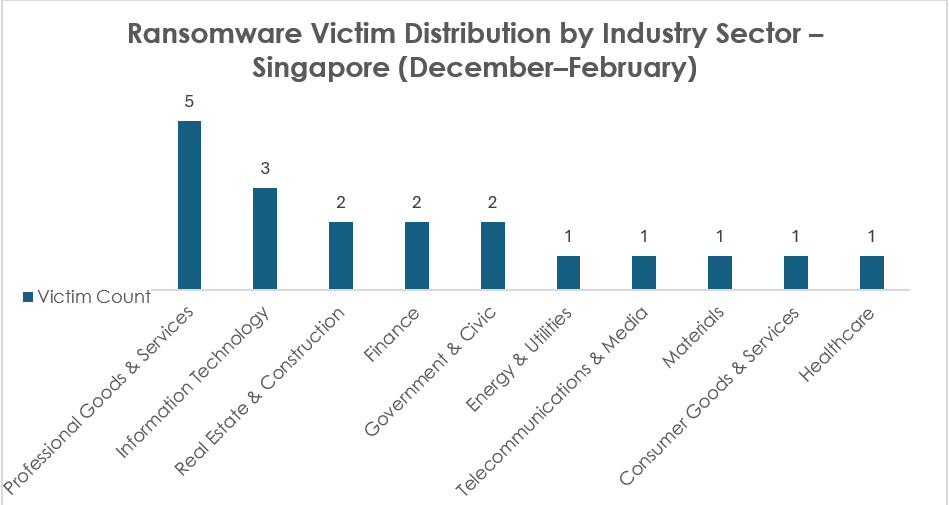
Between December and February, ransomware victim distribution in Singapore shows Professional Goods & Services (5 incidents) as the most targeted sector, indicating threat actors are prioritizing firms that manage client data, consulting portfolios, and outsourced business functions, likely due to high leverage for double extortion. Information Technology (3 incidents) follows, reinforcing the risk of supply-chain compromise and managed service provider exposure. Real Estate & Construction (2), Finance (2), and Government & Civic (2) demonstrate continued interest in sectors holding sensitive financial records, regulatory data, and infrastructure-linked information. Single-incident targeting across Energy & Utilities, Telecommunications & Media, Materials, Consumer Goods & Services, and Healthcare reflects opportunistic activity but also signals broad cross-sector exposure. Overall, the distribution suggests financially motivated actors focusing on data-rich, service-oriented enterprises while maintaining diversified targeting to maximize extortion opportunities across Singapore’s interconnected economic ecosystem.
Recent vulnerability exploitation trends targeting Singapore indicate sustained scanning and compromise attempts against high-severity remote code execution flaws affecting web servers, enterprise applications, and network edge devices. The majority of the identified CVEs carry critical CVSS scores ranging from 9.8 to 10.0, enabling full system compromise with minimal interaction. Notably, 14 out of the 15 listed vulnerabilities have publicly available exploit code, significantly increasing exposure by lowering the technical barrier for both opportunistic threat actors and state-aligned groups. This high exploit availability, combined with the continued presence of legacy and internet-facing systems, reinforces the elevated risk environment for organizations operating in Singapore.
| Vulnerability | CVSS | Vendor | Product | Exploit Available? | Malware/Threat Actors / APTs Exploiting These CVEs |
| CVE-2021-42013 | 9.8 | Apache | Apache HTTP Server | Link | |
| CVE-2017-9841 | 9.8 | PHPUnit – Sebastian Bergmann | PHPUnit | Link | |
| CVE-2017-18368 | 9.8 | Zyxel/Billion | ZyXEL P660HN-T1A v1, ZyXEL P660HN-T1A v2, Billion 5200W-T | Link | |
| CVE-2025-55182 | 10.0 | Meta | React Server Components | Link | Exploited by Salt Typhoon and Ashen Lepus |
| CVE-2022-24816 | 10.0 | Geoserver | Geoserver (JAI-EXT) | Link | |
| CVE-2015-1427 | 9.8 | Elastic | Elasticsearch | Link | |
| CVE-2016-1555 | 9.8 | NETGEAR | WN604, WN802Tv2, WNAP210v2, WNAP320, WNDAP350, WNDAP360, and WNDAP660 | Link | |
| CVE-2016-3088 | 9.8 | Apache | ActiveMQ | Link | |
| CVE-2017-1000486 | 9.8 | PrimeFaces | PrimeTek | Link | |
| CVE-2017-10271 | 9.8 | Oracle | Oracle Weblogic Server | Link | |
| CVE-2017-15944 | 9.8 | Palo Alto Networks | PAN-OS | Link | |
| CVE-2017-9805 | 8.1 | Apache | Struts | Link | |
| CVE-2018-10562 | 9.8 | Dasan | Dasan GPON Home Router | Link | |
| CVE-2018-1273 | 9.8 | Spring | Spring Data Commons | Link | |
| CVE-2018-14839 | 9.8 | LG | NAS N1A1 | – |
Singapore’s current cyber threat landscape is shaped by a convergence of state-sponsored espionage campaigns, financially motivated cybercrime, and data-driven underground economies. Advanced persistent threat (APT) actors linked to nation states such as UNC3886, Mustang Panda, Volt Typhoon, APT41, and Lazarus Group are actively targeting sectors critical to Singapore’s digital economy and strategic influence. Telecommunications networks, fintech platforms, semiconductor manufacturing, government institutions, and regional corporate headquarters remain high-value targets due to the country’s role as a regional connectivity hub, financial center, and diplomatic node in Southeast Asia. These actors commonly exploit unpatched enterprise systems, network edge devices, and virtualization platforms while leveraging techniques such as credential abuse, living-off-the-land activity, and stealthy persistence to maintain long-term access. Parallel to this espionage activity, dark web markets show strong demand for Singapore-linked personal data, financial credentials, and healthcare records, while ransomware groups increasingly target service-oriented industries and IT providers to maximize extortion leverage.
Looking ahead, Singapore’s threat environment is likely to intensify as geopolitical competition, digital transformation, and regional economic interdependence expand the cyber-attack surface. Telecommunications infrastructure, digital finance platforms, and supply-chain ecosystems will remain attractive targets for both espionage actors seeking strategic intelligence and cybercriminal groups pursuing financial gain. However, the same pressures also create opportunities for Singapore to strengthen its position as a regional leader in cybersecurity resilience. By investing in advanced threat intelligence integration, proactive vulnerability management, cross-sector incident response collaboration, and stronger supply-chain security frameworks, Singapore can transform current threat exposure into a driver for improved cyber defense maturity. Continued cooperation between government agencies, critical infrastructure operators, and private sector organizations will be key to detecting sophisticated campaigns earlier, reducing operational impact, and reinforcing trust in Singapore’s digital and financial ecosystems.
Singapore’s evolving cyber risk environment is increasingly shaped by hybrid threat models that blend espionage, financial crime, and strategic prepositioning. Several emerging vectors warrant heightened monitoring:
Singapore’s cyber risk outlook suggests that both strategic espionage operations and financially motivated cybercrime will remain persistent elements of the threat landscape in the coming years. As digital transformation accelerates across government, finance, telecommunications, and advanced manufacturing sectors, the attack surface available to threat actors will continue to expand. State-aligned APT groups are likely to maintain interest in telecommunications infrastructure, cloud environments, and regional corporate networks to support geopolitical intelligence collection and potential operational pre-positioning. Simultaneously, cybercriminal organizations will continue exploiting exposed systems, stolen credentials, and supply-chain relationships to facilitate ransomware operations, financial fraud, and large-scale data monetization. Singapore’s position as a hub for global connectivity, fintech innovation, and multinational headquarters will therefore sustain its attractiveness as a high-value cyber target.
However, Singapore also possesses strong institutional capabilities and cybersecurity governance structures that can transform current challenges into opportunities for enhanced resilience. Continued investment in advanced threat intelligence integration, proactive vulnerability management, cross-sector incident response coordination, and supply-chain security oversight will be essential to mitigating both espionage and cybercrime risks. Strengthening public–private partnerships, expanding regional information-sharing mechanisms, and improving detection capabilities for stealthy intrusion techniques will further enhance national cyber defense. By maintaining a proactive security posture and fostering collaboration between government agencies, critical infrastructure operators, and private sector organizations, Singapore can not only manage the evolving threat environment but also reinforce its reputation as one of the most secure and resilient digital economies in the Asia-Pacific region.