


CVE-2025-8671, dubbed “MadeYouReset“, is a newly disclosed HTTP/2 denial-of-service (DoS) vulnerability identified by researchers at Tel Aviv University and Imperva. It exploits a weakness in some HTTP/2 implementations that incorrectly treat server-sent stream resets as stream closures. Attackers can trigger servers to reset streams using crafted HTTP/2 frames (e.g., malformed WINDOW_UPDATE, PRIORITY, or data frames), while backend processing continues-thus bypassing the standard MAX_CONCURRENT_STREAMS limit and exhausting server resources. The vulnerability bypasses previous protections implemented against the 2023 “Rapid Reset” (CVE-2023-44487) attack and affects a broad range of servers and libraries (e.g., Apache Tomcat, Netty, Varnish, Fastly, F5, SUSE, Wind River). Although no exploitation in the wild has been confirmed, patches and mitigations are being actively released by vendors.
On August 13, 2025, researchers publicly disclosed a new HTTP/2 vulnerability known as “MadeYouReset” (CVE-2025-8671), which allows attackers to cause denial-of-service by exploiting mismatches in stream accounting within HTTP/2 server implementations. Unlike previous attacks, such as Rapid Reset (CVE-2023-44487), which used client-sent cancellations to overwhelm servers, MadeYouReset coerces the server into sending stream resets via crafted, often innocuous-looking frames-circumventing earlier mitigations. This report-prepared by CYFIRMA-provides a concise overview of the vulnerability, its impact, affected versions, mitigation strategies, and concluding insights.
MadeYouReset results from a flawed implementation where server-initiated stream resets (RST_STREAM) are treated as protocol-level closures, while backend processing continues. Attackers send malformed or edge-case HTTP/2 frames-such as invalid WINDOW_UPDATE increments, improper PRIORITY frames, or frames on half-closed streams-to trigger server-side resets. The server acknowledges the stream as closed, freeing it at the protocol level, but continues processing the request. This discrepancy allows attackers to bypass the concurrent stream limit and flood the server with backend work, leading to resource exhaustion and potential denial-of-service.
Multiple vendor products are vulnerable:
Is there already an exploit tool to attack this vulnerability?
Yes. As of now, there are some publicly available proof-of-concept (PoC) exploit tools targeting CVE-2025-8671 (MadeYouReset). Security disclosures (from sources like SUSE, Cloudflare, Netty, and Wind River) describe vulnerability and remediation.
Has this vulnerability already been used in an attack?
No confirmed in-the-wild exploitation has been reported. SUSE’s advisory explicitly notes that prior to August 13, 2025, there were no known attacks leveraging MadeYouReset. Other sources focus on describing the risk and mitigation, with no mention of active exploitation.
Are hackers discussing this vulnerability in the Deep/Dark Web?
There is no evidence that discussions, PoC trading, or exploit chatter on dark web or underground forums currently exist. All public information-CVE entries, vendor advisories, technical blogs-reflects coordinated, responsible disclosure.
What is the attack complexity level?
The attack can be classified as LOW complexity in implementation-assuming one understands how to craft HTTP/2 control-frame anomalies to induce server-side RST_STREAM behavior. However, because no PoC currently exists and deployment environments vary, it remains theoretical as of now. The underlying exploitation mechanics are straightforward based on technical write-ups, but real-world execution would require custom tooling and precise control.
The attack leverages improper handling of HTTP/2 stream resets in lighttpd versions prior to 1.4.80. The exploitation sequence is twofold: reconnaissance and exploitation.
Vulnerability Detection and Reconnaissance
The attack first identifies whether the target web service is running a vulnerable instance of lighttpd. This is achieved by establishing a TCP connection to the specified host and port, sending a lightweight HTTP HEAD request, and parsing the Server’s response header. The version string is compared against the fixed version (1.4.80). If the version is lower, the service is flagged as vulnerable. This phase ensures that exploitation attempts are only directed toward susceptible systems.
Exploitation – HTTP/2 Stream Abuse
Once confirmed, the attacker initiates a raw TCP session to the HTTP/2 service port (commonly 8080 or HTTPS). Using an HTTP/2 client implementation (such as hyper-h2), the attacker negotiates an HTTP/2 session and sends a connection preface.
The exploit core involves rapidly creating new streams using HEADERS frames (typically GET requests to /) and then immediately sending RST_STREAM frames to reset them. Each reset forces the server to allocate and then prematurely tear down internal resources. When executed repeatedly (count parameter) or continuously, the server’s thread pool, memory buffers, or connection queues become saturated. This resource exhaustion results in degraded performance or complete denial of service.
Attack Characteristics
Statelessness: No authentication or session tokens are required; the attack can originate remotely.
Low Bandwidth: The payload size is small (stream creation and reset frames). The power lies in volume and concurrency.
Impact: Causes service unavailability, timeouts, or process crashes.
Apply vendor-released security updates immediately, including Apache Tomcat, Netty, Varnish, F5, Fastly, and SUSE. Temporarily disabling HTTP/2 or routing traffic via HTTP/1.1 can reduce exposure. Enforce stricter protocol validation-drop or treat malformed WINDOW_UPDATE, PRIORITY, or control frames as connection errors rather than stream errors. Implement control-frame rate limiting, per-client connection rate/cap, and monitor anomalies like high RST_STREAM generation or mismatched request processing patterns. Automated detection combined with traffic shaping or blocking of offending connections can further reduce risk until fully patched.
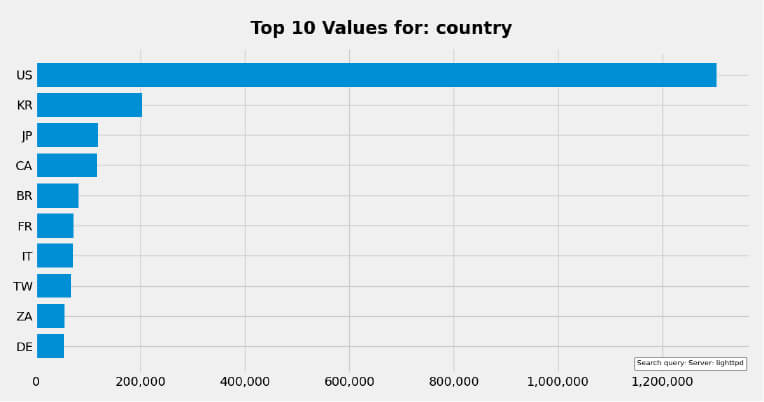
Target Geography
The reach of CVE-2025-8671, known as MadeYouReset, is truly global. Any server supporting HTTP/2-be it web hosts, cloud front ends, API gateways, or edge infrastructure-worldwide could be targeted. Attackers can exploit this flaw, bypassing protocol-level stream limits and driving excessive backend processing over a single connection, enabling widespread denial-of-service threats. More than 2,837,441 instances may be vulnerable.
Target Industry
Industries most at risk include web hosting providers, cloud and CDN operators, finance and banking platforms, government services, and any enterprise relying on HTTP/2 for application delivery. These environments often handle high-volume and mission-critical traffic-successful exploitation could result in severe service disruption or outages.
Target Technology
This vulnerability stems from improper HTTP/2 stream management in implementations such as Apache Tomcat, Netty, Jetty, Varnish, Fastly, F5, AMPHP, Wind River, and others-including newer web servers like lighttpd and the Rust h2 library. The flaw allows attackers to trigger server-side RST_STREAM resets via crafted control frames (e.g., WINDOW_UPDATE with zero increment, invalid PRIORITY frames, HEADERS, or DATA on closed streams)-causing backend processing to continue while the protocol treats streams as closed, effectively circumventing concurrency limits and leading to resource exhaustion.
Currently, there are no threat actors actively discussing the vulnerability. However, the CYFIRMA Research team is continuously monitoring for new developments or discussions.
MadeYouReset signals that even well-crafted mitigations like those for Rapid Reset may be sidestepped by subtle protocol behaviours. Organizations must maintain vigilance, align implementation behaviour with protocol specifications, and monitor anomalous stream processing patterns. Applying updates, hardening HTTP/2 validation, and gaining visibility into control-frame handling are crucial to safeguarding availability and resilience.