


CYFIRMA Research and Advisory Team would like to highlight ransomware trends and insights gathered while monitoring various forums. This includes multiple – industries, geography, and technology – that could be relevant to your organization.
Type: Ransomware
Target Technologies: Windows
Introduction
CYFIRMA Research and Advisory Team has found Zollo Ransomware while monitoring various underground forums as part of our Threat Discovery Process.
Zollo Ransomware
Research identified Zollo as a ransomware variant associated with the MedusaLocker family. Upon successful infection, the malware initiates a file encryption routine that targets user data and appends a distinct extension, such as “.zollo6” (with possible numerical variation), to each affected file, effectively rendering them inaccessible. For example, files like “1.jpg” and “2.png” are renamed to “1.jpg.zollo6” and “2.png.zollo6.” Beyond encryption, Zollo performs additional system modifications, including altering the desktop wallpaper to signal compromise and deploying a ransom note file titled “READ_NOTE.html.” These actions demonstrate a structured post-infection workflow designed to both disrupt normal system use and ensure the victim is immediately aware of the attack.
Screenshot: File encrypted by the ransomware (Source: Surface Web)
The ransom note outlines that the encryption process relies on a combination of RSA and AES cryptographic algorithms and explicitly warns against attempts to restore, rename, or tamper with the encrypted files, stating such actions may lead to permanent data loss. It also claims that confidential and personal data have been exfiltrated and stored on a private server controlled by the attackers. According to the message, this data will be deleted only after payment is completed; otherwise, it may be publicly released or sold. The note provides contact instructions via two email addresses and imposes a 72-hour window for the victim to respond, after which the ransom amount is said to increase, reinforcing urgency and pressure within the communication.
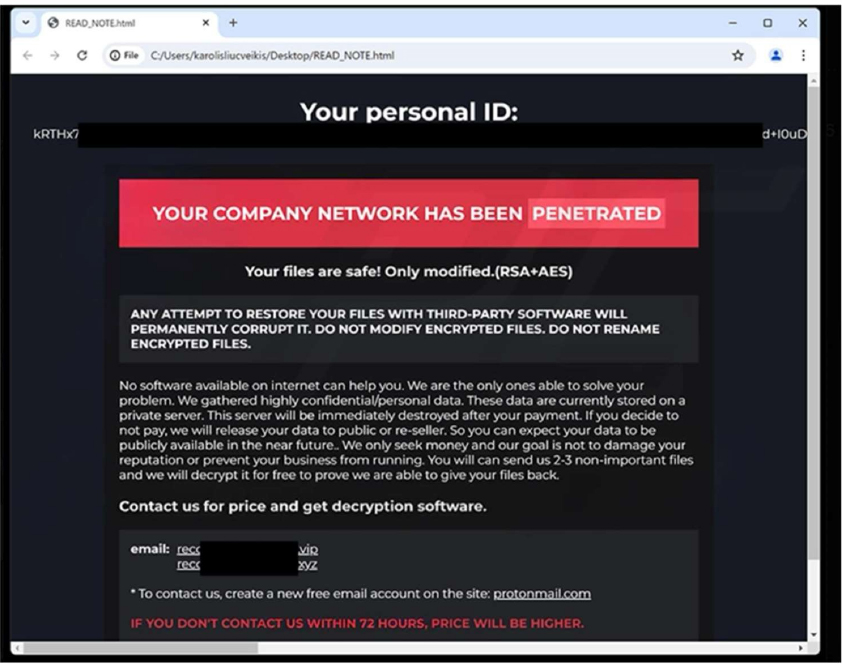
The appearance of the Zollo Ransomware ransom note (READ_NOTE.html) (Source: Surface Web)
The following are the TTPs based on the MITRE Attack Framework
| Tactic | Technique ID | Technique Name |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1129 | Shared Modules |
| Persistence | T1112 | Modify Registry |
| Persistence | T1542.003 | Pre-OS Boot: Bootkit |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1055 | Process Injection |
| Privilege Escalation | T1134.004 | Access Token Manipulation: Parent PID Spoofing |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Defense Evasion | T1014 | Rootkit |
| Defense Evasion | T1027.002 | Obfuscated Files or Information: Software Packing |
| Defense Evasion | T1027.005 | Obfuscated Files or Information: Indicator Removal from Tools |
| Defense Evasion | T1036 | Masquerading |
| Defense Evasion | T1055 | Process Injection |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1112 | Modify Registry |
| Defense Evasion | T1134.004 | Access Token Manipulation: Parent PID Spoofing |
| Defense Evasion | T1140 | Deobfuscate/Decode Files or Information |
| Defense Evasion | T1202 | Indirect Command Execution |
| Defense Evasion | T1222 | File and Directory Permissions Modification |
| Defense Evasion | T1497.001 | Virtualization/Sandbox Evasion: System Checks |
| Defense Evasion | T1542.003 | Pre-OS Boot: Bootkit |
| Defense Evasion | T1564.003 | Hide Artifacts: Hidden Window |
| Credential Access | T1056.001 | Input Capture: Keylogging |
| Discovery | T1010 | Application Window Discovery |
| Discovery | T1012 | Query Registry |
| Discovery | T1016 | System Network Configuration Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1497.001 | Virtualization/Sandbox Evasion: System Checks |
| Discovery | T1518.001 | Software Discovery: Security Software Discovery |
| Discovery | T1614 | System Location Discovery |
| Collection | T1056.001 | Input Capture: Keylogging |
| Collection | T1074 | Data Staged |
| Command and Control | T1071 | Application Layer Protocol |
| Command and Control | T1573 | Encrypted Channel |
| Impact | T1486 | Data Encrypted for Impact |
| Impact | T1490 | Inhibit System Recovery |
Relevancy and Insights:
ETLM Assessment:
CYFIRMA’s assessment indicates that Zollo is a ransomware threat that encrypts data on compromised systems, leading to restricted access to critical files and disruption of normal operations. Its execution reflects a structured and multi-stage workflow, where the malware performs system-level interactions to ensure effective deployment and impact. It demonstrates environmental awareness through checks such as CPU identification and available disk space evaluation, which can be used to assess execution conditions. The malware also establishes persistence within the infected system, enabling it to remain active across reboots and maintain control over time. In addition, it undertakes actions that support uninterrupted execution, including interacting with system processes and services to facilitate broader access to targeted data.
From a forward-looking perspective, this ransomware has the potential to evolve into a more adaptive and resilient threat by enhancing its operational depth and evasion capabilities. Future iterations could incorporate more advanced environment profiling techniques, enabling more precise targeting and improved avoidance of analysis or security controls. The persistence mechanisms may become more sophisticated and layered, ensuring long-term access even in partially remediated environments. Furthermore, the integration of more efficient data handling and exfiltration workflows, combined with expanded system interference techniques, could increase overall impact. Such developments would allow the threat to operate with greater stealth, sustain longer dwell times, and exert increased pressure on affected systems through a combination of disruption and data control.
Additionally, the threat could progress toward more automated and scalable attack capabilities, enabling wider distribution and faster execution across multiple environments. Enhancements in lateral movement techniques and network propagation could allow it to spread more effectively within organizational infrastructures. Coupled with improved coordination between encryption routines and system disruption mechanisms, these advancements would further strengthen its ability to maximize damage, maintain persistence across endpoints, and complicate detection and incident response efforts.
Sigma rule:
title: New RUN Key Pointing to Suspicious Folder tags:
– attack.privilege-escalation
– attack.persistence
– attack.t1547.001 logsource:
category: registry_set product: windows
detection: selection_target:
TargetObject|contains:
– ‘\Software\Microsoft\Windows\CurrentVersion\Run’
– ‘\Software\WOW6432Node\Microsoft\Windows\CurrentVersion\Run’
– ‘\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run’ selection_suspicious_paths_1:
Details|contains:
– ‘:\Perflogs’
– :\ProgramData’
– ‘:\Windows\Temp’
– ‘:\Temp’
– ‘\AppData\Local\Temp’
– ‘\AppData\Roaming’
– ‘:\$Recycle.bin’
– ‘:\Users\Default’
– ‘:\Users\public’
– ‘%temp%’
– ‘%tmp%’
– ‘%Public%’
– ‘%AppData%’ selection_suspicious_paths_user_1:
Details|contains: ‘:\Users\’ selection_suspicious_paths_user_2:
Details|contains:
– ‘\Favorites’
– ‘\Favourites’
– ‘\Contacts’
– ‘\Music’
– ‘\Pictures’
– ‘\Documents’
– ‘\Photos’ filter_main_windows_update:
TargetObject|contains: ‘\Microsoft\Windows\CurrentVersion\RunOnce\’ Image|startswith: ‘C:\Windows\SoftwareDistribution\Download\’ Details|contains|all:
– ‘rundll32.exe ‘
– ‘C:\WINDOWS\system32\advpack.dll,DelNodeRunDLL32’ Details|contains:
– ‘\AppData\Local\Temp\’
– ‘C:\Windows\Temp\’ filter_optional_spotify:
Image|endswith:
– ‘C:\Program Files\Spotify\Spotify.exe’
– ‘C:\Program Files (x86)\Spotify\Spotify.exe’
– ‘\AppData\Roaming\Spotify\Spotify.exe’ TargetObject|endswith:
‘SOFTWARE\Microsoft\Windows\CurrentVersion\Run\Spotify’ Details|endswith: ‘Spotify.exe –autostart –minimized’
condition: selection_target and (selection_suspicious_paths_1 or (all of selection_suspicious_paths_user_* )) and not 1 of filter_main_* and not 1 of filter_optional_*
falsepositives:
– Software using weird folders for updates level: high
(Source: Surface Web)
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
Type: Remote Access Trojan | Objectives: Data Exfiltration/ Remote Control | Target Technology: Windows OS | Target Geography: Global
CYFIRMA collects data from various forums based on which the trend is ascertained. We identified a few popular malware that were found to be distributed in the wild to launch cyberattacks on organizations or individuals.
Active Malware of the week
This week, “Raton RAT” is in focus.
Overview of Operation Raton RAT Malware
The analysed Raton RAT sample functions as a remote access tool designed to provide an external operator with control over a compromised Windows system. When executed, the malware begins interacting with the local environment and initiates communication with external infrastructure to establish a connection with its operator. During execution, it performs several system queries, including checks related to the operating system, running processes, and registry entries. These activities indicate that the malware attempts to gather basic information about the host system while preparing the environment for further interaction.
Network analysis shows that the sample sends requests to external IP lookup services such as ip-api.com to determine the public IP address and network characteristics of the infected machine. Such queries are commonly used by malware to identify the geographical location or network environment of a target system. In addition to these lookups, the malware establishes outbound connections to remote infrastructure that may serve as command-and-control communication channels, enabling the operator to exchange commands and data with the compromised host.
Further observation reveals that the malware interacts with several Windows services and system components during runtime. It accesses registry paths, creates temporary files within user directories, and loads multiple system libraries required for its execution. These behaviours allow the malware to operate alongside legitimate system processes and maintain its functionality while remaining relatively unobtrusive. Taken together, these activities indicate that malware is designed to collect basic system information, establish network connectivity with external infrastructure, and enable remote interaction with the infected system.
Attack Method
Upon execution, the malware begins performing a sequence of operations to integrate itself into the system environment. It interacts with several core Windows processes, including svchost.exe, services.exe, and lsass.exe, allowing the malicious process to run in parallel with legitimate system activities. During this stage, multiple Windows libraries are loaded, particularly those associated with service management and registry operations. These components enable the malware to access system resources and carry out actions that require elevated interaction with the operating system.
Following successful execution, malware conducts reconnaissance activities to gather information about the host system. It leverages Windows Management Instrumentation (WMI) to query system classes such as Win32_OperatingSystem and AntivirusProduct, which provide details about the operating system and the presence of installed security solutions. The malware also collects additional system information by invoking functions related to process enumeration and network configuration. Furthermore, it accesses several registry locations across both user and system hives, likely to obtain configuration details and assess the system environment before proceeding with additional operations.
Network communication plays a key role in malware’s behaviour. During analysis, the sample was observed by issuing HTTP requests to external IP lookup services, including ip-api.com, to determine the public IP address and network attributes of the infected system. Such requests allow attackers to identify the network environment of the compromised host, including its geographical location or whether it is operating within a hosting or proxy-based network. In parallel, the malware performs DNS lookups and establishes outbound TCP connections to infrastructure linked to the domain cloudpub[.]ru, which appears to support command-and-control communication.
In addition to reconnaissance and network activity, the malware carries out several runtime management tasks. Temporary files are created within user directories during execution and are later removed, indicating their use for temporary operational purposes. The malware also generates mutex objects to regulate process execution and prevent multiple instances from running simultaneously. Registry entries associated with Windows tracing services are modified as well, which may assist in controlling or monitoring certain internal functions. Collectively, these actions demonstrate how malware prepares the system environment, gathers system.
The following are the TTPs based on the MITRE Attack Framework for Enterprise
| Tactic | Technique ID | Technique Name |
| Execution | T1053 | Scheduled Task/Job |
| Execution | T1059 | Command and Scripting Interpreter |
| Execution | T1106 | Native API |
| Execution | T1129 | Shared Modules |
| Persistence | T1112 | Modify Registry |
| Persistence | T1547 | Boot or Logon Autostart Execution |
| Privilege Escalation | T1055 | Process Injection |
| Privilege Escalation | T1134 | Access Token Manipulation |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1070 | Indicator Removal |
| Defense Evasion | T1222 | File and Directory Permissions Modification |
| Defense Evasion | T1497 | Virtualization/Sandbox Evasion |
| Defense Evasion | T1620 | Reflective Code Loading |
| Discovery | T1012 | Query Registry |
| Discovery | T1033 | System Owner/User Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1087 | Account Discovery |
| Discovery | T1518 | Software Discovery |
| Command and control | T1071 | Application Layer Protocol |
| Command and control | T1095 | Non-Application Layer Protocol |
| Impact | T1496 | Resource Hijacking |
INSIGHTS
The behaviour of the analysed sample indicates that it operates as a multi-purpose remote access tool rather than a single-function piece of malware. Its design and feature set suggest that it was developed to provide operators with broad control over infected systems. The presence of several configurable functions and management options indicates that the tool can be adjusted depending on the operator’s needs or the conditions of the compromised environment.
Another noticeable characteristic is the way the malware operates alongside normal system activity. Instead of relying solely on suspicious standalone processes, it interacts with legitimate Windows components and services during execution. By utilizing standard system libraries and processes, the malware’s activity can appear similar to routine operating system behaviour, which helps it remain less conspicuous during runtime.
The analysis also shows that malware attempts to understand the system and network environment before further interaction occurs. By collecting basic host and network information, the operator can obtain a clearer picture of the compromised system. This behaviour indicates that the tool is not only intended for remote control, but also for assessing and managing the infected environment during an intrusion.
ETLM ASSESSMENT
From an ETLM perspective, Raton RAT highlights a future in which Windows-focused threats may become increasingly adaptive and integrated with normal system operations, making malicious activity more difficult to detect. Such tools are likely to leverage legitimate services and everyday applications to maintain covert access and control. For organizations and employees, this evolution could increase the risk of unauthorized data access, system manipulation, and ongoing surveillance of user activity. Over time, even routine processes may be exploited, potentially undermining trust in standard IT environments and increasing the complexity of maintaining effective security.
IOCs:
Kindly refer to the IOCs Section to exercise controls on your security systems.
YARA Rules
rule RatonRAT_Comprehensive
{
meta:
description = “detection for Raton RAT including hashes and behavioral indicators” author = “CYFIRMA”
date = “2026-03-16”
strings:
/* File Hashes */
$hash_1 = “b15562c0771ce6855e2186998be98482584951039424400b2413dd2f86362820”
$hash_2 = “25b442da47743d5c195cdf6178248d2b1eeb5238d22341dc6a7fedfa5abdab37”
$hash_3 = “13f4b05abe78f7a5714f32ecddc9b5b463803c62cd8355f493b42af8cb4fa9db”
$hash_4 = “a9123cc28991a45d576c7a1302fb4c335cff34d4548c8a8f78aae54aa839c173”
$hash_5 = “15734c54d25341317a2f58bbc3c9ed3f8efa73af50fb5feb1ef46b6c3e02cab9”
$hash_6 = “3578222693be106eac90343c12f06454b6de6e19a50d31ae5105218c36514bbd”
/* Mutexes created */
$mutex_1 = “eed3bd3a-a1ad-4e99-987b-d7cb3fcfa7f0”
$mutex_2 = “pXKpWDdoLzpgwPiRSUNkUJ9”
$mutex_3 = “Local\\MidiMapper_modLongMessage_RefCnt”
/* Registry keys accessed or modified */
$reg_1 = “HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Tracing\\qZGuNez_RASAPI32”
$reg_2 = “HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Tracing\\qZGuNez_RASMANCS”
$reg_3 = “HKEY_CURRENT_USER\\Software\\Microsoft\\.NETFramework”
$reg_4 = “HKEY_CURRENT_USER\\Control Panel\\International”
/* Network indicators */
$net_1 = “cloudpub.ru”
/* Behavioural indicators */
$behavior_1 = “ExecQueryWmi”
$behavior_2 = “GetAdaptersAddresses”
$behavior_3 = “advapi32.RegOpenKeyExW”
$behavior_4 = “GetTickCount”
$behavior_5 = “IsDebuggerPresent”
condition:
any of ($hash_*) or any of ($mutex_*) or any of ($reg_*) or any of ($net_*) or any of ($behavior_*)
}
Strategic Recommendations
Management Recommendations
Tactical Recommendations
Key Intelligence Signals:
Camaro Dragon, aka Mustang Panda, Carries Out Rapid Espionage Operations
About the Threat Actor
Mustang Panda is a Chinese state-associated espionage group active since at least 2012, known for conducting structured, geopolitically motivated intelligence operations with a strong focus on adaptability and long-term persistence. Its campaigns often start with targeted spear-phishing emails, typically using politically themed lures delivered via ZIP, RAR, LNK, or malicious URLs, followed by multi-stage payload deployment, where initial loaders introduce backdoors, reverse shells, and tools for lateral movement.
The group frequently uses malware families such as PlugX, Poison Ivy, ToneShell, StarProxy, Claimloader, and SplatCloak, relying heavily on techniques like DLL sideloading and encrypted command-and-control channels to remain undetected and maintain access. In some cases, it has also leveraged infected USB drives for propagation. Overall, Mustang Panda demonstrates a high level of capability, combining precise targeting with modular malware frameworks to sustain prolonged access to sensitive networks.
Details on Exploited Vulnerabilities
| CVE ID | AffectedProducts | CVSS Score | Exploit Links |
| CVE-2021-1675 | Microsoft Windows | 7.8 | link1, link2, link3 |
| CVE-2021-40444 | Microsoft Windows | 7.8 | link1, link2, link3 |
TTPs based on MITRE ATT&CK Framework
| Tactic | ID | Technique |
| Reconnaissance | T1598.003 | Phishing for Information: Spear phishing Link |
| Resource Development | T1585.002 | Establish Accounts: Email Accounts |
| Resource Development | T1608 | Stage Capabilities |
| Resource Development | T1608.001 | Stage Capabilities: Upload Malware |
| Resource Development | T1588.004 | Obtain Capabilities: Digital Certificates |
| Resource Development | T1583.001 | Acquire Infrastructure: Domains |
| Initial Access | T1091 | Replication Through Removable Media |
| Initial Access | T1566.001 | Phishing: Spear phishing Attachment |
| Initial Access | T1566.002 | Phishing: Spear phishing Link |
| Execution | T1059.003 | Command and Scripting Interpreter: Windows Command Shell |
| Execution | T1059.005 | Command and Scripting Interpreter: Visual Basic |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
| Execution | T1203 | Exploitation for Client Execution |
| Execution | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Execution | T1204.001 | User Execution: Malicious Link |
| Execution | T1204.002 | User Execution: Malicious File |
| Execution | T1047 | Windows Management Instrumentation |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Persistence | T1546.003 | Event Triggered Execution: Windows Management Instrumentation Event Subscription |
| Persistence | T1574.001 | Hijack Execution Flow: DLL |
| Persistence | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Privilege Escalation | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
| Privilege Escalation | T1546.003 | Event Triggered Execution: Windows Management Instrumentation Event Subscription |
| Privilege Escalation | T1574.001 | Hijack Execution Flow: DLL |
| Privilege Escalation | T1053.005 | Scheduled Task/Job: Scheduled Task |
| Defense Evasion | T1480 | Execution Guardrails |
| Defense Evasion | T1564.001 | Hide Artifacts: Hidden Files and Directories |
| Defense Evasion | T1574.001 | Hijack Execution Flow: DLL |
| Defense Evasion | T1070.004 | Indicator Removal: File Deletion |
| Defense Evasion | T1036.005 | Masquerading: Match Legitimate Resource Name or Location |
| Defense Evasion | T1036.007 | Masquerading: Double File Extension |
| Defense Evasion | T1036.004 | Masquerading: Masquerade Task or Service |
| Defense Evasion | T1027 | Obfuscated Files or Information |
| Defense Evasion | T1027.013 | Obfuscated Files or Information: Encrypted/Encoded File |
| Defense Evasion | T1027.016 | Obfuscated Files or Information: Junk Code Insertion |
| Defense Evasion | T1553.002 | Subvert Trust Controls: Code Signing |
| Defense Evasion | T1218.004 | System Binary Proxy Execution: InstallUtil |
| Defense Evasion | T1218.005 | System Binary Proxy Execution: Mshta |
| Defense Evasion | T1218.014 | System Binary Proxy Execution: MMC |
| Defense Evasion | T1218.007 | System Binary Proxy Execution: Msiexec |
| Credential Access | T1003.003 | OS Credential Dumping: NTDS |
| Discovery | T1083 | File and Directory Discovery |
| Discovery | T1057 | Process Discovery |
| Discovery | T1518 | Software Discovery |
| Discovery | T1082 | System Information Discovery |
| Discovery | T1016 | System Network Configuration Discovery |
| Discovery | T1049 | System Network Connections Discovery |
| Lateral Movement | T1091 | Replication Through Removable Media |
| Collection | T1557.004 | Adversary-in-the-Middle: Evil Twin |
| Collection | T1560.001 | Archive Collected Data: Archive via Utility |
| Collection | T1119 | Automated Collection |
| Collection | T1560.003 | Archive Collected Data: Archive via Custom Method |
| Collection | T1074.001 | Data Staged: Local Data Staging |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and Control | T1219.002 | Remote Access Tools: Remote Desktop Software |
| Command and Control | T1573.001 | Encrypted Channel: Symmetric Cryptography |
| Command and Control | T1105 | Ingress Tool Transfer |
| Command and Control | T1102 | Web Service |
| Command and Control | T1090 | Proxy |
| Command and Control | T1095 | Non-Application Layer Protocol |
| Exfiltration | T1052.001 | Exfiltration Over Physical Medium: Exfiltration over USB |
Latest Developments Observed
The threat actor is suspected of conducting targeted campaigns against Qatari entities using Middle East conflict-themed lures to improve delivery success. The activity involved deploying PlugX through DLL hijacking alongside the use of Cobalt Strike for initial access and reconnaissance. Furthermore, the actor utilized a previously unseen Rust-based loader exploiting NVDA components, reflecting evolving tradecraft and a rapid operational pivot aligned with geopolitical developments, likely for espionage objectives.
ETLM Insights
Mustang Panda is a state-aligned cyber espionage actor focused on intelligence collection in line with China’s geopolitical priorities, demonstrating a high degree of operational agility in response to evolving regional dynamics.
China’s cyber operations strategy remains closely aligned with its broader national economic and strategic objectives. State-linked advanced persistent threat (APT) groups are consistently observed pursuing four primary goals:
Cyber espionage campaigns attributed to Chinese nation-state actors typically target high-value industrial sectors and multinational enterprises. These operations are designed to advance geopolitical interests while facilitating the collection of sensitive corporate data, research insights, and strategic business intelligence. Such intelligence can be leveraged to accelerate domestic technological development, enhance innovation cycles, and provide a competitive advantage to state-supported enterprises.
IOCs:
Kindly refer to the IOCs section to exercise control of your security systems. (Source: Surface Web)
YARA Rules
rule MustangPanda_CamaroDragon_PlugX_Variant
{
meta:
description = “Detects Mustang Panda (Camaro Dragon) activity using PlugX/Cobalt Strike related infrastructure”
author = “CYFIRMA” date = “2026-03-17”
threat_actor = “Mustang Panda / Camaro Dragon” malware_family = “PlugX / Loader”
hash1 =
“960e06362417ccfbcf4fed3713537961382ee856e83eae93ef528b1512bb9bd0”
hash2 =
“00000077553a5b27a610ac98f29563bbd6e0decc020c2d49e4fa0d89197e7fd8”
strings:
$s1 = “eqfvkn” ascii
/* Domains */
$d1 = “www.dest-working.com” ascii nocase
$d2 = “www.ynsins.com” ascii nocase
$d3 = “www.ainkstore.com” ascii nocase
$d4 = “www.bcller.com” ascii nocase
$d5 = “jcswcd.com” ascii nocase
$d6 = “newsmailnet.com” ascii nocase
/* IPs */
$ip1 = “202.59.10.106” ascii
$ip2 = “188.208.141.196” ascii
$ip3 = “139.59.46.88” ascii
$ip4 = “23.216.147.76” ascii
$ip5 = “20.99.133.109” ascii
/* CVE references */
$cve1 = “CVE-2021-40444” ascii
$cve2 = “CVE-2021-1675” ascii
condition:
(uint16(0) == 0x5A4D) and (
$s1 and
(2 of ($d*) or 2 of ($ip*) or any of ($cve*))
)
}
Strategic Recommendations
Management Recommendations
Tactical Recommendations
Europol and Interpol announce hit cybercrime operations in Bangladesh
Europol, in collaboration with Eurojust and law enforcement agencies from Austria, France, the Netherlands, and the United States, has executed Operation Lightning to dismantle the malicious residential proxy service known as SocksEscort. This service exploited compromised devices—primarily routers and IoT devices infected via vulnerabilities in certain residential modems—to build a large-scale botnet.
The operation targeted a network that had allegedly compromised more than 369,000 such devices across 163 countries, providing cybercriminals with access to over 35,000 proxies in recent years for activities like fraud and other cybercrimes. Authorities seized 34 domains and 23 servers in seven countries, while the United States froze approximately $3.5 million in cryptocurrency linked to the operation.
Separately, Interpol has announced the results of Operation Synergia III, the third phase of its ongoing counter-cybercrime initiative that began in 2023. Running from July 18, 2025, to January 31, 2026, this operation involved law enforcement from 72 countries and territories and focused on disrupting infrastructure used for phishing, malware, ransomware, and related schemes. The effort resulted in the takedown of more than 45,000 malicious IP addresses and servers. Authorities made 94 arrests worldwide, with 110 individuals still under investigation. In total, 212 electronic devices and servers were seized. Notably, Bangladesh saw significant action, with 40 arrests and the seizure of 134 devices tied to various scams, including loan fraud, job scams, identity theft, and credit card fraud. Coordinated raids and disruptions targeted key locations and malicious activities globally.
ETLM Assessment:
The operation focused on disrupting the infrastructure (domains, servers, and cryptocurrency wallets), but despite the initial focus on the hub in Bangladesh, investigations continue, with indications that seized servers may lead to further evidence and pursuits of the operators or downstream users. The hub in Bangladesh was providing anonymizing proxy infrastructure as a service (PaaS-like for cybercrime), enabling widespread fraud and other malicious operations rather than directly carrying out end-user attacks themselves. Roughly half of the arrests were conducted in other countries around the globe.
Russian hackers are targeting Signal and WhatsApp
Dutch intelligence agencies, the General Intelligence and Security Service (AIVD) and the Defence Intelligence and Security Service (MIVD), have issued a joint warning about a large-scale global cyber campaign attributed to Russian state-backed hackers (often referred to as Russian state actors or Kremlin-linked operatives). The attackers are targeting Signal and WhatsApp accounts belonging to high-value individuals, including dignitaries, government officials, military personnel, civil servants, and potentially journalists or others of interest to the Russian government. Dutch authorities confirmed that Dutch government employees have been among the targets and victims.
The primary tactic involves social engineering and phishing: Hackers impersonate official support entities—such as posing as a “Signal Support” chatbot, “Signal Security Support Chatbot,” or similar fake accounts—to trick users into revealing their verification codes, registration codes, or PINs. Once obtained, these credentials allow the attackers to take over the accounts, bypassing end-to-end encryption by gaining direct access to read messages, view contacts, and monitor communications. The agencies emphasized that this campaign relies on deception rather than exploiting technical vulnerabilities in the apps themselves.
ETLM Assessment:
The goal of the Russian state-backed hackers in this large-scale global cyber campaign, as identified by the intelligence agencies and CYFIRMA, is to gain unauthorized access to Signal and WhatsApp accounts belonging to high-value targets such as dignitaries, government officials, civil servants, military personnel, and potentially journalists or others of interest to the Russian government—including confirmed victims among Dutch government employees—in order to conduct espionage by secretly reading private messages, monitoring communications, and eavesdropping on group chats without needing to break the apps’ end-to-end encryption. Thus, enabling surveillance of sensitive discussions related to national security, policy, or other strategic information valuable to the Russian state’s interests.
Iranian hackers wipe a US medical manufacturing company
Iranian hackers have claimed responsibility for a major data-wiping cyberattack against a leading US medical manufacturing company, prompting the firm to instruct its 56,000 employees to disconnect from all networks and avoid powering on company devices. The hacktivist group stated the operation was in retaliation for recent US-Israeli military strikes on Iran. Authorities have linked the group to Iran’s intelligence services. The attackers reportedly gained access to the company’s device management platform, enabling them to remotely trigger wipes on enrolled corporate devices. The company has stated that ransomware was not involved and that its core production systems were not directly compromised. The incident carries significant potential for supply-chain disruptions, given the widespread use of the company’s medical devices in US hospitals.
ETLM Assessment:
Iranian state-linked hackers and affiliated hacktivist groups, such as Handala, typically pursue retaliation against US, Israeli, or Western interests following military strikes by opportunistically exploiting any vulnerable target that offers low barriers to entry and symbolic or disruptive impact, rather than limiting themselves to high-value military or government systems. This approach includes probing poorly secured networks, internet-connected devices, corporate supply chains, and mid-sized enterprises— often using unpatched vulnerabilities, compromised management platforms like Microsoft Intune for mass device wipes, or data exfiltration—to cause visible economic harm, operational chaos, or propaganda value while minimizing their own risk and resource demands amid constrained domestic connectivity or escalation risks. By framing such attacks as direct responses to perceived aggressions, they broaden the cyber battlespace, signal resolve, and impose asymmetric costs on adversaries through indirect, high-visibility disruptions in non-strategic sectors like healthcare manufacturing.
INC Ransomware Impacts LHT Holdings Limited
Summary:
CYFIRMA observed in an underground forum that a company from Singapore, LHT Holdings Limited (https[:]//www[.]lht[.]com[.]sg/), was compromised by INC Ransomware. LHT Holdings is a leading manufacturer of wooden pallets and crates based in Singapore. The company specializes in environmentally friendly packaging solutions, offering a comprehensive range of products, including pest-free IPPC pallets, plastic pallets, and technical wood. LHT also provides services such as industrial packaging, pallet rental, and waste disposal, catering to clients looking for sustainable and innovative packaging options. With a focus on emerging technology and sustainability, LHT aims to reduce carbon footprints while delivering high-quality products and services. Based on the screenshot, the ransomware leak post related to LHT Holdings Limited appears to expose internal corporate and financial documents. The preview images indicate that the compromised data likely includes financial records, invoices, transaction summaries, accounting spreadsheets, and operational documentation. Some of the visible files resemble billing statements, financial reports, and structured data tables, which may contain company financial details, payment information, and internal business records. Additionally, the presence of document forms and tabulated reports suggests that administrative paperwork and internal operational documents may also be part of the leaked dataset. Overall, the exposed data appears to consist primarily of sensitive financial and corporate business documentation, which could potentially reveal commercial transactions, financial performance details, and internal organizational records.
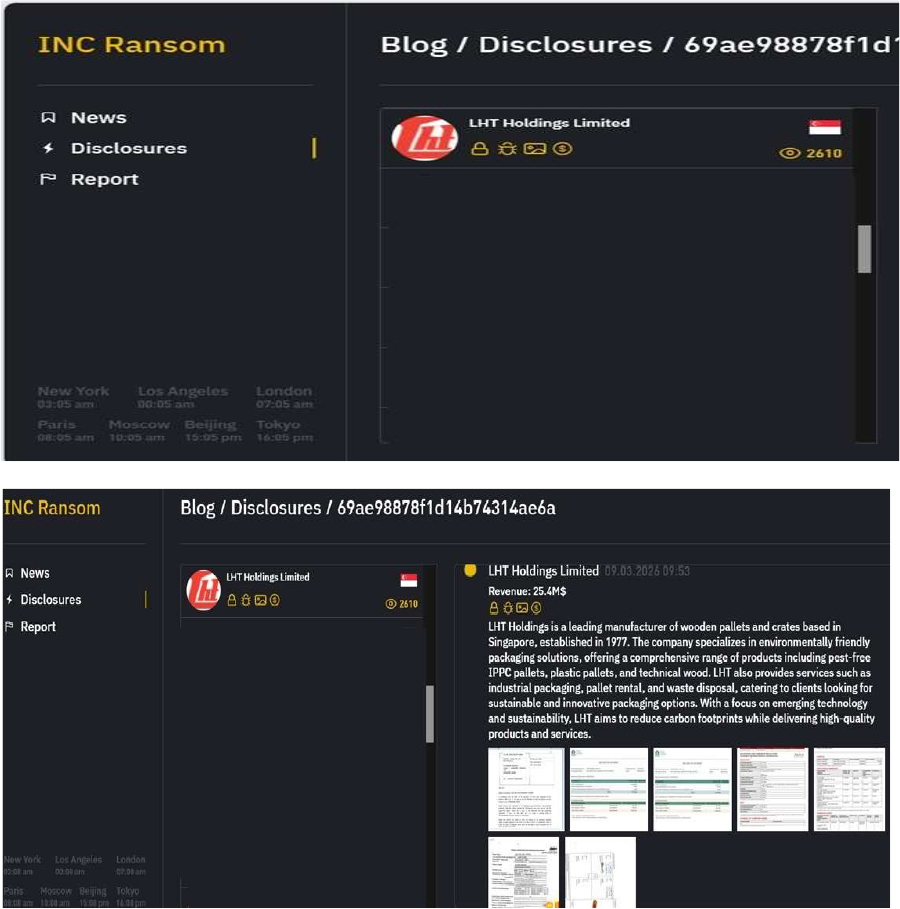
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
Based on recent assessments by CYFIRMA, INC Ransomware represents a significant threat within the evolving landscape of ransomware attacks. Its use of strong encryption methods and double extortion tactics highlights the increasing sophistication of cybercriminal operations. Organizations are advised to enhance their cybersecurity measures by implementing robust defenses against phishing attacks, maintaining updated security protocols, and monitoring for unusual network activity to mitigate risks associated with this and other ransomware variants. Continuous vigilance is essential to protect against the threats posed by emerging ransomware groups like INC Ransomware.
The Gentlemen Ransomware Impacts Malia Group
Summary:
CYFIRMA observed in an underground forum that a company from the United Arab Emirates, Malia Group(https[:]//www[.]maliagroup[.]com/), was compromised by the Gentlemen Ransomware. Malia Group is a multifaceted organization comprising 21 companies that operate across six sectors, including consumer goods distribution, technology solutions, fashion, engineering and contracting, and hospitality and real estate. With a strong presence in Lebanon, Iraq, and the United Arab Emirates (UAE), the group is committed to excellence in the creation, production, and timely delivery of goods and services. Over the past 80 years, Malia Group has built a portfolio of 60 brands and established partnerships with 50 leading multinationals, making it a preferred choice in the region. The compromised data includes confidential and sensitive information belonging to the organization.
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, the Gentlemen Ransomware is a highly adaptive and globally active threat that leverages dual-extortion tactics, combining data theft with file encryption. The group employs advanced evasion and persistence techniques, supports cross-platform and scalable ransomware deployment, and conducts targeted attacks across multiple industries and geographic regions. This combination of capabilities makes it a significant risk to enterprise cybersecurity defenses, particularly for organizations with limited detection and incident-response maturity.
Vulnerability in Ingress-NGINX Controller for Kubernetes
Relevancy & Insights:
The vulnerability exists due to improper input validation, where the “nginx.ingress.kubernetes.io/rewrite-target” Ingress annotation can be used to inject configuration into nginx.
Impact:
A remote user can inject and execute arbitrary code in the context of the ingress-nginx controller.
Affected Products:
https[:]//github[.]com/kubernetes/kubernetes/issues/137560
Recommendations:
Monitoring and Detection: Implement monitoring and detection mechanisms to identify unusual system behavior that might indicate an attempted exploitation of this vulnerability.
TOP 5 AFFECTED TECHNOLOGIES OF THE WEEK
This week, CYFIRMA researchers have observed significant impacts on various technologies due to a range of vulnerabilities. The following are the top 5 most affected technologies.
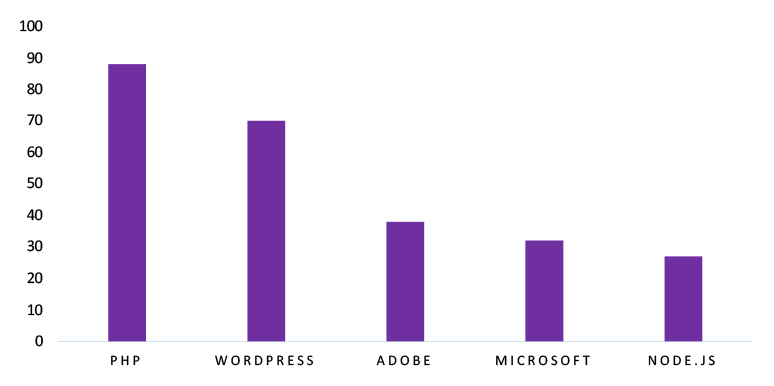
ETLM Assessment
Vulnerability in the Ingress-NGINX Controller for Kubernetes introduces significant risks to cloud-native infrastructures that rely on Kubernetes for container orchestration and application deployment. As Kubernetes is widely used across enterprise environments, cloud platforms, and DevOps pipelines, exploitation of this vulnerability could allow attackers to gain unauthorized access to cluster resources and manipulate containerized workloads. Organizations leveraging Kubernetes- based deployments must ensure timely patching and robust security monitoring to protect against potential compromise. Addressing this vulnerability is essential to maintaining the integrity of container orchestration platforms and safeguarding critical application infrastructure across industries and geographic regions.
DragonForce Ransomware attacked and published the data of Pantomath Group
Summary:
Recently, we observed that DragonForce Ransomware attacked and published the data of Pantomath Group (www[.]pantomathgroup[.]com) on its dark web website. Pantomath is a mid-market investment bank that offers a range of financial services, including investment banking, corporate advisory, asset management, and structured finance. The company serves mid-market businesses, family offices, and leading investors, leveraging a global network across 12+ countries. Based on the screenshot, the ransomware group appears to have published internal corporate documents belonging to Pantómath Group. The visible directory structure and file names suggest that the compromised data includes business development records, internal email folders, financial spreadsheets, and investment-related documentation. Files such as investment process status reports, valuation working sheets, provisional financial statements, and financial reports from March 2025 indicate that confidential financial and accounting information may have been exposed. Additionally, presentation files and annexure documents related to business unit activities and project assessments suggest that internal strategic planning materials, operational reports, and business presentations were also leaked. Overall, the breach appears to involve sensitive corporate financial data, investment documentation, and internal business communications, potentially revealing financial performance details, valuation analyses, and internal business strategies of the affected organization. The total volume of compromised data is estimated to be approximately 123.6 GB.
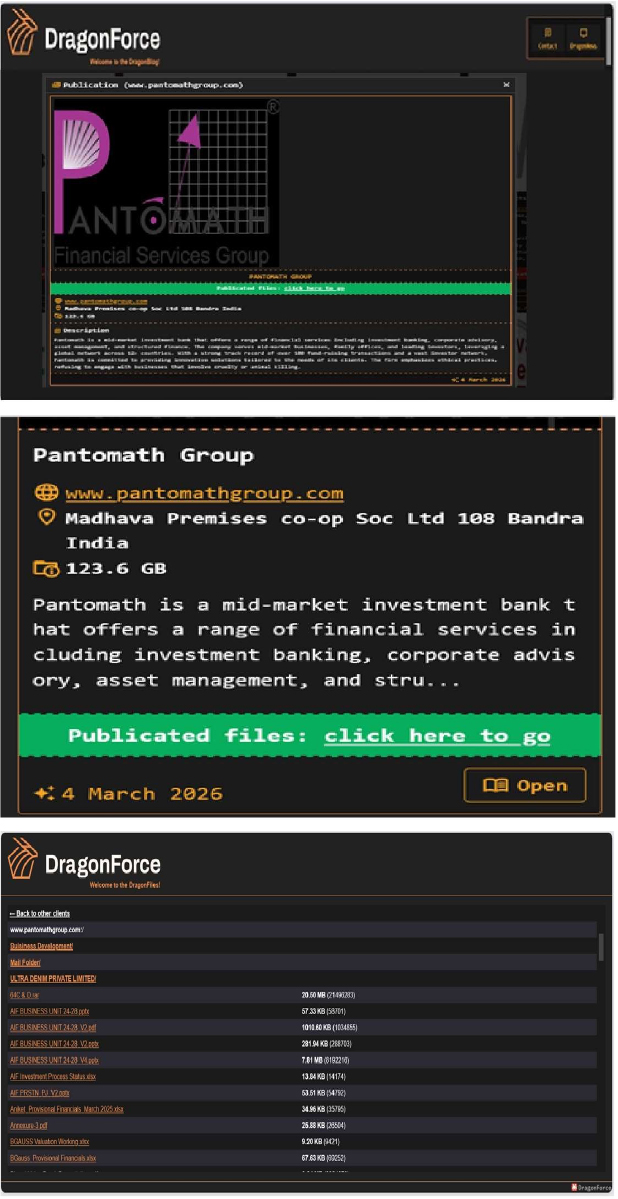
Source: Dark Web
Relevancy & Insights:
ETLM Assessment:
According to CYFIRMA’s assessment, DragonForce represents a significant threat in the ransomware landscape due to its advanced operational methods and extensive use of modified ransomware tools. As it continues to target high-profile organizations globally, ongoing vigilance and proactive cybersecurity strategies will be essential for mitigating risks associated with this formidable threat actor. Organizations should remain alert to the evolving tactics employed by groups like DragonForce to protect their sensitive data and maintain operational integrity.
Mideast Data Advertised on a Leak Site
Summary:
The CYFIRMA research team identified a post on a dark web forum by a threat actor operating under the alias “Anonymous2090”, who claims responsibility for a major data breach involving Mideast[.]com[.]sa (Saudi Arabia). According to the post, the compromise impacted the organization’s website, associated subdomains, mobile applications (available on Google Play and the Apple App Store), and backend infrastructure, with the attacker allegedly gaining access to the complete source code of both the web platform and mobile applications.
The threat actor further claims that the attack led to the deletion of databases and disruption of services, requiring the organization to rebuild its systems from the ground up. The exposed dataset is reported to exceed 40 GB of database content, in addition to sensitive source code.
The post also indicates that the stolen data is being offered for sale, including a sample download link and contact details shared via a messaging platform.
The allegedly compromised data includes:
At the time of analysis, the authenticity of the breach claim remains unverified. The available information originates solely from the threat actor’s forum post, and there has been no official confirmation from the affected organization or relevant authorities.
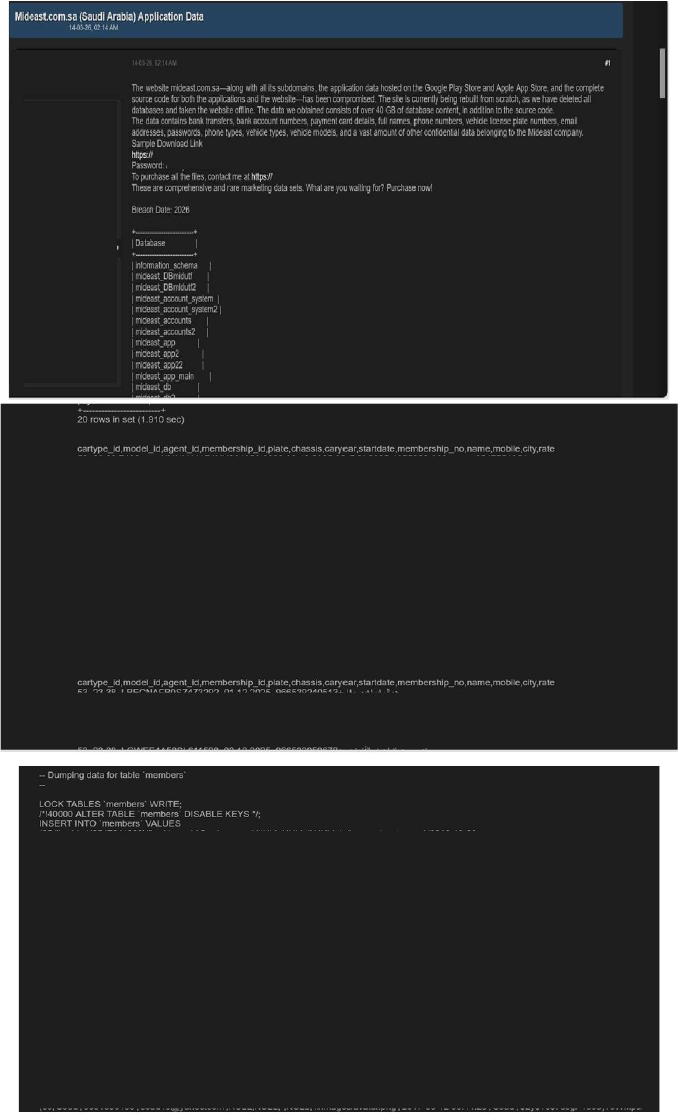
Source: Underground Forums
Electronic City Indonesia Data Advertised on a Leak Site
Summary: CYFIRMA’s research team observed that Electronic City Indonesia, a prominent online retail platform specializing in consumer electronics and home appliances, has allegedly been compromised by a threat actor. In a post published on a hacker forum, the actor claims to have breached the company’s backend systems on March 10, 2026, acquiring a substantial customer and order database.
According to the actor, the complete database contains over 618,000 unique customer records, with a sample of 54,000 rows publicly released to the community. The allegedly compromised data includes:
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
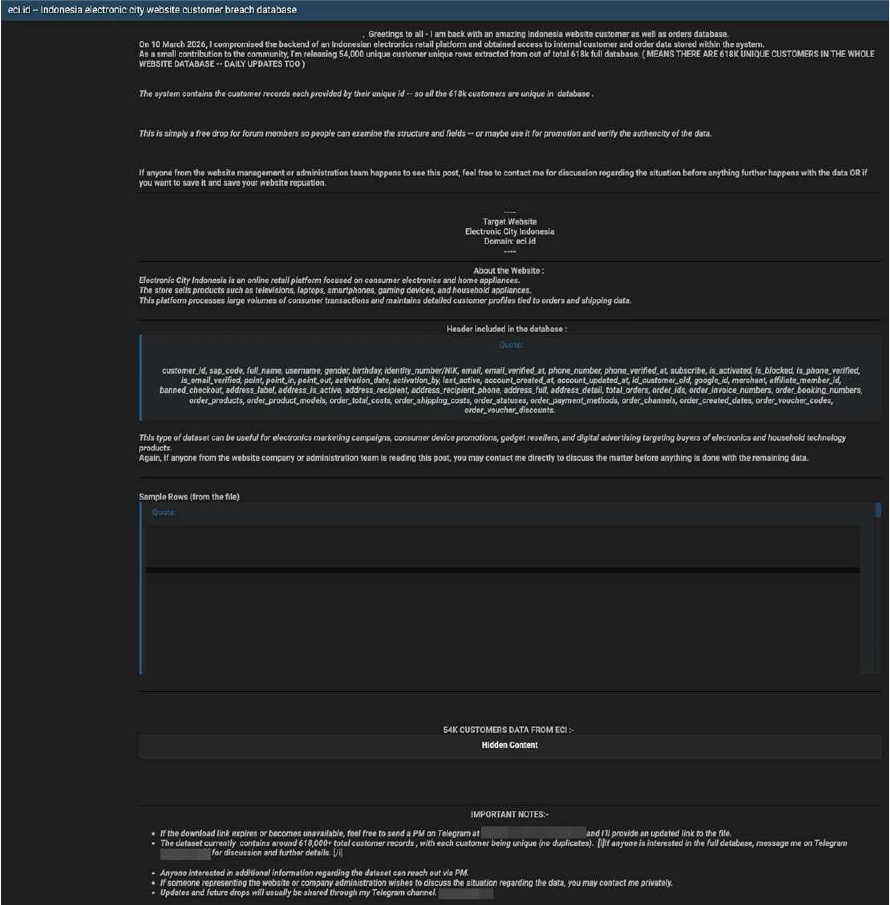
Source: Underground Forums
Relevancy & Insights:
Financially motivated cybercriminals are continuously looking for exposed and vulnerable systems and applications to exploit. A significant number of these malicious actors congregate within underground forums, where they discuss cybercrime and trade stolen digital assets. Operating discreetly, these opportunistic attackers target unpatched systems or vulnerabilities in applications to gain access and steal valuable data. Subsequently, the stolen data is advertised for sale within underground markets, where it can be acquired, repurposed, and utilized by other malicious actors in further illicit activities.
ETLM Assessment:
The threat actor known as “Anonymous2090” appears to be an active entity involved in data leak activities, frequently associated with claims of unauthorized system access and the sale of allegedly stolen data on dark web forums. Reports linking this alias to multiple incidents suggest a pattern of targeting organizations and attempting to monetize compromised information. The activity attributed to Anonymous2090 highlights the ongoing and evolving risks posed by actors operating within underground communities. These developments reinforce the need for organizations to strengthen their cybersecurity posture through continuous monitoring, effective use of threat intelligence, and proactive security measures to safeguard sensitive data and critical infrastructure.
Recommendations:
Enhance the cybersecurity posture by:
CYFIRMA’s research team observed that Cgpey International Private Limited, an Indian fintech platform specializing in payment infrastructure, salary disbursement, and business automation, has allegedly been compromised by an unidentified party. The incident, which reportedly took place on February 3, 2026, resulted in the exfiltration of approximately 26 GB of the company’s internal databases. The actor behind the breach claims the compromise was successful despite the platform’s public assertions of providing “100% secure” solutions.
The allegedly compromised data encompasses 3.85 million unique records, primarily consisting of payment processing logs from various merchants. According to the actor, the compromised data includes:
The authenticity of this breach remains unverified at the time of reporting, as the claim originates solely from the threat actor.
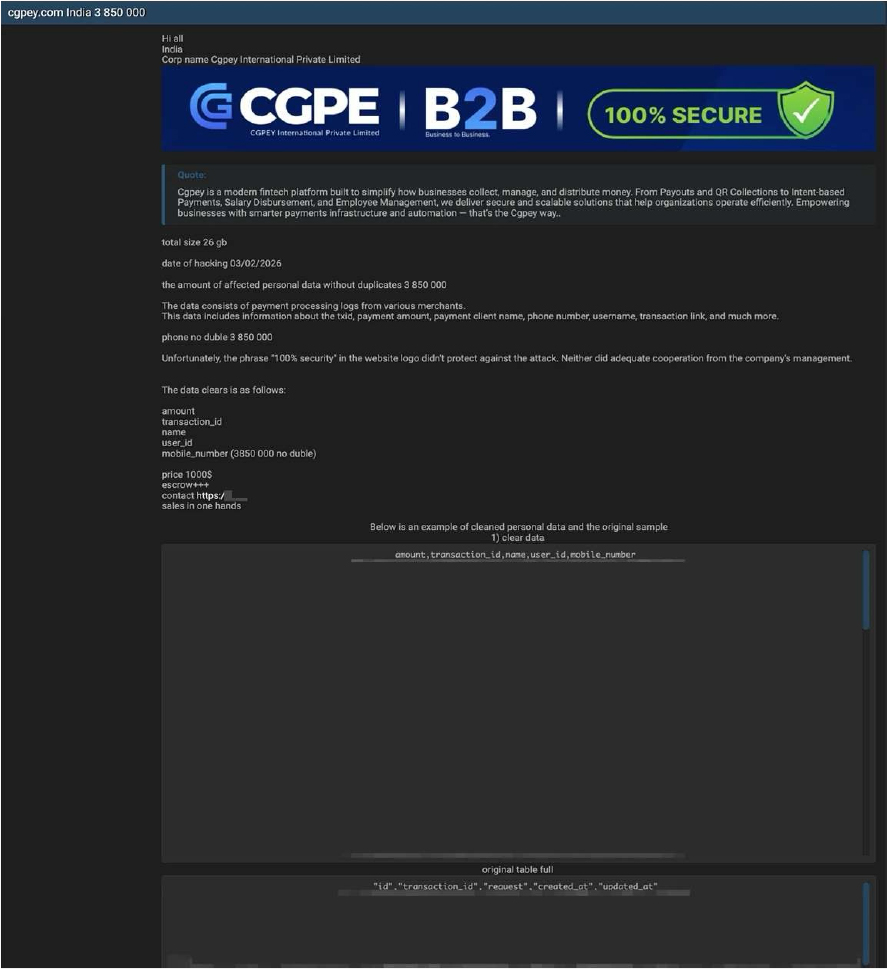
Source: Underground Forums
STRATEGIC RECOMMENDATIONS
MANAGEMENT RECOMMENDATIONS
TACTICAL RECOMMENDATIONS
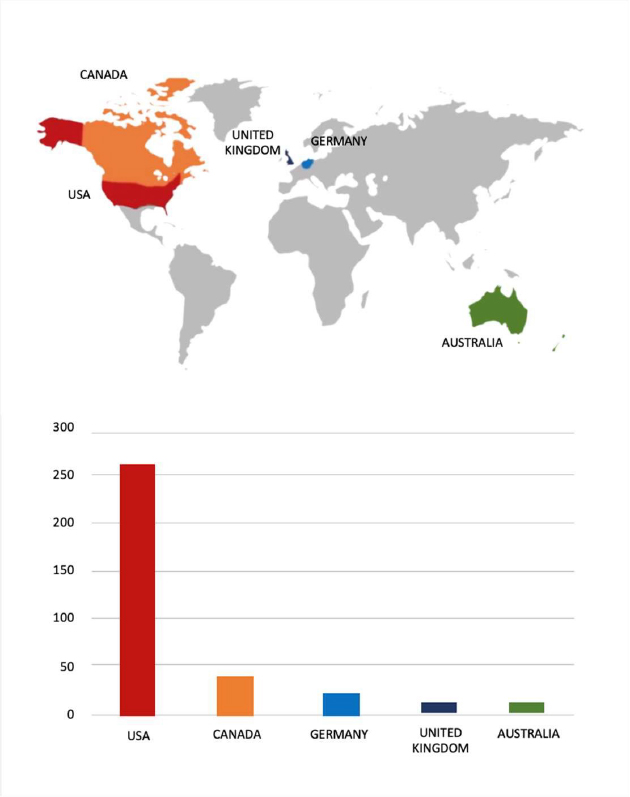
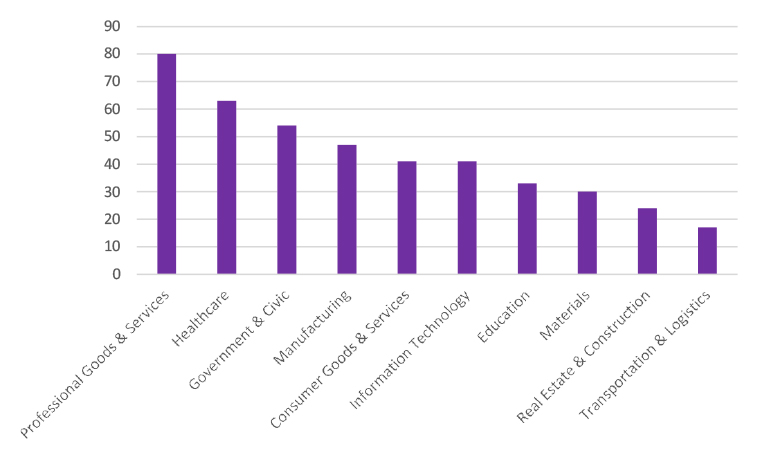
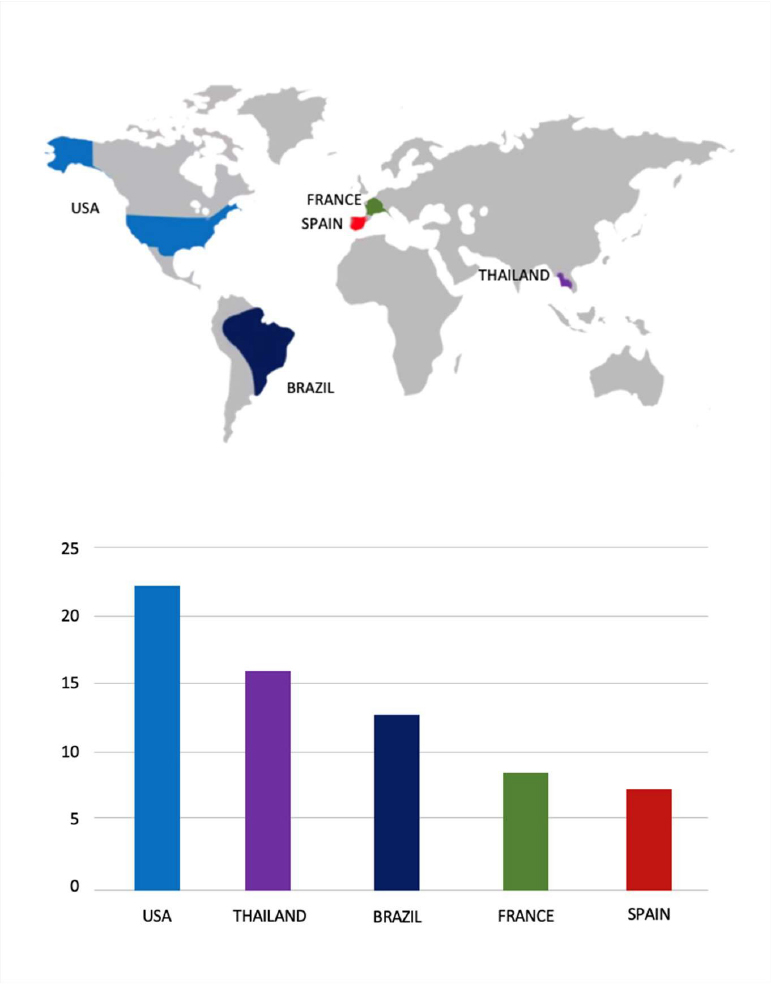
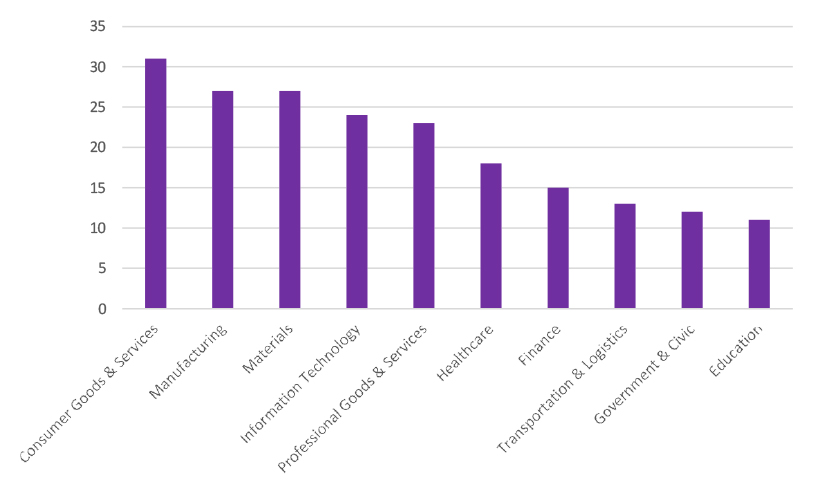
Please find the Geography-Wise and Industry-Wise breakup of cyber news for the last 5 days as part of the situational awareness pillar.
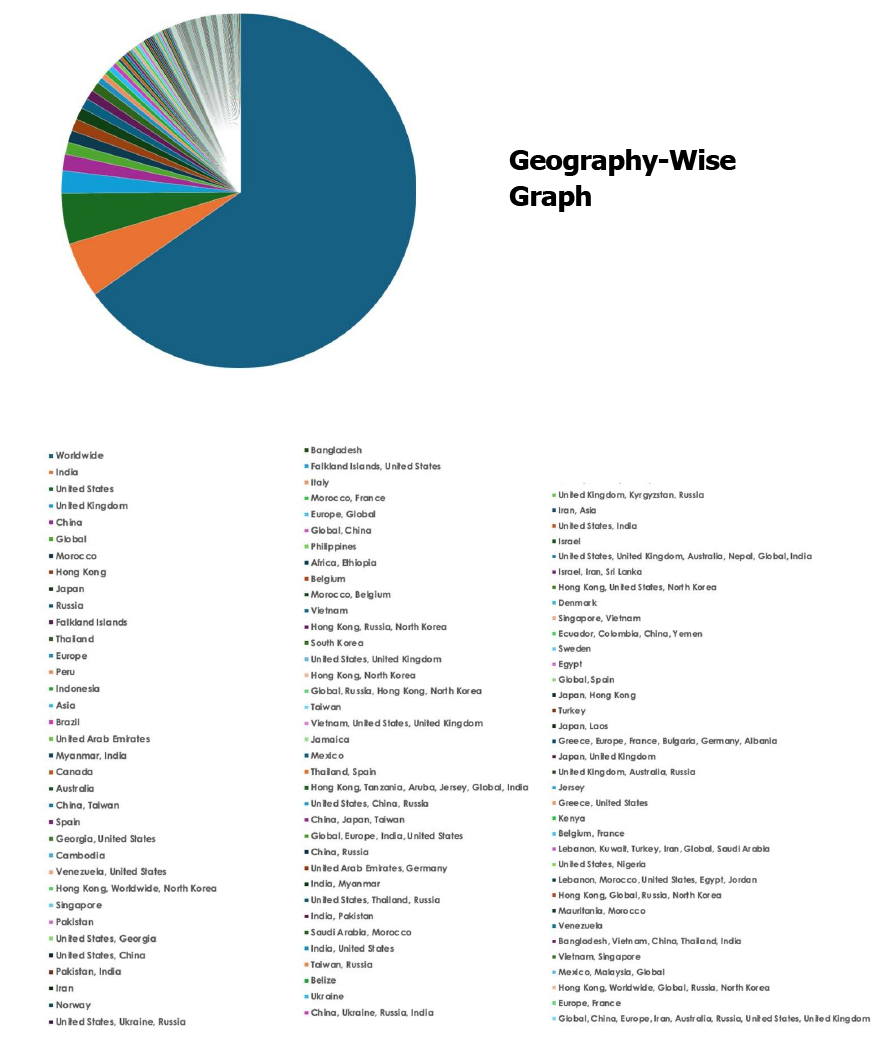
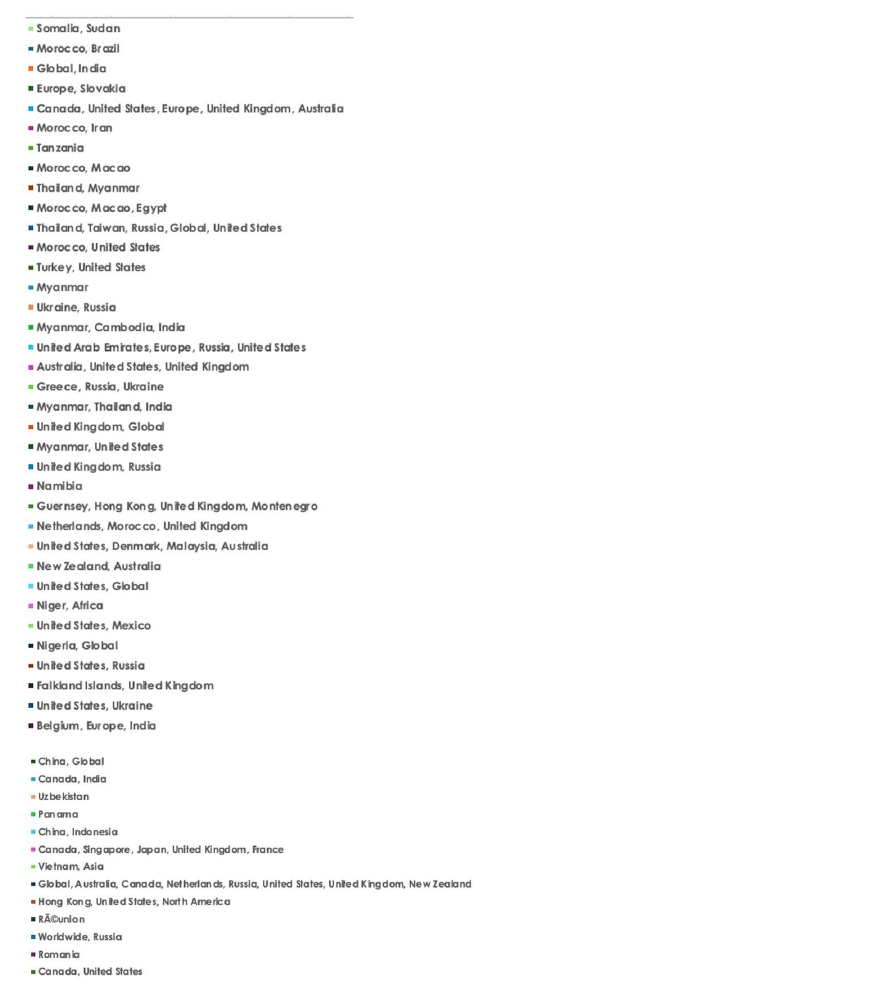
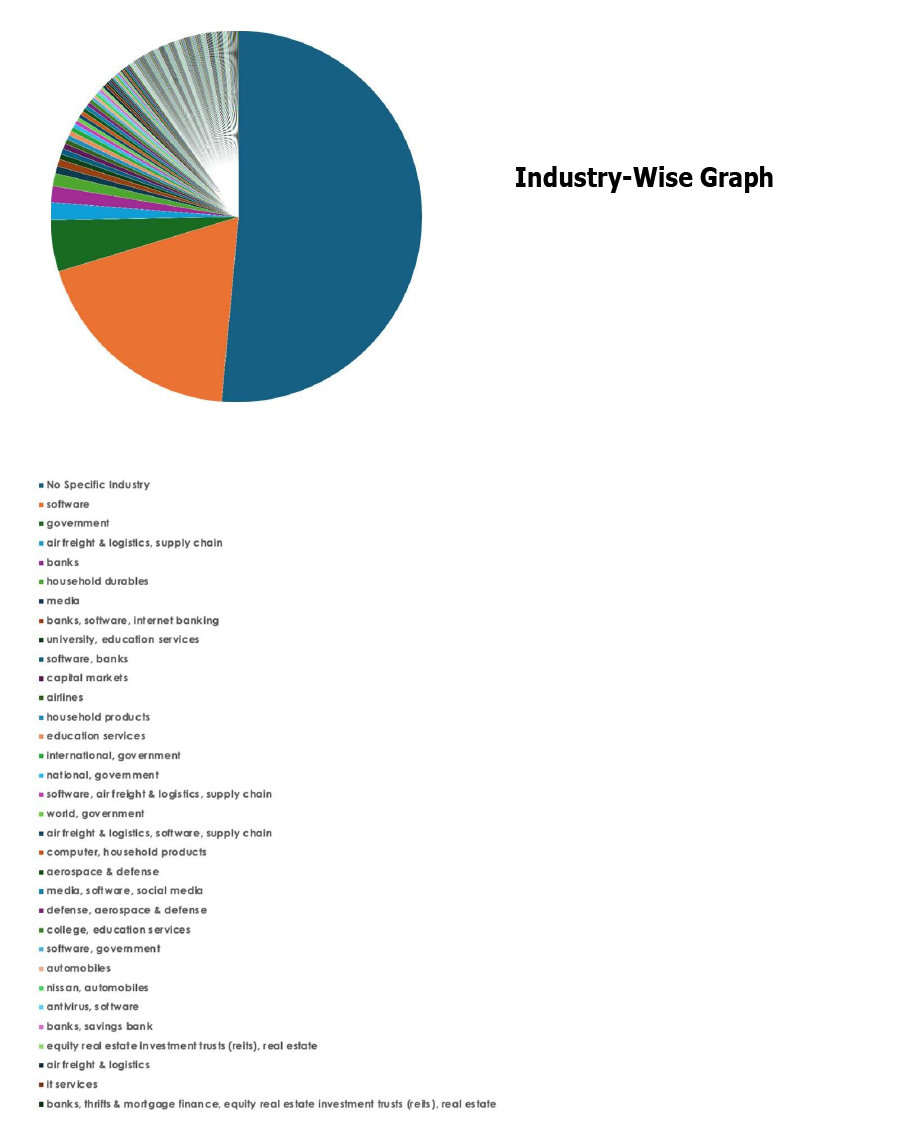
For situational awareness intelligence and specific insights mapped to your organisation’s geography, industry, and technology, please access DeCYFIR.