


The cyber threat landscape in the Philippines has intensified significantly over the past year as rapid digital adoption continues to outpace security maturity across government, businesses, and critical services. Cyber activity is no longer limited to isolated technical breaches but has evolved into large-scale, automated, and increasingly AI-driven campaigns that target trust, identity, and service continuity. Widespread data exposures, rising fraud, and ransomware incidents, particularly affecting healthcare, financial services, and critical infrastructure, highlight systemic weaknesses amplified by legacy systems, supply-chain dependencies, and expanded online services. These risks are further compounded by regional geopolitical tensions, which have driven sustained cyber-espionage and pre-positioning activity against sensitive national sectors. While the government has taken meaningful steps to strengthen cybersecurity policy and defense capabilities, the overall risk environment remains elevated, requiring sustained focus on resilience, coordinated defense, and the protection of public trust as cyber threats increasingly intersect with national security and economic stability.
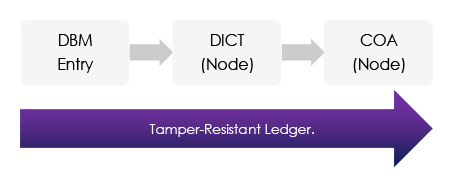
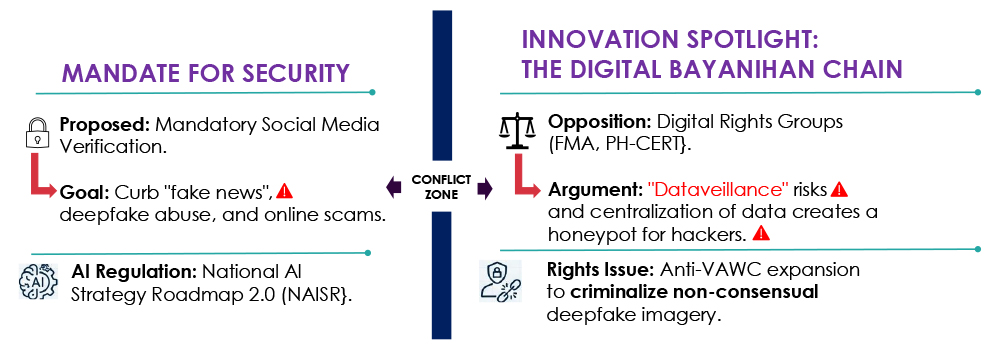
Global First : Integrating blockchain into the 2026 General Appropriations Act (GAA).
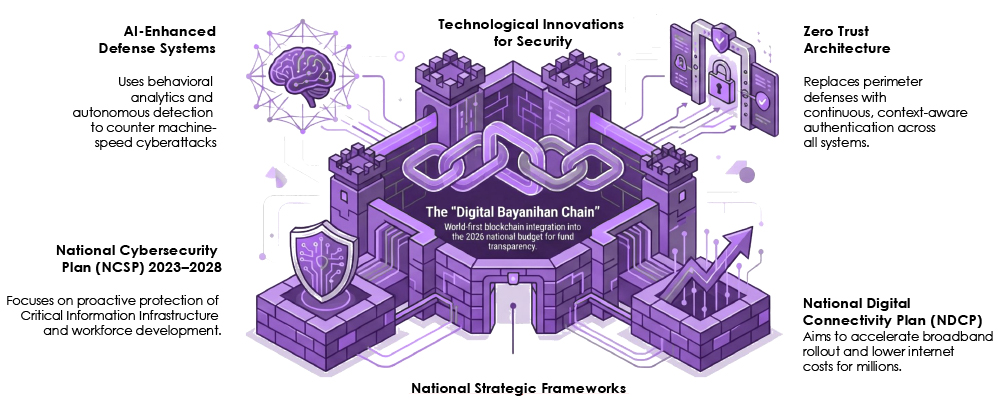
The Philippines is implementing a multi-faceted resilience strategy to protect its digital borders and citizens. This approach integrates high-level government roadmaps with pioneering technologies like blockchain and AI to secure critical infrastructure and public trust.
| IMPACT DOMAIN | Mandatory Verification | Al Regulation |
| SECURITY | HIGH (Risk Mitigation) | HIGH (Control) |
| PRIVACY | HIGH (Erosion) | MEDIUM (Oversight) |
| INNOVATION | MEDIUM (Compliance) | HIGH (Stifling Risk) |
| PUBLIC TRUST | LOW (Surveillance Fear) | MEDIUM (Confidence) |
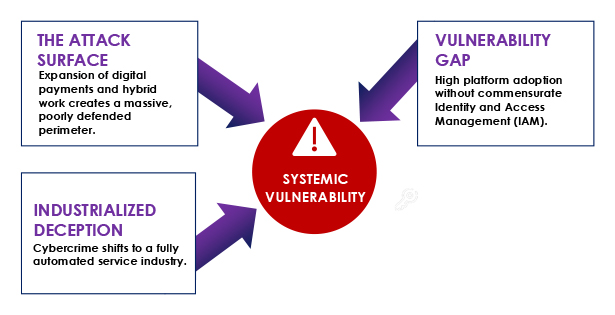
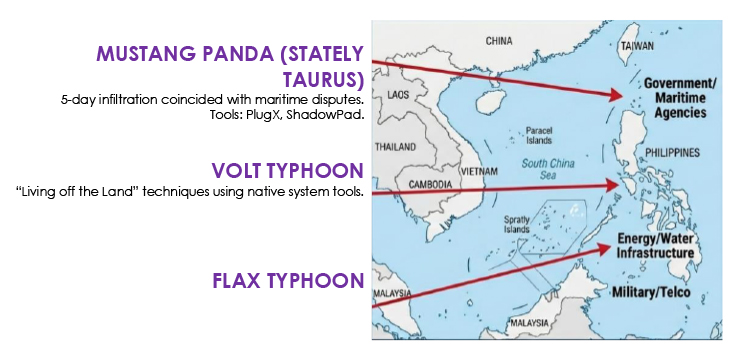
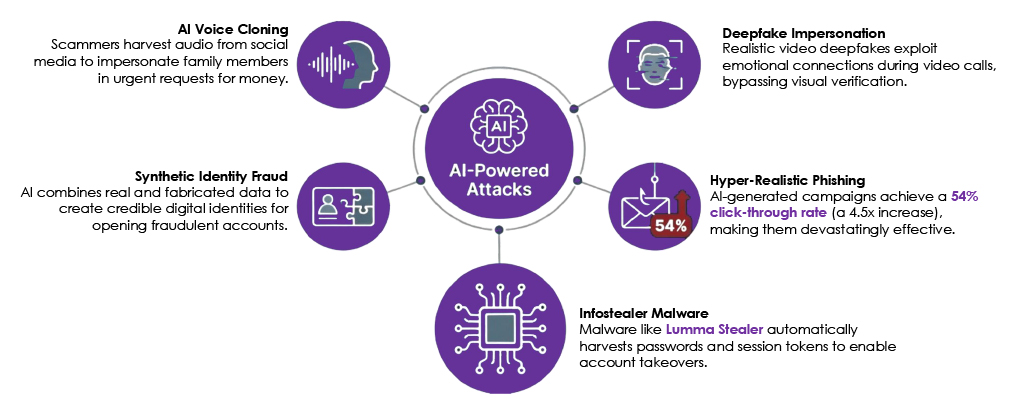
The broader threat environment in the Philippines has entered an era of industrialized deception, where rapid digitalization and high internet penetration are being exploited by automated, machine-speed cyber campaigns. The threat landscape has intensified significantly, with Q3 2025 registering a sharp increase in breach activity that led to the compromise of over 52 million user credentials, reflecting a rapidly escalating risk environment. This escalation is increasingly driven by the AI-fication of threats, including deepfake-as-a-service, real-time voice cloning, and autonomous extortion mechanisms that undermine digital trust and bypass traditional security controls. Beyond financially motivated activity, geopolitical tensions in the South China Sea elevate national cyber risk, with Chinese state-sponsored APT groups conducting cyber-espionage, persistent surveillance, and pre-positioning of disruptive malware against government entities and military telecommunications. These pressures are further compounded by systemic supply-chain vulnerabilities, as a large proportion of organizations report adverse impacts from third-party breaches, while environmental and social stressors such as super typhoons, power outages, and mass anti-corruption protests act as force multipliers that strain the resilience of critical services, particularly healthcare and essential infrastructure.
Internet Penetration:
83.8% (>98M individuals)
Digital Payments:
52.8% of transaction volume
Cybersecurity Market:
$282.68M projected by 2026 (CAGR 8.10%)
Shift from Digital to Kinetic Targets
Data Exfiltration from Internet-Exposed Assets
Exploitation of Legacy and Transitional Systems
Cross-Environment Attack Pathways
Escalating Use of Botnets, AI, and Deepfake Capabilities
Supply Chain Risks Across Infrastructure and Utility Ecosystems
South China Sea tensions have tightly linked maritime disputes with cyber operations in the Philippines, driving state-sponsored espionage, infrastructure targeting, and digital disruption. Chinese APT activity increasingly aligns with real-world incidents, focusing on government, military, telecom, and maritime sectors, while risks such as GPS interference and undersea cable exposure elevate national resilience concerns. In response, the Philippines has adopted an active cyber defense posture, strengthened military cyber units, and expanded international partnerships, even as geopolitical friction fuels nationalist hacktivism and low-level cyber attacks.
78.3% of dark web threats targeting the Philippines are domestic-focused or state-linked.
The intent is pre-positioning for disruption, not just data theft.
The healthcare sector has become the most targeted industry in the Philippines, where cyberattacks now pose direct patient safety and public health risks rather than purely technical disruptions. High dark-web demand for medical data, combined with legacy systems, weak access controls, and expanding IoMT adoption, has enabled ransomware groups to paralyze hospitals, disrupt emergency care, and even extort patients directly. These cyber risks are further amplified by environmental disruptions and geopolitical activity affecting critical infrastructure, forcing the sector to shift rapidly toward Zero Trust architectures, AI-driven security, and nationally mandated resilience standards to prevent cyber incidents from cascading into life-threatening outcomes.
Threat: Ransomware (Medusa, Qilin) paralyzing operations.
Medical records are valued 10–20× higher than financial data on underground markets.
Over 60% of healthcare breaches lead to operational disruption


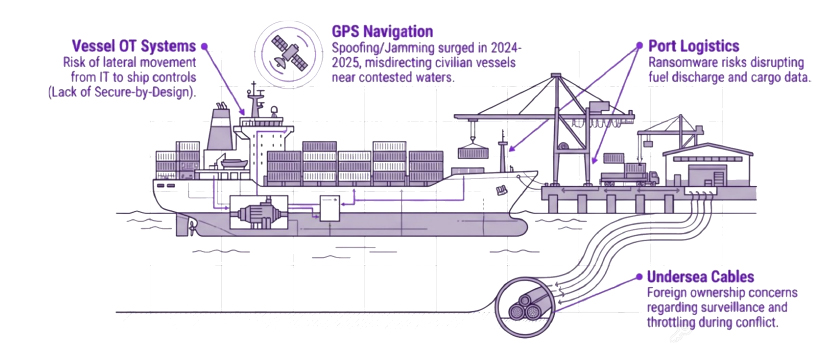
Strategic Note: Maritime trade accounts for 90% of global trade; the Philippines is a critical logistics hub.
SHIFT TOWARD NATION-STATE TARGETING
Increased activity from China- and North Korea–linked Advanced Persistent Threat (APT) groups reflects Southeast Asia’s growing geopolitical and economic importance, particularly in semiconductors, energy supply chains, critical manufacturing, and regional diplomacy.
RANSOMWARE ATTACKS BECOMING INDUSTRIALIZED
The continued rise in ransomware campaigns highlights the growing maturity of Ransomware-as-a-Service (RaaS) ecosystems. These operations are increasingly targeting a broad range of sectors, from financial services and healthcare to government and public administration, with improved operational efficiency and monetization strategies.
FINANCIAL PLATFORMS IN THE CROSSHAIRS
Threat actors are targeting Southeast Asia’s expanding digital finance ecosystem, with recent data exposure incidents highlighting systemic weaknesses that enable credential abuse, large-scale data monetization, and fraud.
CRITICAL INFRASTRUCTURE UNDER SIEGE
Telecommunications, finance, transportation, and energy sectors are facing increased targeting for both service disruption and strategic intelligence collection. These incidents highlight persistent vulnerabilities across Southeast Asia’s Critical National Information Infrastructure (CNII) and the growing convergence of cyber risk with national security concerns.
WEB APPLICATIONS & REMOTE ACCESS EXPLOITATION
Web-facing applications and remote access services remain the primary attack vectors, driven by misconfigurations, exposed APIs, unpatched vulnerabilities, and weak identity and access management (IAM) controls.
DATA BROKERAGE ON THE RISE
Leaked databases containing sensitive personal, corporate, and government-related data are increasingly traded on underground forums. This data fuels secondary attacks, including financial fraud, phishing campaigns, identity theft, and credential stuffing.
DARK WEB ECONOMY TARGETING SOUTHEAST ASIA
Access to compromised telecom systems, corporate admin panels, and government dashboards is being sold with growing frequency on dark web marketplaces. This trend signals a shift toward persistent, long-term access as a monetizable asset rather than one-off intrusions.
Geopolitical Position: Southeast Asia’s location along key global trade routes and within major power competition places the Philippines at the center of regional intelligence and influence operations affecting ASEAN coordination and cross-border policy dynamics.
Economic Significance: The Philippines role in regional trade, manufacturing, and financial flows spanning energy, logistics, and digital finance—drives interest from actors seeking economic intelligence and financial exploitation.
Critical Infrastructure Expansion: Rapid digital transformation across energy, telecom, transport, financial services, and data center infrastructure has expanded the Philippines attack surface and exposure to supply-chain compromise.
Regional and Political Influence: Cyber operations provide a covert means to shape regulatory direction and political narratives, with the Philippines regional influence amplifying downstream impacts across Southeast Asia.
Intelligence and Strategic Visibility: The Philippines scale, regulatory evolution, and regional engagement make it a high-value environment for intelligence collection on economic policy, security posture, and geopolitical alignment.
Targeting of Financial Intelligence: Banks, fintechs, and investment platforms in the Philippines hold sensitive data on transactions, investments, counterparties, and sovereign-linked assets, attracting both nation-state and financially motivated threat actors.
Data brokerage in the Philippines has surged as part of an era of industrialized deception, where large-scale breaches and AI-driven harvesting turn personal, healthcare, and government data into tradable assets. In response, the country is shifting toward Zero Trust security, stronger cyber policy, international cooperation, and transparency technologies to reduce the value and reuse of stolen data.
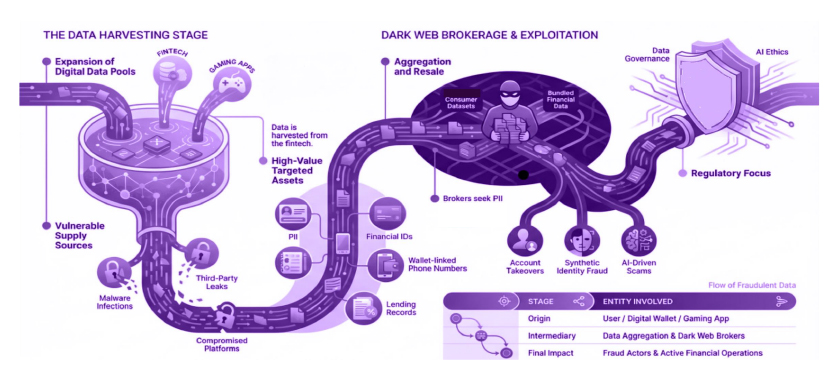
The Philippine shadow economy has entered an era of industrialized deception, where AI-driven tools enable automated fraud, deepfakes, voice cloning, and data brokerage at machine speed, fueling large-scale cybercrime and espionage. This environment is sustained by mass data breaches, underground markets for stolen identities and mule accounts, and state-linked cyber operations that pre-position malware within critical infrastructure amid geopolitical tensions. In response, the Philippines is shifting toward Zero Trust security, AI-driven defense, and stronger cyber legislation to counter threats that now outpace traditional, human-led controls.

The weaponization of AI has driven the Philippines into an era of industrialized deception, where deepfakes, voice cloning, and automated attacks undermine digital trust and bypass traditional defenses, creating a growing crisis of knowing. National response is shifting toward AI-driven security, Zero Trust models, and blockchain-based transparency, with resilience dependent on both advanced automation and strong cyber hygiene.
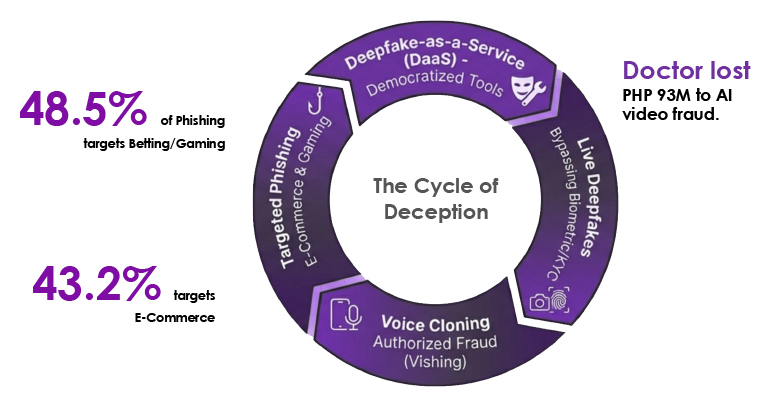
Cybercriminals are leveraging generative AI to create hyper-realistic and massively scalable attacks. These methods bypass traditional defenses and exploit human psychology with unprecedented sophistication.
Online romance scams are increasingly conducted by highly organized, cross-border criminal syndicates operating from regions such as Southeast Asia. These groups target victims in Western countries using fake dating platforms, cloned personas, and coordinated social engineering campaigns.
Attackers exploit emotional trust through prolonged interaction, gradually steering victims toward fraudulent financial transactions via digital payment channels. This human-centric approach makes detection difficult and significantly increases victim compliance.
Beyond monetary theft, romance scams are used to harvest personal, financial, and behavioral data, enabling identity theft and long-term victim exploitation. Collected data is often reused across campaigns or monetized through underground data brokers.
When victims include individuals in sensitive roles such as IT administrators, corporate employees, or government personnel, scammers can pivot from personal fraud to broader organizational compromise, enabling credential abuse, insider-assisted breaches, or intelligence collection.

Precise Target Profiling
Scammers use dark web data and social profiles to identify emotionally vulnerable individuals.

AI-Enhanced Personas
Attackers utilize AI-generated images, voice cloning, and deepfakes to build authentic-looking profiles.

Trust Manipulation
Scammers build emotional dependence through daily contact and fabricated personal crises.

Financial Monetization
Once trust is established, victims are coerced into sending money via cryptocurrency or digital wallets.

Compounded Impact
Beyond financial loss, victims face emotional distress and secondary identity theft risks.
FULLY AUTOMATED RANSOMWARE
Al agents will autonomously discover, exploit, and negotiate with victims. Cybercrime becomes fully industrialized, with minimal human involvement. Signal Red: Threat, Critical.
HARVEST NOW, DECRYPT LATER
State actors are exfiltrating encrypted intelligence now, anticipating Quantum decryption capabilities.
Signal Red: Threat, Critical.

AUTONOMOUS TRANSPARENCY
Supply chain security moves from manual audits to automated, real-time visibility and continuous validation.
Signal Red: Alert, Critical.
CYFIRMA Intelligence Assessment (Last 12 Months)
CYFIRMA is currently tracking 7 campaigns targeting central and affiliated public-sector networks.
Among those, 3 campaigns remain active and operationally adaptive in 2025:
| Campaign | Attribution | Objective | Current Focus | Status (2025) | Key Observations |
| Blue Yonder | APT41 / Volt Typhoon supporting units | Establish and maintain long-term credential footholds | Silent persistence in SSO / federation layers | Active | Infrastructure rotation every ~4–6 weeks; avoids malware; identity-first approach |
| Hegemon | APT10 / SALT-aligned contractor networks | Collection of internal documentation and policy decision intelligence | Use of MSP support channels and updater binaries | Active | Persistence maintained through “legitimate” support workflows |
| Dunan | Volt Typhoon/Salt Typhoon | Opportunistic data exfiltration for extortion leverage | Web Application and operating system | Active | Activation is exposure-driven; exploits credential weakness and misuse of remote tools |
What is Significant for the Philippines:
CYFIRMA Intelligence Assessment (Last 12 Months)
Alongside the three primary campaigns, our intelligence indicates the presence of several ongoing and repeated targeting efforts directed at organizations, highlighting sustained adversary interest.
| Campaign | Attribution | Objective | Current Focus | Status (2025) | Key Observations |
| Thunderstorm | Volt Typhoon/Salt Typhoon | Establish weakness of hosts and maintain extended duration digital presence | Silent persistence and lateral movement | Active | Initial access to target organizations using phishing attacks, vulnerabilities, and exploits |
| Tumen | Lazarus Group | To target organizations in key sectors that help in the GDP growth of Southeast Asian Nations | Collection of sensitive information, targeted attacks with clear outcomes | Partially Active | Deployment of malware for long-term exfiltration and evading detection |
| N43QIL | Lazarus Group | Dual motive of exfiltration of data and monetary benefits | Look for credential compromise and leverage it to encrypt key data stored in systems | Partially Active | Exploiting the weakness in the system, Malware Implant, and lateral movement |
| Hwasong | Lazarus Group | Dual motive: Exfiltration of data for Chinese in return for monetary benefits for North Koreans. | Credential stealing for elevated access and leverage it to encrypt key data stored in systems | Active | Carry out ransomware attacks, exploit weakness in applications, stealing credentials to cause service disruption, financial loss |
What is Significant for the Philippines :
This section translates adversary behaviors into actionable steps that ministries and national security stakeholders can implement. Each recommendation is tied directly to active campaign TTPs to ensure relevance and impact.
| Campaign Behaviour | Weakness Exploited | Required Countermeasure | Strategic Benefit |
| Blue Yonder: Credential & token-based persistence across federated SSO | Identity & session trust | Identity Threat Analytics + session anomaly baselining across all IdPs | Detects session replay and token theft that bypass MFA |
| Hegemon: Persistence via update channels and MSP support workflows | Supplier operational authority | Mandatory software update provenance verification + MSP access timeboxing and session recording | Removes the quietest long-term foothold currently in use |
| Thunderstorm: Remote access impersonation for privilege escalation | Admin workstation trust | Application control on privileged systems + lateral movement anomaly alerts | Prevents silent privilege escalation without architecture changes |
| Tumen: Initial access through phishing and exploiting vulnerabilities and maintain silent persistence. | Identity and access management controls | Enhance EDR coverage and implement network segmentation and firewall rules to restrict and monitor lateral movement, enforce least privilege and strong MFA. | Establish persistence, which prevents data theft and operational disruption without triggering alerts. |
| N43QIL: Deploys customized malware for long term exfiltration. | Unpatched endpoints and weak email security. Exploiting specific vulnerabilities in public-facing software | Patch management acceleration and vulnerability prioritization for external assets. | Acquisition of strategic intelligence and trade data supporting economic advantage.
Long-term access to sensitive governmental and industrial information. |
| Dunan: Deploys customized malware, exploits the weakness of the asset, and performs lateral movement across the network | Poor credential management and lack of network segmentation. | Deploy comprehensive anti-ransomware solutions with behavioral detection. Maintain immutable, offline backups and test recovery procedures. | Financial gain via extortion and ransom payments. • Data theft and reputational damage to coerce victims into compliance. |
| Hwasong: Initial access through exploitation of weakness in application, supply chain, credential stealing to carry out ransomware attacks. | Exploiting specific vulnerabilities in public-facing software, weak credentials | Patch management acceleration, Deploy comprehensive anti-ransomware solutions with behavioral detection. Maintain immutable, offline backups and test recovery procedures, Enhance EDR coverage and implement network segmentation. | Financial gain via extortion and ransom payments, Long-term access to sensitive governmental and industrial information. |
This section translates the campaign-aligned countermeasures into measurable targets, policy levers, and near-term execution steps. The goal is to provide leadership with clear metrics to demand, tailwinds to leverage, and a 30/60/90-day action plan that drives visible security improvement across ministries and SIs.
METRICS YOU SHOULD DEMAND (BOARD-LEGIBLE, NOT VANITY)
STRATEGIC TAILWINDS YOU CAN LEVERAGE
“IF WE WERE IN YOUR CHAIR” – NEXT 30/60/90
UNIFIED THREAT VISIBILITY FRAMEWORK
Applicable Campaigns: Thunderstorm, Blue Yonder, Hwasong
Applicable Threat Actors: APT41, Volt Typhoon, Salt Typhoon, Lazarus Group.
Applicable Campaigns: Dunan, Hegemon
Applicable Threat Actors: APT41, Volt Typhoon, Salt Typhoon
Applicable Campaigns: Thunderstorm, Blue Yonder, Hegemon
Applicable Threat Actors: APT41, Volt Typhoon, Salt Typhoon.
Applicable Campaigns: All.
Applicable Threat Actors: All.
Applicable Campaigns: All.
Applicable Threat Actors: All.
Applicable Campaigns: All.
Applicable Threat Actors: All.
Applicable Campaigns: All.
Applicable Threat Actors: All.
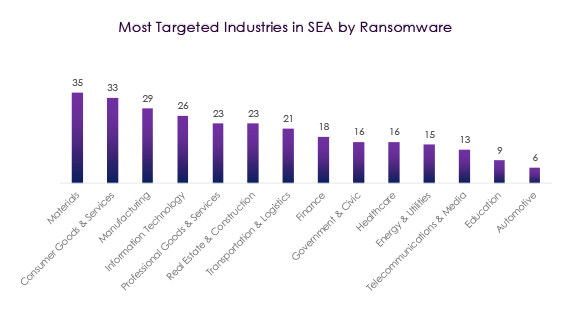
Ransomware activity in Southeast Asia is heavily concentrated in asset-intensive and operationally critical sectors, with Materials (35) and Consumer Goods & Services (33) emerging as the most targeted, underscoring attacker focus on supply-chain–dependent industries where downtime rapidly converts into financial pressure. Manufacturing (29) and Information Technology (26) follow, reflecting exposure from legacy environments, complex vendor ecosystems, and high-value data. Professional Goods & Services (23) and Real Estate & Construction (23) remain attractive due to fragmented operations and uneven security maturity, while Transportation & Logistics (21) and Finance (18) indicate a growing emphasis on service disruption and monetizable data. Government & Civic (16) and Healthcare (16) continue to face elevated risk driven by urgency-based payment dynamics, with Energy & Utilities (15) and Telecommunications & Media (13) representing high-impact disruption targets. Overall, the distribution highlights adversary preference for sectors with low tolerance for operational outages and high extortion leverage, rather than purely data-centric targeting.
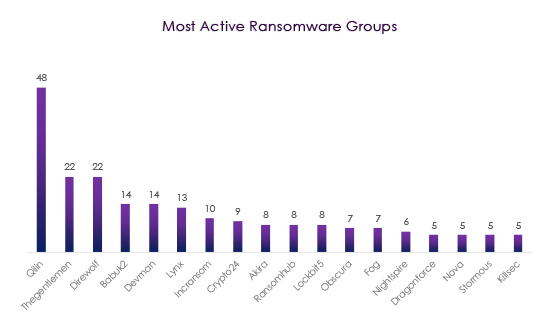
Ransomware activity in Southeast Asia remains highly active and fragmented, led by Qilin (48 incidents), which now clearly dominates regional operations. A strong second tier TheGentlemen (22) and Direwolf (22), reflects sustained, organized campaigns, while Babuk2 (14), Devman (14), and Lynx (13) add consistent pressure across the region. Mid-volume groups such as Incransom (10), Crypto24 (9), and Akira, Ransomhub, and LockBit5 (8 each) indicate broad tooling reuse rather than novel capability development. The long tail of low-volume actors (Obscura, Fog, Nightspire, Dragonforce, Nova, Stormous, Killsec) highlights high attacker churn and rebranding. Overall, the landscape is persistent, opportunistic, and dominated by double-extortion ransomware, with primary targeting focused on manufacturing, IT services, logistics, and SMBs where disruption yields rapid leverage.
Note: The authenticity of the below breaches remains unverified at the time of reporting, as the claims originate solely from the threat actor.
Date: 31 January 2026
Actor: Unknown (leak source not identified)
Claim: Exposure of the database related to French substitute doctors
Scale: 23,535 physicians (as reported)
The leaked material was described as a database linked to substitute doctors in France, likely originating from an administrative or professional healthcare registry. The exposed records reportedly included personal and professional details such as names, contact information, practice locations, registration numbers, and validity dates. Although the authenticity and full scope remain unverified, the exposure raises concerns about the protection of healthcare workforce data and the risk of phishing, fraud, and misuse of professional credentials.
Date: 26 January 2026
Actor: Unknown (publicly disclosed breach; threat actor not identified)
Claim: Exposure of Lena Health patient data and communications
Scale: 2,000+ patients; tens of thousands of call records (as reported)
The breach involved a full data dump linked to Lena Health, exposing sensitive medical data of over 2,000 patients, including clinical records and thousands of recorded calls. The data reportedly stemmed from improperly secured cloud infrastructure and third-party integrations. Although unverified, the incident raises serious concerns about patient data protection and risks from cloud misconfigurations in healthcare systems.
Date: 23 January 2026
Actor: Unknown (leak source not identified)
Claim: Exposure of the Taiwan-based health, medical, and life insurance database
Scale: ~2.9 million records (as reported)
The leaked dataset was described as a large CSV file containing personal and insurance-related information on individuals across Taiwan, including demographic data, identifiers, and health or insurance attributes. Although the authenticity and exact source remain unverified, the scale of the exposure raises serious concerns about data protection practices and presents heightened risks of identity fraud, insurance abuse, and privacy violations involving sensitive health information.
Date: 12 January 2026
Actor: Unknown (data scraping activity; actor not identified)
Claim: Exposure of Mon Logiciel Médical patient data linked to Ameli
Scale: 19+ million patient records (as reported)
The incident stemmed from a large-scale data scraping activity in 2025 affecting Mon Logiciel Médical, a SaaS medical platform linked to Ameli, France’s national health insurance system. The exposed data reportedly included patient names, contact details, dates of birth, gender, and addresses. Although the authenticity remains unverified, the scale and sensitivity of the records suggest a significant impact on patient privacy and raise serious concerns about data protection and the security of third-party digital health services integrated with national healthcare infrastructure.
Date: 3 January 2026
Actor: Unknown (leak source not identified)
Claim: Exposure of the Philippine Army’s classified military documents
Scale: 81 documents (as reported)
The leaked material was described as top secret Philippine Army manuals, allegedly originating from internal military systems and intended strictly for authorized use. The documents reportedly include operational, tactical, or training-related content, indicating a high-sensitivity classification level. While the authenticity of the materials remains unverified, the volume and nature of the files suggest a serious security breach affecting a core national defense organization. If confirmed, the incident poses significant risks to operational security, military readiness, and broader national security through potential misuse or dissemination of classified information.
Date: 18 October 2025
Actor: Dark web user (alias not specified)
Claim: Sale of the Philippine government’s COVID-19 vaccination database
Scale: ~1 million individual records (as advertised)
The actor claimed the dataset is an SQL database originating from a Philippine government public health system and contains COVID-19 vaccination records, including sensitive personal and demographic information. Sample data referenced individuals from Cebu, with indications that records from additional cities may also be included. Although the authenticity of the dataset remains unverified, the exposure suggests a significant security lapse within a government health-related organization. If genuine, the incident poses elevated risks of privacy violations, identity misuse, and secondary abuse of large-scale health data collected during the COVID-19 response.
Date: 15 September 2025
Actor: Unknown (data leak source not identified)
Claim: Exposure of RCC College Philippines user database
Scale: Unspecified (database sample shared)
The leaked material was described as a database sample originating from RCC College Philippines and appears to contain student and staff records. The exposed fields reportedly include full names, identification numbers, and enrollment-related details, suggesting extraction from an internal academic or administrative system. While the full scope and authenticity of the dataset remain unverified, the presence of structured records indicates a potential compromise of institutional systems. If confirmed, the incident presents risks of privacy violations, identity misuse, and targeted social engineering against affected individuals.
Most Exploited Vulnerabilities in Southeast Asia – Last 3 months
| Exploited Vulnerabilities | Vendor | Product | Threat Actor Attribution |
| CVE-2025-64446 | Fortinet | Fortinet FortiWeb | N/A |
| CVE-2025-59287 | Microsoft | Windows Server Update Service | Chinese APT groups actively used to distribute the Shadowpad backdoor malware |
| CVE-2025-55182 | Meta | React Server Components | Distinct Campaigns are very actively leveraging this vulnerability to deploy several backdoors |
| CVE-2025-34028 | Commvault | Commvault Command Center | N/A |
| CVE-2025-31324 | SAP | NetWeaver | APT41, BianLian Ransomware groups were actively exploiting this vulnerability in 2025 in Taiwan, India, and Germany |
| CVE-2025-24813 | Apache | Tomcat | N/A |
| CVE-2025-12480 | Gladinet | Gladinet CentreStack & Triofox | N/A |
| CVE-2025-4427 | Ivanti | Endpoint Manager Mobile (EPMM), formerly MobileIron Core | N/A |
| CVE-2025-0108 | Palo Alto Networks | PAN-OS | N/A |
| CVE-2024-53704 | SonicWall | SonicOS | N/A |
All the observed exploited vulnerabilities in the above list are also part of the CISA Known Exploited Vulnerability list.