


Telegram is no longer just a messaging application. It has evolved into a primary operational playground for modern threat actors. What underground forums on Tor once represented, Telegram now replicates — but faster, more scalable, and significantly more accessible.
Over the past few years, elements of the cybercriminal ecosystem have progressively shifted away from traditional darknet marketplaces and closed forums toward Telegram’s hybrid architecture of public channels, private groups, and automated bots. The barriers that once required Tor access, reputation building, and escrow systems have been replaced with instant channel creation, subscription-based malware distribution, real-time broadcasting, and bot-enabled commerce.
Telegram’s structure provides threat actors with several strategic advantages: global reach without specialized tooling, frictionless onboarding of buyers and affiliates, integrated payment coordination, automated log search bots, rapid leak amplification, and built-in audience growth mechanisms. As a result, the platform now supports a wide spectrum of malicious activity, including:
For financially motivated actors, Telegram functions as a scalable storefront and customer support hub. For hacktivists, it serves as a mobilization and propaganda amplifier. For state-aligned operations, it offers a rapid distribution channel for narratives and leaks. In many cases, telegram complements and increasingly replaces traditional Tor-based ecosystems by removing technical friction while maintaining operational flexibility.
This shift reflects a broader platformization of cybercrime. Services are packaged, automated, subscription-based, and marketed in real time. Bots validate payments, distribute malware builds, search stolen credential logs, and manage affiliate access, all within the same ecosystem.
Telegram’s rise signals a structural change in how cyber operations are coordinated, monetized, and publicized. The underground is no longer confined to hidden services; it is increasingly embedded within mainstream platforms that combine scale, speed, and automation.
Understanding this evolution is critical for anticipating how modern threat actors organize, advertise, and execute operations in an environment where accessibility and velocity now outweigh exclusivity.
For years, Tor-based forums and darknet marketplaces formed the backbone of the cybercriminal underground. Platforms such as Hydra Market and RaidForums operated as centralized hubs where reputation, escrow systems, and restricted access defined participation. Entry required technical familiarity, and longevity depended on maintaining trust within a closed community.
However, these platforms have proven highly vulnerable to law enforcement disruption. When a major darknet marketplace is seized, or a forum is dismantled, entire ecosystems can collapse overnight. Vendors lose storefronts, reputation, histories vanish, and users scatter in search of alternatives. Rebuilding that trust structure takes time.
Telegram alters that equation.
Unlike centralized darknet forums hosted on hidden services, Telegram’s channel-based architecture allows threat actors to rapidly reconstitute their presence. If a channel is removed or restricted, a new one can be created within minutes, and subscriber migration can occur almost instantly through forwarding mechanisms and backup channels.
This resilience reduces operational downtime.
For example, the hacktivist collective “IndoHaxSec” has operated across multiple Telegram channels following restrictions and takedowns, continuing activity through successive iterations. The model is simple: maintain backup channels, redirect followers, and resume operations with minimal disruption.
This adaptability represents a structural shift in underground operations. Instead of relying on a single high-risk centralized forum, threat actors now operate within a flexible, distributed communication environment. Telegram enables persistence through redundancy, a key advantage in an era of increased law enforcement pressure on darknet infrastructure.
The underground has not abandoned Tor entirely. Rather, it has diversified. Telegram increasingly serves as the visible, rapidly replaceable layer, while more sensitive transactions may still occur elsewhere.
This shift does not signal the end of traditional underground forums. In many cases, forums still serve as the first point of advertisement, where actors post previews of stolen data, access listings, or service promotions. Increasingly, however, these posts include Telegram channel links for follow-up engagement. The forum builds visibility and credibility; Telegram handles the execution.
Rather than replacing Tor entirely, Telegram has become the operational extension of it.
Telegram hosts a broad spectrum of threat actors whose motivations range from financial gain to ideological disruption. Unlike traditional underground forums that often specialize in specific activity types, Telegram’s flexible architecture allows multiple criminal services to coexist within the same ecosystem. Channels, bots, and private groups support everything from credential resale to hacktivist coordination.
Hacktivist groups leverage Telegram as a primary coordination and broadcast platform. Channels are used to recruit volunteers, announce targets, claim responsibility for attacks, and publish leaked data. The platform’s broadcast model enables rapid amplification and audience mobilization.
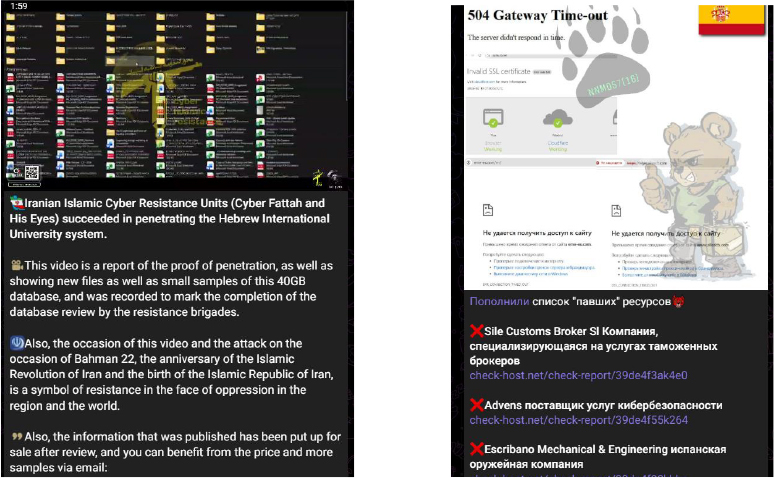
Groups such as the Cyber Fattah team and NoName057 have demonstrated how Telegram can serve both operational and psychological objectives. Claims of DDoS attacks, defacements, or data breaches are often disseminated through Telegram before appearing in mainstream reporting.
The visibility and immediacy of these announcements enhance narrative control, allowing groups to shape perception and maximize media impact regardless of the technical scale of the underlying activity.
Several ransomware operations maintain Telegram channels to publicize victims, threaten data exposure, and direct attention to dedicated leak sites. These channels often serve as an additional pressure mechanism, reinforcing extortion demands through public visibility.
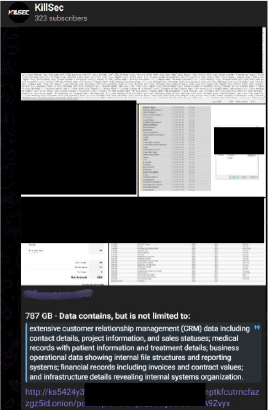
Beyond public shaming, these channels sometimes double as operational hubs. Groups may advertise affiliate programs, outline commission structures, publish targeting restrictions (e.g., excluded regions or sectors), and recruit skilled operators to support campaigns. In some cases, they explicitly seek penetration testers or trusted partners, requiring established forum reputations or deposits before collaboration.
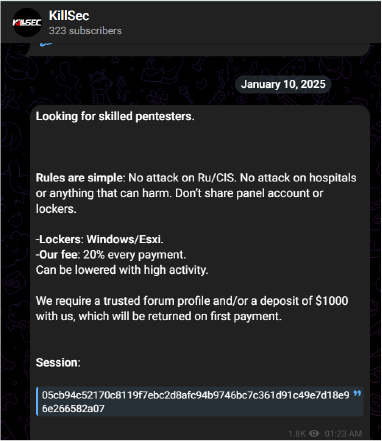
By combining negotiation, recruitment, intimidation, and amplification within a single platform, Telegram increases the psychological and operational leverage applied to victims. Posts may include countdowns, sample data screenshots, or statements intended to attract media attention.
This use of Telegram complements traditional ransomware infrastructure, transforming it into both a communication and coordination layer that extends beyond the technical breach itself.
Telegram is widely used to advertise and broker unauthorized access to corporate environments, including VPN, RDP, cloud accounts, and domain administrator credentials. Listings often include company revenue, geographic location, sector, and level of privilege, allowing buyers to quickly assess value.
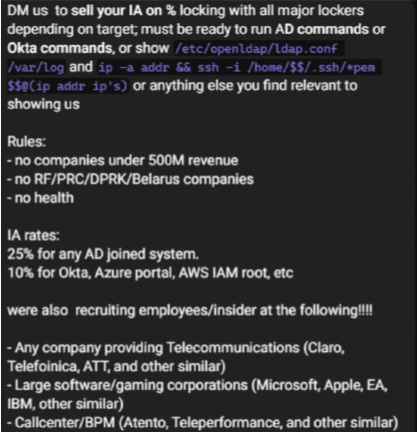
In addition to simple listings, many brokers require technical proof of access before negotiations proceed. Sellers may be asked to demonstrate Active Directory domain control, provide configuration files, share command outputs, or validate access to platforms such as Okta, Azure, or AWS IAM. This real-time validation model reduces fraud and accelerates deal-making.
Unlike traditional darknet forums where access to sales required extended negotiation or escrow mechanisms, Telegram enables rapid, direct communication between broker and buyer. Many sellers maintain dedicated channels for advertising while moving detailed discussions into private chats.
This streamlined model accelerates monetization and supports the broader ransomware ecosystem, where purchased access is frequently leveraged for lateral movement and eventual data exfiltration or encryption. The visibility, validation, and speed provided by Telegram reduce transaction friction and shorten the operational cycle between initial compromise and full-scale intrusion.
Telegram functions as a distribution and support hub for subscription-based malware offerings, including loaders, stealers, crypters, and phishing kits. Operators use channels to advertise features, post update logs, share testimonials, and announce new builds.
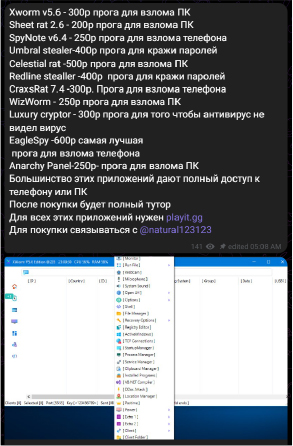
Unlike traditional underground forums, where malware sales relied heavily on reputation threads, Telegram allows operators to manage marketing, customer support, and version updates within a single ecosystem. Some vendors integrate bots for automated build generation or subscription validation, further streamlining the service model.
This structure reflects the broader platformization of cybercrime: malware is packaged, branded, updated, and supported like legitimate software products. Telegram reduces operational overhead while expanding reach to a global customer base.
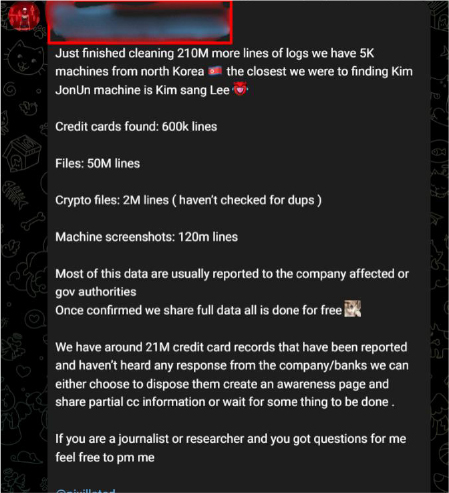
Telegram also hosts channels dedicated to advertising stolen databases, breached user records, and scraped datasets. Sellers frequently post previews of partial data samples or screenshots to validate authenticity before directing buyers to private negotiation channels.
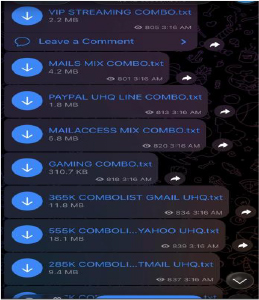
Unlike static forum posts, Telegram enables continuous reposting and resharing of leaked data across multiple channels, increasing exposure and resale opportunities. The forwarding feature allows datasets to circulate rapidly across interconnected communities.
This dynamic environment increases the speed at which breached information spreads, complicating containment efforts and extending the lifecycle of compromised data.
Telegram does not merely host isolated criminal services, it enables an interconnected ecosystem where advertisement, automation, monetization, and operational activity coexist within a single platform. Unlike traditional darknet forums that separate discussion, escrow, and distribution functions, Telegram consolidates these processes into a layered environment.
At the foundation is the discovery layer, where public channels and cross-platform advertisements attract followers and establish visibility. In many cases, underground forum posts redirect users to Telegram for further engagement.
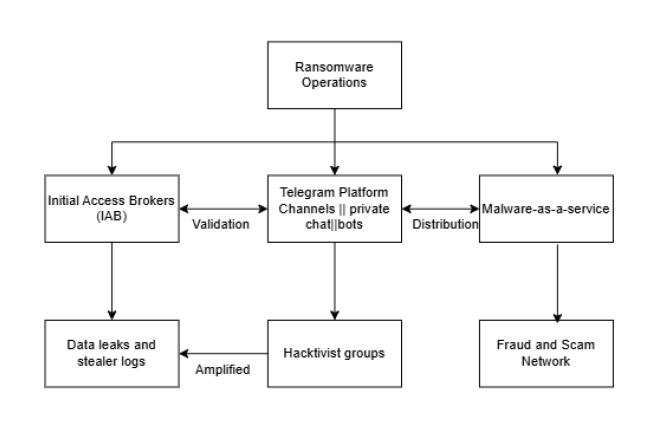
Telegram as a Coordination Layer in the Cybercrime Ecosystem
Above this sits the marketplace layer, where stolen credentials, corporate access, malware subscriptions, and leaked databases are actively promoted. Sellers maintain dedicated channels to broadcast offerings and migrate negotiations into private chats.
The automation layer distinguishes Telegram from legacy underground spaces. Bots facilitate searchable log databases, subscription validation, build generation, and payment confirmation. This automation reduces friction and increases scalability, enabling services to function in near real time.
At the top is the operational and amplification layer. Hacktivist groups coordinate campaigns, ransomware operators publicize victims, and actors broadcast breach claims to maximize psychological and media impact.
Together, these layers form a resilient and scalable cybercrime infrastructure model. Telegram’s architecture allows rapid regeneration of disrupted channels, seamless migration of audiences, and integration of automated service delivery characteristics that enhance both persistence and operational velocity.
Telegram has emerged as a structural layer within the modern cybercriminal ecosystem. It does not replace darknet forums, but enhances them by accelerating negotiation, recruitment, validation, and public amplification.
Its resilience, automation capabilities, and hybrid public–private communication model reduce operational friction for ransomware groups, Initial Access Brokers, malware operators, and hacktivist collectives.
Rather than serving merely as a messaging tool, Telegram functions as a connective infrastructure linking access brokers to ransomware affiliates, leak channels to media visibility, and recruitment posts to active operations.
As cybercriminal ecosystems continue to adapt, platforms that combine scalability, persistence, and low entry barriers will remain attractive operational environments. Telegram represents a clear example of this evolution.